Introduction
In an era where cyber threats are escalating at an alarming rate, the healthcare sector stands at a critical crossroads regarding its cybersecurity measures. This guide is designed to help leaders navigate the complexities of mastering the FTC MFA requirements, ensuring organizations protect sensitive data while staying compliant with evolving regulations. As cyber threats become more sophisticated, organizations face increasing pressure to adapt their security measures swiftly. The challenge lies not just in compliance, but in ensuring that security measures are seamlessly integrated into daily operations without burdening staff.
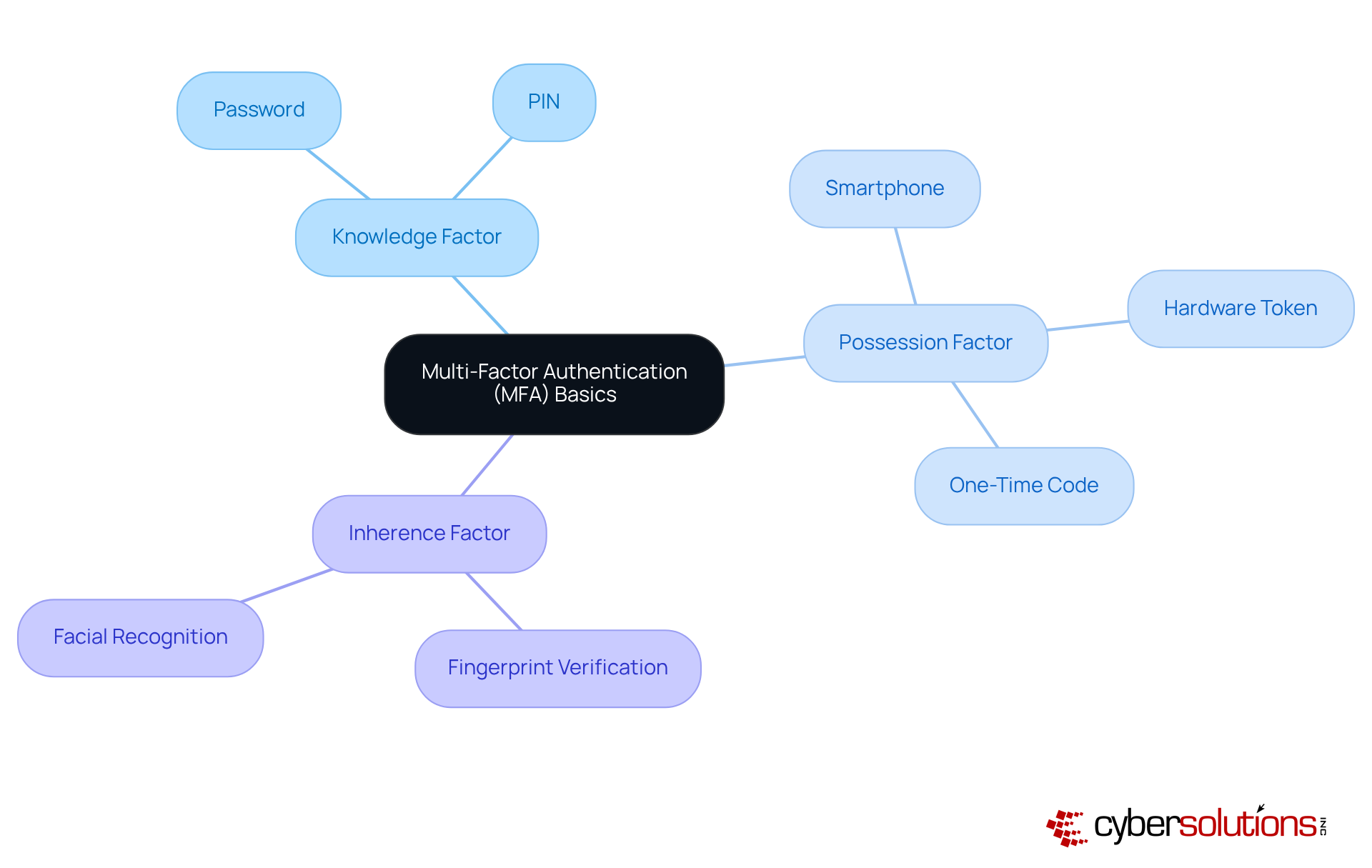
Understand Multi-Factor Authentication (MFA) Basics
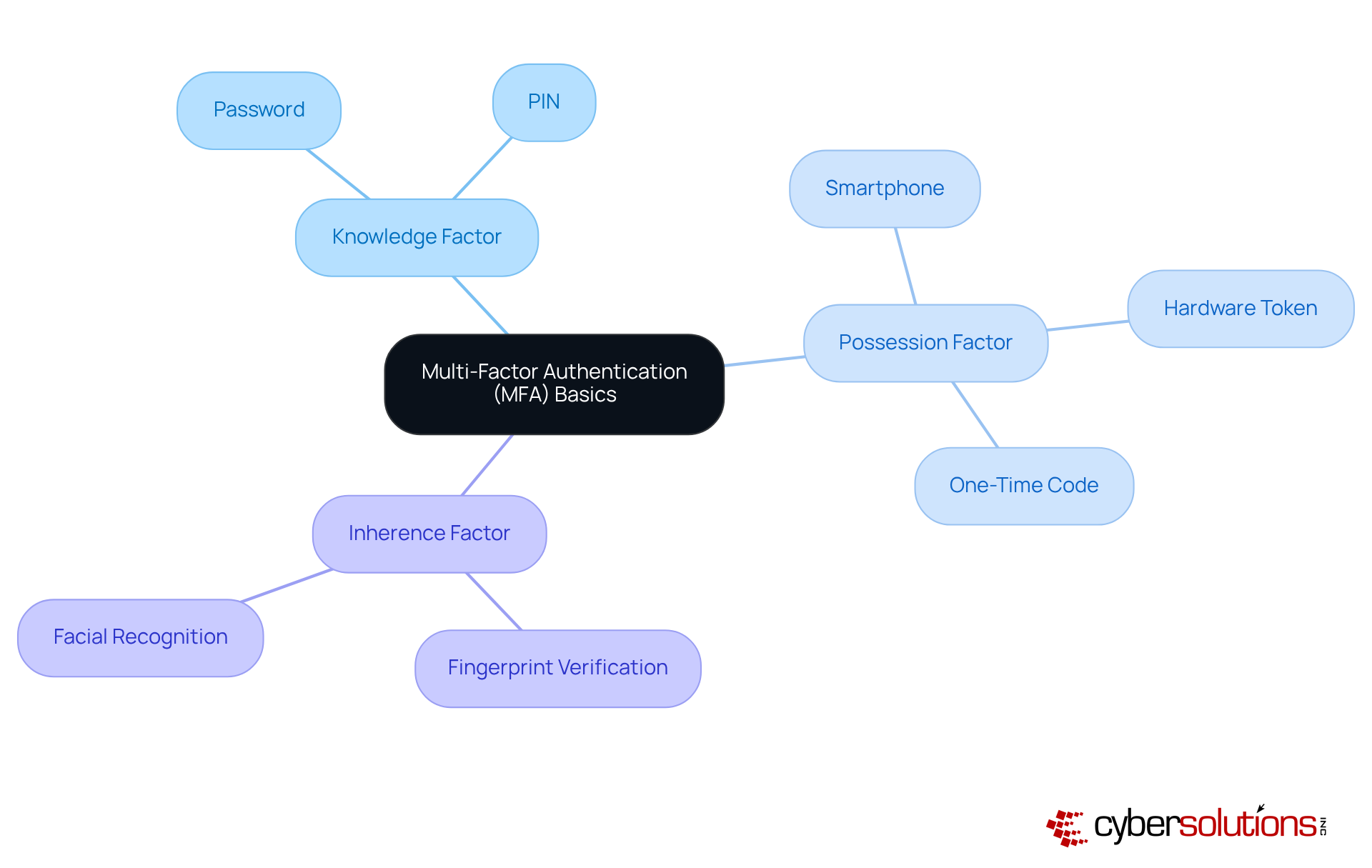
In an era where cyber attacks occur every 39 seconds, the importance of Multi-Factor Authentication (MFA) in safeguarding healthcare resources cannot be overstated. MFA is a vital protective mechanism that requires users to present two or more verification factors to access resources, such as applications or online accounts. Its main aim is to enhance safety by adding extra layers of protection beyond a simple username and password.
Key Components of MFA:
- Knowledge Factor: This includes something the user knows, such as a password or PIN.
- Possession Factor: This refers to something the user has, like a smartphone or a hardware token that generates a one-time code.
- Inherence Factor: This encompasses something the user is, which involves biometric verification methods like fingerprints or facial recognition.
Implementing these components is crucial for creating effective MFA solutions that fulfill the FTC MFA requirements, which require businesses to safeguard customer information systems against unauthorized access.
Failing to invest in robust cybersecurity measures can result in financial losses that far exceed the initial investment in protection. With cyber attacks happening every 39 seconds, companies are increasingly acknowledging the necessity for strong protective measures. For example, the technology industry is at the forefront of MFA adoption, with 87% of organizations applying these protective protocols. This trend reflects a broader understanding of the necessity for layered defenses in protecting sensitive data.
Expert insights highlight that neglecting cybersecurity can lead to costs far exceeding the investment required for securing digital assets. Liviu Arsene, a Senior E-Threat Analyst, emphasizes that the evolving landscape of cyber threats demands our constant vigilance and proactive strategies. MFA acts as a fundamental component in this approach, greatly improving protection by decreasing the risk of unauthorized access and data breaches.
Statistics further illustrate the impact of MFA on data breach prevention. Organizations that have adopted MFA report a marked decrease in successful breaches, with studies indicating that MFA can significantly reduce the risk of unauthorized access. As the MFA market is projected to reach USD 49.7 billion by 2032, prioritizing these protective measures is not just advisable; it's imperative for the future of cybersecurity in healthcare.
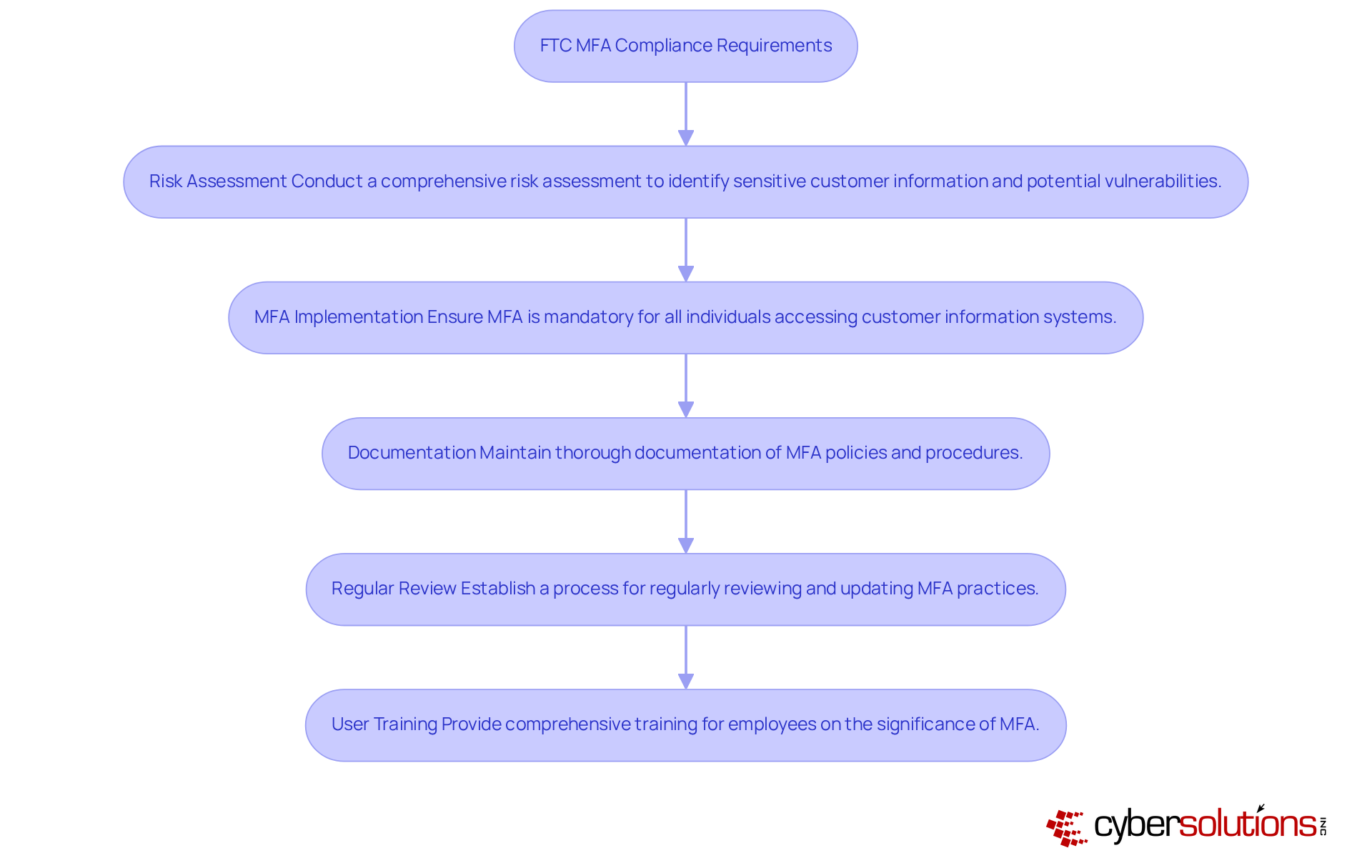
Identify FTC MFA Compliance Requirements
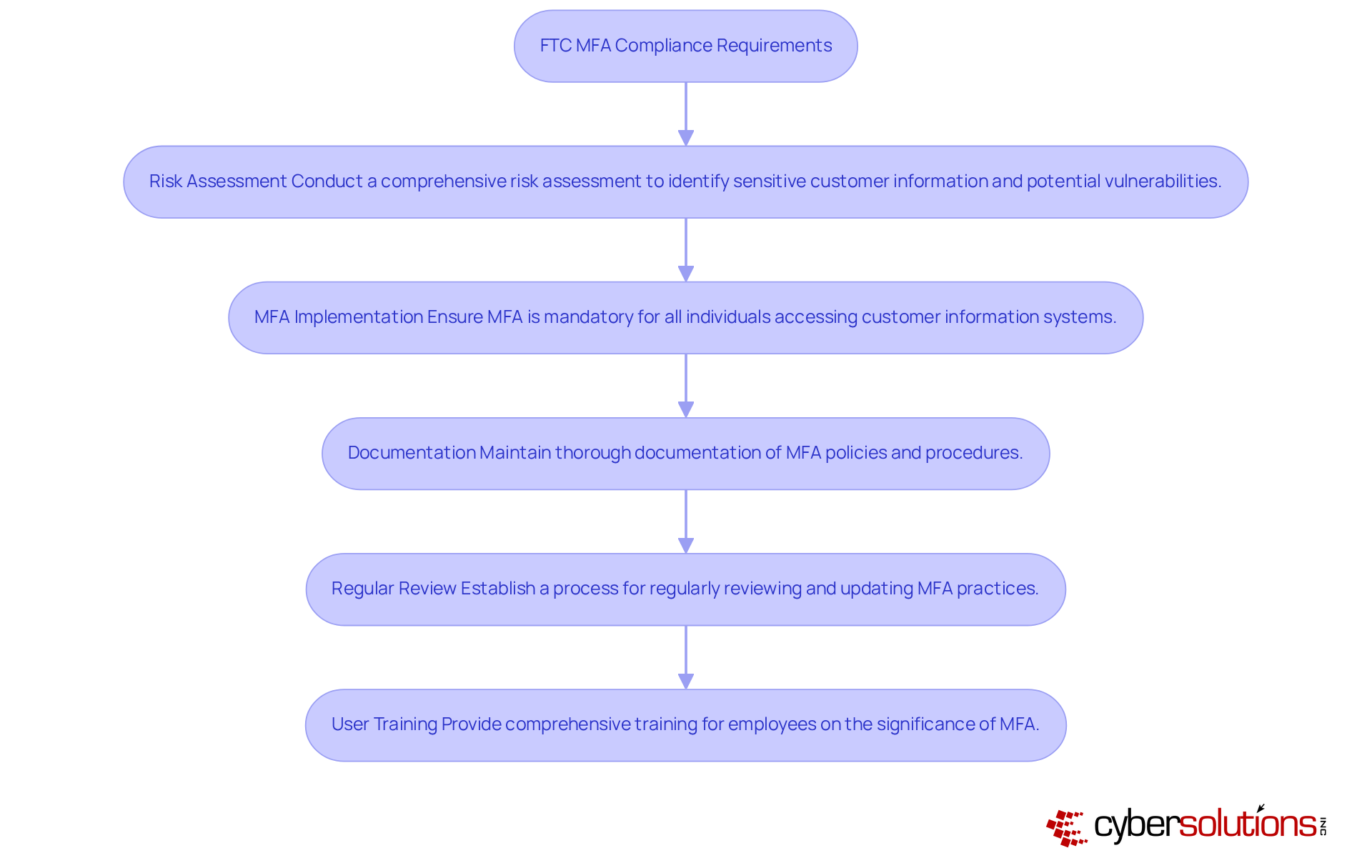
In an era where healthcare data breaches are increasingly common, the importance of robust cybersecurity measures cannot be overstated. To comply with the FTC's MFA requirements, organizations must implement the following key practices:
- Risk Assessment: Conduct a comprehensive risk assessment to identify sensitive customer information and potential vulnerabilities. Regular evaluations are essential, as they allow organizations to proactively tackle vulnerabilities.
- MFA Implementation: Ensure that multi-factor authentication (MFA) is mandatory for all individuals accessing customer information systems, including employees, contractors, and third-party vendors. This is essential, as MFA serves as a critical barrier against unauthorized access.
- Documentation: Maintain thorough documentation of MFA policies and procedures, including risk assessments and incident response plans. This documentation is crucial for demonstrating compliance and making sure that everyone understands the protective measures in place.
- Regular Review: Establish a systematic process for regularly reviewing and updating MFA practices to adapt to evolving threats and compliance standards. Ongoing observation and evaluation of MFA effectiveness are advised to guarantee that protective measures remain strong against emerging attack techniques.
- User Training: Provide comprehensive training for employees on the significance of MFA and effective usage. Making certain that employees comprehend the protective measures in place is vital, as human mistakes continue to be a major factor in data breaches.
By following these guidelines, entities can greatly minimize the risk of data breaches and improve their overall safety stance, aligning with the FTC MFA requirements and safeguarding sensitive customer information. Furthermore, utilizing Compliance as a Service (CaaS) can offer SMBs budget-friendly access to regulatory expertise, streamlining the process and guaranteeing continuous adherence to legal requirements. By prioritizing these practices, organizations not only protect sensitive information but also fortify their reputation and trust with customers.
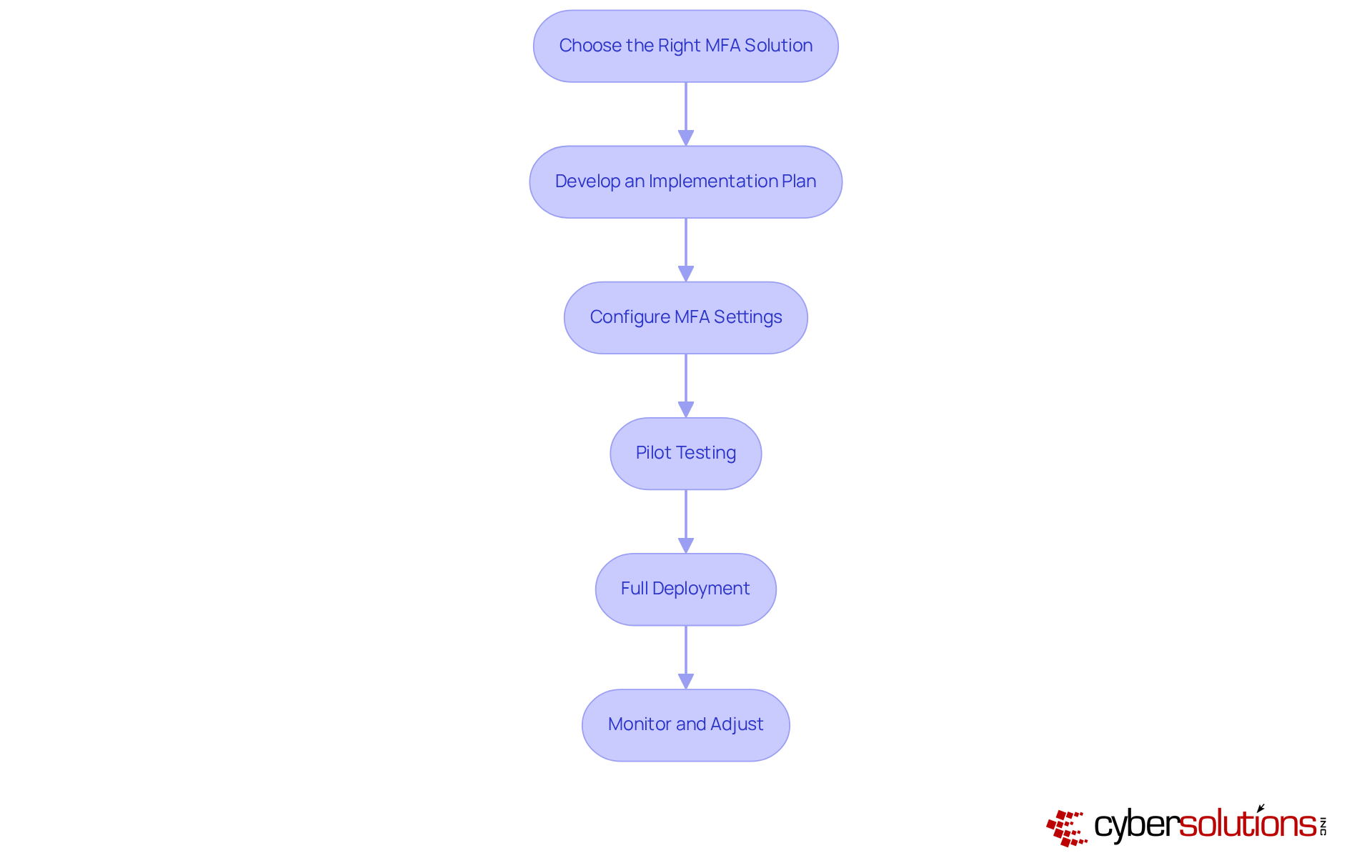
Implement MFA Solutions in Your Business
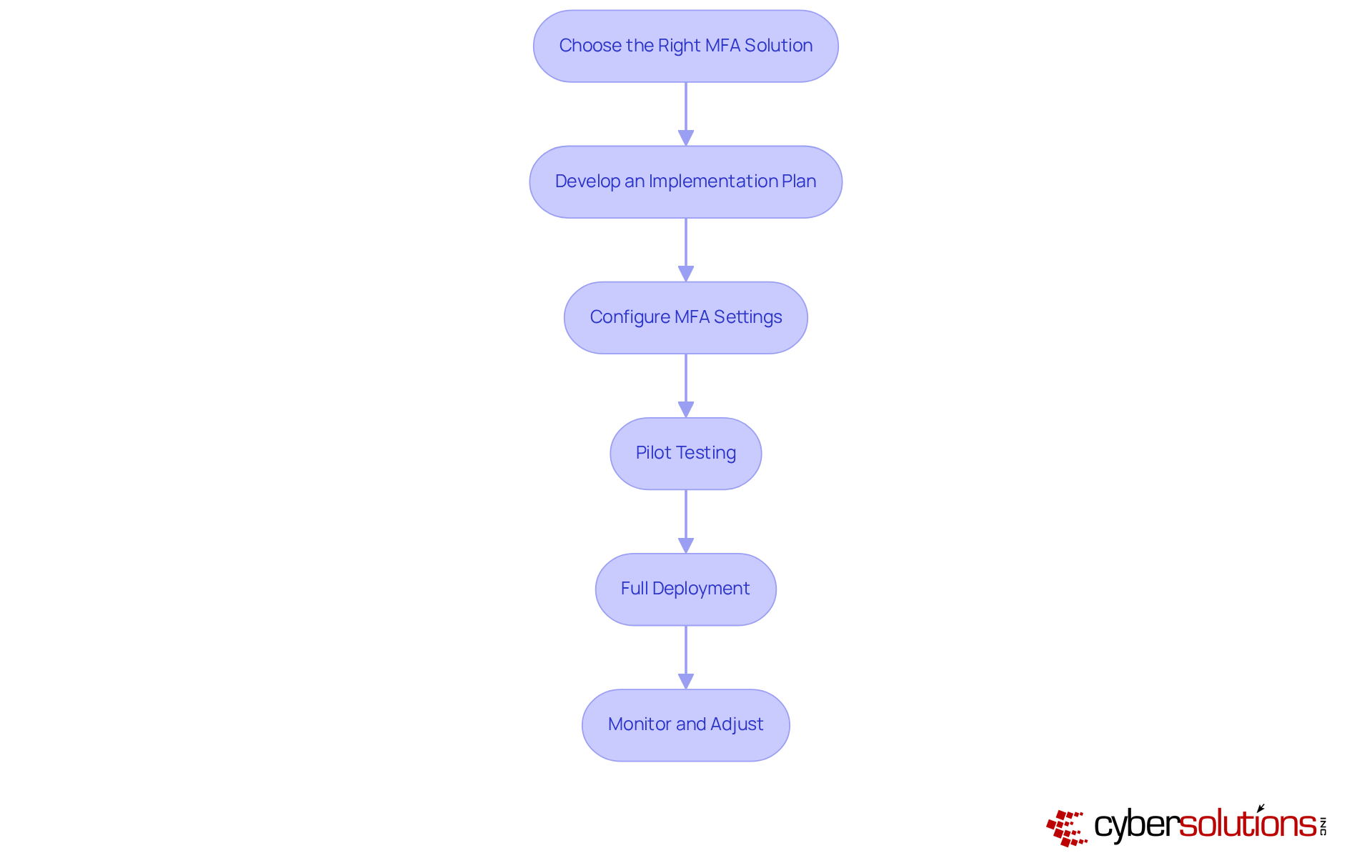
In an era where cyber threats loom large, the implementation of Multi-Factor Authentication (MFA) is not just a recommendation; it's a necessity for healthcare organizations to safeguard sensitive data. Implementing MFA in your enterprise requires a strategic approach to enhance protection and compliance. Here are the essential steps:
- Choose the Right MFA Solution: Assess various MFA solutions tailored to your organization's specific needs. Consider factors such as user-friendliness, integration capabilities with existing systems, and overall cost. Leading options include Google Authenticator, Microsoft Authenticator, and hardware tokens, each offering unique benefits. Using an authenticator app with number matching is a smart move for MFA; it helps cut down on those pesky accidental approvals during login.
- Develop an Implementation Plan: Formulate a comprehensive plan detailing the deployment process. This should include timelines, assigned responsibilities, and effective communication strategies to ensure all stakeholders are informed and engaged.
- Configure MFA Settings: Implement the selected MFA solution following industry best practices. Ensure that all users are required to verify their identity using multiple factors, thereby significantly improving protection. By 2026, enforcing MFA across all accounts will be crucial to fortifying defenses against account compromise attacks.
- Pilot Testing: Initiate a pilot test with a select group of users to identify potential issues and gather valuable feedback. This step is crucial for refining the implementation before a broader rollout.
- Full Deployment: Execute the full deployment of MFA across the company. Ensure that all employees and relevant third parties are enrolled and adequately trained on the new authentication system to facilitate a smooth transition.
- Monitor and Adjust: Continuously evaluate the effectiveness of the MFA implementation. Be prepared to make necessary adjustments to improve both user experience and security measures, ensuring that the system remains robust against evolving threats. Organizations must eliminate SMS and email MFA as default options, given their susceptibility to attacks.
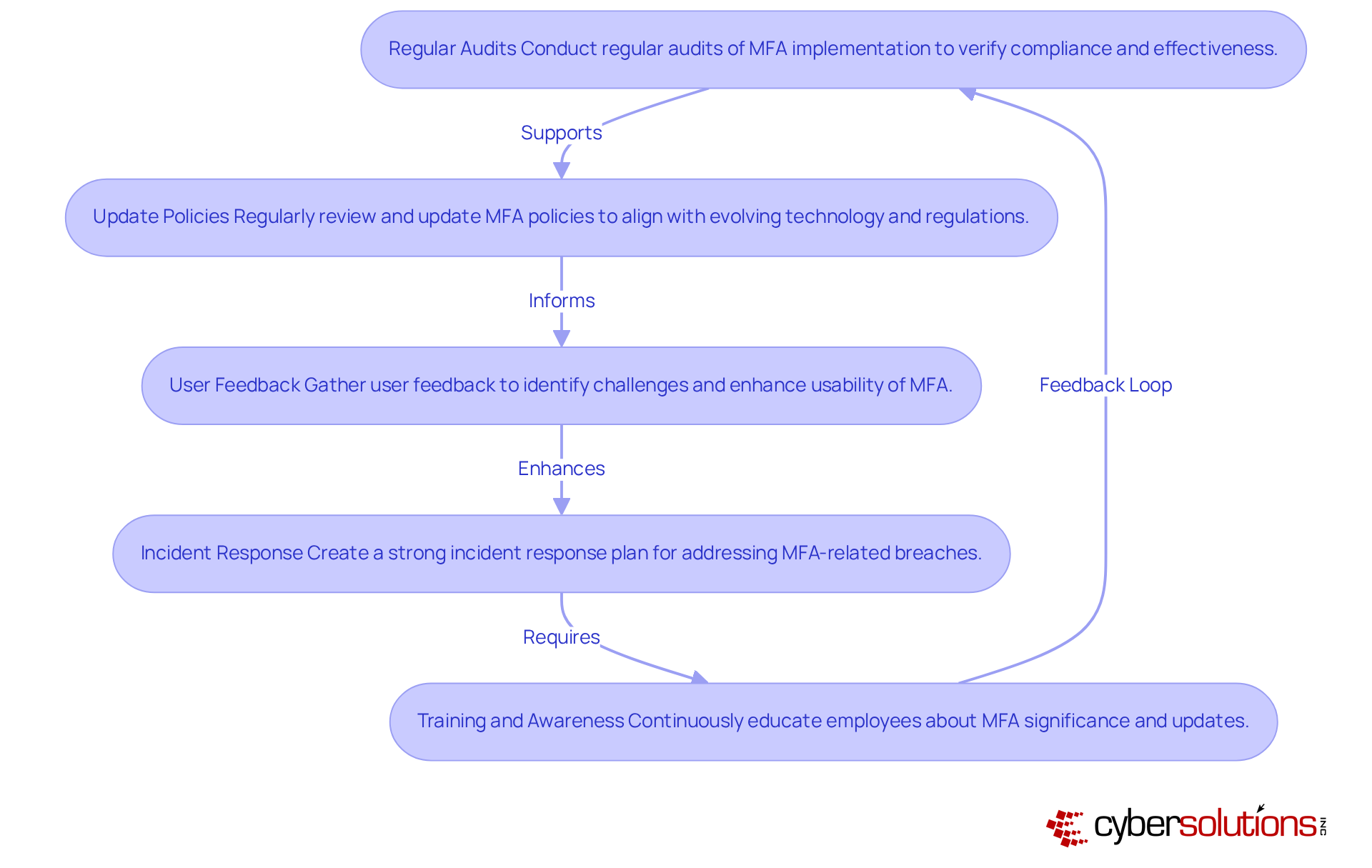
Maintain and Monitor MFA Compliance
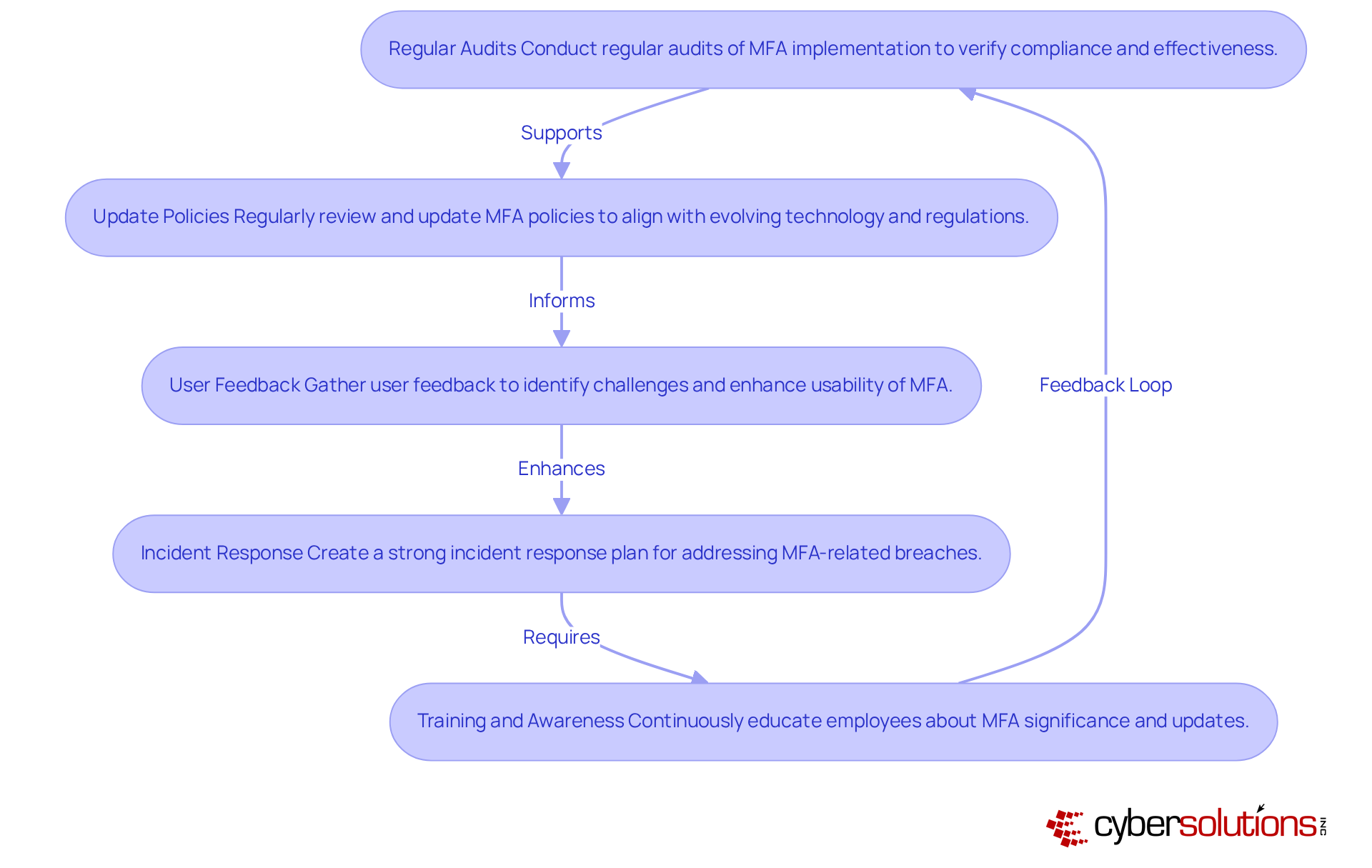
In an era where cyber threats loom larger than ever, the healthcare sector must prioritize robust cybersecurity measures to protect sensitive patient data. To ensure ongoing compliance with MFA requirements, organizations should adopt the following strategies:
- Regular Audits: Conduct regular audits of your MFA implementation to verify user compliance and ensure the system operates effectively. This proactive method aids in spotting gaps and strengthens protective measures.
- Update Policies: Are your MFA policies keeping pace with the rapid changes in technology? Regularly reviewing and updating MFA policies to align with evolving business processes and the FTC MFA requirements is vital. Last year, 61% of organizations reported cloud-related incidents, emphasizing the need for adaptive protective measures.
- User Feedback: Actively gather feedback from users to pinpoint challenges they encounter with MFA. Adjustments based on this feedback can enhance usability and encourage broader adoption, as 33% of respondents find MFA annoying, which can hinder compliance efforts.
- Incident Response: Create and uphold a strong incident response plan that incorporates specific procedures for addressing MFA-related breaches. Leveraging Cyber Solutions' Incident Response services can help reduce the impact of any breaches, ensuring rapid identification, containment, and mitigation of threats.
- Training and Awareness: Continuously educate employees about the significance of MFA and any updates to the system or policies. Nurturing a culture of awareness regarding safety is crucial, particularly as 68% of breaches include a non-malicious human factor, such as social engineering or mistakes. Furthermore, leveraging Cyber Solutions' Compliance as a Service (CaaS), which encompasses risk assessments and policy creation, can enhance your regulatory efforts, offering continuous monitoring and assistance to fulfill standards.
Failing to implement these strategies could leave your organization vulnerable, jeopardizing both patient trust and regulatory compliance.
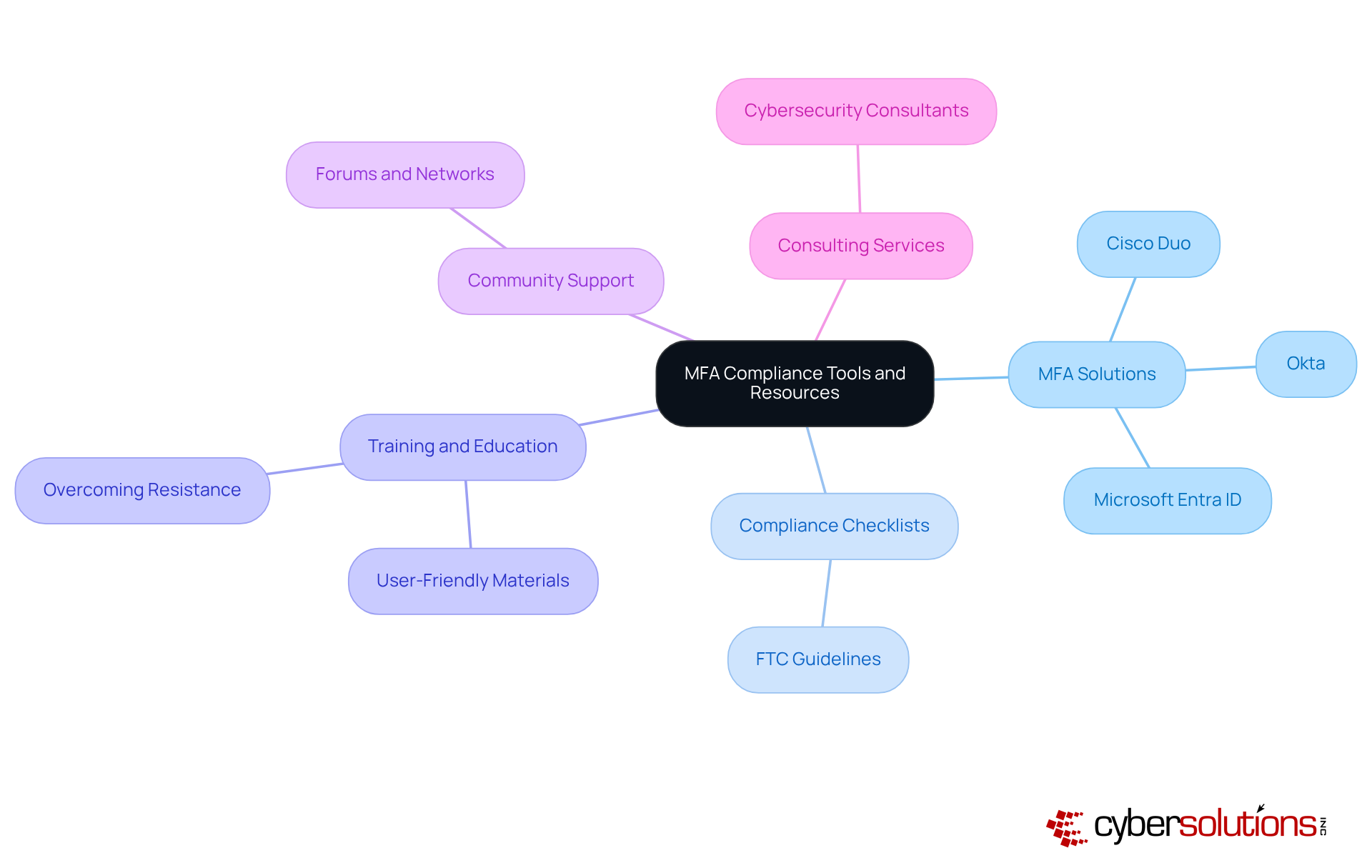
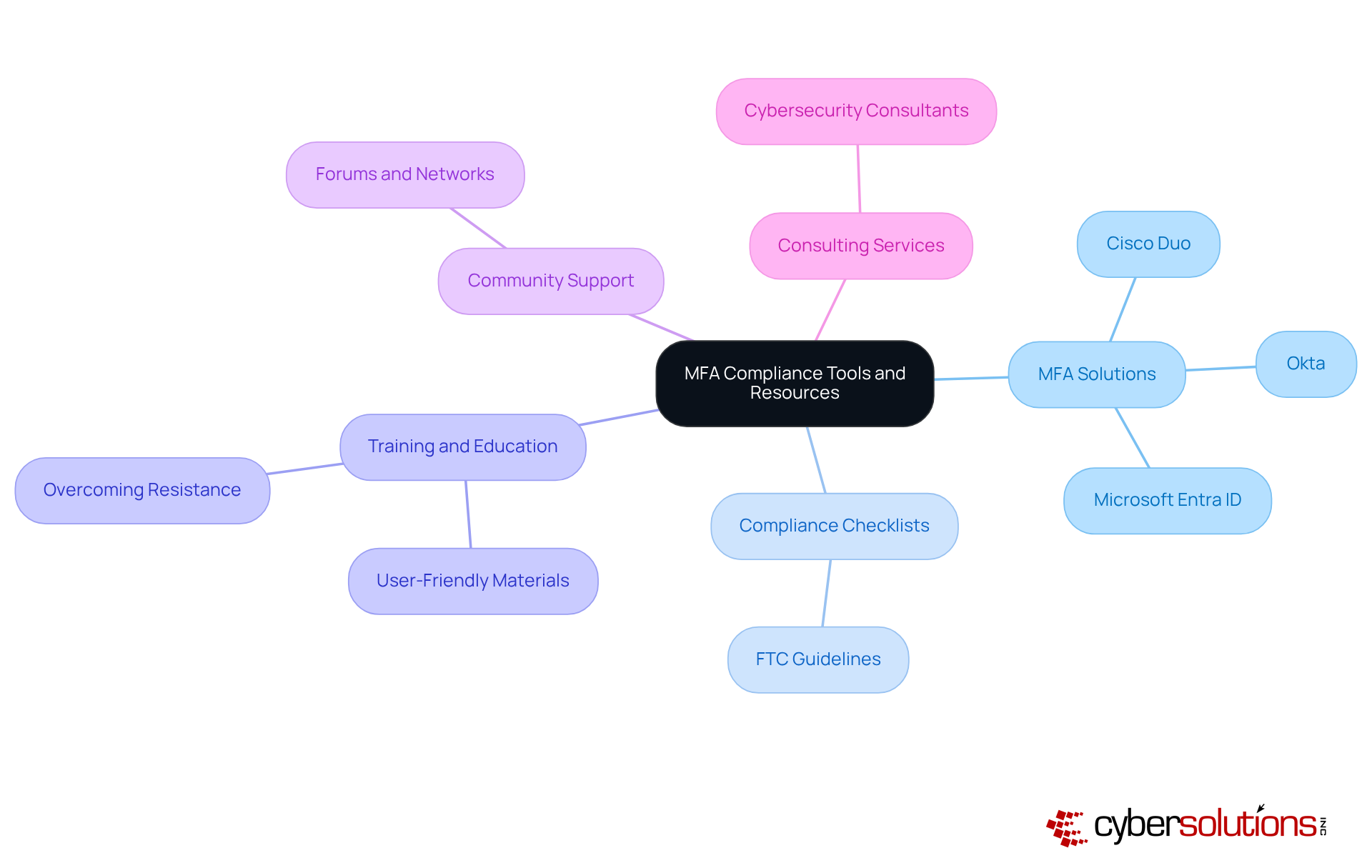
In an era where cyber threats loom large, the implementation of Multi-Factor Authentication (MFA) has become a non-negotiable aspect of healthcare security. Leading MFA solutions like Cisco Duo, Okta, and Microsoft Entra ID offer comprehensive features for secure authentication. These platforms are proven to effectively reduce breaches, with 88% of companies that adopted MFA seeing a drop in phishing success rates. Additionally, 62% of breaches could have been prevented by MFA, underscoring its critical importance in enhancing security.
To ensure compliance with the FTC MFA requirements, organizations should utilize adherence checklists from the FTC and cybersecurity entities. These checklists serve as essential tools, helping organizations systematically address each aspect of MFA implementation. Regulatory specialists emphasize the importance of these checklists in maintaining standards and improving security measures.
Regular training is crucial; accessing materials and webinars from cybersecurity firms can enhance understanding of MFA best practices and user education. This is particularly important as 40% of organizations report user resistance as a barrier to MFA adoption, and 60% of users abandon MFA if it's not user-friendly. Effective communication and training strategies are vital to overcoming these challenges.
Connecting with community forums and professional networks can provide valuable insights into MFA implementation challenges and solutions. Collaborating with peers allows organizations to share experiences and gather strategies for overcoming common obstacles.
Hiring cybersecurity consultants who specialize in MFA compliance can provide tailored guidance and support, ensuring robust security measures are in place. Their expertise can help navigate the complexities of FTC MFA requirements, ultimately enhancing your organization's security posture.
Conclusion
In an era where cyber threats are increasingly sophisticated, implementing Multi-Factor Authentication (MFA) is essential for safeguarding sensitive information. The necessity for robust protective measures in an age of frequent cyber threats cannot be overstated. Adopting MFA empowers businesses to drastically cut the risk of unauthorized access, thereby protecting sensitive information and maintaining customer trust.
We’ve explored the key components of MFA, the essential steps for compliance with FTC regulations, and the best practices for successful implementation. Key strategies include:
- Conducting thorough risk assessments
- Maintaining detailed documentation
- Providing user training
Furthermore, organizations are encouraged to regularly review their MFA practices, ensuring they adapt to evolving threats and compliance standards.
As the landscape of cyber threats continues to evolve, prioritizing MFA is not merely a compliance requirement but a vital investment in the future of organizational security. By prioritizing MFA, organizations not only protect their data but also build a resilient foundation for future security challenges. Taking action now to implement and maintain effective MFA solutions can safeguard sensitive data and ensure compliance in an increasingly regulated environment.
Frequently Asked Questions
What is Multi-Factor Authentication (MFA)?
Multi-Factor Authentication (MFA) is a security mechanism that requires users to present two or more verification factors to access resources, such as applications or online accounts, enhancing safety beyond just a username and password.
What are the key components of MFA?
The key components of MFA are:
- Knowledge Factor: Something the user knows, such as a password or PIN.
- Possession Factor: Something the user has, like a smartphone or a hardware token that generates a one-time code.
- Inherence Factor: Something the user is, which includes biometric verification methods like fingerprints or facial recognition.
Why is implementing MFA important for organizations?
Implementing MFA is crucial for safeguarding customer information systems against unauthorized access, fulfilling FTC requirements, and reducing the risk of data breaches.
What are the consequences of neglecting cybersecurity measures?
Failing to invest in robust cybersecurity measures can lead to financial losses that exceed the initial investment in protection, as well as increased risk of unauthorized access and data breaches.
How prevalent is MFA adoption in the technology industry?
The technology industry is leading in MFA adoption, with 87% of organizations implementing these protective protocols to enhance their cybersecurity measures.
What are the FTC's MFA compliance requirements for organizations?
The FTC's MFA compliance requirements include:
- Conducting a comprehensive risk assessment to identify sensitive customer information and vulnerabilities.
- Making MFA mandatory for all individuals accessing customer information systems.
- Maintaining thorough documentation of MFA policies and procedures.
- Regularly reviewing and updating MFA practices.
- Providing comprehensive training for employees on MFA significance and usage.
How can organizations minimize the risk of data breaches?
Organizations can minimize the risk of data breaches by implementing MFA, conducting regular risk assessments, maintaining documentation, reviewing practices, and training employees on cybersecurity measures.
What is the projected market growth for MFA?
The MFA market is projected to reach USD 49.7 billion by 2032, indicating its increasing importance in the future of cybersecurity, particularly in healthcare.
List of Sources
- Understand Multi-Factor Authentication (MFA) Basics
- 8 Great Cyber Security Quotes From Influencers | Proofpoint US (https://proofpoint.com/us/blog/identity-threat-defense/8-great-cyber-security-quotes-influencers)
- Multi-Factor Authentication Statistics and Facts (2026) (https://scoop.market.us/multi-factor-authentication-statistics)
- 41 Cybersecurity Quotes to Protect Your Digital Life (https://acecloudhosting.com/blog/cybersecurity-quotes)
- Multi-Factor Authentication (MFA) Statistics You Need To Know In 2025 | Dental Technologies (https://njda.org/news-information/news-archive/2025/11/25/multi-factor-authentication-(mfa)-statistics-you-need-to-know-in-2025---dental-technologies)
- Identify FTC MFA Compliance Requirements
- Multi-Factor Authentication (MFA) Statistics You Need To Know In 2025 | Dental Technologies (https://njda.org/news-information/news-archive/2025/11/25/multi-factor-authentication-(mfa)-statistics-you-need-to-know-in-2025---dental-technologies)
- 2025 Multi-Factor Authentication (MFA) Statistics & Trends to Know (https://jumpcloud.com/blog/multi-factor-authentication-statistics)
- Multi-Factor Authentication Statistics and Facts (2026) (https://scoop.market.us/multi-factor-authentication-statistics)
- FTC Safeguards Rule: What Your Business Needs to Know (https://ftc.gov/business-guidance/resources/ftc-safeguards-rule-what-your-business-needs-know)
- FTC Safeguards Rule 2026: Avoid Costly Compliance Mistakes (https://alphacis.com/ftc-safeguards-rule-2026-avoid-costly-compliance-mistakes)
- Implement MFA Solutions in Your Business
- How Should You Implement MFA in 2026? | Managed IT Services & Tech Support in West Michigan (https://hungerford.tech/blog/how-should-you-implement-mfa-in-2026)
- 13 Identity Management Day Quotes from Industry Experts in 2023 (https://solutionsreview.com/identity-management/13-identity-management-day-quotes-from-industry-experts-in-2023)
- The Cost & ROI of Multi-Factor Authentication (https://trustedtechteam.com/blogs/security/the-cost-roi-of-multi-factor-authentication)
- Multi-Factor Authentication Statistics and Facts (2026) (https://scoop.market.us/multi-factor-authentication-statistics)
- Maintain and Monitor MFA Compliance
- Multi-Factor Authentication (MFA) Statistics You Need To Know In 2025 | Dental Technologies (https://njda.org/news-information/news-archive/2025/11/25/multi-factor-authentication-(mfa)-statistics-you-need-to-know-in-2025---dental-technologies)
- 2025 Multi-Factor Authentication (MFA) Statistics & Trends to Know (https://jumpcloud.com/blog/multi-factor-authentication-statistics)
- 2026 HIPAA Security Rule Update: New Requirements (https://medcurity.com/hipaa-security-rule-2026-update)
- HIPAA 2026 Security Rule : Imperatives for Healthcare Providers (https://skycomcallcenter.com/blog/healthcare/hipaa-2026-security-rule)
- 5 HIPAA Security Rule Changes in 2026 and How to Prepare | CBIZ (https://cbiz.com/insights/article/5-hipaa-security-rule-changes-in-2026-and-how-to-prepare)
- Explore Tools and Resources for MFA Compliance
- Top 13 MFA Providers in 2026: Features, Pricing & Comparison (https://miniorange.com/blog/mfa-providers)
- Multi-Factor Authentication Adoption Rates: Are We Doing Enough? (https://patentpc.com/blog/multi-factor-authentication-adoption-rates-are-we-doing-enough)
- Multi-Factor Authentication Statistics and Facts (2026) (https://scoop.market.us/multi-factor-authentication-statistics)
- FTC Safeguards Rule: What Your Business Needs to Know (https://ftc.gov/business-guidance/resources/ftc-safeguards-rule-what-your-business-needs-know)
- 2025 Multi-Factor Authentication (MFA) Statistics & Trends to Know (https://jumpcloud.com/blog/multi-factor-authentication-statistics)