
In an era where cyber threats loom large, the healthcare sector must prioritize cybersecurity to protect sensitive patient data and maintain operational integrity. Understanding the digital landscape is crucial for businesses operating in today's technology-driven world, especially as cyber threats like adware and spyware become increasingly prevalent. Organizations face mounting pressure to safeguard sensitive data against relentless cyber threats while navigating complex regulatory landscapes.
These forms of malware not only jeopardize sensitive information but also disrupt operations, leading to significant financial and reputational damage. We’ll explore the characteristics and differences between adware and spyware, how they infiltrate systems, and actionable strategies to safeguard your data and maintain operational integrity.
Without robust cybersecurity measures, organizations risk not only their financial stability but also the trust of those they serve.
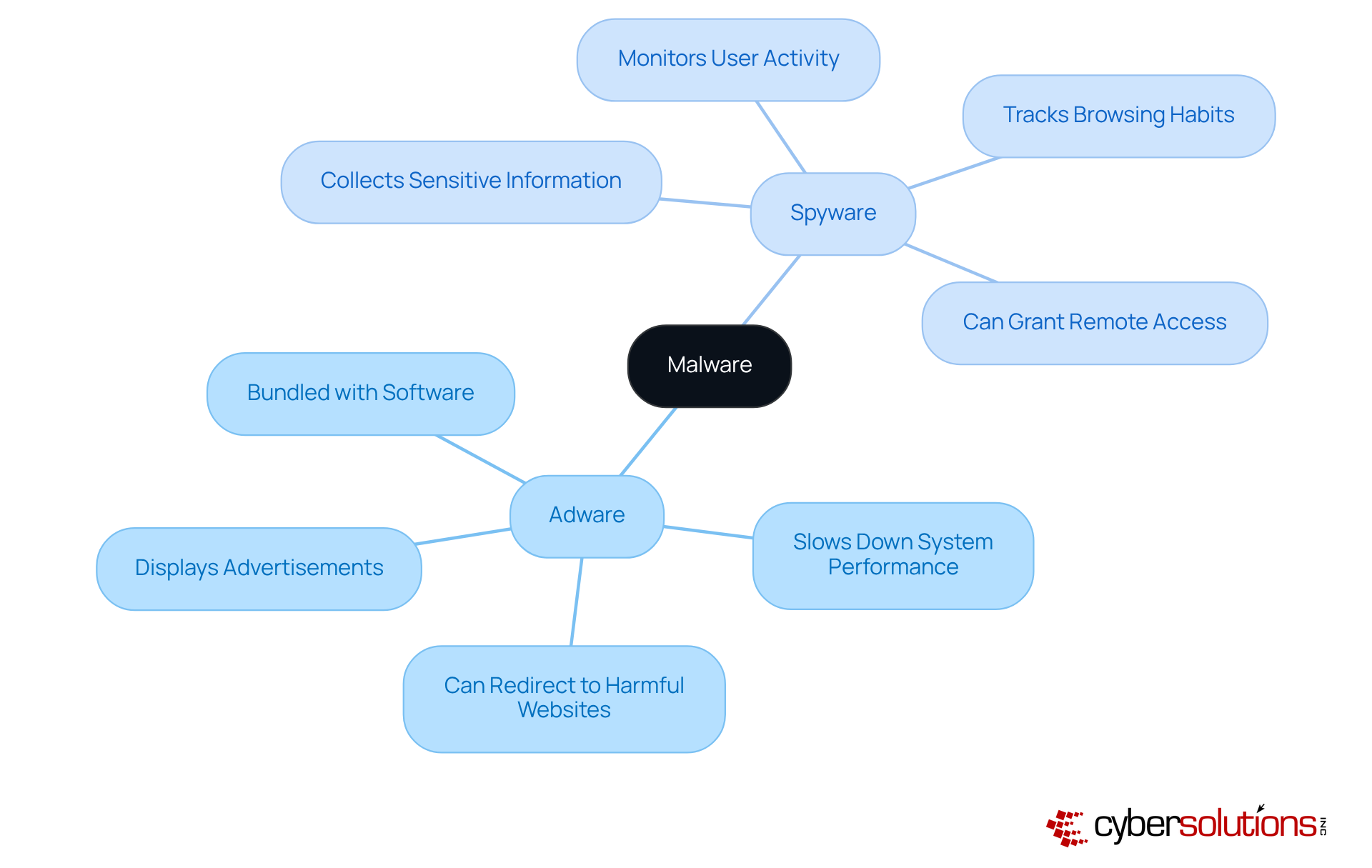
In an era where cyber threats are increasingly sophisticated, understanding the nuances of malware is essential for safeguarding sensitive information in healthcare. Adware and spyware are both forms of malware, yet they serve different purposes and operate in unique ways:
Grasping these differences is vital for organizations looking to strengthen their cybersecurity efforts. Without proper backups, organizations risk losing critical data forever during an attack, underscoring the urgent need for proactive security measures to safeguard their data. Application allowlisting is an essential instrument in this context, as it stops unauthorized applications, including malicious software, from running on systems. By limiting the applications that can run, organizations can significantly reduce their attack surface and enhance compliance with regulations like HIPAA and GDPR. The increase in advanced tracking software attacks, especially aimed at messaging applications, highlights the necessity for continuous alertness and strong protections against developing dangers.
Cyber Solutions offers expert malware removal and system reconstruction services, ensuring that compromised endpoints are cleaned, patched, and fortified against future attacks. By identifying the traits of malicious software, businesses can better protect their sensitive information and uphold operational integrity. By prioritizing cybersecurity, organizations can not only protect their data but also maintain trust and integrity in their operations.
In an era where healthcare organizations are increasingly targeted by cybercriminals, it is crucial to understand the threats posed by adware and spyware to safeguard sensitive patient data and maintain operational integrity.
Adware and spyware infiltrate systems through various methods, creating significant risks to organizational security and productivity.
These threats not only compromise sensitive data but also disrupt daily operations, leading to financial losses and reputational damage, highlighting the urgent need for robust security measures. To combat these threats, organizations must prioritize regular updates, empower employees with training to spot phishing attempts, and invest in trusted anti-spyware solutions. Furthermore, applying application allowlisting can enhance security by ensuring that only authorized applications can operate on your systems, effectively preventing unauthorized software and decreasing the chance of malware infiltration. Additionally, application allowlisting helps organizations meet compliance requirements for standards such as HIPAA, PCI-DSS, and GDPR, ensuring adherence to strict data protection protocols. By adopting comprehensive security strategies, organizations not only protect their assets but also uphold their commitment to patient trust and regulatory compliance.
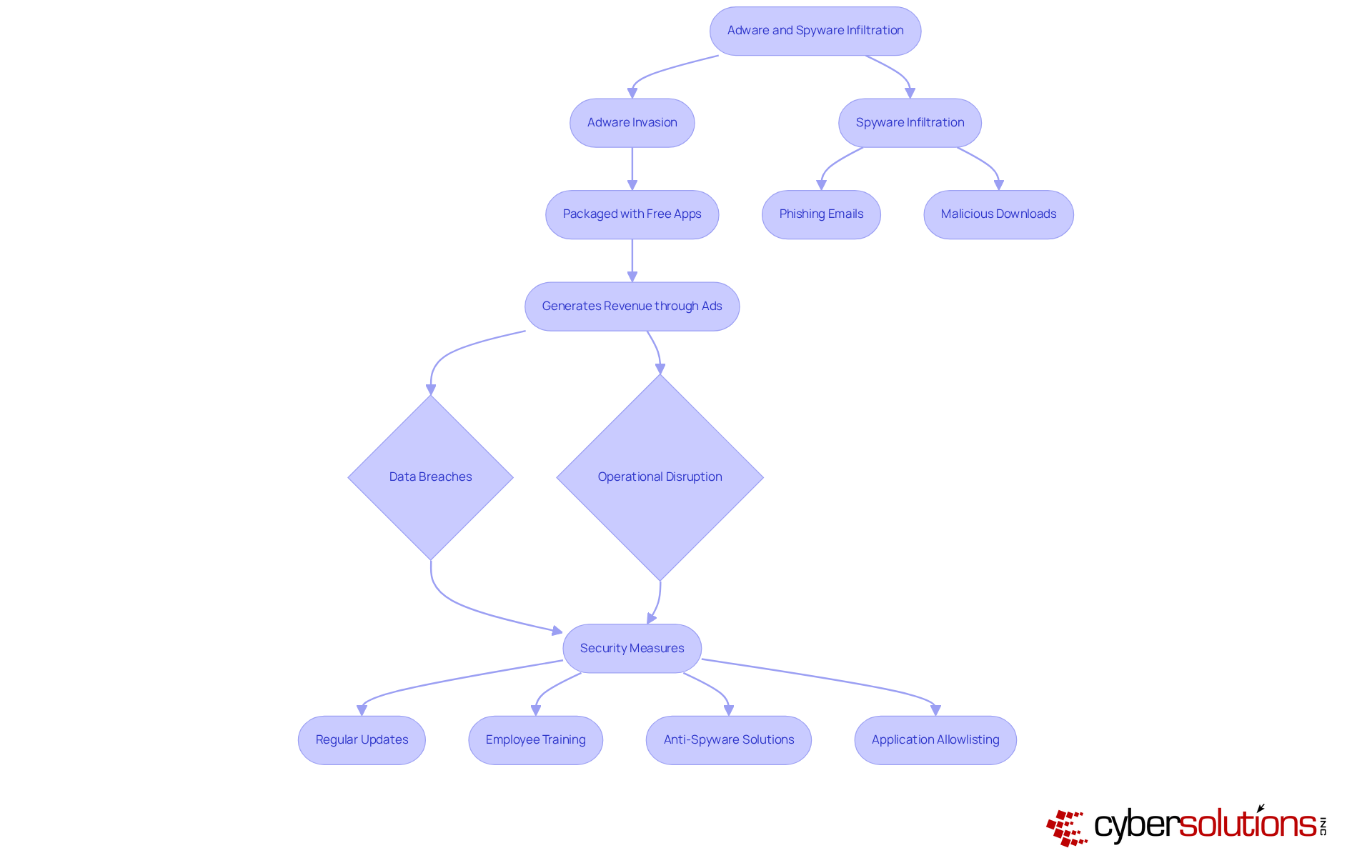
In an era where cyber threats loom large, safeguarding healthcare organizations against threats such as adware and spyware is not just a necessity; it's a critical imperative for survival. To effectively protect your business, consider implementing the following best practices:
By adopting these strategies, organizations not only protect their data but also fortify their reputation and trustworthiness in an increasingly digital world.

In an era where cyber threats loom large, the impact of adware and spyware on business operations should not be underestimated.
Operational disruption can occur as both adware and spyware significantly hinder system performance, resulting in decreased productivity and heightened frustration among employees. This disruption doesn’t just slow things down; it can hit the bottom line hard. With a staggering 32% rise in cyberattacks reported in 2025, can organizations afford to ignore the need for robust cybersecurity measures? Application allowlisting serves as a frontline defense, blocking unauthorized software and significantly reducing the risk of malware disruptions. Continuous monitoring further enhances this defense by detecting and blocking unauthorized attempts in real-time.
By recognizing these impacts, businesses can better prioritize their cybersecurity initiatives and allocate resources effectively to mitigate the risks associated with adware and spyware, while utilizing solutions such as application allowlisting to enhance their overall security posture. By prioritizing cybersecurity measures like application allowlisting, organizations can not only protect their assets but also secure their future in an increasingly digital landscape.

In an era where digital threats are ever-evolving, understanding the distinct challenges posed by adware and spyware is essential for organizations committed to safeguarding sensitive information. These two forms of malware disrupt business operations in unique ways, making it vital for organizations to understand their differences. Adware primarily generates revenue through intrusive advertisements, while spyware covertly collects sensitive data, posing significant privacy risks. By recognizing these differences, businesses can adopt targeted strategies to effectively mitigate their impact.
The insights shared in this article underscore the critical need for proactive cybersecurity measures. By implementing practices such as:
organizations can significantly reduce their vulnerability to these threats. Moreover, the financial implications of data breaches and the compliance risks associated with adware and spyware highlight the necessity of robust security protocols to safeguard assets and uphold regulatory standards.
By prioritizing cybersecurity, organizations not only protect their data but also fortify the trust that is vital for their long-term success. Taking decisive action against adware and spyware enables organizations to navigate the complex digital landscape with confidence, securing their future against evolving cyber threats. Investing in comprehensive security strategies today will pave the way for a more resilient tomorrow.
What is adware?
Adware is a type of software designed to display advertisements on a device, often through pop-ups or banners. While some adware can be benign, it typically slows down system performance and can redirect users to harmful websites.
What is spyware?
Spyware, also known as surveillance software, is malicious code that operates covertly to monitor user activity and collect sensitive information without consent. It can track browsing habits, capture keystrokes, and access personal data, posing significant privacy risks.
How do adware and spyware differ?
The primary difference is their purpose: adware displays advertisements and can slow down system performance, while spyware secretly monitors user activity and collects sensitive information, posing serious privacy and security threats.
Why is understanding adware and spyware important for organizations?
Understanding the differences between adware and spyware is crucial for organizations to strengthen their cybersecurity efforts and protect sensitive information from potential threats.
What are the risks associated with adware and spyware?
Adware can lead to exposure to more serious malware and disrupt system performance, while spyware poses significant privacy risks by stealing financial or personal information.
What proactive measures can organizations take to safeguard against malware?
Organizations can implement application allowlisting to prevent unauthorized applications, including malicious software, from running on their systems, thus reducing their attack surface.
How can Cyber Solutions assist organizations with malware threats?
Cyber Solutions offers expert malware removal and system reconstruction services to ensure that compromised endpoints are cleaned, patched, and fortified against future attacks.
What is the significance of maintaining strong cybersecurity measures?
Prioritizing cybersecurity helps organizations protect their data, maintain trust and integrity in their operations, and comply with regulations like HIPAA and GDPR.