
In a time when cyber threats are more pronounced than ever, the healthcare sector stands at a pivotal juncture. The necessity for robust cybersecurity measures cannot be overstated, particularly as organizations face increasingly sophisticated attacks targeting sensitive patient data.
At the forefront of this challenge is the concept of defense in depth, a crucial strategy that employs multiple layers of security to safeguard information. This article explores the fundamental principles of this comprehensive approach, emphasizing how healthcare CFOs can utilize it to bolster security, ensure compliance, and mitigate risks.
However, as organizations grapple with the complexities of implementing such strategies, a pressing question arises: how can they effectively balance the imperative for strong protection against the backdrop of an ever-evolving cyber landscape?
What is defense in depth? It is an essential strategy that employs multiple layers of protective measures to secure an organization's information and systems. In the healthcare sector, where data security is of utmost importance, this approach is particularly vital. The core principle of layered security ensures that if one tier fails, additional layers remain to provide protection, significantly reducing the likelihood of a successful cyberattack.
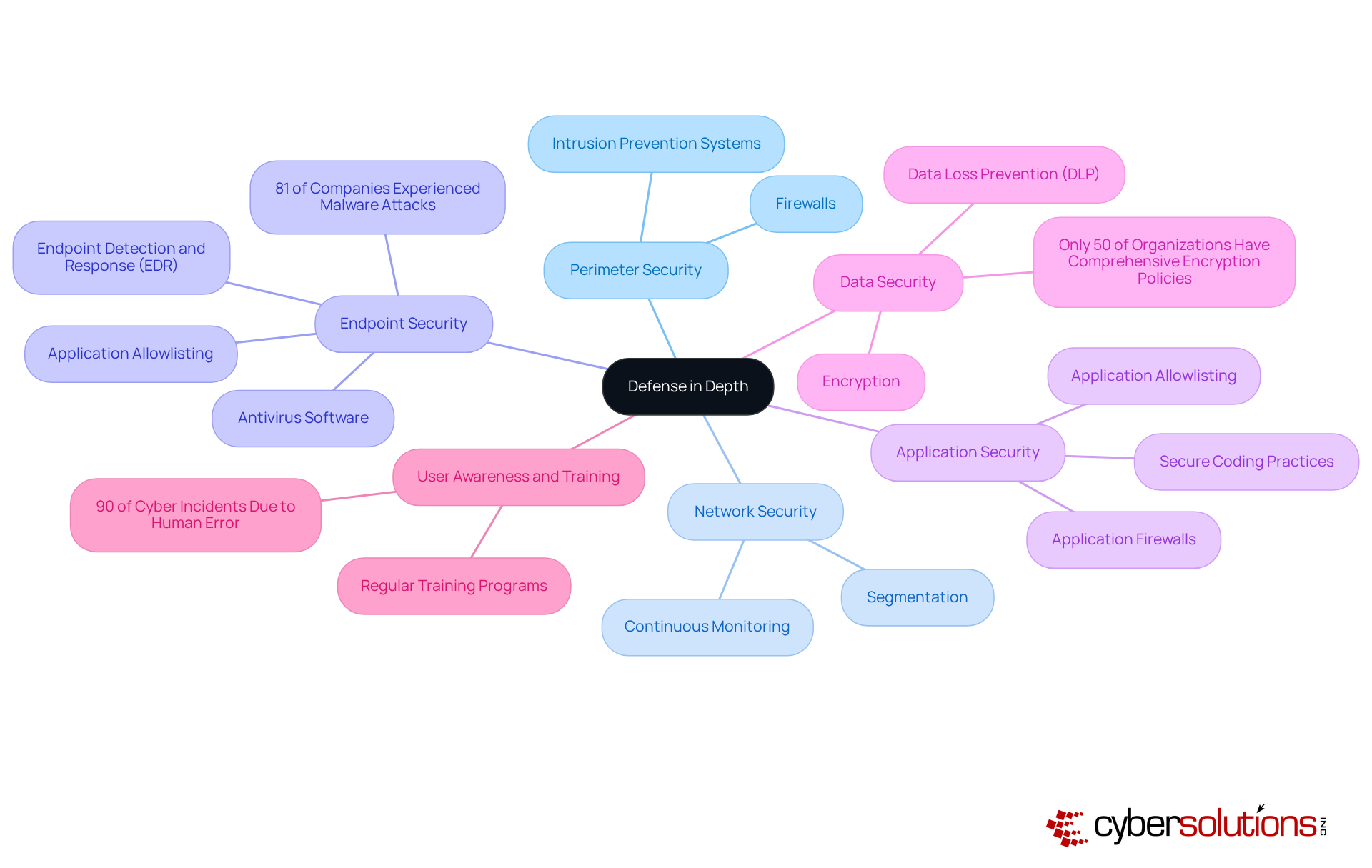
In healthcare, the integration of diverse protective measures—such as firewalls, intrusion detection systems, encryption, multi-factor authentication, and antivirus software—creates a formidable defense against a variety of threats. Antivirus software stands out as a critical component, proactively blocking unauthorized or malicious software from executing, thus minimizing the attack surface and vulnerabilities. Centralized management and continuous monitoring capabilities further enhance its effectiveness, allowing organizations to efficiently manage allowlists across all devices and swiftly detect unauthorized software attempts.
Real-world examples underscore the effectiveness of multi-layered security controls. In 2024, healthcare entities that adopted a multi-layered security approach reported a remarkable 93% decrease in data breaches compared to those relying on single-layer protections. Moreover, the implementation of Security Information and Event Management (SIEM) solutions has facilitated real-time monitoring, enabling organizations to swiftly identify and respond to suspicious activities.
The fundamental principles of defense in depth for healthcare encompass:
Ultimately, adopting a defense in depth strategy is crucial for healthcare organizations striving to maintain security while effectively protecting sensitive patient information from evolving cyber threats. As Stephen Kines, COO/Co-Founder of Goldilock, emphasizes, "To combat these intelligent threats, businesses must adopt a multilayered cybersecurity approach."

In today's digital landscape, the importance of cybersecurity in healthcare cannot be overstated. Defense in depth refers to the idea of layered protection, derived from military tactics, which emphasizes the necessity of employing multiple levels of security to safeguard essential assets. This strategy began gaining traction in the late 1990s and early 2000s as organizations encountered increasingly sophisticated cyber threats. Initially, protective measures were often isolated, primarily focusing on boundary safeguards. However, as cyberattacks grew in complexity and frequency, it became evident for a comprehensive approach.
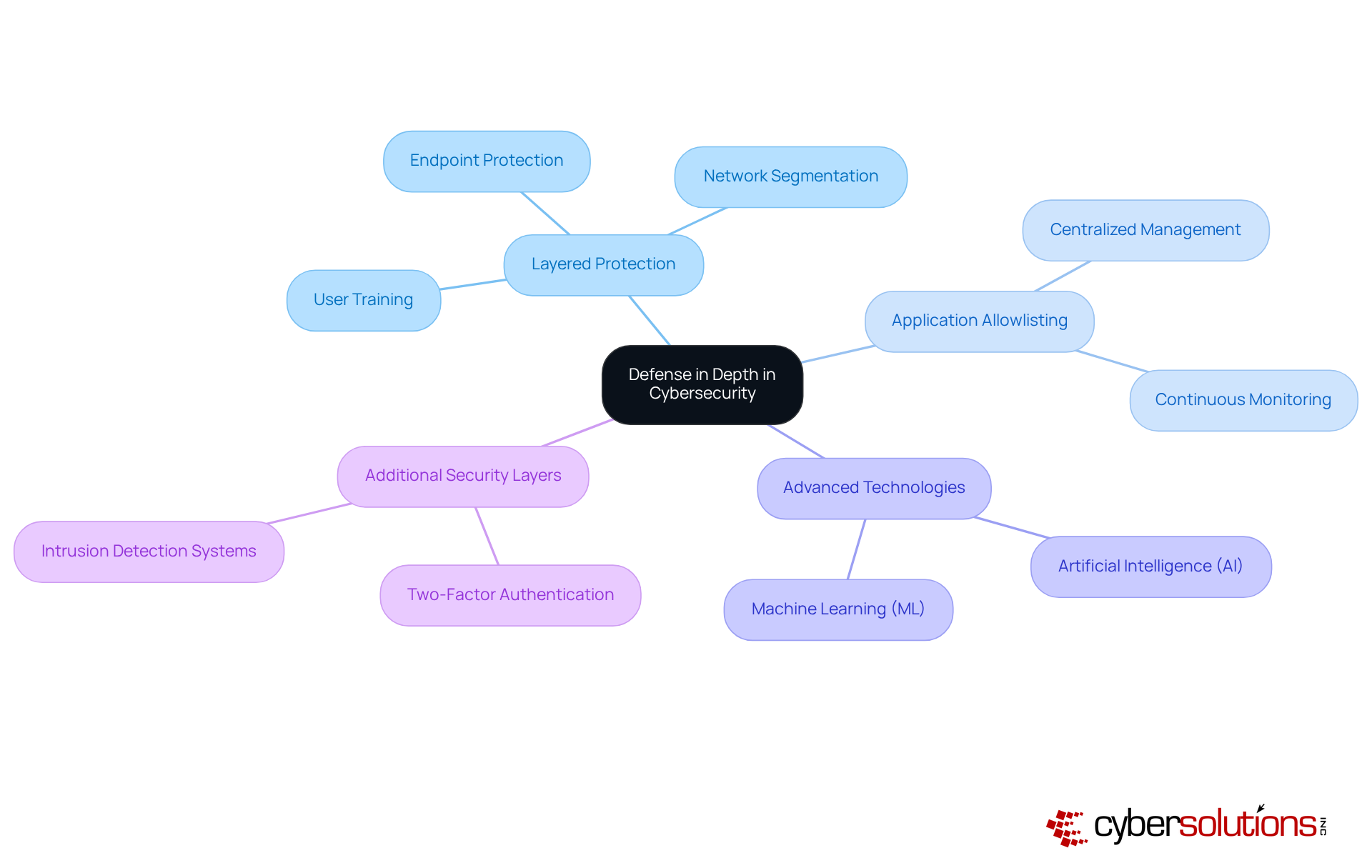
Currently, layered protection integrates various technologies and practices, such as:
These exemplify key strategies in illustrating a holistic view of cybersecurity. A pivotal component of this strategy is application whitelisting, which proactively prevents unauthorized or malicious applications from executing, thereby minimizing the attack surface and reducing vulnerabilities. This is particularly critical in sectors like healthcare, where data security is essential.
Features of application whitelisting, including:
Significantly enhance its effectiveness in protecting sensitive data. Moreover, the integration of artificial intelligence (AI) and machine learning (ML) has become vital for improving threat detection and risk mitigation. Organizations are also adopting additional security layers, such as:
To strengthen their defenses.
Statistics reveal that 43% of healthcare organizations experience data breaches, underscoring the urgency of this approach for healthcare entities. Furthermore, the principle of least privilege plays a crucial role in safeguarding sensitive data, ensuring that users have only the minimum access necessary for their roles. As companies grapple with challenges like outdated anti-malware software and untrained staff, it is increasingly essential to know that defense in depth, as a robust strategy, including multiple layers of security, is necessary to combat evolving cyber threats.
In today's healthcare landscape, a robust cybersecurity strategy is not just an option; it is a necessity. A strategy encompasses several critical layers that work together to fortify an organization's cybersecurity posture:
What is defense in depth involves each layer serving a distinct purpose, collectively enhancing the entity's resilience against cyber threats. As the market is expected to expand from USD 13.37 billion in 2023 to USD 31.2 billion by 2032, investing in these layers is not merely a necessity but a strategic benefit for healthcare entities navigating the intricacies of contemporary cybersecurity. Moreover, the growth of remote work has heightened challenges, requiring increased vigilance from system administrators. Partnering with Cyber Solutions ensures that your systems remain secure, compliant, and audit-ready at all times.
In today's digital landscape, the importance of defense in depth cannot be overstated. Understanding its benefits provides numerous advantages for organizations, particularly in this sensitive field.

Implementing a defense in depth strategy is not merely advisable but essential for healthcare organizations striving to protect sensitive patient information from cyber threats. By integrating multiple layers of security, this approach significantly bolsters system resilience, ensuring that if one layer falters, others remain intact to provide ongoing protection. This multi-faceted method is particularly critical in the healthcare sector, where adherence to regulations like HIPAA is non-negotiable.
Key arguments underscore the necessity of layered security measures, including:
Together, these elements forge a robust defense against potential breaches. Organizations that embrace a defense in depth approach witness substantial reductions in data breaches and enhanced compliance with regulatory standards. Additionally, the advantages extend beyond security, offering cost-effectiveness and improved incident response capabilities.
The importance of grasping and implementing defense in depth cannot be overstated. As cyber threats continue to evolve, healthcare organizations must prioritize this strategy to safeguard sensitive data and maintain patient trust. Investing in a comprehensive cybersecurity framework is not just a necessity; it is a strategic imperative that secures the longevity and integrity of healthcare systems in an increasingly digital landscape.
What is defense in depth in cybersecurity?
Defense in depth is a cybersecurity strategy that employs multiple layers of protective measures to secure an organization's information and systems, significantly reducing the likelihood of a successful cyberattack.
Why is defense in depth particularly important in the healthcare sector?
In the healthcare sector, safeguarding sensitive patient data is crucial, making a multi-layered security approach essential to protect against various threats.
What are some protective measures included in a defense in depth strategy?
Protective measures include firewalls, intrusion detection systems, encryption, multi-factor authentication, and application allowlisting.
What role does application allowlisting play in defense in depth?
Application allowlisting proactively blocks unauthorized or malicious software from executing, minimizing the attack surface and vulnerabilities within an organization.
How does centralized management and continuous monitoring enhance defense in depth?
Centralized management allows organizations to efficiently manage allowlists across all devices, while continuous monitoring enables swift detection of unauthorized software attempts and other suspicious activities.
What evidence supports the effectiveness of a multi-layered security strategy in healthcare?
In 2024, healthcare entities that adopted a multi-layered strategy reported a 93% decrease in data breaches compared to those relying on single-layer protections.
What is the significance of Security Information and Event Management (SIEM) solutions in defense in depth?
SIEM solutions facilitate real-time threat intelligence, enabling organizations to quickly identify and respond to suspicious activities.
What are the fundamental principles of defense in depth for healthcare?
The fundamental principles include layered security, continuous monitoring, and incident response planning to identify, contain, and mitigate breaches.
How does adopting a layered approach help healthcare organizations?
A layered approach helps healthcare organizations maintain compliance with regulations like HIPAA while effectively protecting sensitive patient information from evolving cyber threats.