Introduction
In an era where cyber threats are not just common but alarmingly advanced, the healthcare sector must urgently enhance its cybersecurity strategies. Selecting the right Endpoint Detection and Response (EDR) provider is pivotal, as it can significantly bolster an organization's ability to protect sensitive patient data and maintain operational integrity.
With so many EDR providers on the market, how can healthcare organizations ensure they choose the right one? Let’s explore some best practices for making an informed selection, so healthcare organizations can effectively combat the evolving tide of cyber threats.
Understand the Fundamentals of EDR Technology
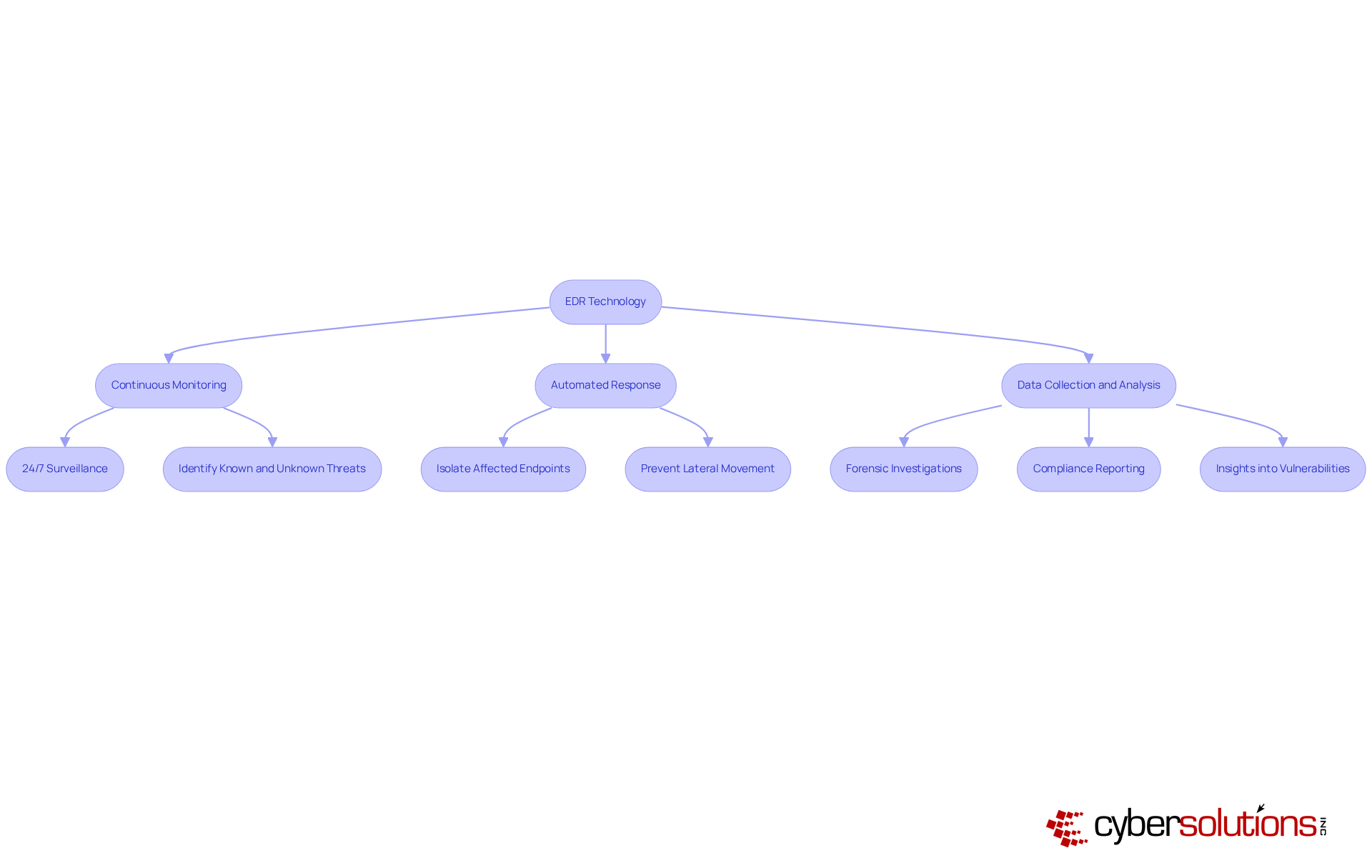
In an era where cyber threats loom larger than ever, the healthcare sector must prioritize robust cybersecurity measures to safeguard sensitive patient data. An EDR provider offers Endpoint Detection and Response (EDR) technology, which is a cornerstone of modern cybersecurity strategies, providing a strong framework for real-time risk management. EDR tools continuously monitor endpoint devices - like laptops, desktops, and servers - to identify, examine, and respond to potential threats. Here are some key functionalities of EDR:
- Continuous Monitoring: EDR systems provide 24/7 surveillance of endpoint activities, enabling immediate detection of suspicious behavior. This constant vigilance is crucial; organizations that contain breaches within 30 days can save over $1 million, underscoring the financial impact of timely responses. By leveraging advanced algorithms and machine learning, an EDR provider can enhance danger detection by identifying both known and unknown threats, including sophisticated malware and ransomware. In fact, 90% of cyberattacks and 70% of breaches originate at endpoints, highlighting the necessity of effective detection mechanisms.
- Automated Response: When a risk is detected, the EDR provider can automatically isolate affected endpoints, preventing lateral movement within the network. This capability is essential, particularly since lateral movement is now the leading cyber risk, with attacks capable of compromising up to 60% of systems in just one hour.
- Data Collection and Analysis: EDR tools gather extensive data on endpoint activities, which can be analyzed for forensic investigations and compliance reporting. This data-driven approach not only aids in prompt risk response but also strengthens long-term security strategies by providing insights into potential vulnerabilities.
Understanding these fundamentals allows organizations to appreciate the critical role of an EDR provider in protecting sensitive data and maintaining operational integrity, especially as cyber risks continue to evolve and proliferate. Without the implementation of an EDR provider, healthcare organizations risk not only their financial stability but also the trust of their patients and stakeholders.
Evaluate Key Selection Criteria for EDR Providers
In an era where cyber threats are increasingly sophisticated, the choice of an EDR provider can make or break your organization's security strategy. When selecting an EDR provider, organizations should prioritize several critical criteria to ensure alignment with their security objectives:
- Detection Capabilities: Assess the provider's proficiency in identifying a broad spectrum of threats, including zero-day vulnerabilities and advanced persistent threats (APTs). Effective detection, including behavioral detection and automated response, is essential for mitigating risks associated with sophisticated cyber attacks.
- Integration with Existing Frameworks: Verify that the EDR tool can seamlessly connect with your current security infrastructure, such as firewalls and SIEM platforms. This integration depth is essential for improving your overall security stance and ensuring comprehensive risk visibility.
- Scalability: Opt for a provider that can scale its services in line with your organization's growth, accommodating an increasing number of endpoints without sacrificing performance. This flexibility is crucial as businesses expand and evolve.
- User Experience: Evaluate the usability of the EDR platform, focusing on the interface and deployment ease. An intuitive approach allows your team to manage the system effectively, reducing the learning curve and enhancing operational efficiency.
- Support and Training: Consider the level of customer support and training provided by the vendor. Continuous support, including validation of the analyst staffing model and SLA details, is crucial for enhancing the efficiency of the EDR system and ensuring your team is adequately prepared to address challenges.
With so many options available, how can organizations ensure they choose the right EDR provider? Taking the time to evaluate these criteria ensures that your organization selects an EDR provider that aligns with both your immediate security needs and your long-term cybersecurity goals. Selecting the appropriate EDR provider is not merely a choice; it is a crucial step in strengthening your organization against the ongoing wave of cyber threats.

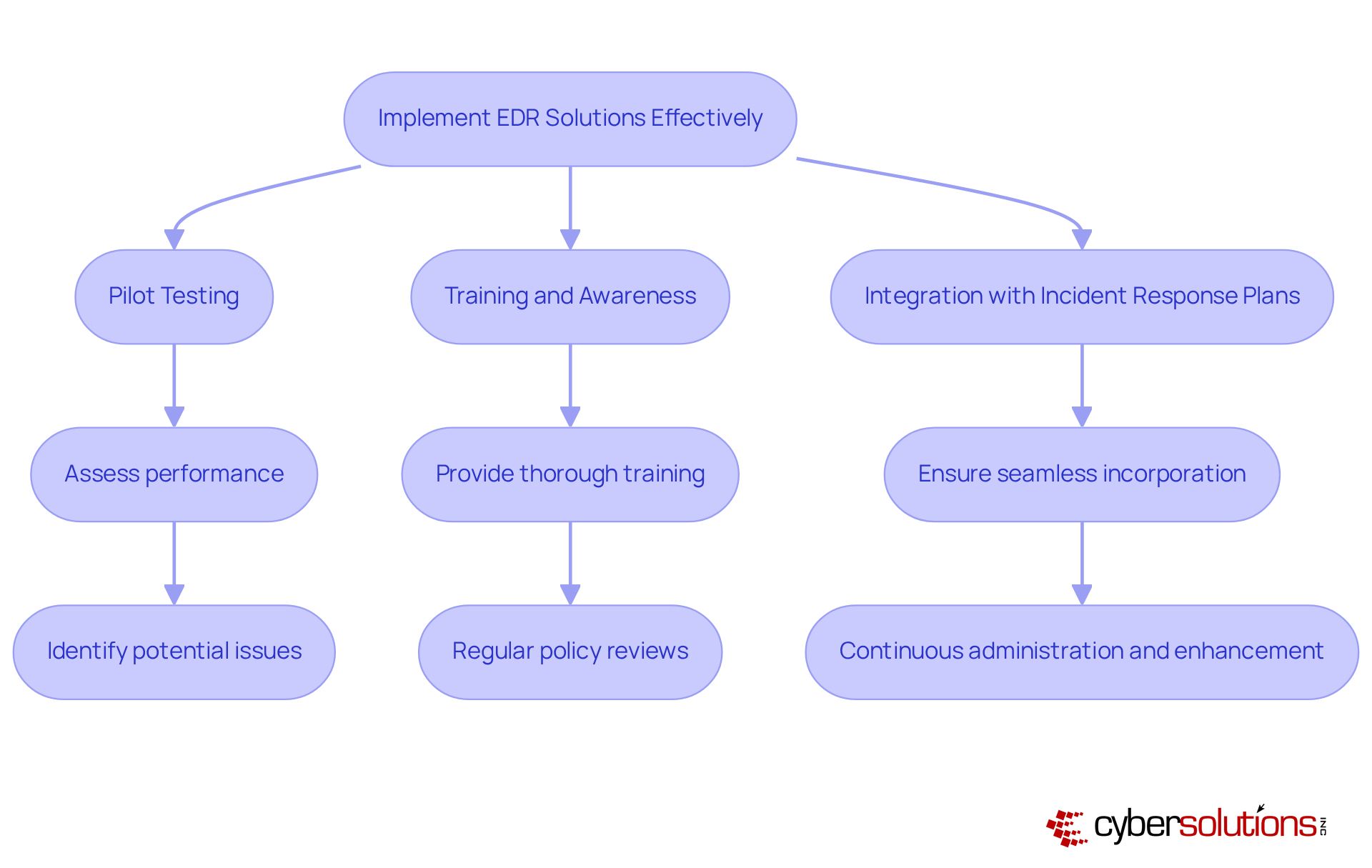
Implement EDR Solutions Effectively
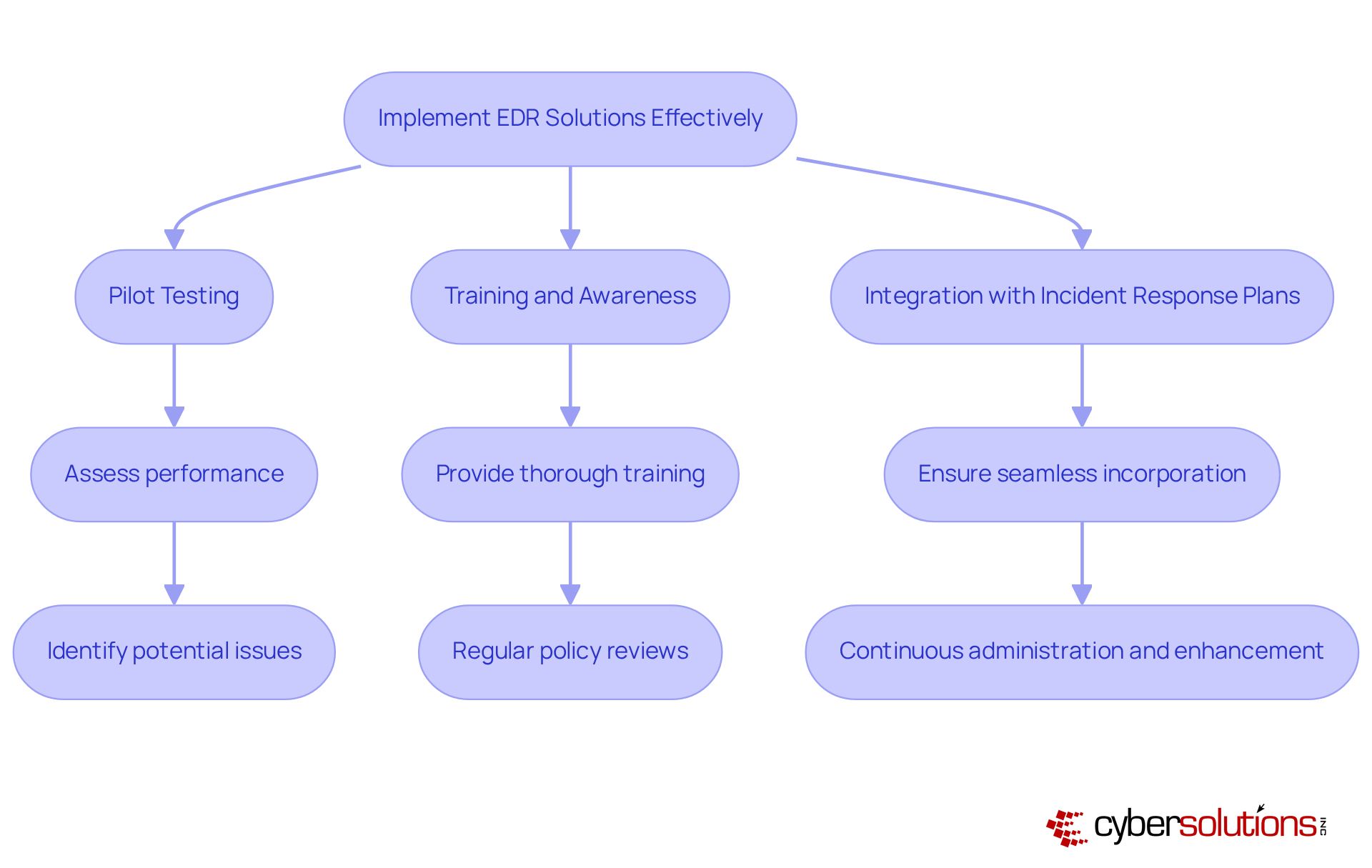
In an era where cyber threats are evolving at an unprecedented pace, the healthcare sector must prioritize robust cybersecurity measures to safeguard sensitive patient data. To implement EDR solutions effectively, organizations should adhere to the following best practices:
- Pilot Testing: Initiate a pilot deployment on a small subset of endpoints to assess the EDR solution's performance and identify potential issues before a full rollout. This phased approach allows for adjustments based on real-world feedback, ensuring smoother integration across the organization. As Nathan Hall, Principal of an EDR provider, emphasizes, 'When deploying an EDR system, ensure your initial policies are set to Detect Only mode.' Define clear objectives by establishing specific goals for the EDR provider implementation, such as reducing response times or improving detection rates. Clear objectives guide the deployment process and help measure success.
- Training and Awareness: It's essential to provide thorough training for your IT and security teams. Research indicates that effective training from an EDR provider greatly improves the performance of EDR systems, allowing teams to react to alerts more efficiently and accurately. For instance, organizations that invest in training can see a marked improvement in their incident response capabilities. Regular policy reviews should involve continuously updating the policies of the EDR provider to adapt to the changing risk landscape. Regular assessments ensure that detection rules remain effective and aligned with organizational needs. Avoiding policy exceptions during implementation is vital, as Nathan Hall notes, "One of the key pitfalls to avoid is the creation of exceptions to policies during this phase."
- Integration with Incident Response Plans: Ensure that the EDR system is seamlessly incorporated into your organization's incident response plans. This integration enables a coordinated strategy for risk management, improving overall security stance. Furthermore, continuous administration and enhancement of EDR systems by an EDR provider are crucial for sustaining efficiency against new challenges.
Neglecting these best practices could leave your organization vulnerable to attacks that compromise not just data, but patient trust and safety.
Manage and Optimize EDR Systems Continuously
In an era where cyber threats are increasingly sophisticated, the healthcare sector must prioritize cybersecurity to safeguard sensitive patient data and maintain trust. To ensure the ongoing effectiveness of EDR systems, organizations must adopt a proactive approach to management and optimization:
- Regular Performance Monitoring: Continuously assess the performance of the EDR solution by analyzing detection rates, false positives, and response times. This examination aids in recognizing areas for enhancement, guaranteeing the framework adjusts to changing challenges.
- Risk Intelligence Integration: Incorporate risk intelligence feeds to bolster the EDR system's capabilities. This integration enables the detection of the latest threats and vulnerabilities, enhancing overall security effectiveness.
- Feedback Loops: Establish mechanisms for security teams to provide feedback on the EDR solution's performance. This feedback enables prompt modifications to detection rules and response protocols, ensuring the framework stays adaptable to new challenges.
- Compliance Audits: Conduct regular audits to verify that the EDR framework adheres to relevant regulations and standards, such as GDPR and HIPAA. These audits help mitigate legal risks and ensure compliance with industry requirements.
Invest in upgrades by staying informed about updates and new features from your EDR provider. Investing in these upgrades can significantly enhance the platform's capabilities and performance, keeping pace with the rapidly changing cybersecurity landscape.
By adopting a proactive approach, organizations can not only enhance their security but also stay ahead of potential threats. Failing to optimize EDR systems could leave organizations vulnerable, jeopardizing not just their data but their reputation in the industry.
Conclusion
In an era where cyber threats are evolving at an alarming rate, the choice of an EDR provider becomes a pivotal decision for healthcare organizations. Choosing the right EDR provider is essential for safeguarding sensitive data and ensuring a robust cybersecurity posture within organizations, particularly in the healthcare sector. The effectiveness of an Endpoint Detection and Response system relies on three key factors:
- Understanding its core functionalities
- Evaluating essential selection criteria
- Implementing best practices for deployment and management
When organizations focus on these key areas, they can really boost their defenses against the ever-evolving cyber threats.
Throughout the article, critical points have been highlighted, including the importance of continuous monitoring, automated responses, and data analysis capabilities offered by EDR solutions. Additionally, the selection process should focus on:
- Detection capabilities
- Integration with existing systems
- Scalability
- User experience
- Support services
Implementing EDR solutions effectively involves:
- Pilot testing
- Comprehensive training
- Ongoing optimization to adapt to evolving threats and maintain compliance with industry standards
Choosing the wrong EDR provider can expose organizations to serious risks that could jeopardize their operations and reputation. As cyber threats continue to rise in complexity and frequency, organizations must take proactive steps to protect their data and maintain the trust of their stakeholders. By investing in a suitable EDR solution and adhering to best practices for management and optimization, organizations can fortify their cybersecurity defenses and ensure resilience in the face of emerging challenges. The right EDR solution not only protects sensitive data but also reinforces the organization's commitment to safeguarding patient trust and operational integrity.
Frequently Asked Questions
What is EDR technology?
Endpoint Detection and Response (EDR) technology is a cybersecurity solution that provides a framework for real-time risk management by continuously monitoring endpoint devices like laptops, desktops, and servers to identify, examine, and respond to potential threats.
Why is EDR important for the healthcare sector?
EDR is crucial for the healthcare sector as it helps safeguard sensitive patient data against cyber threats, which are increasingly prevalent. Effective EDR systems can significantly reduce the financial impact of breaches by enabling timely responses.
What are the key functionalities of EDR?
Key functionalities of EDR include continuous monitoring of endpoint activities, automated response to detected threats, and data collection and analysis for forensic investigations and compliance reporting.
How does continuous monitoring work in EDR systems?
EDR systems provide 24/7 surveillance of endpoint activities, enabling immediate detection of suspicious behavior. This constant vigilance is vital for organizations to contain breaches quickly, potentially saving significant financial resources.
What is the significance of automated response in EDR?
Automated response in EDR allows for the immediate isolation of affected endpoints upon detection of a risk, preventing lateral movement within the network, which is a leading cyber risk.
How does EDR contribute to data collection and analysis?
EDR tools gather extensive data on endpoint activities that can be analyzed for forensic investigations and compliance reporting. This data-driven approach aids in prompt risk response and strengthens long-term security strategies by identifying potential vulnerabilities.
What risks do healthcare organizations face without EDR?
Without the implementation of an EDR provider, healthcare organizations risk not only their financial stability due to potential breaches but also the trust of their patients and stakeholders.
List of Sources
- Understand the Fundamentals of EDR Technology
- Top Cybersecurity Trends for 2026 - The Greentree Group (https://greentreegroup.com/news/top-cybersecurity-trends-for-2026)
- The 2026 Ultimate Guide to Endpoint Detection and Response (https://techday.co.uk/tag/endpoint-detection-and-response)
- EDR Market Overview: Key Stats & Insights (https://expertinsights.com/endpoint-security/edr-market-overview)
- Endpoint Detection and Response (EDR) Market Size, Vendors & Companies (https://mordorintelligence.com/industry-reports/endpoint-detection-and-response-market)
- The Importance of Endpoint Detection & Response (EDR) Solutions - DMC Technology Group (https://dmctechgroup.com/the-importance-of-endpoint-detection-response-edr)
- Evaluate Key Selection Criteria for EDR Providers
- What to consider when evaluating EDR | Red Canary (https://redcanary.com/blog/security-operations/evaluating-edr)
- What to Expect from Leading EDR Solution Providers (https://clearnetwork.com/what-to-expect-from-leading-edr-solution-providers-in-2026)
- Endpoint Detection and Response (EDR) Buyers' Guide 2026 (https://expertinsights.com/endpoint-security/endpoint-detection-and-response-edr-buyers-guide)
- Best EDR (endpoint detection and response) solutions in 2026 (https://acronis.com/en/blog/posts/best-edr-endpoint-detection-and-response-solutions-in-2026)
- EDR Platforms: Choosing the Right One in 2026 (https://sentinelone.com/cybersecurity-101/endpoint-security/edr-platforms)
- Implement EDR Solutions Effectively
- 8 EDR Best Practices You Need to Pay Attention to in 2026 (https://heimdalsecurity.com/blog/edr-best-practices)
- Best EDR (endpoint detection and response) solutions in 2026 (https://acronis.com/en/blog/posts/best-edr-endpoint-detection-and-response-solutions-in-2026)
- What Is Endpoint Detection and Response (EDR) Deployment? (https://paloaltonetworks.com/cyberpedia/what-is-edr-deployment)
- Endpoint Detection and Response Best Practices in 2024 (https://deepwatch.com/blog/endpoint-detection-and-response-best-practices-in-2024)
- Effective EDR: Balancing testing rigor and velocity | Federal News Network (https://federalnewsnetwork.com/commentary/2024/10/effective-edr-balancing-testing-rigor-and-velocity)
- Manage and Optimize EDR Systems Continuously
- CISA flags rising threats to endpoint management systems after Stryker breach, urges stronger defense - Industrial Cyber (https://industrialcyber.co/cisa/cisa-flags-rising-threats-to-endpoint-management-systems-after-stryker-breach-urges-stronger-defense)
- EDR Benefits: Superior Handling of Large Security Incidents (https://nri-secure.com/blog/endpoint-detection-response-edr-benefits)
- (PDF) Effectiveness of Endpoint Detection and Response Solutions in Combating Modern Cyber Threats (https://researchgate.net/publication/387318838_Effectiveness_of_Endpoint_Detection_and_Response_Solutions_in_Combating_Modern_Cyber_Threats)
- Cybersecurity Trends to Consider in 2026 (https://blog.enterprisemanagement.com/cybersecurity-trends-to-consider-in-2026)
- What’s EDR? Endpoint Detection & Response | Splunk (https://splunk.com/en_us/blog/learn/endpoint-detection-response-edr.html)