
In an era where cyber threats are increasingly sophisticated, the healthcare sector must prioritize robust cybersecurity measures to protect sensitive patient data.
It’s essential for organizations to grasp the financial impact of investing in a new firewall to effectively shield their networks from unauthorized access and data breaches.
With costs varying widely based on the type and complexity of the firewall, organizations struggle to find the right balance between investing in cybersecurity and managing their budgets effectively.
What costs should organizations prepare for when investing in this vital security tool, and how can they plan strategically to ensure comprehensive cybersecurity?
Strategic financial planning for cybersecurity investments is not just a necessity; it’s a critical step in safeguarding the future of healthcare organizations.
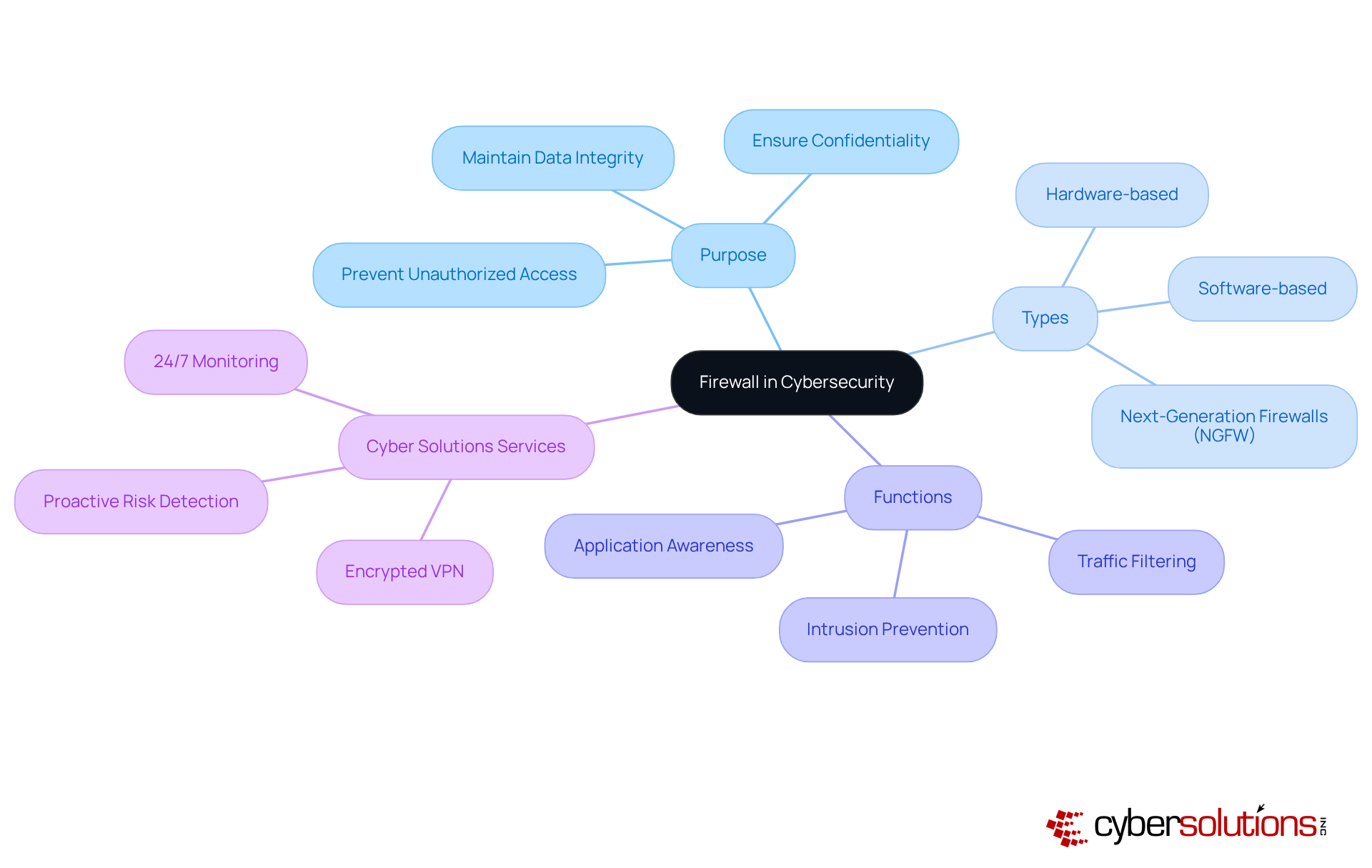
In an era where healthcare data breaches are on the rise, the importance of robust cybersecurity measures cannot be overstated. A network security device is essential for monitoring and managing incoming and outgoing network traffic according to established security protocols. Acting as a barrier between a trusted internal network and untrusted external networks, such as the internet, firewalls - whether hardware-based, software-based, or a combination of both - serve to prevent unauthorized access, data breaches, and various cyber threats. By filtering traffic, security systems help organizations maintain data integrity and confidentiality, making them essential to any cybersecurity strategy.
At Cyber Solutions, we provide robust security services that act as a formidable barrier against unauthorized access and malware, ensuring your network remains secure and efficient. Our 24/7 monitoring detects anomalies and potential vulnerabilities, while our encrypted VPN services offer secure remote access solutions. The advancement of security barriers has led to the development of sophisticated next-generation security systems (NGFW), which include additional functionalities like intrusion prevention systems (IPS) and application awareness. Through proactive monitoring and advanced risk detection, we ensure that your security system adapts to evolving threats, protecting your business from ransomware, phishing, and other malware attacks. Investing in advanced cybersecurity solutions is not just a precaution; it's a necessity for safeguarding your organization’s future against evolving threats.
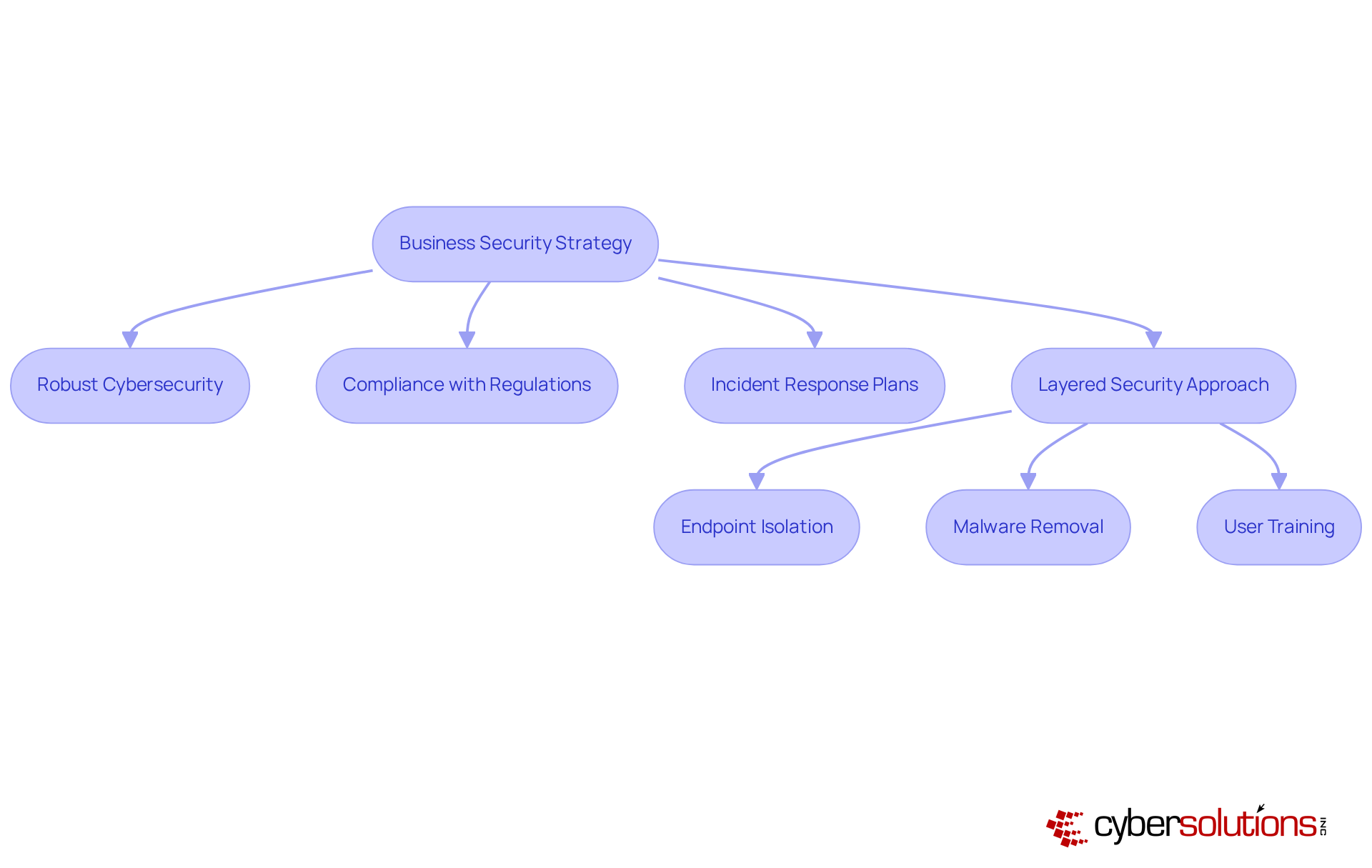
In an era where cyber threats are increasingly sophisticated, the need for robust cybersecurity in healthcare has never been more critical. Security systems serve as the first line of defense against these threats, protecting sensitive information from unauthorized access and potential breaches. As organizations rely more on digital infrastructure, the need for effective security barriers is clearer than ever. These protective tools not only safeguard data but also help ensure compliance with regulatory requirements such as HIPAA, PCI-DSS, and GDPR. By implementing effective security solutions, companies can mitigate risks, enhance their security posture, and maintain customer trust.
Security barriers play a crucial role in incident response plans. They enable organizations to swiftly identify and address potential risks. Cyber Solutions exemplifies this with its 24-hour on-site response capability, allowing for rapid containment of threats and minimizing damage through a layered approach that includes:
Research indicates that organizations with comprehensive security systems experience up to 50% fewer data breaches, underscoring their vital role in protecting customer records and financial data. Organizations that have effectively established security measures to adhere to regulations have shown improved operational integrity and decreased risk of regulatory penalties.
In a time when cyber threats are becoming more advanced, investing in security systems is a strategic decision that not only safeguards sensitive information but also enhances long-term business resilience. Without these investments, organizations risk not only data breaches but also significant financial and reputational damage. Ongoing surveillance and software enhancements are crucial for sustaining the effectiveness of network protection systems. Combining these systems with other security measures, such as endpoint controls and identity verification, is necessary for a layered security strategy that Cyber Solutions promotes.
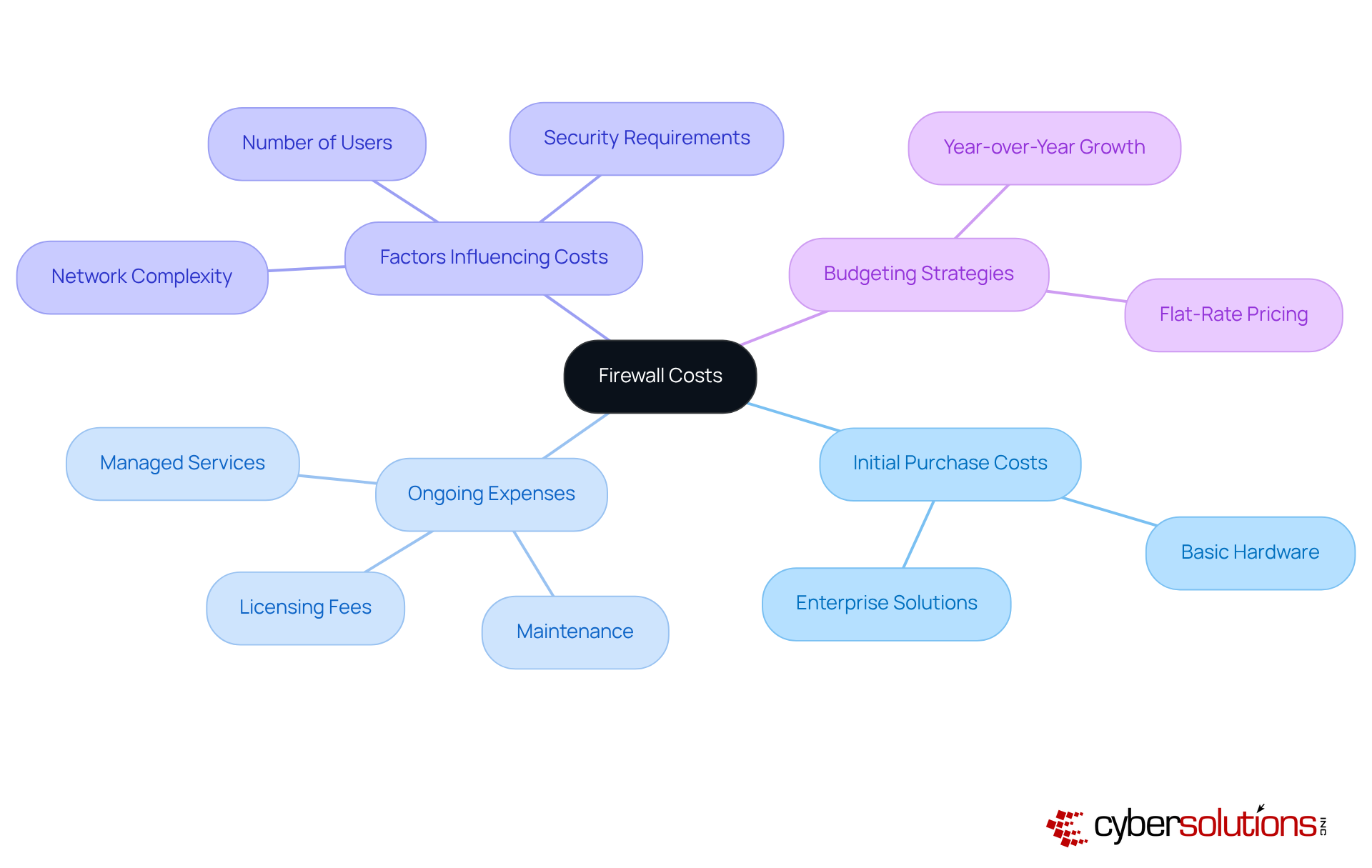
In an era where cyber threats loom larger than ever, the healthcare sector faces unprecedented challenges in safeguarding sensitive data. When considering the expense of obtaining a network security system, one might ask what kind of expense is the purchase of a new firewall device, as it can fluctuate significantly based on essential elements such as the type of system, its features, and the organization's size. Basic hardware security systems typically start around $200, while enterprise-grade solutions can exceed $100,000. Ongoing expenses, including licensing fees, maintenance, and support services, significantly contribute to the total cost. For instance, managed firewall services generally range from $150 to $300 per month, covering software updates and technical support.
Understanding these factors is vital for organizations to determine what kind of expense is the purchase of a new firewall device in order to create a solid budget for their cybersecurity needs. Key elements influencing these costs include:
As organizations manage these expenses, they must also consider the long-term effects of security system maintenance and support. Ignoring these long-term costs can lead to unexpected financial burdens that jeopardize cybersecurity efforts.
Furthermore, budgeting for protective measures should account for the anticipated increase in cybersecurity expenditure, with vendors projecting a year-over-year growth of 25% to 30% for 2026. Adopting a flat-rate pricing model for managed IT and cybersecurity services, such as those offered by Cyber Solutions, can simplify budgeting and enhance operational efficiency. This approach ensures predictable monthly costs for businesses and underscores the importance of strategic financial planning in the face of evolving cybersecurity demands. Without a proactive approach to budgeting for cybersecurity, organizations risk not only financial strain but also the integrity of their operations and patient trust.
In an era where cyber threats are increasingly sophisticated, the right firewall is not just an option; it's a necessity for healthcare organizations to safeguard sensitive patient data. Firewalls can be categorized into several types, each offering distinct features and cost structures that reflect their capabilities and intended use cases.
When considering the right firewall, one must ask what kind of expense is the purchase of a new firewall device, as this decision goes beyond technical aspects and is crucial for the future security and integrity of your organization.

In an era where cyber threats are evolving at an alarming rate, understanding firewall costs is not just important; it's essential for safeguarding sensitive data. Firewalls are not optional tools; they are critical components in protecting sensitive information against increasingly sophisticated cyber threats. Investing in the right firewall solutions allows businesses to build a strong defense. This not only protects their information but also boosts their overall security posture.
Key factors influencing the cost of firewalls include:
From basic packet-filtering solutions to advanced next-generation firewalls, the pricing spectrum reflects varying levels of protection and functionality. Additionally, ongoing expenses such as licensing, maintenance, and support must be factored into the overall budget to ensure long-term cybersecurity effectiveness.
Given the rising cyber risks, organizations need to prioritize their cybersecurity investments and take a proactive budgeting approach. By understanding the intricacies of firewall costs and implementing a layered security strategy, businesses can protect their sensitive information while maintaining compliance with regulatory standards and building trust with their clients. Ultimately, the decision to invest in robust firewall solutions could mean the difference between security and vulnerability in a digital-first world.
What is the role of a firewall in cybersecurity?
A firewall acts as a barrier between a trusted internal network and untrusted external networks, such as the internet. It monitors and manages incoming and outgoing network traffic according to established security protocols to prevent unauthorized access, data breaches, and various cyber threats.
What types of firewalls are there?
Firewalls can be hardware-based, software-based, or a combination of both.
Why are firewalls important for organizations?
Firewalls are essential for maintaining data integrity and confidentiality by filtering traffic, which helps organizations protect against unauthorized access and cyber threats.
What additional services does Cyber Solutions provide related to firewalls?
Cyber Solutions offers robust security services, including 24/7 monitoring for anomalies and potential vulnerabilities, as well as encrypted VPN services for secure remote access.
What are next-generation firewalls (NGFW)?
Next-generation firewalls (NGFW) are advanced security systems that include additional functionalities like intrusion prevention systems (IPS) and application awareness to enhance protection against evolving threats.
How does Cyber Solutions ensure its security systems adapt to threats?
Through proactive monitoring and advanced risk detection, Cyber Solutions ensures that security systems adapt to evolving threats, protecting businesses from ransomware, phishing, and other malware attacks.
Why is investing in advanced cybersecurity solutions important?
Investing in advanced cybersecurity solutions is necessary for safeguarding an organization’s future against evolving threats, as it provides a robust defense against potential cyber attacks.