
In an era where cyber threats are evolving at an alarming rate, the need for robust IT policies in healthcare has never been more critical. These policies serve as the backbone of organizational security, guiding how companies manage their information technology resources while ensuring compliance with stringent regulations. Yet, many organizations struggle to align their IT policies with the unique demands of the healthcare sector. Failure to do so can lead to devastating breaches that compromise patient trust and organizational integrity.
How can organizations navigate these complexities to create a resilient framework that not only protects sensitive data but also fosters trust and operational efficiency?
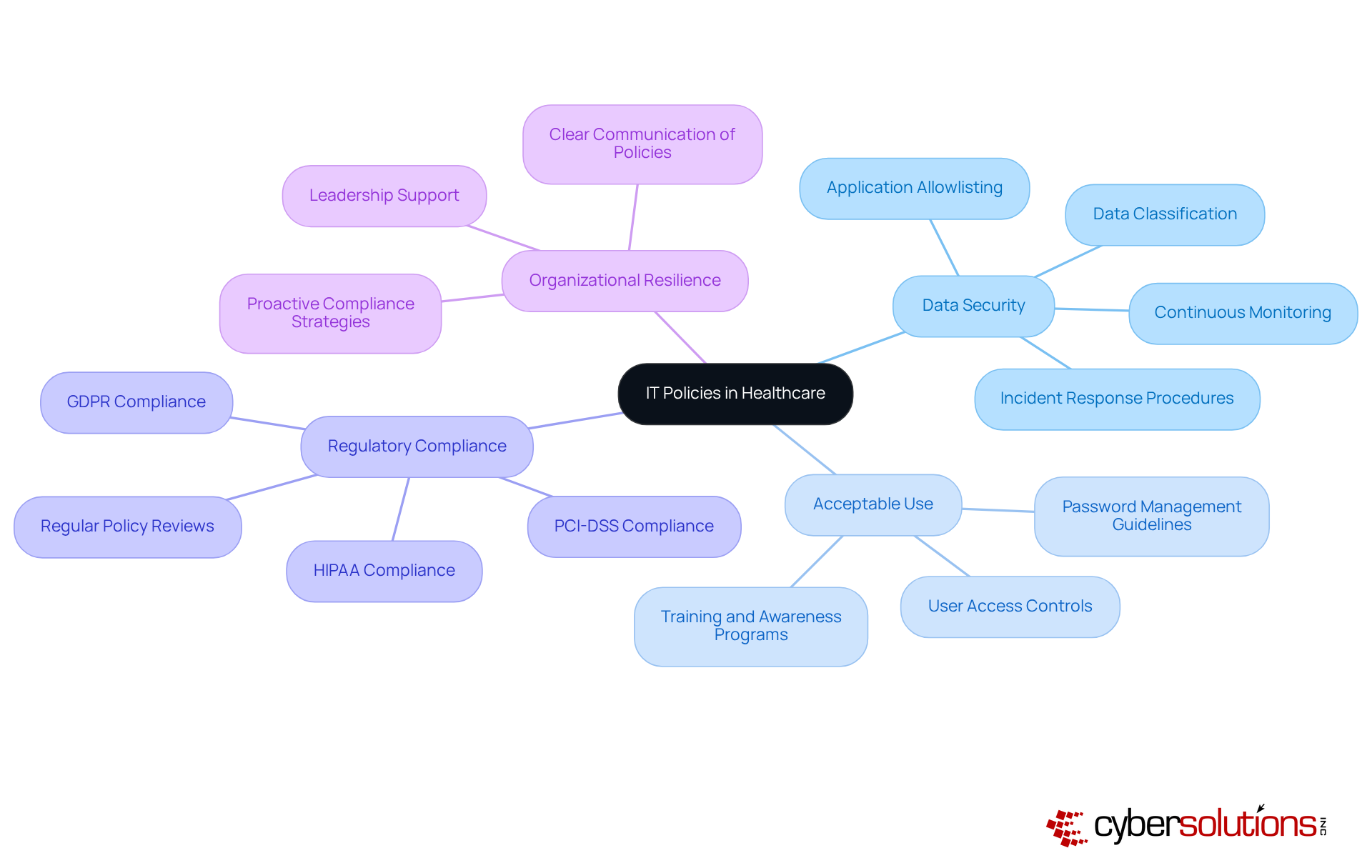
In an era where cyber threats loom large, the healthcare sector stands at a critical juncture, facing unprecedented challenges in safeguarding sensitive information. IT frameworks are organized principles that direct how an organization oversees its information technology resources, which includes the IT policy for the company that addresses crucial aspects such as data security, acceptable use, and adherence to legal and regulatory standards. These guidelines are crucial, offering a solid foundation for protecting sensitive information, ensuring operational continuity, and complying with industry regulations like HIPAA, PCI-DSS, and GDPR.
A key element of these guidelines is application allowlisting, which proactively prevents malware and unauthorized software from executing. By limiting the applications that can run, organizations can significantly reduce their attack surface and minimize vulnerabilities, thereby enhancing their cybersecurity posture. Application allowlisting features continuous monitoring of application activity and centralized management of allowlists, ensuring immediate identification and blocking of threats.
Establishing clear expectations and procedures not only mitigates cyber threats but also fortifies organizational resilience, ensuring long-term stability and trust. Without robust IT frameworks, healthcare organizations risk not only their data but also their very reputation and financial viability in an increasingly hostile digital landscape.
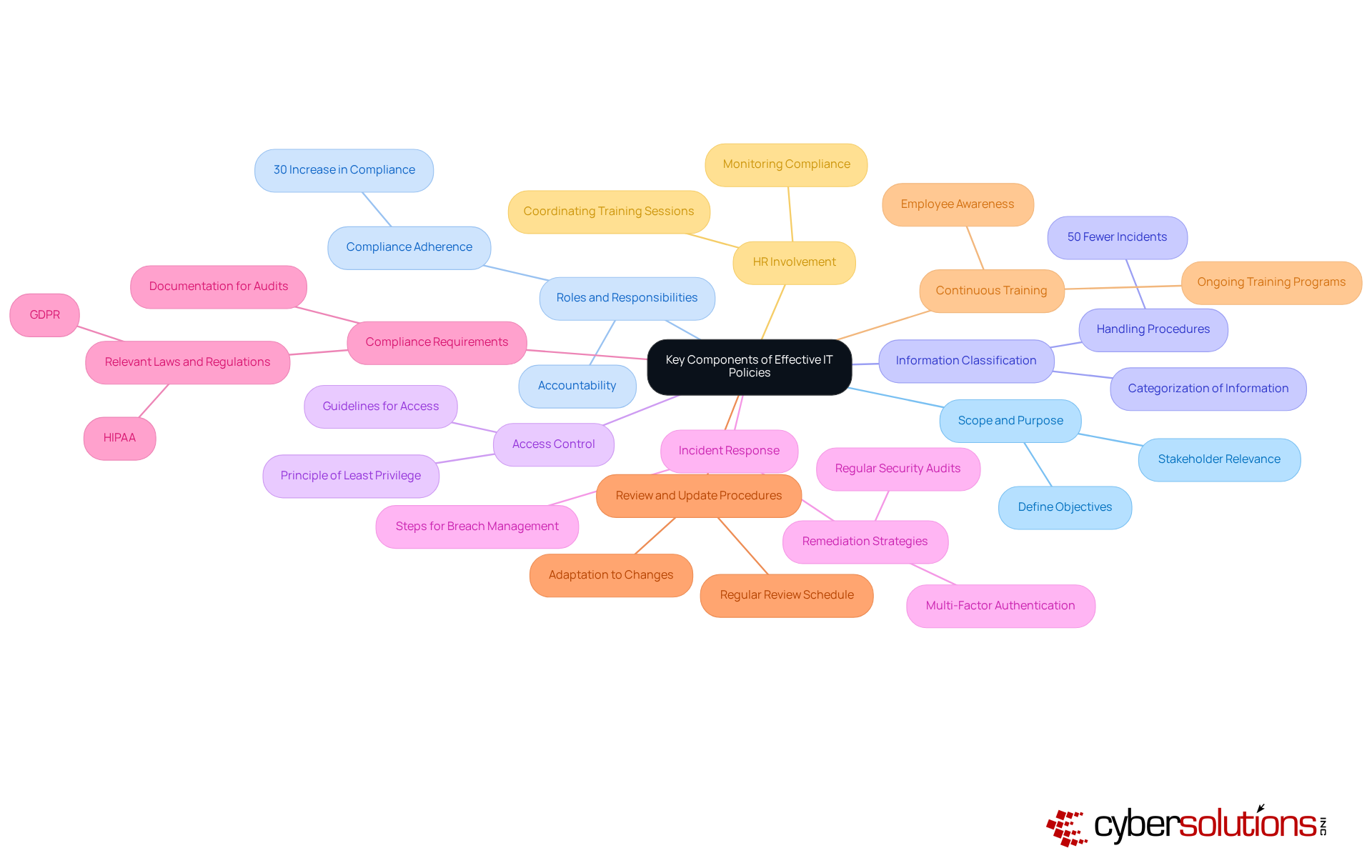
In an era where cyber threats loom large, the healthcare sector faces unprecedented challenges in safeguarding sensitive information. Effective IT policies should encompass several essential components to ensure organizational security and compliance:
By integrating these elements, organizations can create an effective IT policy for the company that not only safeguards their assets but also improves operational efficiency and regulatory stance, especially in readiness for audits such as CMMC and following HIPAA standards. Without robust IT policies, organizations risk not only their data but also their reputation and trust within the community.
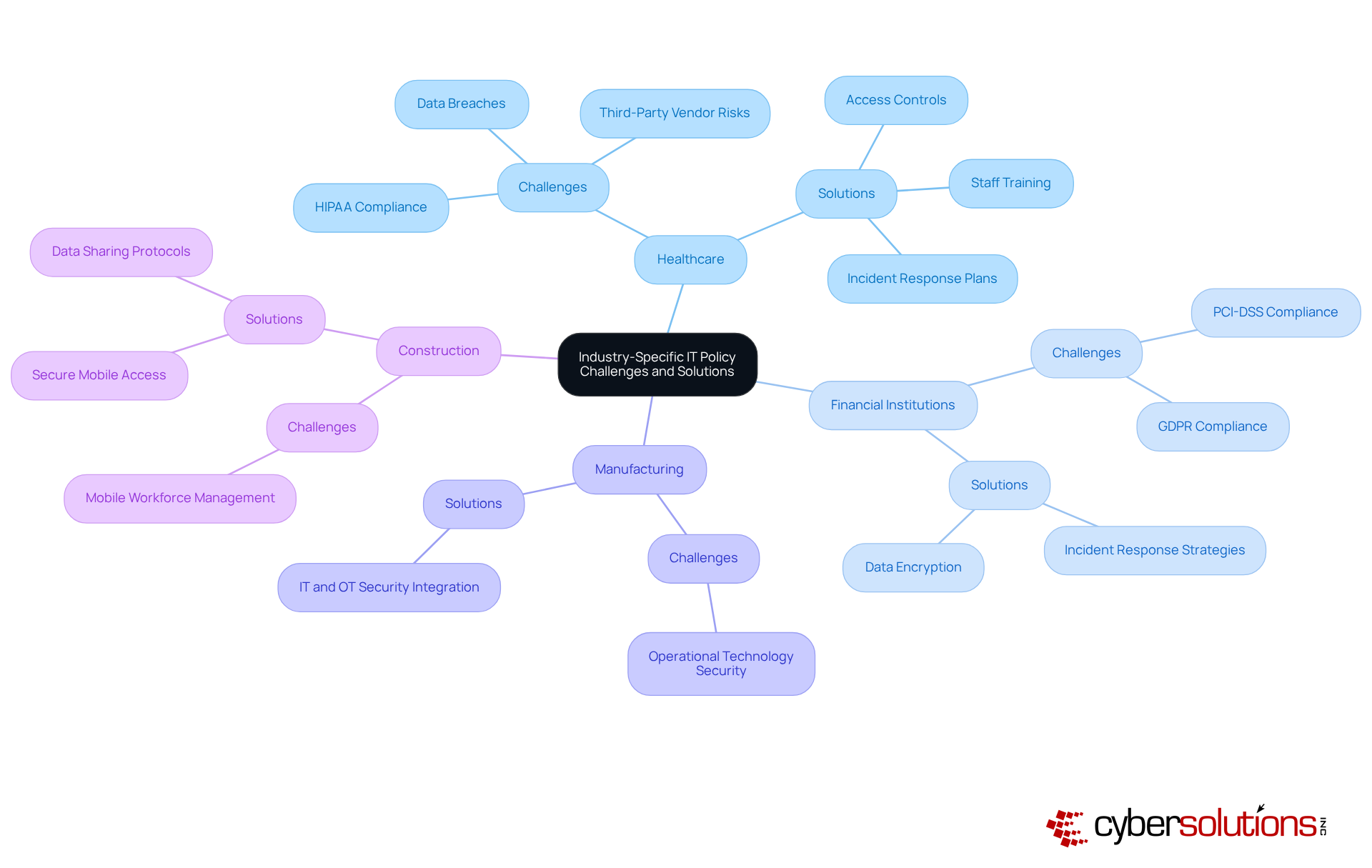
In an era where cybersecurity threats loom larger than ever, the healthcare sector stands at a critical crossroads, facing unique challenges that demand immediate attention. A significant hurdle is maintaining compliance with HIPAA regulations while safeguarding sensitive patient information. Effective solutions include implementing stringent access controls and conducting regular training for staff on data privacy. Alarmingly, the majority of HIPAA breaches stem from inadequate access to Protected Health Information (PHI), often due to weak access control measures and insufficient training. Healthcare organizations must conduct annual enterprise risk analyses to effectively prioritize and address compliance gaps. With a 21.4% month-over-month rise in healthcare information breaches reported in August 2023, this alarming trend highlights the urgent need for a robust IT policy for companies that is tailored to the healthcare sector's unique challenges. Rapid incident response strategies, such as having an incident response team on-site within 24 hours, can significantly enhance recovery efforts. A layered approach - including endpoint isolation, malware removal, and user training - enables a faster and more complete recovery from breaches, reinforcing cybersecurity confidence in healthcare settings.
Financial institutions must navigate intricate regulations such as PCI-DSS and GDPR. Strong IT policy for companies in this sector usually emphasizes effective data encryption and thorough incident response strategies to tackle potential breaches. With 59% of healthcare breaches involving third-party vendors, financial organizations must also conduct rigorous third-party risk assessments before onboarding and annually thereafter to ensure compliance and protect sensitive information.
The manufacturing industry often grapples with securing operational technology (OT) systems against cyber threats. Solutions may involve combining IT and OT security strategies to provide comprehensive protection, thereby reducing vulnerabilities associated with legacy systems.
Challenges in the construction sector frequently relate to managing a mobile workforce and facilitating secure information sharing across various sites. The IT policy for companies should concentrate on creating secure mobile access and data sharing protocols to reduce risks linked to data exposure.
By understanding these industry-specific challenges, organizations can proactively fortify their defenses and ensure compliance in an increasingly complex landscape.
In an era where cybersecurity threats loom large, healthcare organizations must prioritize a robust IT policy for the company to safeguard their operations and patient data. Implementing these guidelines effectively requires a structured approach that prioritizes stakeholder engagement and ongoing enhancement. Key strategies include:
Without these proactive measures, organizations risk not only their compliance but also the trust of those they serve.

In today's digital landscape, the stakes of inadequate IT policies have never been higher. These frameworks guide organizations in managing their IT resources. They also act as a bulwark against the complex cyber threats that jeopardize sensitive data and operational integrity. By establishing comprehensive IT policies, companies can ensure compliance with industry regulations, safeguard their reputation, and maintain the trust of their stakeholders.
Key components of effective IT policies include:
The discussion illuminated the unique challenges faced by various industries, from healthcare's stringent HIPAA compliance to the financial sector's intricate regulatory landscape. Each sector requires tailored solutions to navigate these challenges effectively, emphasizing the need for a proactive approach in policy development and implementation.
Navigating the complexities of cyber threats can feel overwhelming for many organizations. The call to action is clear: organizations must prioritize developing and enforcing comprehensive IT policies to thrive in today's digital landscape. By investing in these frameworks, businesses not only protect their assets but also enhance their operational resilience and adaptability in an ever-evolving regulatory environment. The future of your organization hinges on the strength of your IT policies - are you prepared to take action?
What are IT policies and why are they important in business?
IT policies are organized principles that guide how an organization manages its information technology resources. They are crucial for protecting sensitive information, ensuring operational continuity, and complying with industry regulations such as HIPAA, PCI-DSS, and GDPR.
What are the key components of IT policies?
Key components of IT policies include data security, acceptable use, and adherence to legal and regulatory standards.
What is application allowlisting and how does it enhance cybersecurity?
Application allowlisting is a security measure that prevents malware and unauthorized software from executing by limiting the applications that can run on an organization's systems. This significantly reduces the attack surface and minimizes vulnerabilities, enhancing the organization's cybersecurity posture.
How does application allowlisting work?
Application allowlisting features continuous monitoring of application activity and centralized management of allowlists, allowing for immediate identification and blocking of threats.
What are the consequences of not having robust IT frameworks in place?
Without robust IT frameworks, healthcare organizations risk compromising their data, damaging their reputation, and jeopardizing their financial viability in a hostile digital landscape.
How do IT policies contribute to organizational resilience?
Establishing clear IT policies and procedures mitigates cyber threats and fortifies organizational resilience, ensuring long-term stability and trust.