Introduction
In today's healthcare landscape, the stakes are higher than ever: cyber threats loom large, threatening not just data but the very essence of operational continuity. For CFOs in healthcare, grasping the critical nature of data backup isn't just important - it's a necessity to protect vital information and ensure resilience against potential crises.
Imagine the fallout when a healthcare organization overlooks a robust backup strategy - financial losses, reputational damage, and a crisis of trust can ensue. The repercussions are severe, prompting the question: how can healthcare organizations not only navigate these risks but also fortify their defenses to ensure data security?
Define Data Backup and Its Role in Cybersecurity
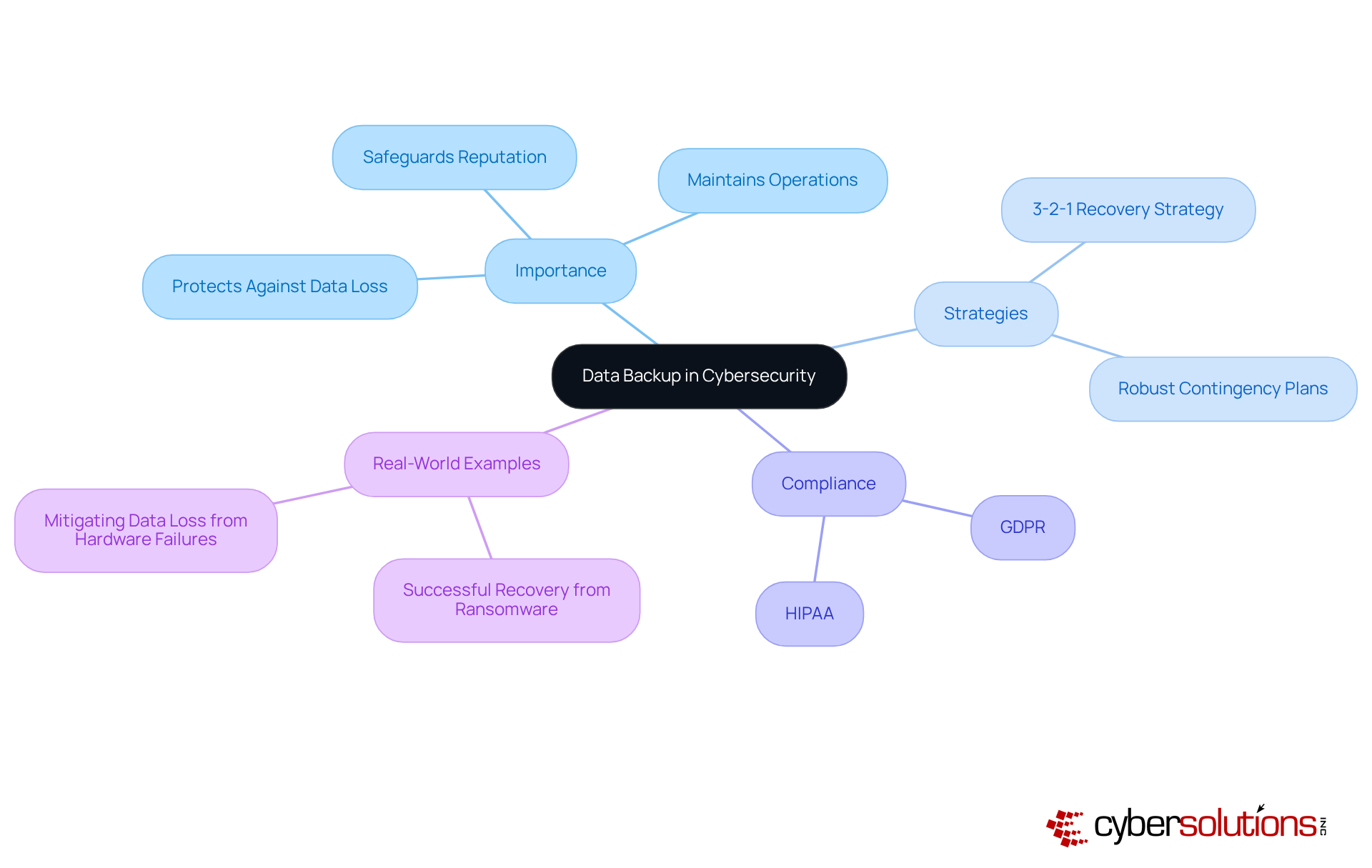
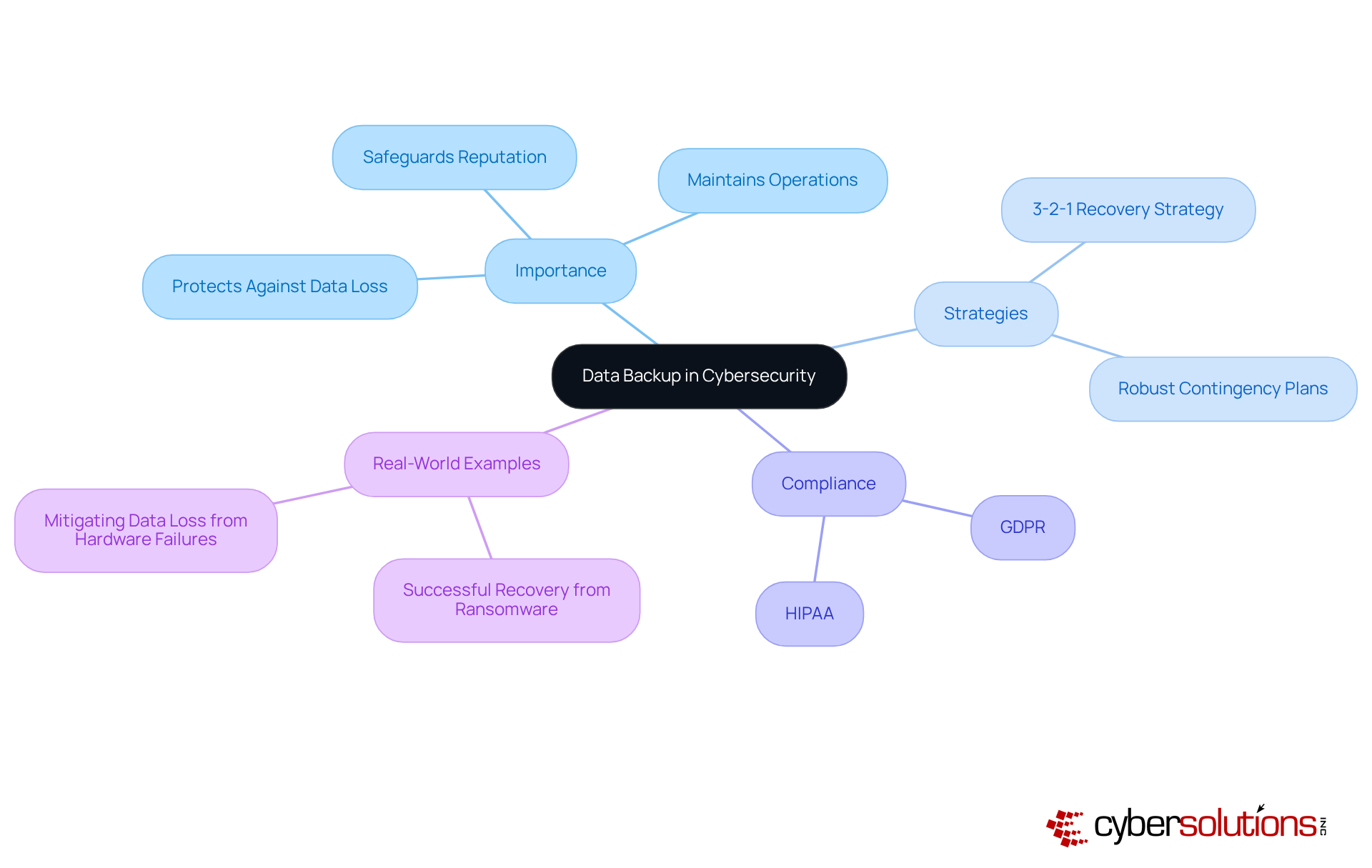
In an era where data breaches are rampant, safeguarding information is not just a precaution; it's a necessity for survival in the healthcare sector. To protect against various threats like hardware failures and cyberattacks, it is crucial to explain the importance of data backup by creating copies of information. In cybersecurity, this practice is essential to explain the importance of data backup as a crucial part of a comprehensive security plan, enabling businesses to retrieve vital information and maintain operations during breaches or system failures.
A well-organized information preservation plan can help explain the importance of data backup, as it not only reduces the risk of loss but also aids organizations in complying with industry regulations such as HIPAA and GDPR, which mandate the safeguarding of sensitive information. For instance, organizations that adopt the 3-2-1 recovery strategy - maintaining three copies of information on two distinct devices, with one copy kept off-site - can significantly enhance their resilience against information loss incidents.
Did you know that nearly 30% of computers in the U.S. fall victim to malware? This stark reality underscores the need for robust recovery solutions. To mitigate the severe impact of information loss, it is essential to explain the importance of data backup to avoid lost clients, revenue, and trust, as well as potential fines and reputational damage. Organizations must explain the importance of data backup, as without a solid recovery strategy, they face dire consequences. A robust contingency plan can explain the importance of data backup by acting as a safety net, allowing companies to recover swiftly from incidents without yielding to ransom requests.
Real-world examples illustrate the effectiveness of information recovery strategies. Companies that faced ransomware attacks were able to recover their systems and information from validated reserves, minimizing downtime and operational disruption. This really highlights how crucial information preservation is to explain the importance of data backup for ensuring that organizations can continue to operate smoothly in the face of evolving cyber threats.
Ultimately, recognizing the strategic significance of data preservation allows organizations to explain the importance of data backup, enabling them to improve their cybersecurity stance and tackle challenges while sustaining operational integrity. Organizations not only protect their assets and fortify their reputation in an increasingly digital world, but they also need to explain the importance of data backup by prioritizing data preservation.
Explore Different Types of Data Backups
In an era where cyber threats loom large, the healthcare sector must prioritize robust data protection strategies to safeguard sensitive information and maintain operational integrity. To enhance business resilience, organizations must explain the importance of data backup and understand the various types of data storage copies to select the appropriate strategy. Here are the primary backup methods:
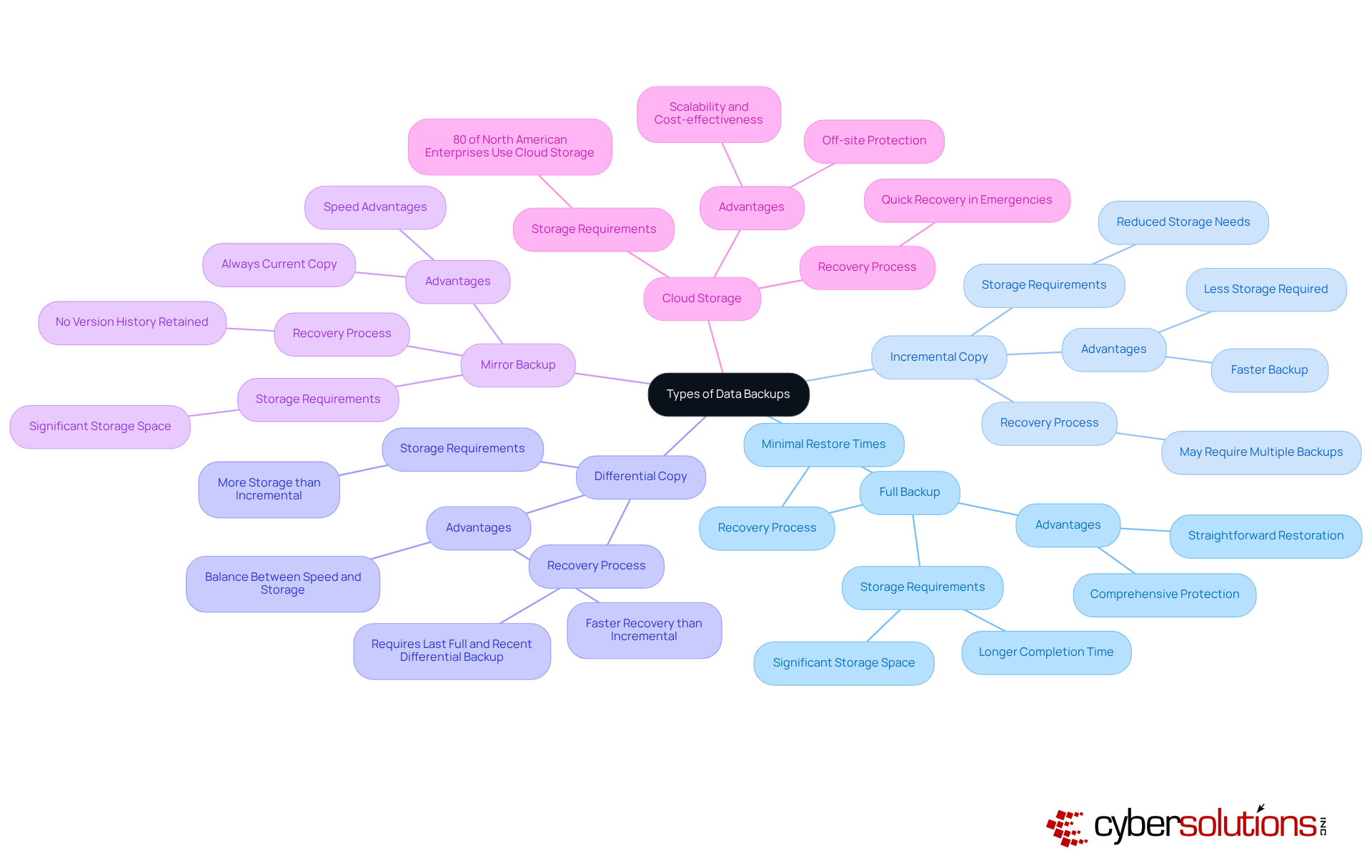
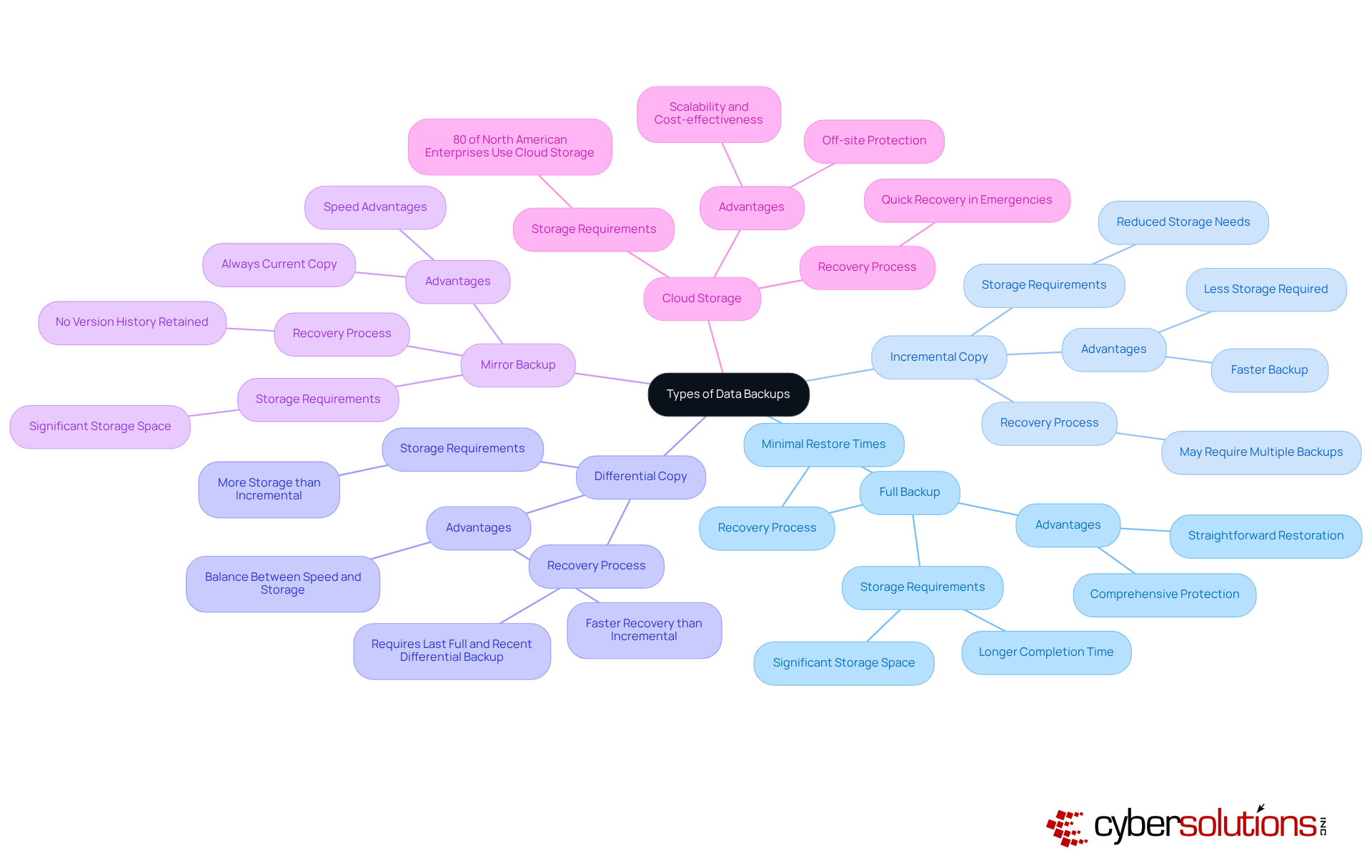
- Full Backup: This method creates a complete copy of all selected information at a specific point in time. While it offers comprehensive protection, it demands significant storage space and time to complete. IT specialists often note that although complete data copies are resource-intensive, they provide a straightforward restoration process, which is vital in the event of a ransomware attack.
- Incremental Copy: This method saves only the information that has changed since the previous copy, whether it was a complete or incremental one. It is faster and requires less storage, making it a favored choice for businesses managing large datasets. Incremental copies can significantly reduce storage periods, allowing for more frequent updates without overwhelming resources, which is crucial for maintaining operational continuity during incidents.
- Differential Copy: Similar to incremental copies, differential copies store changes made since the last complete copy. This method strikes a balance between speed and storage efficiency, requiring more storage than incremental methods but less than full backups. It allows for faster recovery than incremental saves since only the last complete save and the most recent differential save are needed for restoration, which can be essential in minimizing downtime after an attack.
- Mirror Backup: This type creates a precise duplicate of the information, ensuring that the copy is always current. However, it does not retain previous versions of files, which can be a drawback in scenarios where version history is crucial. IT managers frequently emphasize the importance of maintaining version control, particularly when handling sensitive or critical information, as losing historical records can complicate recovery efforts.
- Cloud Storage: Utilizing cloud storage for data preservation offers off-site protection and accessibility from anywhere. This method is increasingly popular due to its scalability and cost-effectiveness. With 80% of North American enterprises utilizing cloud storage, organizations benefit from features such as end-to-end encryption and multi-factor authentication, enhancing information security. The case of a small accounting firm that successfully recovered their data within hours following a ransomware attack demonstrates the efficacy of cloud storage in emergency scenarios.
As cyber threats evolve, healthcare organizations need to explain the importance of data backup while investing in comprehensive data storage solutions, as it is a necessity for ensuring their future resilience.
Establish a Backup Schedule and Best Practices
In an era where cyber threats loom large, the integrity of healthcare data is paramount, making robust cybersecurity measures non-negotiable for CFOs. To ensure effective data backup, businesses should establish a regular backup schedule and adhere to best practices:
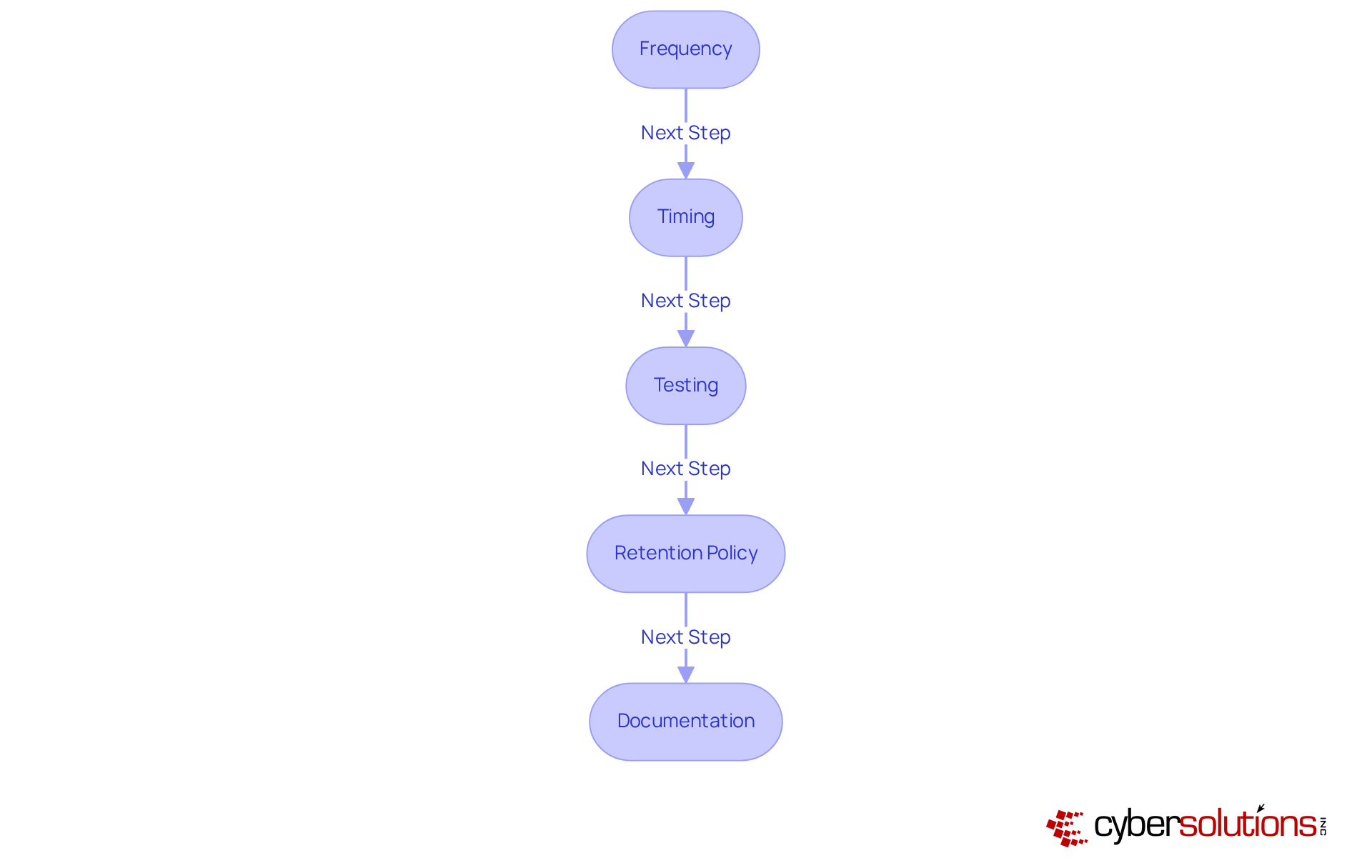
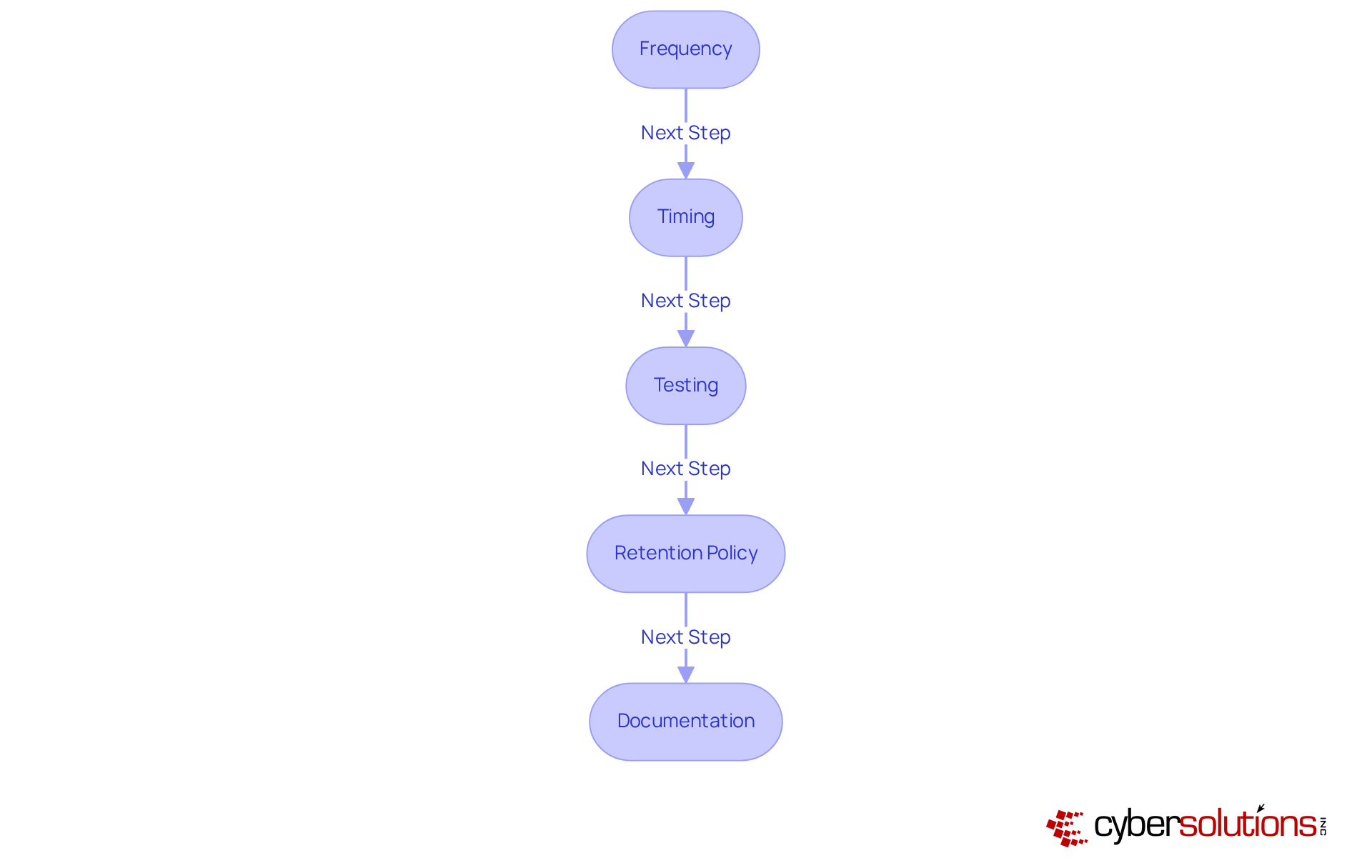
- Frequency: Establish how frequently copies should take place depending on the importance of the information. For example, mission-critical information may need daily copies, while less essential information can be stored weekly. Consistent data saves are crucial, and this situation serves to explain the importance of data backup, as 35% of companies that encountered data disruptions last year were unable to restore their lost information due to insufficient saves, malware-related corruption, and intervals between data saves.
- Timing: Arrange data saves during off-peak hours to minimize the impact on system performance. This method guarantees that data copies do not disrupt daily operations, which is vital since 37% of servers faced unexpected outages in 2023, mainly due to cyberattacks, infrastructure failures, storage hardware issues, and software problems.
- Testing: Regularly examine recovery systems to ensure information can be restored successfully. This practice assists in recognizing any issues before a loss incident happens. Executing test restores is essential, as it confirms the completeness and precision of copies, ensuring they operate as intended.
- Retention Policy: Establish a retention policy that specifies the duration for which copies should be maintained. This policy should balance storage costs with the need for historical data, ensuring that businesses can access necessary information without incurring excessive costs.
- Documentation: Maintain clear documentation of data preservation procedures, schedules, and recovery processes. This documentation is essential for training personnel and ensuring consistency in storage practices, which can significantly enhance operational efficiency.
Cyber Solutions can empower organizations to implement these optimal methods, ensuring they are well-prepared for any data loss scenario. The 3-2-1 preservation guideline, which stresses keeping three copies of information on two distinct storage types, with one copy located off-site, is a suggested framework for enhancing information safety. As Glanze Patrick mentions, "The 3‑2‑1 rule is widely considered the optimal method for practical and comprehensive protection of information." Organizations must explain the importance of data backup, as without a solid data backup strategy, they risk not just financial loss but also damage to their reputation and trustworthiness in the eyes of patients and stakeholders.
Understand the Risks of Data Loss Without Backups
In today's digital landscape, it is important to explain the importance of data backup, as failing to implement a robust strategy can jeopardize your organization's financial stability and operational integrity.
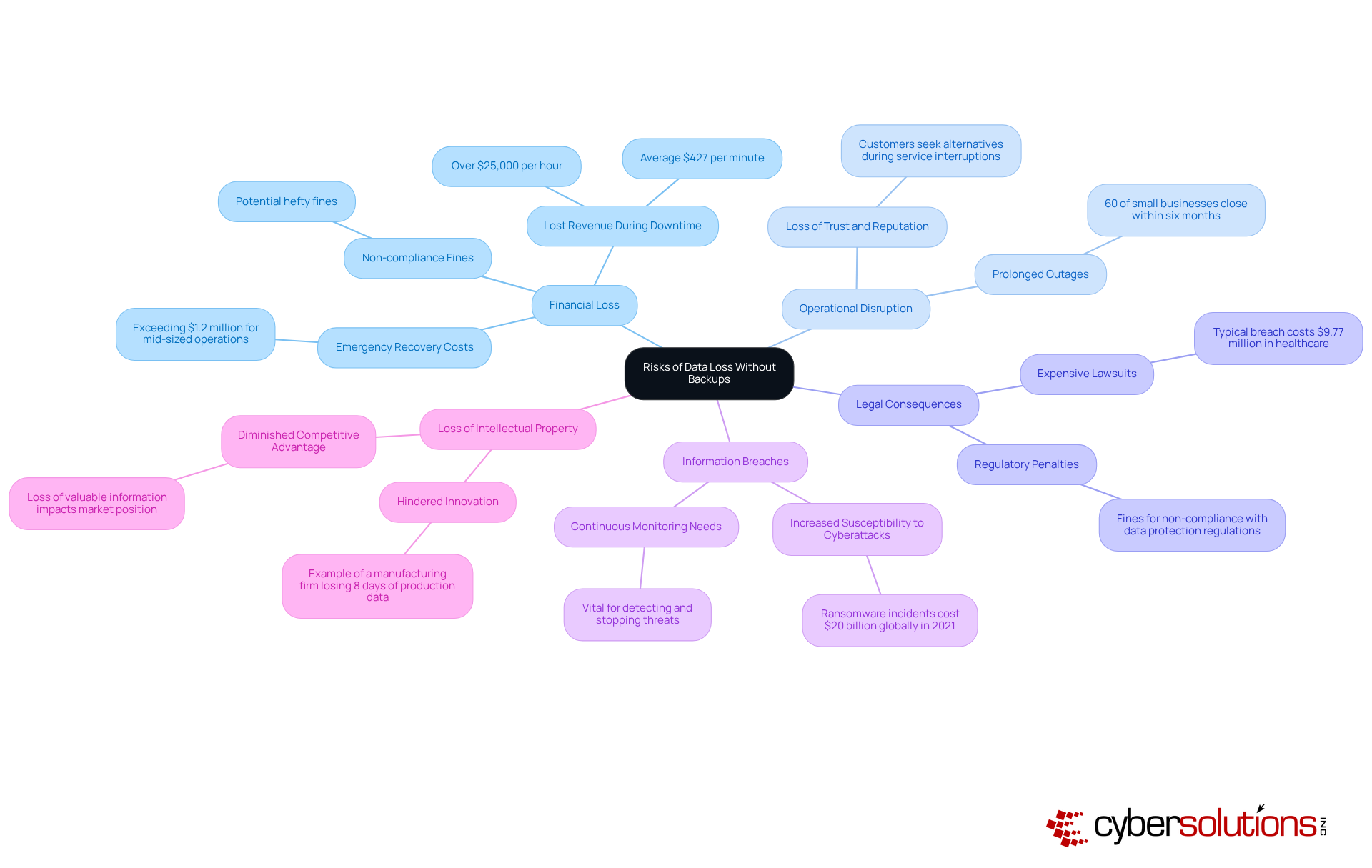
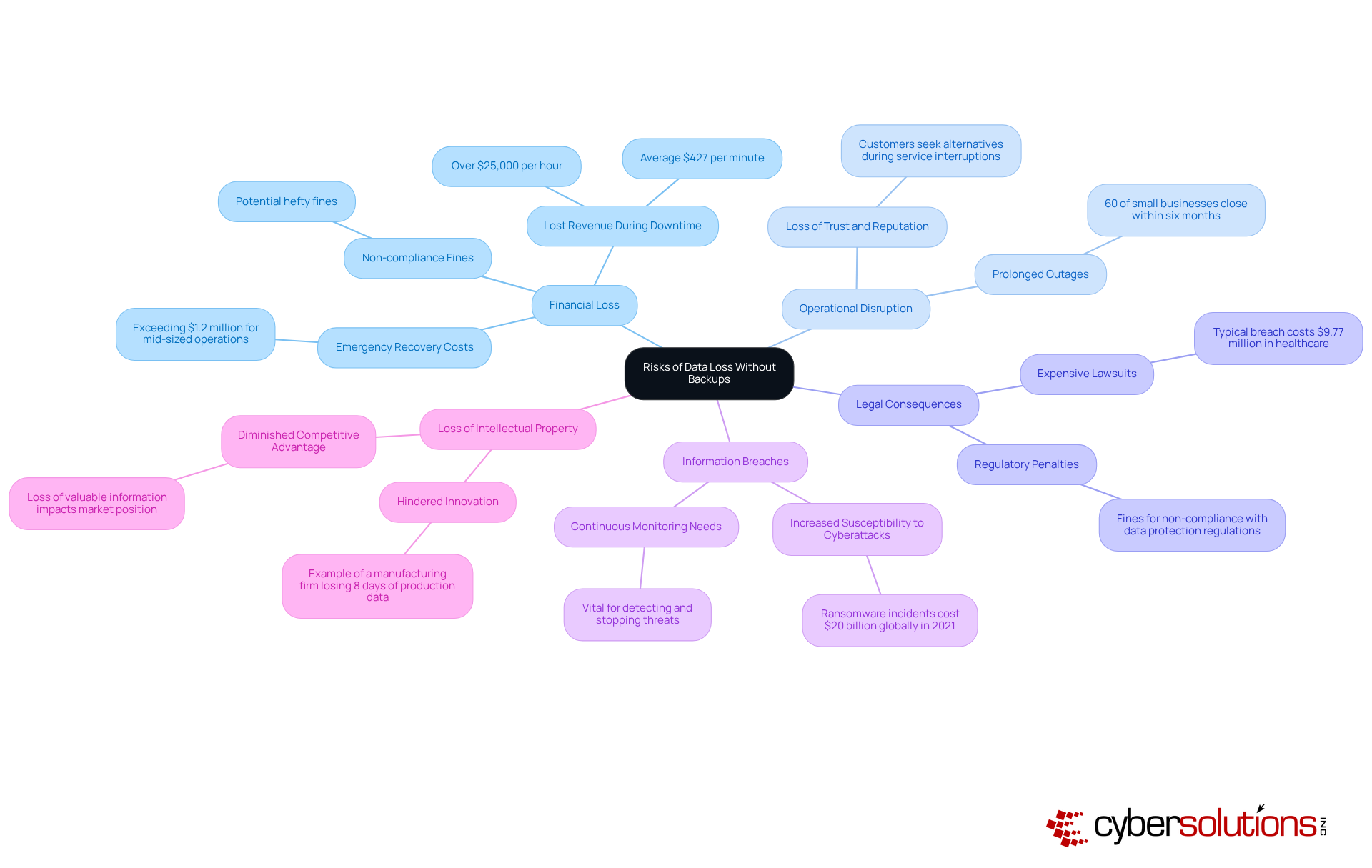
- Financial Loss: Data loss can have serious financial consequences. Businesses may experience lost revenue during downtime, averaging $427 per minute, which translates to over $25,000 per hour. Recovery efforts can also incur significant costs, with emergency response expenses often exceeding $1.2 million for mid-sized operations. Non-compliance with data protection regulations can lead to hefty fines, further straining financial resources. Rapid incident response strategies, such as having an on-site team within 24 hours, can help mitigate these financial impacts by enabling quicker recovery.
- To prevent operational disruption, organizations must explain the importance of data backup, as failure to do so may lead to prolonged outages that disrupt operations and adversely affect customer service. Did you know that 60% of small businesses that lose essential information close within six months? Such disruptions can lead to a loss of trust and reputation, as customers may seek alternatives when services are interrupted. A layered approach to cybersecurity, including endpoint isolation and user training, can enhance recovery efforts and minimize operational downtime.
- Legal Consequences: Organizations that fail to protect sensitive information may face legal actions from customers or regulatory bodies. This can lead to expensive lawsuits and fines, with the typical expense of a security breach reaching $9.77 million in the healthcare sector alone. The financial implications of legal repercussions can be devastating, especially for small businesses. Establishing efficient information storage solutions is crucial to show adherence and safeguard against legal consequences.
- Information Breaches: Insufficient backup plans can heighten susceptibility to cyberattacks, such as ransomware, where perpetrators encrypt information and request payment for its retrieval. Ransomware incidents alone incurred an estimated $20 billion worldwide in 2021, emphasizing the urgent necessity for effective information protection measures. Continuous monitoring and threat intelligence are vital in detecting and stopping suspicious activities before they escalate into serious threats.
- Loss of Intellectual Property: For many businesses, information represents valuable intellectual property. Losing this information can hinder innovation and diminish competitive advantage. A manufacturing firm in the Chicago suburbs lost eight days of production information in a ransomware attack, revealing that their recovery system hadn't finished a complete save in 11 months. Understanding these risks helps to explain the importance of data backup, as it is not just about compliance; it's about ensuring your organization's survival in an increasingly hostile cyber environment.
Conclusion
In an era where cyber threats loom larger than ever, the importance of data backup in healthcare cannot be ignored. Implementing robust data backup strategies helps organizations protect vital information. It also boosts their resilience against cyber threats and operational disruptions.
This guide explored various types of data backups, including full, incremental, differential, and cloud backups. Each type offers unique advantages tailored to different organizational needs. Establishing a regular backup schedule and adhering to best practices, such as frequent testing and maintaining clear documentation, further solidifies an organization's ability to recover swiftly from data loss incidents. The alarming statistics surrounding data loss incidents highlight the urgent need for businesses to prioritize these measures to avoid severe financial and reputational consequences.
Failing to prioritize data backup can lead to devastating financial losses and irreparable damage to reputation. In the end, committing to a solid data backup strategy goes beyond technicalities; it’s essential for business continuity and resilience. As cyber threats continue to escalate, organizations must recognize that investing in reliable data backup solutions today is not just a precaution; it’s a strategic move that can define an organization’s future success and stability. Taking proactive steps now ensures that businesses are well-prepared to navigate the challenges of tomorrow, safeguarding their assets and maintaining the trust of their clients and stakeholders.
Frequently Asked Questions
What is data backup and why is it important in cybersecurity?
Data backup involves creating copies of information to protect against data loss due to threats like hardware failures and cyberattacks. It is essential in cybersecurity as it enables businesses to retrieve vital information and maintain operations during breaches or system failures.
How does a data backup plan help organizations comply with regulations?
A well-organized data backup plan helps organizations comply with industry regulations such as HIPAA and GDPR by ensuring the safeguarding of sensitive information, thus reducing the risk of data loss and potential legal penalties.
What is the 3-2-1 recovery strategy?
The 3-2-1 recovery strategy involves maintaining three copies of information on two distinct devices, with one copy kept off-site. This approach enhances resilience against information loss incidents.
What are the risks of not having a solid data backup strategy?
Without a solid data backup strategy, organizations face severe consequences, including lost clients, revenue, trust, potential fines, and reputational damage due to information loss.
How can a contingency plan support data backup efforts?
A robust contingency plan acts as a safety net, allowing companies to recover swiftly from incidents without yielding to ransom requests, thereby minimizing downtime and operational disruption.
Can you provide examples of the effectiveness of data backup strategies?
Real-world examples show that companies facing ransomware attacks were able to recover their systems and information from validated reserves, which minimized downtime and operational disruption, highlighting the importance of data backup.
Why is recognizing the strategic significance of data preservation important for organizations?
Recognizing the strategic significance of data preservation allows organizations to improve their cybersecurity stance, tackle challenges, and sustain operational integrity while protecting their assets and reputation in a digital world.
List of Sources
- Define Data Backup and Its Role in Cybersecurity
- Data Expert Details How Cyber Resilience Starts Where Backup Strategy Ends -- Virtualization Review (https://virtualizationreview.com/articles/2026/04/data-expert-details-how-cyber-resilience-starts-where-backup-strategy-ends.aspx)
- The Critical Role of Data Backup in Cybersecurity (https://security-everywhere.com/the-critical-role-of-data-backup-in-cybersecurity)
- Data Backups: Its Importance for Cybersecurity | Morgan Stanley (https://morganstanley.com/articles/data-backup-importance-cybersecurity)
- World Backup Day Quotes from Experts for 2025 - Best Backup and Disaster Recovery Tools, Software, Solutions & Vendors (https://solutionsreview.com/backup-disaster-recovery/world-backup-day-quotes-from-experts-for-2025)
- Explore Different Types of Data Backups
- Top Data Backup and Recovery Trends to Watch in 2026 (https://godataglobal.com/blog/top-data-backup-and-recovery-trends-to-watch)
- Cloud Backup Case Studies (https://meegle.com/en_us/topics/cloud-backup/cloud-backup-case-studies)
- Different Types Of Data Backups: Differential, Mirror, Etc. (https://zmanda.com/blog/different-types-of-data-backup)
- Backup Statistics By Users, Companies, Frequency, Country And Technology Adoption (2025) (https://electroiq.com/stats/backup-statistics)
- Protecting Research Data with Cloud Backup: A University Case Study (https://backblaze.com/cloud-backup/business/case-studies/leading-research-university)
- Establish a Backup Schedule and Best Practices
- Essential Data Backup and Recovery Statistics for 2024 - TeleData Select (https://teledataselect.com/7-essential-data-backup-and-recovery-statistics-for-the-year-2024)
- How to Back Up Your Data the Right Way in 2026: 3‑2‑1 Backup Rule Explained (https://techtimes.com/articles/314910/20260303/how-back-your-data-right-way-2026-321-backup-rule-explained.htm)
- Case Study: Solving Challenges with Backup Management (https://linkedin.com/pulse/case-study-solving-challenges-backup-management-manoj-bhole-clmnf)
- Best Practices for Data Backup: Protect Your Valuable Information - I.T. Matters, Inc. (https://itmattersinc.com/best-practices-for-data-backup-protect-your-valuable-information)
- Understand the Risks of Data Loss Without Backups
- Why Real Estate Agency Requires Tech Support (https://cmitsolutions.com/tempe-az-1141/blog/cost-of-not-having-data-backup-strategy)
- The Devastating Impact of Data Loss on Small Businesses (https://fields-data-recovery.com/blog/the-devastating-impact-of-data-loss-on-small-businesses)
- The Financial Impact Of Data Loss And How To Mitigate It With DLP Policies? – Secure IT Consult (https://secureitconsult.com/data-loss-financial-impact)
- 3 Startling Statistics About Data Loss and Recovery (https://frameworkit.com/blog/startling-statistics-about-data-loss)
- Why Data Loss Really Costs Enterprises Millions Per Incident (https://crashplan.com/blog/why-data-loss-really-costs-enterprises-millions-per-incident)