
In an era where data breaches are increasingly prevalent, the role of CFOs in safeguarding sensitive information has reached a critical juncture. The emergence of OAuth, an authorization framework designed to bolster data security without compromising user credentials, presents CFOs with a unique opportunity to strengthen their organizations against unauthorized access. Yet, as cyber threats continue to evolve, a pressing question arises: how can CFOs effectively manage and restrict access to ensure compliance while protecting financial data? This article explores best practices for implementing OAuth management, providing insights that empower CFOs to navigate the complexities of cybersecurity with confidence.
In today's digital landscape, cybersecurity is paramount, particularly in the healthcare sector. OAuth, or Open Authorization, serves as a vital authorization framework that empowers programs to access user information without the need for password sharing. This capability is especially critical for CFOs, who bear the responsibility of safeguarding against unauthorized access.
By implementing OAuth, organizations can enhance security by:
Furthermore, OAuth supports secure communication, providing a secure method for external applications to interact with sensitive information without exposing user credentials. For CFOs, grasping the intricacies of OAuth, including its benefits, is essential for making informed decisions regarding their organization's security strategy.

In the current landscape of cybersecurity threats, it is imperative for CFOs to take decisive action to enforce OAuth app access limitations. A comprehensive assessment of all programs that currently possess access to sensitive data is the first step. This involves examining access to external programs and to those that may pose a risk. Once this inventory is complete, organizations can establish a robust policy for approving new requests, based on criteria such as security certifications and adherence to industry standards, including request allowlisting.
Implementing access restrictions is not just a best practice; it is crucial for proactively preventing unauthorized or malicious applications from executing. This approach significantly reduces the attack surface and minimizes vulnerabilities, while also ensuring data protection. Moreover, employing tools that facilitate real-time observation of OAuth app activity is essential for identifying unauthorized intrusion attempts. Consistently refreshing permissions and eliminating access for unused programs are vital strategies for maintaining a secure environment.
By implementing these measures, including software allowlisting with features such as centralized management, CFOs can substantially decrease the risk of data breaches. This ensures that only approved programs have access to sensitive information, thereby safeguarding the organization's data integrity and fostering trust among stakeholders. The time to act is now—to navigate the complexities of cybersecurity effectively.

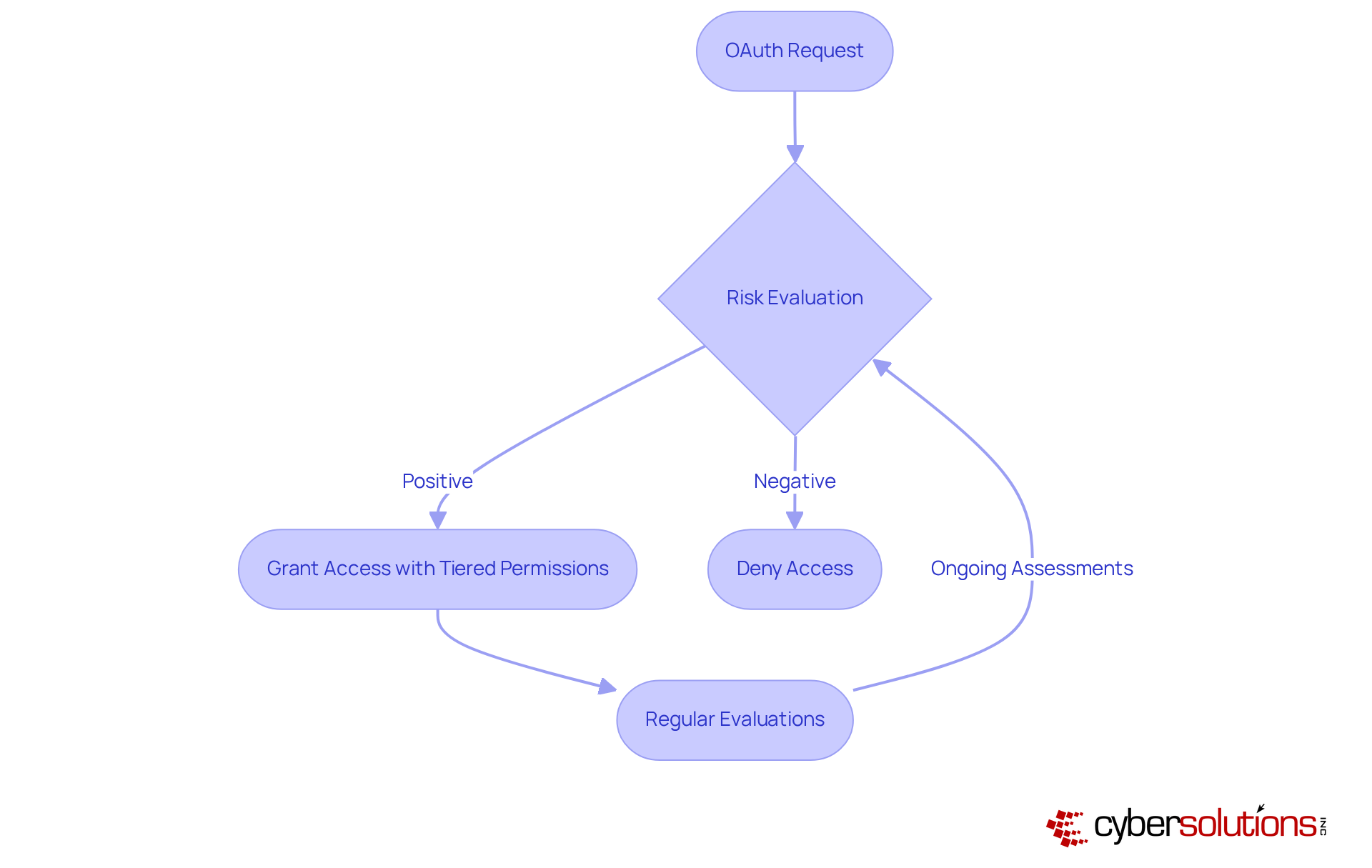
In today's landscape, security is paramount, especially for CFOs tasked with risk management. Establishing a transparent procedure for approving and rejecting OAuth requests is essential for data protection, ensuring that only secure and compliant requests gain entry. This process must involve a thorough evaluation, assessing the software's security features, data handling practices, and adherence to relevant regulations. For instance, programs lacking security measures or failing to follow the principle of least privilege should be denied entry.
Moreover, adopting a risk-based approach can enhance security by granting software varying degrees of access based on their risk profile. Regular evaluations of authorized requests are crucial for restricting access to those that may no longer meet security criteria, thereby allowing for timely cancellation of permissions. By enforcing stringent oversight over which programs can access confidential information, CFOs not only protect their organizations but also significantly bolster their security posture. The proactive measures taken today will pave the way for a more secure future in data management.
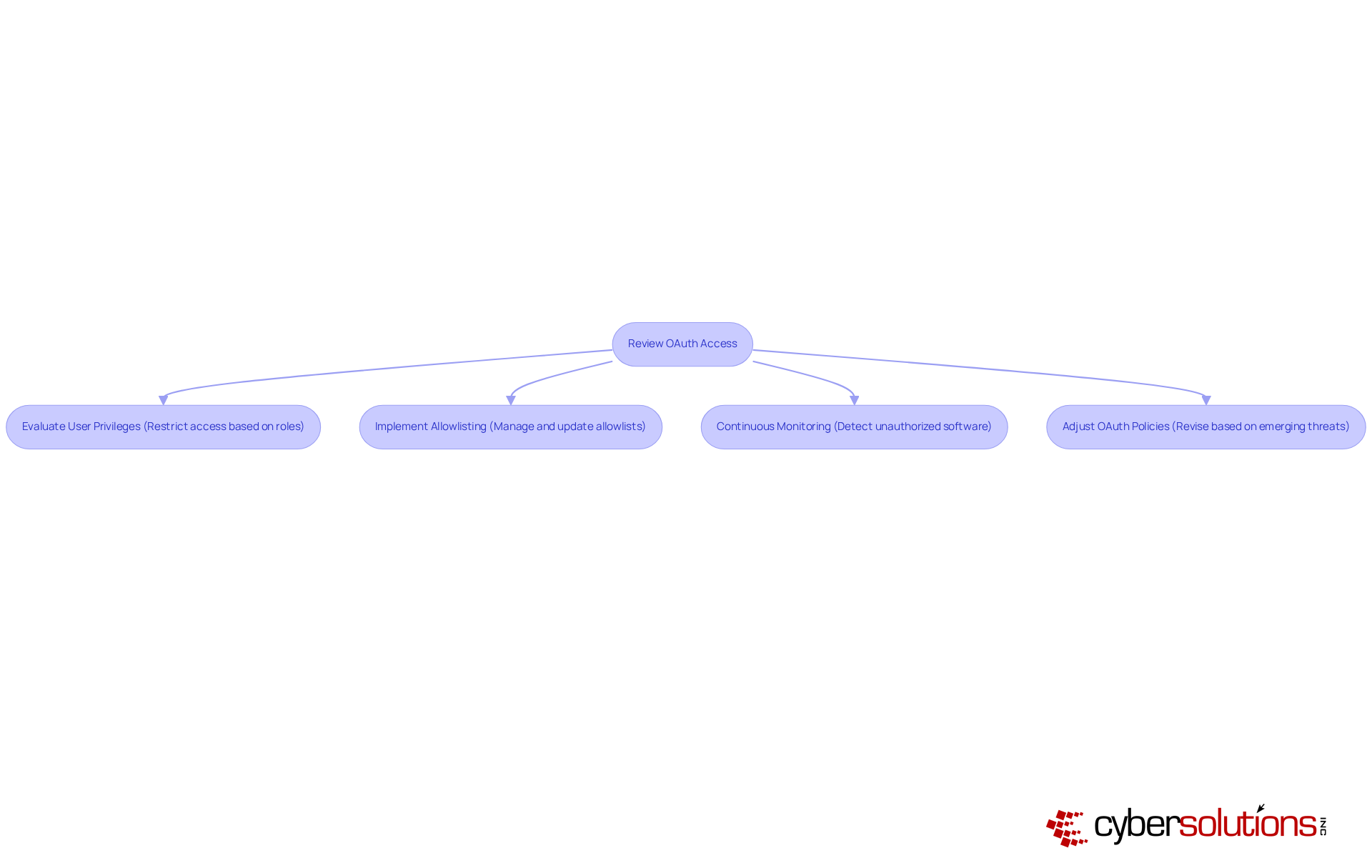
In today's rapidly evolving digital landscape, maintaining a robust security framework is essential. Establishing a routine evaluation procedure for OAuth permissions is essential, integrating program allowlisting as a critical component of this strategy. This process necessitates periodic reviews of all systems, with a focus on application security, evaluating their current security status, and confirming their alignment with the organization's security requirements.
Permit allowlisting serves as a safeguard to thwart unauthorized or malicious software from executing, significantly reducing the risk of malware and ensuring system integrity. Key features of application allowlisting include:
During these assessments, it is crucial for organizations to review access permissions, which includes restricting access to ensure that permissions align with current roles and responsibilities. Any software that is no longer in use or poses a security risk should have its permissions revoked without delay. Furthermore, organizations must stay vigilant regarding emerging threats and adjust their OAuth policies accordingly. By conducting regular reviews and implementing necessary changes, including the management of application allowlists, CFOs can effectively mitigate risks and safeguard their organization's data.
Implementing OAuth effectively is essential for CFOs who seek to safeguard sensitive financial data in today's digital landscape. Understanding and utilizing OAuth allows organizations to restrict access to authorized applications, thereby enhancing security and ensuring compliance with regulations such as GDPR and HIPAA. This framework not only protects user credentials but also empowers CFOs to make informed decisions that strengthen their organization’s cybersecurity strategy.
Key practices, including:
have been emphasized throughout the article. Regular reviews of OAuth access and permissions are vital to guarantee that only compliant and secure applications retain access to sensitive data. Collectively, these measures contribute to a robust security posture that mitigates the risk of data breaches.
The proactive strategies outlined serve as a clarion call for CFOs to prioritize OAuth management as a cornerstone of their cybersecurity framework. As threats continue to evolve, maintaining vigilance and adapting OAuth policies will be crucial in protecting organizational data. By embracing these best practices, CFOs not only shield their organizations but also cultivate trust among stakeholders, ensuring a secure future in the realm of data security.
What is OAuth and why is it important for data security?
OAuth, or Open Authorization, is an authorization framework that allows programs to access user information without requiring password sharing, enhancing security, particularly in sensitive sectors like healthcare.
How does OAuth enhance security for organizations?
OAuth enhances security by restricting access to pre-approved programs and significantly mitigating the risk of data breaches.
How does OAuth support regulatory compliance?
OAuth supports compliance with regulations such as GDPR and HIPAA by enabling secure interactions between external applications and sensitive information without exposing user credentials.
Why is it essential for CFOs to understand OAuth?
It is essential for CFOs to understand OAuth because they are responsible for safeguarding sensitive financial data and making informed decisions regarding their organization's cybersecurity strategy, including the use of OAuth's token-based methodology.