
In the healthcare sector, where patient data is a prime target for cybercriminals, the urgency of robust cybersecurity measures cannot be overstated. In an age where cyber threats are not only prevalent but increasingly sophisticated, organizations must prioritize their cybersecurity strategies.
Effective external vulnerability scanning is a vital weapon in this fight, allowing organizations to pinpoint and rectify vulnerabilities in their public-facing systems before cybercriminals can take advantage of them. This proactive approach is essential for safeguarding sensitive data and maintaining trust with patients.
But with so much at stake, what steps can organizations take to make sure they have the right tools and practices to strengthen their defenses against these constantly changing cyber threats?
In an era where cyber threats are increasingly sophisticated, the need for robust cybersecurity measures in healthcare has never been more critical. External vulnerability scanning is vital for assessing a company's public-facing systems to identify weaknesses. These scans aim to [[uncover vulnerabilities](https://thehackernews.com/search/label/Vulnerability Scanning)](https://thehackernews.com/search/label/Vulnerability Scanning) that cybercriminals could exploit, enabling organizations to take proactive measures to mitigate risks. As cyber threats evolve, organizations face increasing pressure to stay ahead of potential vulnerabilities.
Organizations encounter various challenges, including:
Routine external vulnerability scanning is essential for detecting possible entry points for attackers, enabling businesses to address these weaknesses before they can be exploited. Statistics reveal that 60% of data breaches stem from the failure to implement available patches, underscoring the urgency of prompt risk management. How can organizations ensure they are not the next target in this evolving cyber landscape?
Moreover, external vulnerability scanning helps organizations comply with critical regulations like GDPR and HIPAA, ensuring they effectively protect sensitive data. By investing in external threat assessments, companies not only strengthen their security posture but also demonstrate a commitment to safeguarding client data, ultimately fostering trust and credibility in the marketplace. Failing to conduct these assessments could lead to devastating breaches and loss of client trust. As the cybersecurity environment changes, the necessity for strong external threat assessment practices grows more essential for businesses seeking to safeguard their assets and ensure compliance.

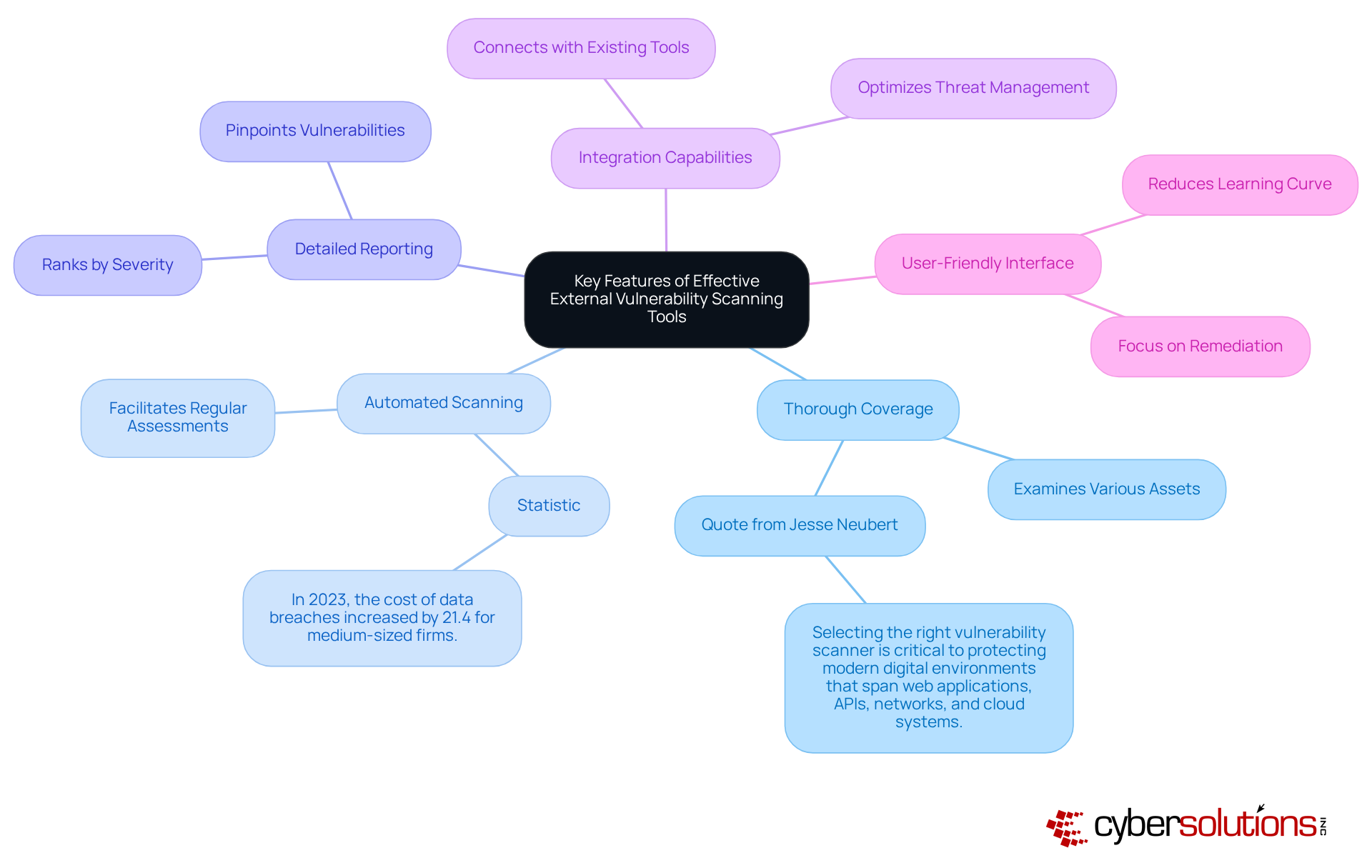
In an era where healthcare organizations are prime targets for cyberattacks, the need for robust cybersecurity measures has never been more critical. When selecting external vulnerability scanning tools, organizations should prioritize several key features to ensure effective investment in their cybersecurity strategy:
Failing to invest in the right scanning tools can lead to devastating financial and reputational damage. Focusing on these key features allows organizations to select external vulnerability scanning tools that align with their security needs and operational objectives, significantly boosting their cyber resilience. Additionally, case studies such as those involving Invicti and Qualys VMDR demonstrate the effectiveness of these tools in real-world applications, providing further validation for their selection.
In an era where cyber threats loom large, the importance of external vulnerability scanning in safeguarding sensitive information cannot be overstated. Real-world applications of external vulnerability scanning illustrate its critical role in enhancing cybersecurity across various sectors. For example:
These instances illustrate how entities can utilize external vulnerability scanning to recognize and reduce risks, enhance their overall security structures, ensure adherence, and safeguard sensitive information. Ultimately, proactive external assessments are not just a safeguard; they are a strategic imperative for any organization aiming to thrive in today's digital landscape.

In an era where cyber threats are escalating, the healthcare sector stands at a critical juncture, necessitating robust cybersecurity measures to protect sensitive patient data and maintain trust. Hosted external vulnerability scanning solutions provide significant advantages that strengthen a company's cybersecurity posture. Key benefits include:
By utilizing external vulnerability scanning that is hosted, organizations can enhance their protective measures while optimizing resource allocation, ultimately resulting in a more resilient cybersecurity framework. Embracing external vulnerability scanning in a hosted environment is not just a strategic choice; it’s a vital step toward safeguarding your organization’s future in an increasingly perilous digital landscape.

Organizations today face an alarming rise in cyber threats, making external vulnerability scanning an essential strategy for safeguarding sensitive data and ensuring operational integrity. By proactively identifying weaknesses in public-facing systems, businesses can mitigate risks before they are exploited by malicious actors, thereby fortifying their cybersecurity posture against the evolving landscape of cyber threats.
The importance of regular external vulnerability scanning cannot be overstated. It plays a critical role in compliance with regulations like GDPR and HIPAA, while also preventing data breaches that can lead to significant financial and reputational damage. Effective scanning tools must offer thorough coverage, automated scanning, and user-friendly interfaces, enabling organizations to select the right tools that align with their security needs. Real-world examples illustrate how various sectors have successfully implemented these strategies, resulting in improved security outcomes and increased customer trust.
Ultimately, making external vulnerability scanning a priority - especially through hosted solutions - is not just a tactical choice; it’s a strategic necessity for organizations. By investing in these proactive measures, businesses can enhance their defenses and foster a culture of security that prioritizes the protection of critical data assets. Failure to implement these strategies could lead to devastating data breaches and loss of customer trust. Organizations must prioritize external vulnerability scanning as a foundational element of their cybersecurity strategy to ensure a safer and more resilient future.
What is the purpose of external vulnerability scanning?
The purpose of external vulnerability scanning is to assess a company's public-facing systems to identify weaknesses that cybercriminals could exploit, enabling organizations to take proactive measures to mitigate risks.
Why is external vulnerability scanning important for organizations?
External vulnerability scanning is important because it helps organizations detect potential entry points for attackers, ensures compliance with regulations like GDPR and HIPAA, and strengthens their security posture to protect sensitive data.
What challenges do organizations face that make external vulnerability scanning necessary?
Organizations face challenges such as data breaches, regulatory compliance issues, and reputational damage, which make external vulnerability scanning crucial for identifying and addressing vulnerabilities.
What statistics highlight the urgency of conducting external vulnerability scans?
Statistics reveal that 60% of data breaches stem from the failure to implement available patches, highlighting the urgency of prompt risk management through external vulnerability scanning.
How does external vulnerability scanning contribute to regulatory compliance?
External vulnerability scanning helps organizations comply with critical regulations like GDPR and HIPAA by ensuring they effectively protect sensitive data and address vulnerabilities.
What are the consequences of failing to conduct external vulnerability assessments?
Failing to conduct external vulnerability assessments could lead to devastating data breaches and a loss of client trust, negatively impacting an organization's reputation and security.