
As cybercriminals evolve their tactics, the urgency for effective cybersecurity in healthcare has never been more pressing. This reality highlights the urgent need for businesses to implement strong anti-phishing software that not only safeguards sensitive information but also strengthens organizational integrity against escalating cyber threats.
With countless anti-phishing solutions available, how can organizations navigate this overwhelming landscape? Choosing the wrong software could leave organizations exposed to devastating breaches.
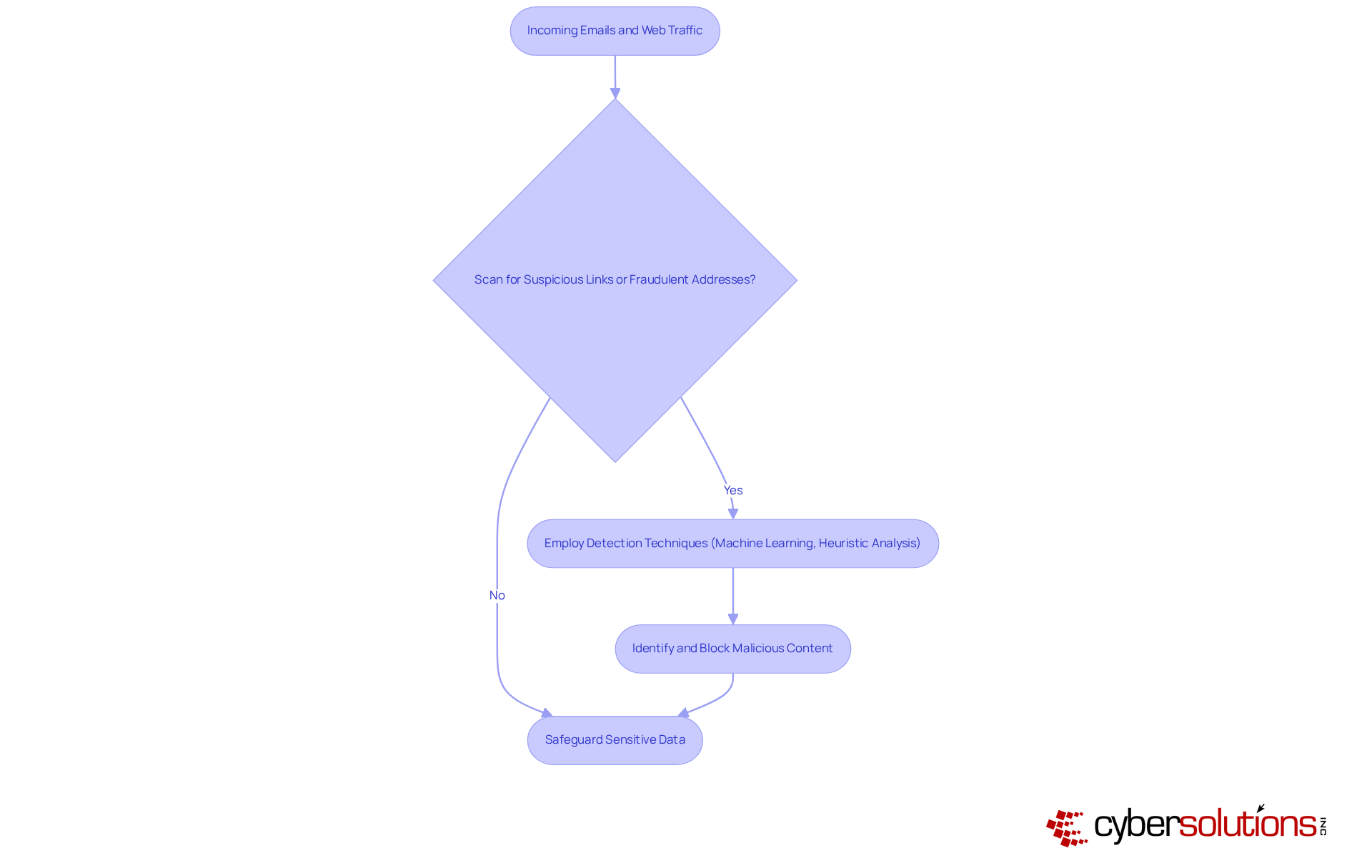
In an era where cybercriminals are constantly devising new tactics, the need for robust anti-fraud software has never been more critical. This software actively scans incoming emails and web traffic, hunting for signs of scam attempts, like suspicious links or fraudulent sender addresses. By employing advanced detection techniques, such as machine learning algorithms and heuristic analysis, anti-phishing software can identify and block malicious content before it reaches the user, safeguarding sensitive data and maintaining organizational integrity.
With fraudulent attacks happening every 30 seconds, the stakes have never been higher for organizations to protect their sensitive data. For instance, Microsoft Defender for Office 365 offers features like Zero-hour auto purge (ZAP), which retroactively isolates harmful emails based on newly obtained intelligence, enhancing user protection.
Furthermore, organizations employing anti-fraud software have noted considerable decreases in successful scams, with financial services achieving a 74% success rate in training against such risks. Without these essential tools, organizations leave themselves vulnerable to devastating cyber threats that could compromise their very existence.
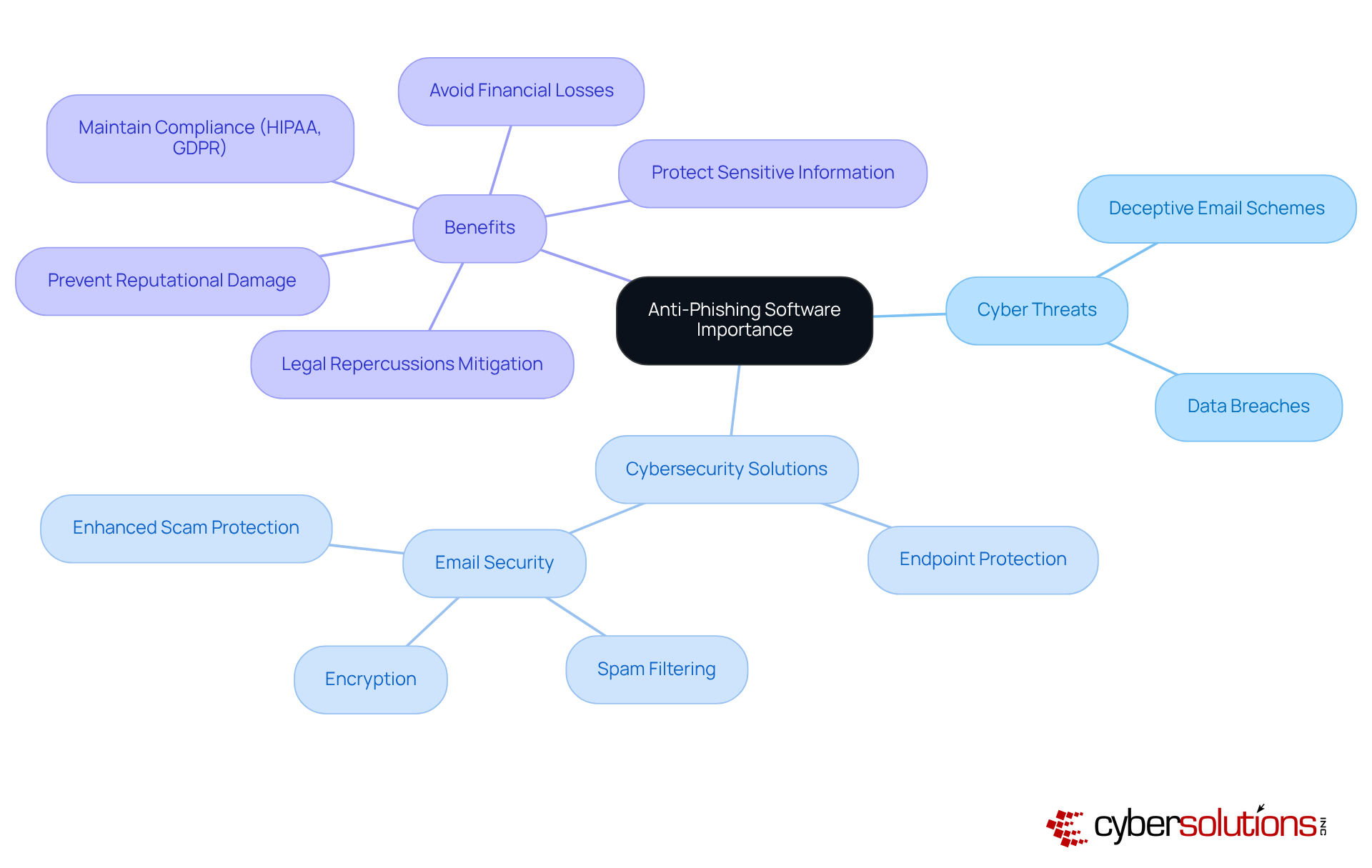
As cyber threats evolve, companies risk falling victim to devastating breaches, making cybersecurity a top priority in healthcare. Deceptive email schemes have emerged as one of the most common types of cybercrime, with online scams accounting for over 90% of data breaches. This alarming statistic underscores the need for companies to establish effective defenses. At Cyber Solutions, we provide advanced cybersecurity solutions, including:
These solutions are essential for businesses of all sizes. They not only protect sensitive information but also help maintain compliance with industry regulations such as HIPAA and GDPR.
Our Email Support & Security services encompass:
This ensures that your email communication remains secure and efficient. By preventing data breaches, organizations can avoid significant financial losses, reputational damage, and legal repercussions. Investing in robust cybersecurity measures is not just a choice; it's a necessity for survival, complemented by our 24/7 threat monitoring to proactively safeguard against ransomware and fraud attacks.
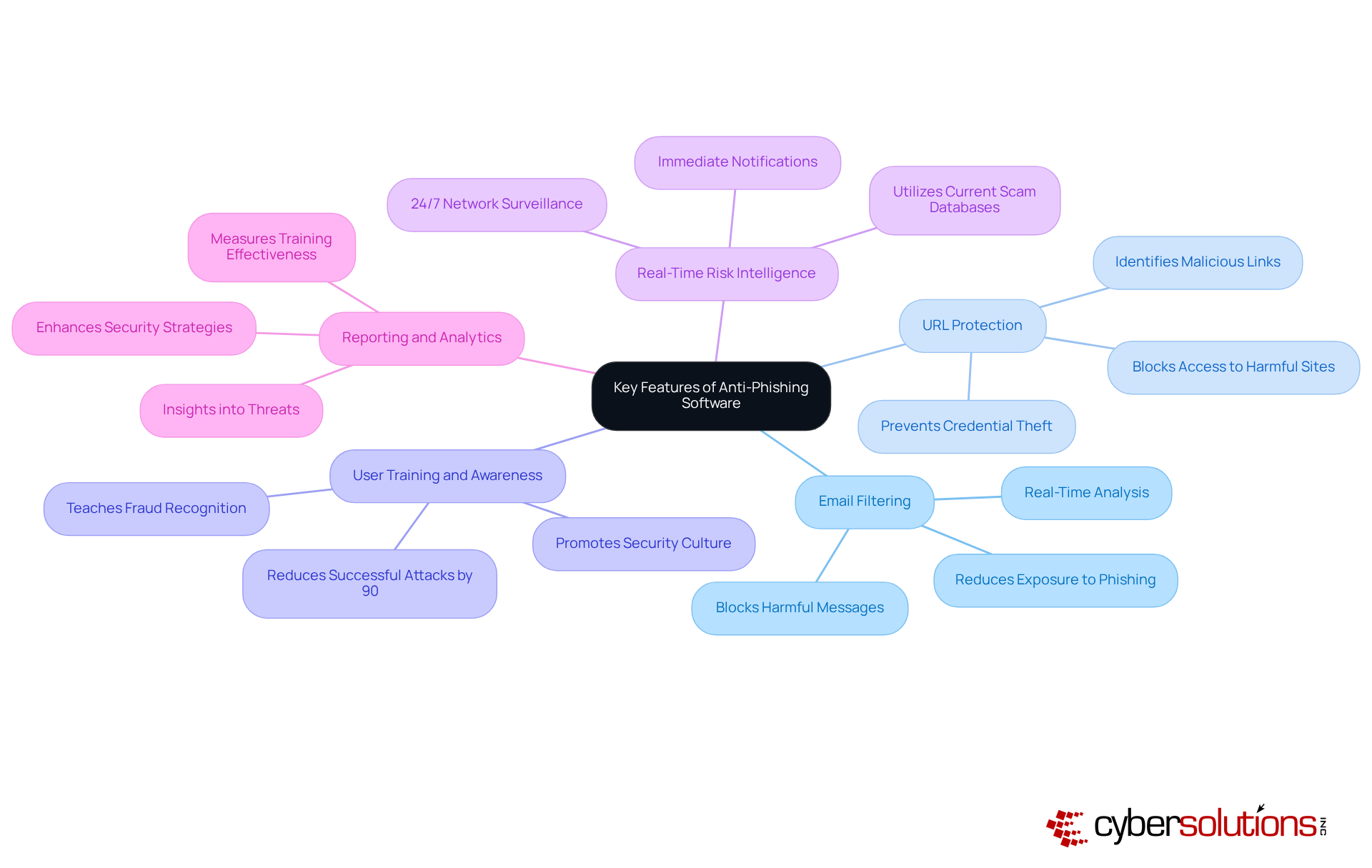
In an era where cyber threats loom large, the healthcare sector faces unprecedented challenges that demand immediate attention and robust solutions. Effective anti-phishing software encompasses several essential features that bolster an organization's defenses against cyber threats:
By investing in comprehensive solutions, healthcare organizations can understand what anti-phishing software is, allowing them to safeguard sensitive information and fortify their overall cybersecurity posture against evolving threats.
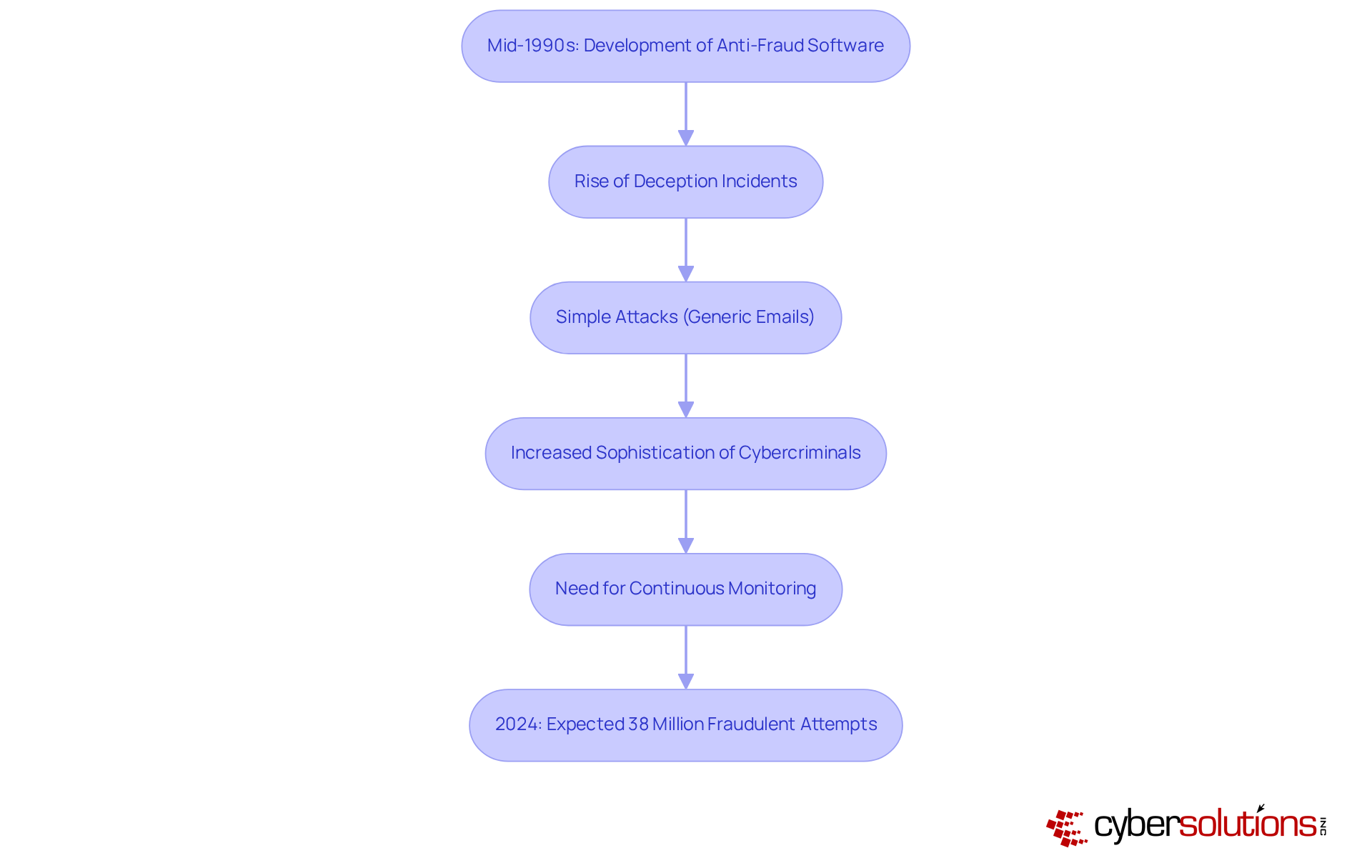
In an era where cyber threats are increasingly sophisticated, the healthcare sector faces unprecedented challenges in safeguarding sensitive information. The development of anti-fraud software began in the mid-1990s, coinciding with a rise in deception incidents. Initially, these attacks were straightforward, often involving generic emails sent to large user groups. However, as cybercriminals became more sophisticated, organizations struggled to keep pace with evolving threats. This evolution showcases what is anti phishing software, as it enables modern tools to recognize known threats and adapt in real-time to new phishing tactics, ensuring that organizations are prepared to defend against the ever-changing landscape of cyber risks.
Continuous monitoring is crucial; it helps catch suspicious activities before they turn into serious threats. Phishing incidents accounted for a quarter of all cybersecurity occurrences worldwide, underscoring the urgent need to understand what is anti phishing software. In 2024, more than 38 million fraudulent attempts are expected to be identified globally, emphasizing the necessity for organizations to establish strong protections. By leveraging cutting-edge threat intelligence and 24/7 threat monitoring, Cyber Solutions empowers businesses to defend against ransomware, phishing, and other malware attacks. Investing in advanced cybersecurity solutions is not just a precaution; it's a necessity for survival in today's digital landscape.
In an era where cyber threats are increasingly sophisticated, the importance of anti-phishing software cannot be overstated. This software acts as a crucial defense, spotting and stopping phishing attempts before they cause damage. By leveraging advanced detection techniques and real-time monitoring, businesses can protect sensitive information, ensuring both operational integrity and compliance with industry regulations.
Throughout this discussion, we’ve uncovered key insights into the functionality and benefits of anti-phishing software. Features such as email filtering, URL protection, and user training play vital roles in strengthening an organization’s defenses. With phishing attacks on the rise, businesses face an escalating threat that demands immediate attention. Organizations that adopt comprehensive anti-phishing solutions can significantly reduce their risk of falling victim to costly breaches.
Taking action now to implement anti-phishing software is crucial for protecting your organization’s future. As cyber threats continue to grow in complexity and frequency, businesses must prioritize their cybersecurity posture. Investing in robust anti-fraud measures will not only safeguard sensitive data but also foster a culture of security awareness that empowers employees and enhances overall resilience against cyber threats.
What is anti-phishing software?
Anti-phishing software is a type of security tool that scans incoming emails and web traffic for signs of scam attempts, such as suspicious links or fraudulent sender addresses, to protect sensitive data.
How does anti-phishing software work?
It employs advanced detection techniques, including machine learning algorithms and heuristic analysis, to identify and block malicious content before it reaches the user.
Why is anti-phishing software important?
It is crucial because cybercriminals are constantly developing new tactics, and the software helps safeguard sensitive data and maintain organizational integrity by preventing successful phishing attacks.
How often do fraudulent attacks occur?
Fraudulent attacks happen every 30 seconds, highlighting the urgent need for organizations to protect their sensitive data.
Can you provide an example of anti-phishing software?
Microsoft Defender for Office 365 is an example, featuring capabilities like Zero-hour auto purge (ZAP), which retroactively isolates harmful emails based on newly obtained intelligence.
What impact does anti-fraud software have on organizations?
Organizations using anti-fraud software have reported significant decreases in successful scams, with financial services achieving a 74% success rate in training against phishing risks.
What risks do organizations face without anti-phishing software?
Without these tools, organizations are vulnerable to devastating cyber threats that could compromise their existence and sensitive information.