Introduction
In an era where cyber threats are not just a possibility but a reality, healthcare organizations must confront the urgent need for robust cybersecurity measures. With financial repercussions from data incidents projected to exceed $10 million per occurrence by 2026, organizations must adopt effective strategies to mitigate these risks.
So, what can businesses do to not just defend against breaches but also foster a culture of security awareness among their teams? Exploring proven strategies for breach prevention reveals essential practices that can protect both data integrity and corporate reputation in an increasingly perilous digital environment.
Failure to act could lead to devastating financial and reputational damage.
Understand the Nature of Data Breaches
In an era where cyber threats loom larger than ever, the healthcare sector faces unprecedented challenges in breach prevention for safeguarding sensitive information. Security incidents occur when unauthorized individuals gain access to confidential data, including personal details, financial records, or intellectual property. The fallout from these breaches can be catastrophic, underscoring the need for effective breach prevention to avoid staggering financial losses and irreparable reputational harm.
According to the IBM Cost of a Data Incident Report:
This underscores the importance of investing in advanced AI protective tools for breach prevention, which can save organizations an average of $1.9 million per incident, making proactive measures not just beneficial but essential. Understanding these dynamics is not just beneficial; it’s essential for any healthcare organization aiming to thrive in a perilous digital landscape.

Implement Proactive Prevention Strategies
In an era where cyber threats loom larger than ever, the healthcare sector must prioritize robust cybersecurity measures to protect sensitive patient data. To effectively achieve breach prevention, companies should implement a multi-layered protection strategy. Key strategies include:
- Multi-Factor Authentication (MFA): Implementing MFA significantly enhances security by requiring users to provide two or more verification factors to gain access to systems. This measure can block 99.9% of account compromise attacks, making it essential for safeguarding sensitive information.
- Regular Software Updates: Keeping software and systems updated is crucial for protecting against known vulnerabilities. Cybercriminals often exploit outdated software to gain unauthorized access, with 62% of breaches potentially preventable through effective MFA and regular updates. Organizations should prioritize timely updates to mitigate risks associated with unpatched vulnerabilities.
- Network Security Measures: Employ firewalls, intrusion detection systems, and encryption to safeguard sensitive information both in transit and at rest. These measures create a fortified perimeter around critical assets, which is essential for breach prevention and reducing the likelihood of unauthorized access. With Cyber Solutions, you gain access to comprehensive firewall and network protection that not only ensures compliance but also proactively defends against evolving threats.
- Information Classification: Recognize and categorize information according to sensitivity to implement suitable protective measures. This assists in prioritizing protection efforts where they are most necessary, ensuring that the most vital data receives the highest level of safeguarding.
- Regular Security Audits: Conducting periodic audits can help identify vulnerabilities and ensure compliance with industry regulations. These audits should include penetration testing and vulnerability assessments to proactively address potential weaknesses, reinforcing the organization’s overall security posture. Additionally, Cyber Solutions offers 24/7 monitoring to identify and prevent suspicious activities before they escalate, protecting businesses from ransomware, phishing, and other malware attacks. Furthermore, our Co-Managed IT Services enhance these strategies by providing expert support and resources to ensure comprehensive cybersecurity management. Without these essential strategies for breach prevention, healthcare organizations risk not only their data but also their reputation and trust with patients.

Develop a Robust Incident Response Plan
In an era where cyber threats loom larger than ever, the healthcare sector must prioritize a robust incident response plan (IRP) to safeguard its operations and reputation. A well-structured IRP is essential for organizations to effectively manage cyber threats. Key components include:
- Preparation: Establish a dedicated response team with clearly defined roles and responsibilities. Ensure team members receive comprehensive training and are well-acquainted with the IRP. Lauren Winchester, Head of Cyber Risk Services at Travelers, puts it succinctly: "A well-thought-out and documented plan is critical so you don’t have to rely on your memory during a crisis." Integrate tailored remediation strategies, including policy updates and process improvements, into the IRP to effectively address compliance gaps.
- Detection and Analysis: Utilize advanced monitoring tools to identify violations in real-time. Conduct thorough analyses of incidents to assess their scope and impact, as attackers can exfiltrate data within 72 minutes of gaining access. In 2026, cybercrime damages are estimated to exceed $1 trillion, underscoring the financial implications of inadequate cybersecurity measures.
- Containment, Eradication, and Recovery: Develop robust procedures for containing incidents to minimize damage, eradicating threats, and swiftly recovering affected systems. This proactive approach is crucial, especially as ransomware can spread in minutes. Rapid deployment of incident response teams, as demonstrated in case studies, significantly enhances recovery efforts and bolsters security measures.
- Post-Incident Review: After an incident, perform a detailed review to extract lessons learned and enhance future response efforts. Regular updates to the IRP based on these findings are vital for continuous improvement. Organizations should also be aware of common pitfalls in incident response planning, such as failing to test the IRP regularly or not involving all relevant stakeholders.
- Communication Plan: Clearly outline communication strategies for engaging stakeholders, including customers, employees, and regulatory bodies, during and after an incident. Transparency is essential for maintaining trust and demonstrating a commitment to cybersecurity.
In 2026, organizations without an IRP face significant risks, as 45% of businesses lack such a plan, according to the 2025 Travelers Cyber Risk Index. Without a proactive IRP, organizations not only jeopardize their data but also their very existence in an increasingly perilous digital landscape. Applying these optimal strategies not only readies organizations for possible incidents but also strengthens their robustness in a swiftly changing risk environment. Moreover, incorporating AI into incident response strategies is becoming progressively essential, as it improves the capacity to identify and react to dangers effectively.

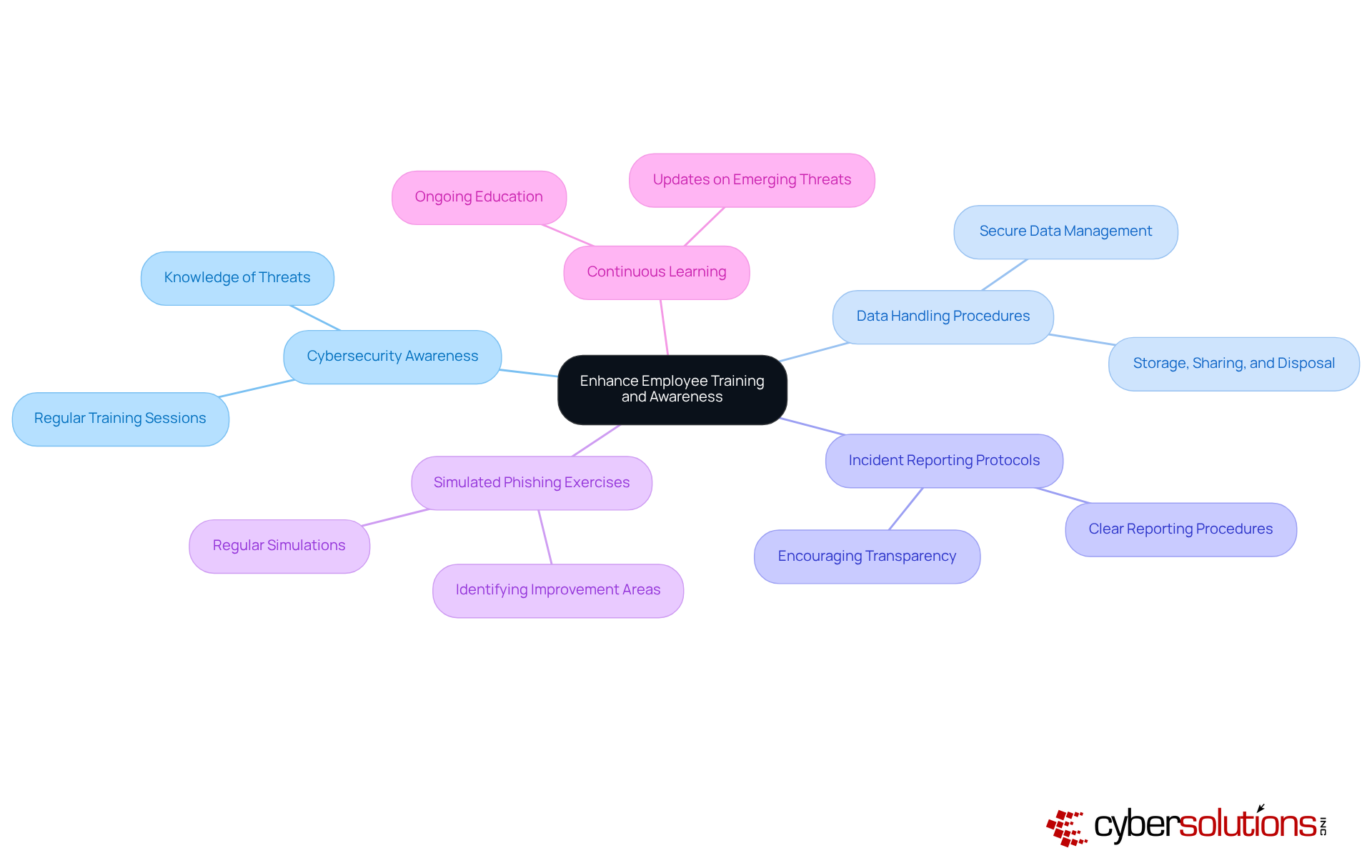
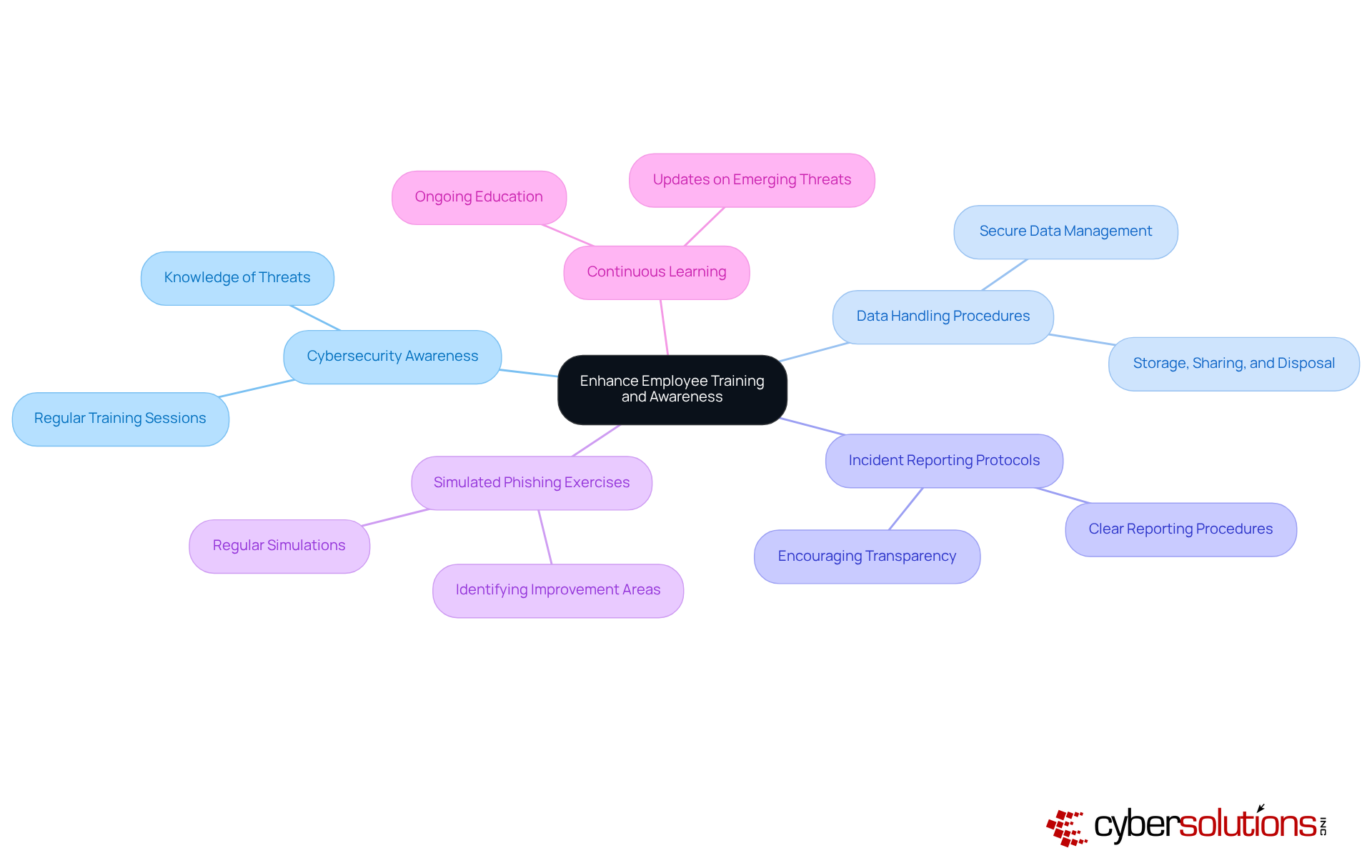
Enhance Employee Training and Awareness
In an era where healthcare data breaches are increasingly common, the need for robust breach prevention measures has never been more critical. To safeguard against the rising tide of data breaches, organizations must prioritize comprehensive employee training programs that address key areas of vulnerability:
- Cybersecurity Awareness: Equip employees with knowledge about prevalent threats like phishing, malware, and social engineering to fortify defenses. Regular training sessions can reinforce safe practices and keep awareness high.
- Data Handling Procedures: Instruct employees on secure methods for managing sensitive data, encompassing storage, sharing, and disposal practices. This ensures that sensitive information is treated with the utmost care.
- Incident Reporting Protocols: Implement straightforward procedures for reporting suspicious activities or potential breaches, empowering employees to act without hesitation. A culture of transparency encourages vigilance.
- Simulated Phishing Exercises: Regularly conduct phishing simulations to evaluate employee awareness and response, identifying areas for improvement in training. This hands-on approach sharpens skills and prepares staff for real threats.
- Continuous Learning: Cultivate a culture of ongoing education by offering continuous training and updates on emerging threats and best practices, ensuring employees stay informed and vigilant.
Without a proactive approach to employee training that emphasizes breach prevention, healthcare organizations risk not only their data but also their reputation and financial stability.
Conclusion
In an era where cyber threats loom large, healthcare organizations face an urgent need to prioritize effective breach prevention strategies to safeguard sensitive data and maintain trust. The financial burden of a single data breach can cripple an organization, making prevention not just a priority but a necessity. Embracing a proactive approach not only protects valuable information but also fortifies the organization’s reputation in an increasingly digital landscape.
Key strategies for effective breach prevention include:
- Implementing multi-factor authentication
- Conducting regular software updates
- Developing a robust incident response plan
Additionally, fostering a culture of cybersecurity awareness through comprehensive employee training is essential. Together, these measures boost an organization’s ability to prevent breaches and respond effectively if an incident occurs, greatly reducing potential risks.
Ultimately, the significance of adopting these proven strategies cannot be overstated. Organizations that invest in cybersecurity measures and cultivate awareness among their teams position themselves to navigate the complexities of the digital world with resilience. By taking decisive action today, organizations not only shield themselves from potential breaches but also reinforce their commitment to safeguarding patient trust and data integrity.
Frequently Asked Questions
What is a data breach?
A data breach occurs when unauthorized individuals gain access to confidential information, such as personal details, financial records, or intellectual property.
Why are data breaches particularly concerning for the healthcare sector?
Data breaches in the healthcare sector are concerning due to the sensitive nature of the information involved and the potential for catastrophic fallout, including significant financial losses and irreparable reputational harm.
What is the projected average cost of a data incident for U.S. organizations by 2026?
By 2026, U.S. organizations are projected to face an average data incident cost of $10.22 million.
How can organizations reduce the costs associated with data breaches?
Organizations that utilize AI protective tools extensively can save an average of $1.9 million per data incident, highlighting the importance of investing in these advanced tools for breach prevention.
Why is it essential for healthcare organizations to understand data breach dynamics?
Understanding the dynamics of data breaches is essential for healthcare organizations to effectively safeguard sensitive information and thrive in a challenging digital landscape.
List of Sources
- Understand the Nature of Data Breaches
- Average Cost of a Data Breach 2026 | 46 Facts From IBM & Verizon (https://cnicsolutions.com/cybersecurity-threat-protection/average-cost-of-a-data-breach-statistics-2026)
- Cybersecurity Statistics 2026 | 52+ Facts From FBI, IBM & Verizon (https://cnicsolutions.com/cybersecurity-threat-protection/cybersecurity-statistics-2026)
- Cost of a data breach 2025 | IBM (https://ibm.com/reports/data-breach)
- Average Data Breach Cost Hits All-time High of $4.4M | INSURICA (https://insurica.com/blog/average-data-breach-cost-hits-all-time-high-of-4-4m)
- Data Breach Monitoring | Breachsense (https://breachsense.com/breaches)
- Implement Proactive Prevention Strategies
- Multi-Factor Authentication Adoption Rates: Are We Doing Enough? (https://patentpc.com/blog/multi-factor-authentication-adoption-rates-are-we-doing-enough)
- Future of MFA: 10 Authentication Trends That Will Dominate 2026 (https://miniorange.com/blog/future-of-mfa)
- 10 Multi-factor Authentication Trends To Adopt in 2026 | OLOID (https://oloid.com/blog/future-trends-in-multi-factor-authentication-what-to-expect)
- 7 Reasons Why You Need MFA Security in 2026 (https://splashtop.com/blog/why-you-need-MFA-security)
- MFA Evolution: From SMS Codes to Phishing-Resistant Authentication - The LastPass Blog (https://blog.lastpass.com/posts/tracing-the-evolution-of-multi-factor-authentication)
- Develop a Robust Incident Response Plan
- Incident Response in 2026: A Complete Enterprise Guide (https://uscsinstitute.org/cybersecurity-insights/resources/incident-response-in-2026-a-complete-enterprise-guide)
- The Incident Response Plan – An Important Aspect of Your Cybersecurity in 2026 (https://netgainit.com/blogs/the-incident-response-plan-an-important-aspect-of-your-cybersecurity)
- The Importance of Having an Incident Response Plan | Travelers Institute (https://institute.travelers.com/cyber-security/cyber-readiness/incident-response)
- How to Build an Effective Cyber Incident Response Plan in 2026 (https://kaufmanit.com/cyber-incident-response-plan-2026)
- Enhance Employee Training and Awareness
- Federal Bill Proposes Grant Program to Train Cyber Workforce (https://govtech.com/education/higher-ed/federal-bill-proposes-grant-program-to-train-cyber-workforce)
- Why Cyber Security Awareness Training is Critical in 2026 (https://inspired-it.com.au/blog/why-cyber-security-awareness-training-is-critical-in-2026)
- White House launching tech pilots, ‘Cyber Academy’ under new cyber strategy | Federal News Network (https://federalnewsnetwork.com/cybersecurity/2026/03/white-house-launching-tech-pilots-cyber-academy-under-new-cyber-strategy)
- Cybersecurity Training Grants (2026) (https://grantedai.com/grants/cybersecurity-training-grants-cyber-grants-alliance-287ab4b3)
- Cybersecurity Awareness Training for Employees in 2026 (https://uscsinstitute.org/cybersecurity-insights/resources/cybersecurity-awareness-training-for-employees-in-2026)