
In an era where cyberattacks are escalating, the urgency for robust cybersecurity measures in healthcare cannot be overstated, especially for organizations handling Controlled Unclassified Information (CUI). The CMMC Level 2 assessment serves as a pivotal framework for enhancing compliance and fortifying defenses against evolving threats.
Organizations often find themselves overwhelmed by the intricate requirements of the CMMC Level 2 assessment. Failure to effectively navigate these requirements can lead to significant compliance gaps and increased exposure to cyber threats.
How can they not only achieve compliance but also strengthen their cybersecurity posture?
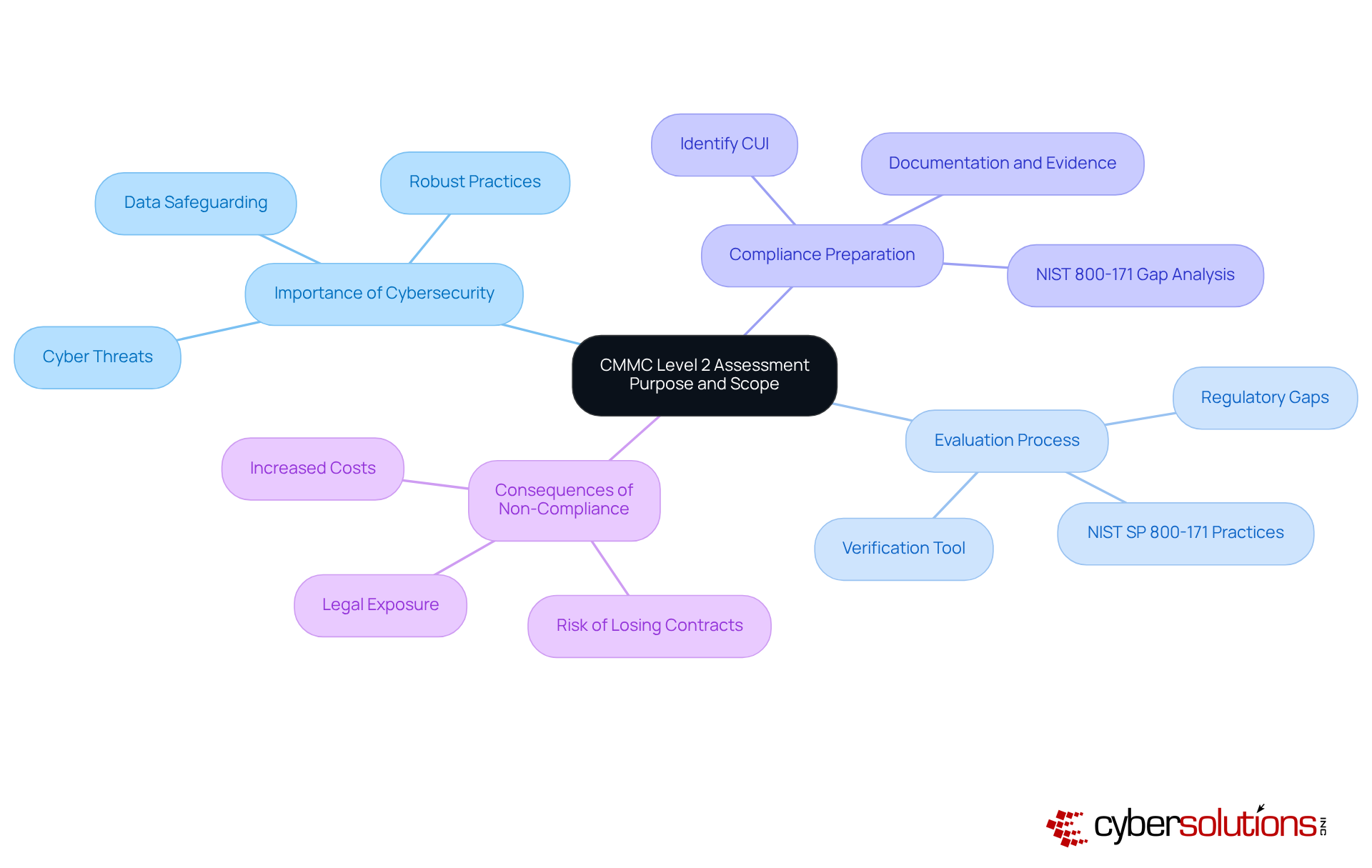
In an era where cyber threats are escalating, the importance of robust cybersecurity in healthcare cannot be overstated. The CMMC assessment guide level 2 evaluation is essential for organizations managing Controlled Unclassified Information (CUI), as it requires the implementation of advanced cybersecurity practices. Building on the foundational requirements of Level 1, this level emphasizes enhanced cyber hygiene and the safeguarding of sensitive data.
Organizations often struggle to keep pace with the evolving landscape of cybersecurity threats, risking their compliance and security. The evaluation functions not only as a verification tool for adherence but also as a method to strengthen their overall security stance, improving resilience against these threats. This evaluation dives deep into current security measures, pinpointing regulatory gaps and ensuring all 110 practices from NIST SP 800-171 are effectively executed.
By grasping the aim and extent of the CMMC assessment guide level 2, entities can strategically prepare for compliance, ensuring that their cybersecurity efforts align with regulatory standards and enhance their operational integrity. As compliance requirements tighten, organizations that fail to adapt may find themselves vulnerable to significant risks and penalties. This proactive approach is crucial, particularly as the need for compliance grows in 2026, making it vital for companies to prioritize their cybersecurity frameworks. Ignoring these evolving standards could leave organizations exposed to risks that compromise not only their data but also their reputation and operational viability.
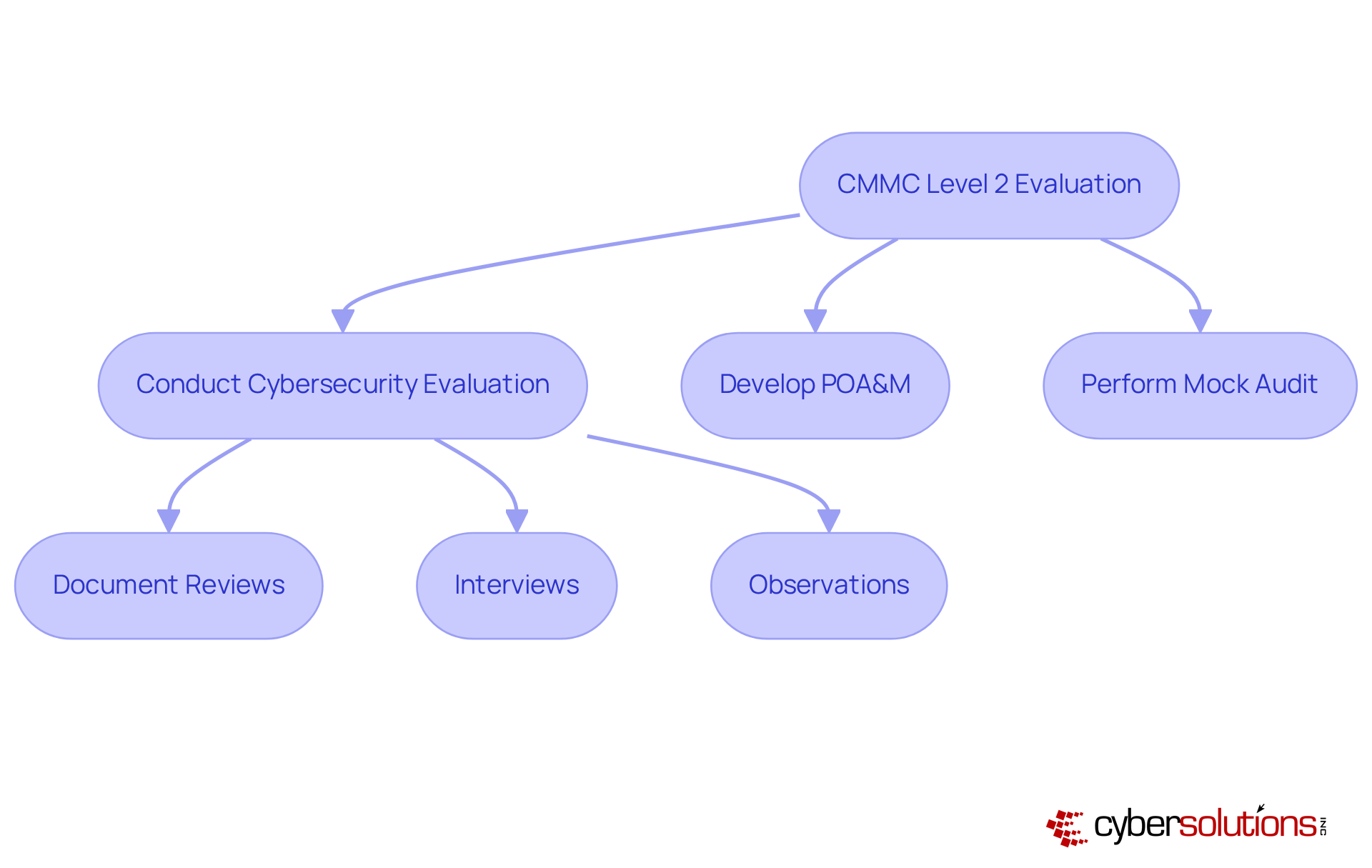
Navigating the complexities outlined in the CMMC assessment guide level 2 evaluation is crucial for organizations aiming for compliance in today's cybersecurity landscape. To successfully navigate this evaluation, organizations must familiarize themselves with the specific criteria and methodology used during the process. Central to this evaluation are the 110 security controls from NIST SP 800-171, which address critical areas such as access control, incident response, and risk evaluation.
It’s essential for organizations to conduct a thorough cybersecurity evaluation and gap analysis to pinpoint existing controls and areas for improvement. This analysis is vital, as it allows organizations to prioritize remediation efforts effectively with tailored strategies, including policy updates and system upgrades.
The evaluation approach typically involves:
Organizations should also develop a Plan of Action and Milestones (POA&M) to document known gaps and the steps to remediate them, which is crucial for preparing for CMMC compliance. Furthermore, performing a mock audit can assist in guaranteeing preparedness for the official evaluation.
Failing to prepare adequately can result in costly delays and setbacks in achieving compliance. By understanding these elements, organizations can better manage the intricacies of Level 2 regulations and prepare for success with the expert guidance and support from Cyber Solutions as detailed in the CMMC assessment guide level 2. Understanding these elements not only streamlines the path to compliance but also fortifies an organization’s cybersecurity posture against evolving threats.
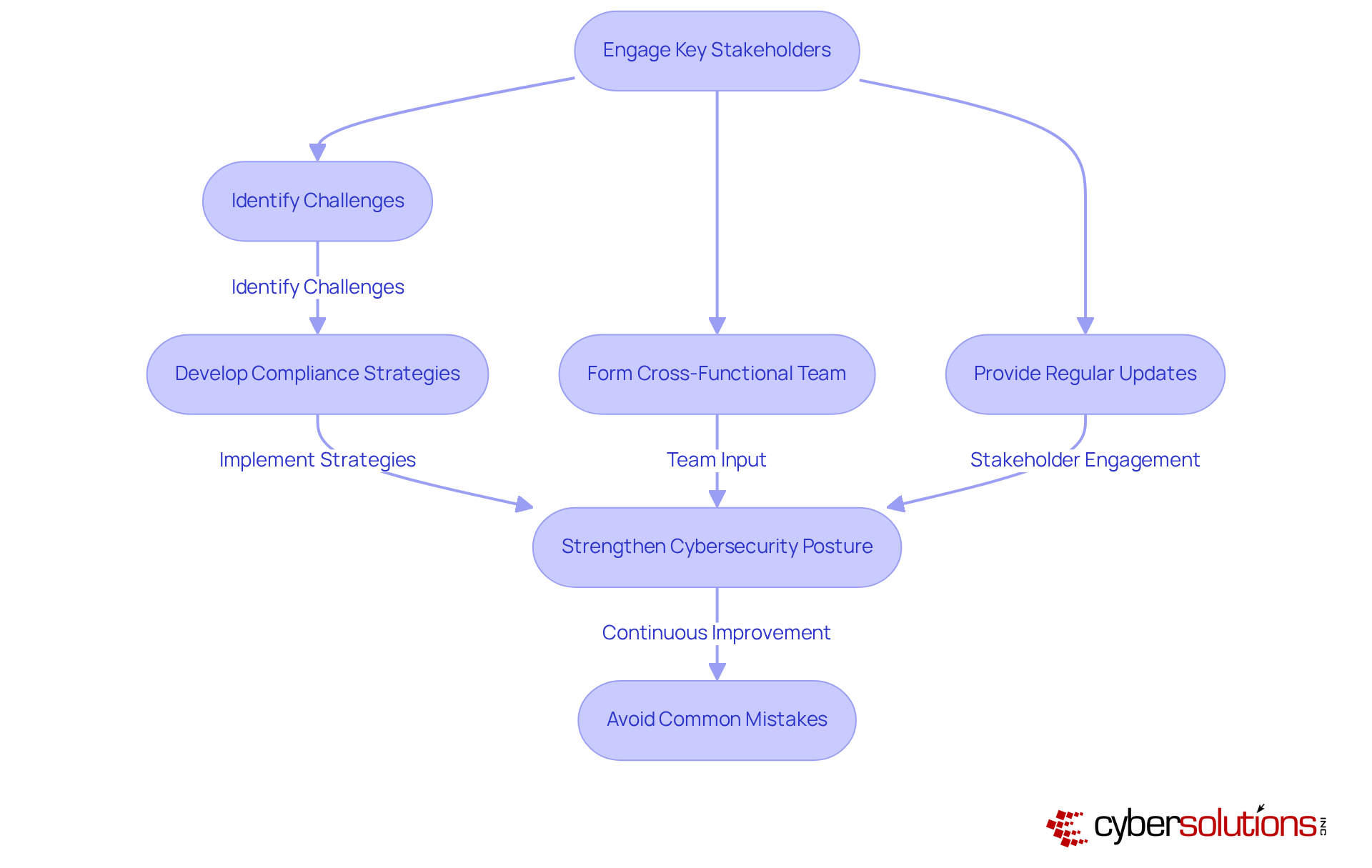
In the complex landscape of cybersecurity, the involvement of crucial stakeholders during the cmmc assessment guide level 2 evaluation process is not just beneficial; it's essential for success. Stakeholders, including IT staff, compliance officers, and executive leadership, each play a vital role in the evaluation's success.
Failing to involve key stakeholders can create misalignment and elevate risks throughout the evaluation process. Engaging these key participants allows organizations to tap into their collective knowledge. This helps identify potential challenges and develop effective compliance strategies, ultimately strengthening their cybersecurity posture.
Significantly, entities that engage key employees in stakeholder involvement enhance the chances of successful transformations by four times. With the cmmc assessment guide level 2 requirements set to take effect by 2026, prompt involvement is essential to prevent operational interruptions and possible loss of contracts. Ignoring the importance of stakeholder engagement could jeopardize compliance efforts and lead to significant operational disruptions.
Furthermore, entities should be aware of typical traps, like viewing compliance as a mere checklist task or postponing readiness until deadlines near, as these can obstruct the efficiency of the evaluation process.
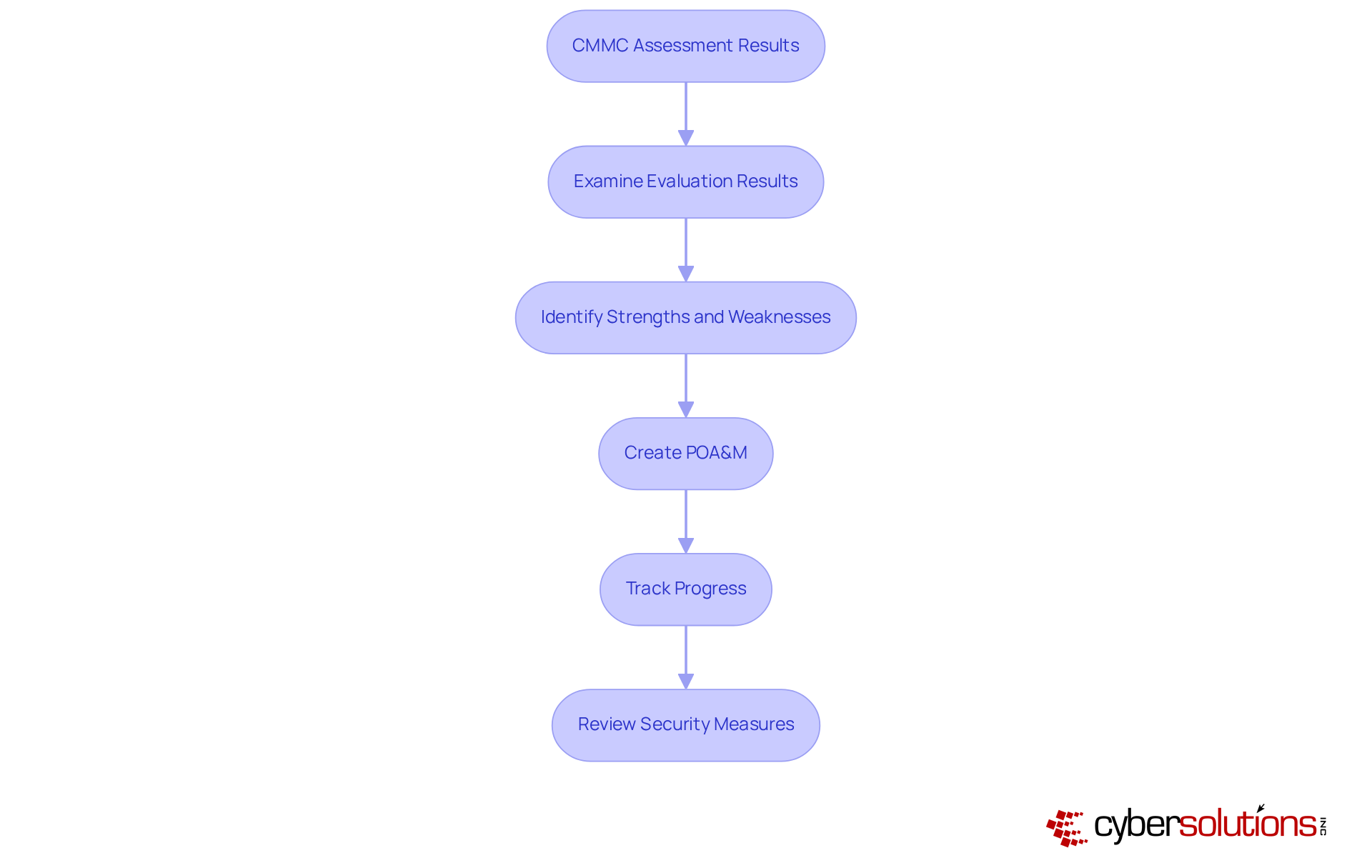
In an era where cyber threats are constantly evolving, healthcare organizations must prioritize robust cybersecurity measures to safeguard sensitive data. After concluding the CMMC assessment guide level 2 evaluation, organizations should utilize the results to drive continuous improvements in their cybersecurity practices.
Start by thoroughly examining the evaluation results to pinpoint strengths and weaknesses in your current security measures. Creating a Plan of Action and Milestones (POA&M) is essential for tackling any identified gaps and systematically tracking progress over time. Consistently reviewing and refreshing security measures in response to evaluation results is vital for adapting to changing threats and ensuring compliance.
Moreover, it's important to recognize that the framework enhances NIST 800-171 by integrating certification tiers that require third-party evaluation. Cultivating a culture of ongoing improvement allows organizations to bolster their cybersecurity posture and achieve long-term resilience against cyber threats.
Data indicates that organizations with fewer open POA&M items tend to be better prepared for certification, underscoring the effectiveness of a well-organized POA&M in enhancing compliance efforts. Additionally, utilizing Compliance as a Service (CaaS) can provide organizations with comprehensive solutions for audit preparation and ongoing regulatory management, including assessments, policy development, and monitoring, ensuring alignment with CMMC standards.
As one expert noted, "The most effective strategy isn’t to push requirements onto a POA&M. It’s to focus on building a compliance program that’s assessment-ready from the start.
In an era where cyber threats loom larger than ever, mastering the CMMC Assessment Guide Level 2 is not just important - it's essential for organizations handling Controlled Unclassified Information (CUI). By understanding the assessment's purpose and scope, businesses can effectively align their cybersecurity measures with regulatory standards and enhance their operational integrity. This proactive approach not only mitigates risks but also fortifies defenses against potential cyber threats.
Throughout this article, we've explored key insights, including:
Organizations must conduct thorough evaluations, prioritize remediation efforts, and foster collaboration among IT staff, compliance officers, and executive leadership to ensure a successful assessment journey. Ignoring these elements can lead to significant compliance challenges and operational disruptions.
Ultimately, embracing the CMMC Level 2 assessment as a continuous journey empowers organizations to not only protect sensitive data but also to thrive in a digital landscape fraught with challenges. By actively engaging in continuous improvement and leveraging compliance resources, businesses can navigate the complexities of cybersecurity and secure their future.
What is the purpose of the CMMC Level 2 assessment?
The purpose of the CMMC Level 2 assessment is to evaluate organizations managing Controlled Unclassified Information (CUI) by requiring the implementation of advanced cybersecurity practices to enhance cyber hygiene and safeguard sensitive data.
How does CMMC Level 2 differ from Level 1?
CMMC Level 2 builds on the foundational requirements of Level 1 by emphasizing enhanced cybersecurity practices and the safeguarding of sensitive data, requiring organizations to implement all 110 practices from NIST SP 800-171.
Why is the CMMC Level 2 evaluation important for organizations?
The CMMC Level 2 evaluation is important because it serves as a verification tool for adherence to cybersecurity standards and helps organizations strengthen their overall security posture, improving resilience against evolving cyber threats.
What challenges do organizations face regarding cybersecurity compliance?
Organizations often struggle to keep pace with the evolving landscape of cybersecurity threats, which can jeopardize their compliance and security efforts.
What does the CMMC Level 2 assessment evaluate?
The assessment evaluates current security measures, identifies regulatory gaps, and ensures that all 110 practices from NIST SP 800-171 are effectively executed.
How can organizations prepare for compliance with CMMC Level 2?
By understanding the aim and scope of the CMMC Level 2 assessment, organizations can strategically prepare for compliance, ensuring their cybersecurity efforts align with regulatory standards and enhance their operational integrity.
What are the consequences of failing to adapt to CMMC compliance requirements?
Organizations that fail to adapt may become vulnerable to significant risks and penalties, compromising their data, reputation, and operational viability.
Why is it crucial for organizations to prioritize their cybersecurity frameworks?
It is crucial to prioritize cybersecurity frameworks as compliance requirements are tightening, particularly with the growing need for compliance by 2026, to avoid exposure to risks and ensure operational integrity.