Introduction
In healthcare, where every second counts, the importance of a robust disaster recovery plan cannot be underestimated. Businesses in this sector must navigate a complex landscape of cyber threats and operational risks, making effective recovery strategies essential. Navigating the complex landscape of cyber threats and operational risks can feel overwhelming for healthcare organizations. Without a robust disaster recovery plan, organizations may find themselves vulnerable to significant operational disruptions and reputational damage.
Let’s explore four essential practices that can help you craft resilient disaster recovery plans that safeguard operations, enhance communication, and foster continuous improvement:
- Assess Risks and Vulnerabilities
- Develop a Comprehensive Recovery Strategy
- Train Staff and Conduct Drills
- Review and Update the Plan Regularly
By implementing these four essential practices, organizations can not only prepare for crises but also emerge from them with renewed strength and resilience.
Identify Key Components of a Disaster Recovery Plan
In an era where cyber threats loom large, the importance of a solid disaster response plan (DRP) in healthcare cannot be overstated. A solid DRP must incorporate several key elements to ensure effective restoration from disruptions. These components typically encompass:
- Inventory of Assets: Document all hardware, software, and data assets critical to business operations. This inventory should include details about servers, applications, and data storage solutions. A thorough inventory is crucial, as it enables organizations to evaluate risks and set time objectives (RTOs) effectively.
- Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO): Define the maximum acceptable downtime (RTO) and the maximum acceptable data loss (RPO) for each critical system. For instance, mission-critical systems typically have an RTO of 1-4 hours, while non-critical systems may have an RTO of 24-72 hours. Setting these metrics aids in prioritizing restoration efforts based on business impact, ensuring that the most essential functions are restored first.
- Backup Solutions: Implement reliable data backup solutions that ensure data is regularly backed up and can be restored quickly. Consider offsite backups or cloud solutions for added security. An RPO of 15 minutes may require continuous replication or very frequent backups to minimize data loss during an emergency.
- Detailed Restoration Procedures: Having clear and tested restoration procedures is crucial for managing crises effectively. Outline step-by-step processes for reinstating systems and data, including roles and responsibilities for team members involved in the restoration process. This clarity ensures that restoration efforts can be carried out efficiently, minimizing downtime and confusion during IT failures.
- Testing and Maintenance Protocols: Establish protocols for regularly testing the DRP to ensure its effectiveness and updating it as necessary to reflect changes in the business environment or technology. Frequent evaluation of the recovery strategy is crucial, as it assists in recognizing vulnerabilities and guarantees that the team is adequately prepared for actual events. As Walter Kenrich states, "Regular testing ensures that the plan is effective and that the team is well-prepared."
- Training and Simulation Exercises: Incorporate regular training sessions and emergency simulation exercises for the Recovery Team (RT) to familiarize them with their roles and responsibilities during crises. This preparation is crucial for effective recovery and minimizes downtime.
- Automated Failover Tools: Consider implementing automated failover tools that can detect system failures and switch to backup systems without human intervention. This technology significantly reduces downtime and ensures quick transitions during routine failures.
- Clear Communication Protocols: Establish clear communication protocols to ensure timely updates to employees, customers, partners, and media during a crisis. Transparency in communication helps preserve trust and manage expectations.
The staggering costs associated with downtime can cripple organizations, making a robust disaster response plan not just beneficial, but essential. Investing in a comprehensive DRP is not merely a precaution; it’s a strategic imperative that can safeguard your organization’s future.

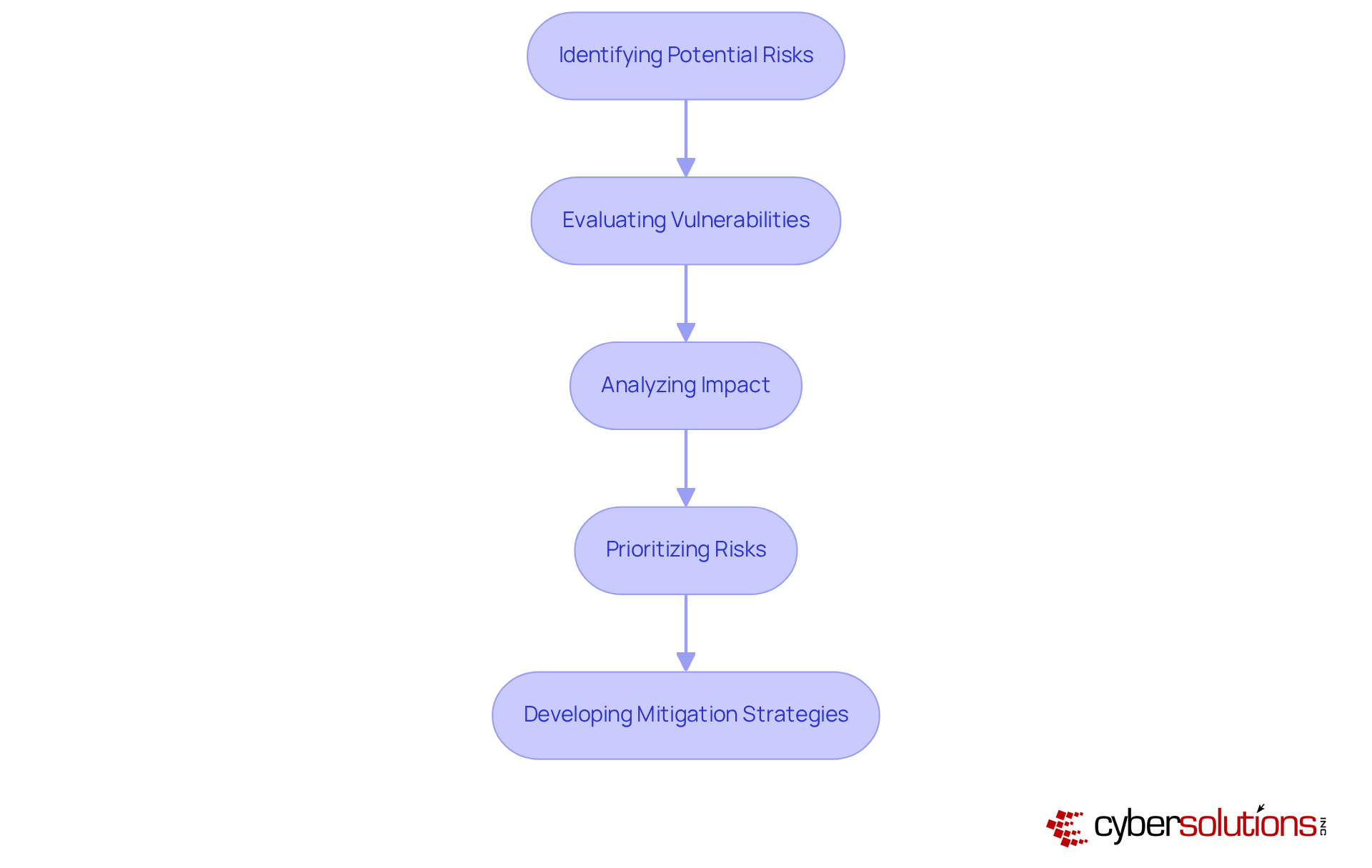
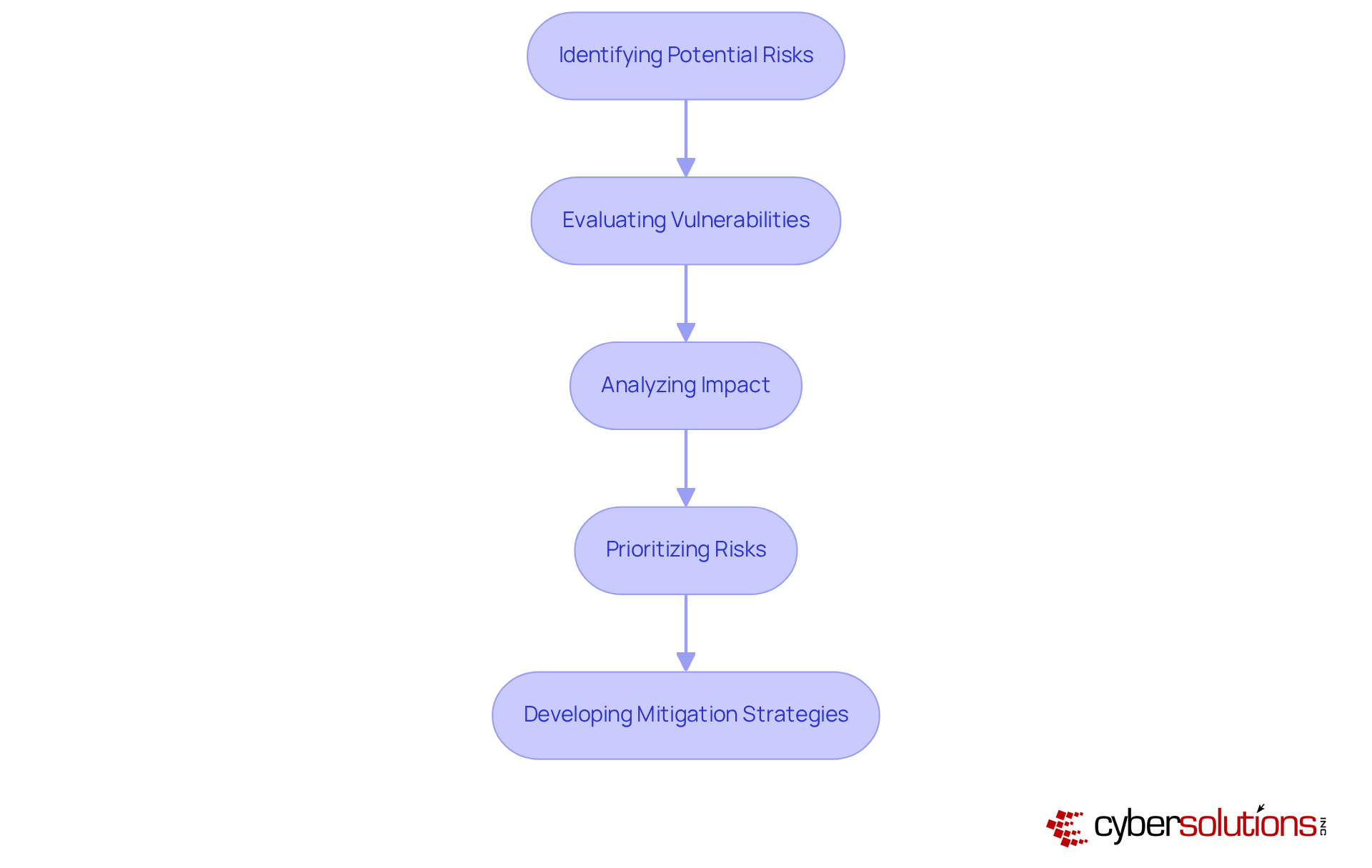
Conduct Comprehensive Risk Assessments
In an era where cybersecurity threats are evolving rapidly, a comprehensive risk evaluation is not just beneficial; it's essential for a successful recovery strategy. Let’s break down the key steps involved in this process:
- Identifying Potential Risks: Organizations must analyze a range of threats that could disrupt operations, including natural disasters, cyberattacks, and equipment failures. As we approach 2026, the threat landscape grows more complex, with geopolitical tensions and climate-related crises presenting significant challenges.
- Evaluating Vulnerabilities: Assessing weaknesses within the organization is crucial. This includes examining physical security measures, network defenses, and the adequacy of employee training programs. Organizations that proactively identify weaknesses can better prepare for potential disruptions. A key aspect of this evaluation is the implementation of application allowlisting, which prevents unauthorized software from executing, thereby reducing the attack surface and minimizing vulnerabilities.
- Analyzing Impact: It is vital to determine the potential impact of each identified threat on business operations. This analysis should consider financial losses, reputational harm, and regulatory effects. Entities with robust disaster recovery plans for businesses experience decreased downtime and enhanced adherence to regulations. Application allowlisting can assist in meeting compliance requirements for standards such as HIPAA, PCI-DSS, and GDPR, ensuring strict data protection protocols are followed.
- Prioritizing Risks: Ranking identified risks based on their likelihood and potential impact allows organizations to allocate resources effectively. High-risk sectors, like healthcare and finance, should prioritize their contingency plans to ensure operational integrity.
- Developing Mitigation Strategies: Organizations should create strategies to mitigate identified risks. This may involve implementing advanced technologies, enhancing security protocols such as application allowlisting, or providing targeted employee training. Efficient emergency response plans not only reduce downtime but also promote operational resilience and agility.
By conducting thorough risk evaluations and implementing advanced cybersecurity measures like application allowlisting, supported by Cyber Solutions' managed IT services, businesses can effectively address vulnerabilities and significantly enhance their resilience, preparing them for the challenges of 2026. Embracing these proactive measures will not only safeguard your organization but also position it for success in an unpredictable future.
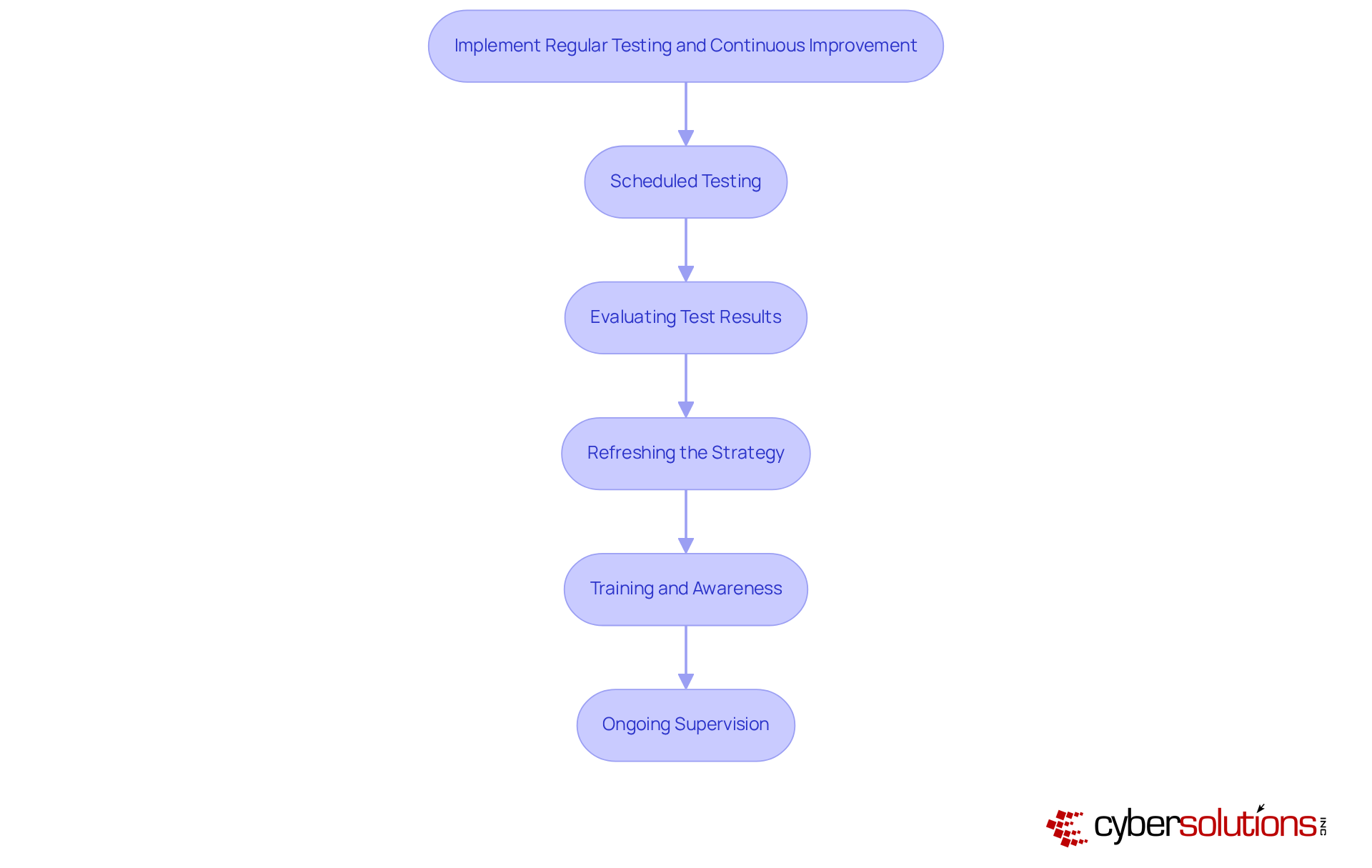
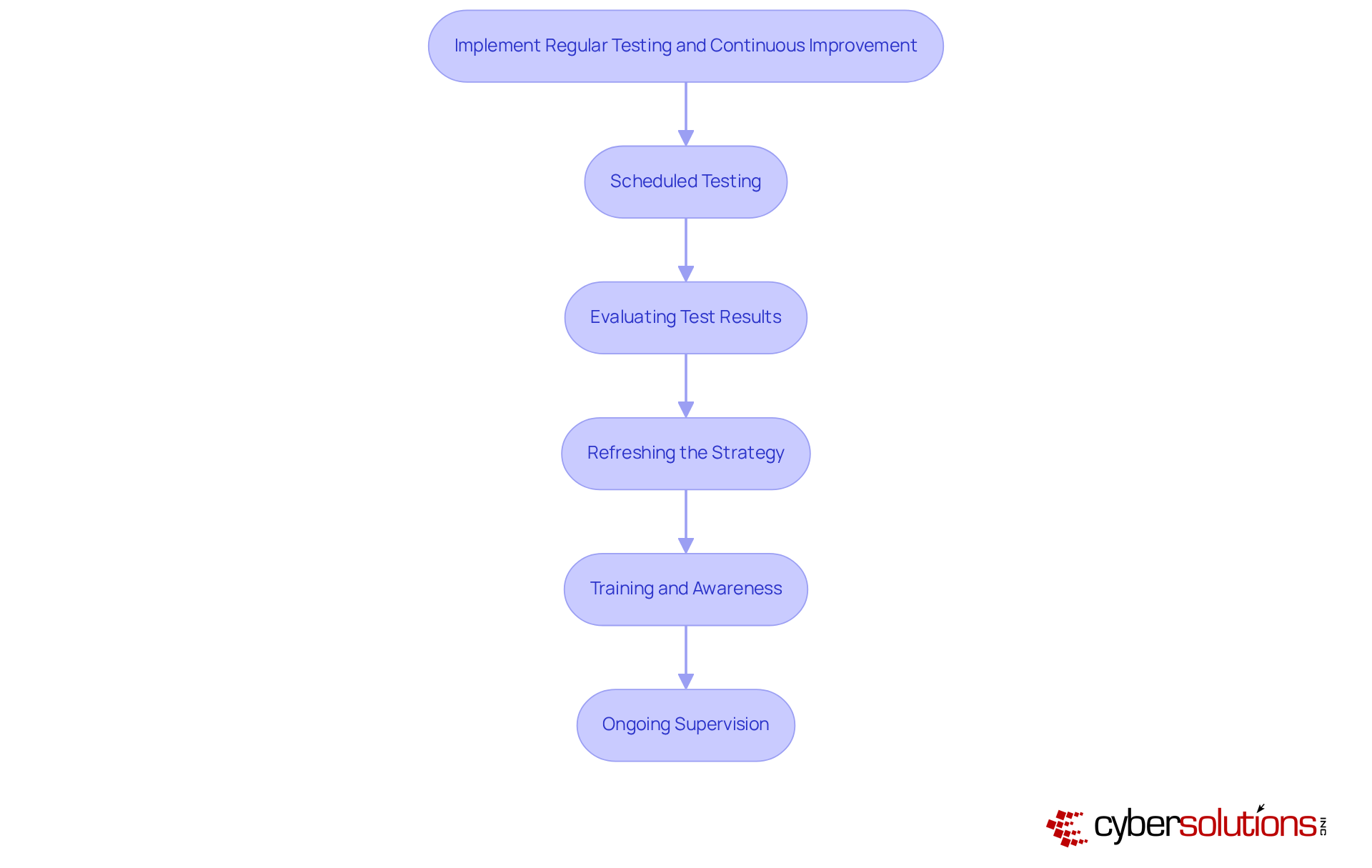
Implement Regular Testing and Continuous Improvement
In an era where cyber threats loom larger than ever, the integrity of healthcare organizations hinges on robust disaster recovery plans. To maintain the effectiveness of these plans, organizations must prioritize regular testing and continuous improvement practices, which include:
- Scheduled Testing: Regularly carry out evaluations of the emergency response plan, including tabletop exercises, simulations, and full-scale drills. This practice helps team members understand their roles during a disaster and boosts confidence in the recovery process. Experts suggest that tabletop exercises take place quarterly at least, while full-scale testing for preparedness should be performed annually. Rapid incident response strategies, such as having an incident response team on-site within 24 hours, can significantly enhance the effectiveness of these tests, as demonstrated by the healthcare provider that recovered ahead of schedule after a ransomware incident.
- Evaluating Test Results: After each test, it is crucial to evaluate the outcomes to identify both strengths and weaknesses in the recovery process. Collecting feedback from participants offers valuable insights into areas requiring enhancement, which is crucial for refining the strategy. Organizations that frequently evaluate their strategies recover more quickly and uphold customer confidence, as shown by the healthcare provider that improved its security measures after a ransomware incident.
- Refreshing the Strategy: Employ the knowledge acquired from test assessments to revise the disaster response strategy. Address identified gaps and incorporate new technologies or processes that can improve restoration efforts. Ongoing enhancement is crucial, as organizations that frequently assess their strategies recover more quickly and uphold customer confidence, particularly amid increasing cyber threats and operational interruptions. A layered strategy-encompassing endpoint isolation and user training-can further enhance restoration efforts.
- Training and Awareness: Continuous instruction for employees is vital to ensure they understand their responsibilities in the emergency response procedure and are informed of any modifications to the strategy. This training should be integrated into standard operational procedures rather than viewed as a distinct initiative, as continuous education is essential for efficient crisis management. Specialized expertise in incident management can empower teams to respond more effectively during crises.
- Ongoing Supervision: Create a strong procedure for consistently observing the efficiency of the emergency response strategy. This includes regular reviews of risk assessments and adapting to changes in the business environment. Organizations that implement continuous monitoring can better respond to evolving threats and ensure compliance with industry regulations. By embracing these proactive measures, organizations not only fortify their defenses but also ensure their operational continuity in the face of adversity.
Establish Clear Communication Protocols
In the high-stakes world of emergency recovery, effective communication can mean the difference between chaos and order. Organizations must establish clear communication protocols that encompass the following elements:
- Communication Channels: It is vital to identify and create various communication channels - such as email, text messages, phone calls, and social media - to ensure that all stakeholders can be contacted during an emergency. Research indicates that more than 70% of organizations have implemented emergency communication strategies in the past year. This trend reflects a growing risk environment that necessitates diverse channels for effective outreach.
- Roles and Responsibilities: Clearly defining the roles and responsibilities of team members involved in the crisis management process is crucial. This ensures that everyone knows whom to contact for specific issues, facilitating a more organized response. Involving at least one member from the C-suite in the crisis communication team can enhance the effectiveness of messaging and decision-making.
- Frequent Updates: Supplying consistent updates to all stakeholders - including employees, clients, and partners - regarding the status of recovery efforts and any modifications to the emergency recovery strategy is essential. Timely information can significantly impact response outcomes, as seen in the case of the Massachusetts hospital cybersecurity incident in 2025, where consistent communication helped manage the crisis effectively.
- Crisis Communication Strategy: Creating a comprehensive crisis communication strategy is essential. This strategy should detail how to engage with the public and media during a crisis, ensuring that messaging stays cohesive and correct. The integration of crisis communication into disaster recovery plans for businesses has proven effective in addressing situations that could cause physical harm.
- Response Systems: Establishing response systems enables entities to collect feedback from stakeholders throughout and following a crisis management effort. This continuous improvement approach is critical for refining communication strategies and enhancing overall preparedness. Regular training and exercises, which over 80% of entities conducted annually, can help identify blind spots and ensure protocols function effectively in real emergencies.
Without these protocols, organizations risk not only their recovery efforts but also their reputation and stakeholder trust.

Conclusion
In today's volatile environment, a robust disaster recovery plan (DRP) is not just a safety net; it's a strategic necessity for businesses. It ensures that organizations can swiftly recover from disruptions and maintain operational integrity. The core components of an effective DRP - ranging from asset inventories and recovery objectives to thorough testing and clear communication protocols - collectively empower organizations to mitigate risks and enhance their resilience.
The article highlights several key practices that underpin a successful disaster recovery strategy:
- Identifying critical assets allows organizations to prioritize their recovery efforts effectively.
- Conducting comprehensive risk assessments helps in recognizing potential vulnerabilities and establishing mitigation strategies.
- Regular testing of the recovery plan ensures that teams are prepared and that the plan remains relevant amid evolving threats.
- Establishing clear communication protocols fosters trust and transparency during crises, which is vital for maintaining stakeholder confidence.
Organizations face constant threats that can disrupt operations and compromise data integrity. Prioritizing these practices is not merely advisable - it is imperative. Organizations must invest in comprehensive disaster recovery strategies that incorporate continuous improvement and proactive training. By doing so, they not only safeguard their assets and reputation but also position themselves for long-term success amidst adversity. By prioritizing disaster recovery, organizations can not only weather the storm but emerge stronger and more resilient.
Frequently Asked Questions
What is the purpose of a Disaster Recovery Plan (DRP) in healthcare?
A Disaster Recovery Plan (DRP) is essential in healthcare to ensure effective restoration from disruptions caused by cyber threats and other emergencies.
What are the key components of a solid Disaster Recovery Plan?
Key components include an inventory of assets, Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO), backup solutions, detailed restoration procedures, testing and maintenance protocols, training and simulation exercises, automated failover tools, and clear communication protocols.
Why is an inventory of assets important in a DRP?
An inventory of assets is crucial as it documents all critical hardware, software, and data, enabling organizations to evaluate risks and set effective RTOs.
What are Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO)?
RTO defines the maximum acceptable downtime for critical systems, while RPO defines the maximum acceptable data loss. RTOs can vary from 1-4 hours for mission-critical systems to 24-72 hours for non-critical systems.
What types of backup solutions should be implemented in a DRP?
Reliable data backup solutions should be implemented, including offsite backups or cloud solutions, to ensure data is regularly backed up and can be restored quickly.
Why are detailed restoration procedures important in a DRP?
Clear and tested restoration procedures are vital for managing crises effectively, as they outline step-by-step processes and define roles and responsibilities, minimizing downtime and confusion during IT failures.
How often should a DRP be tested and maintained?
A DRP should be regularly tested and updated to reflect changes in the business environment or technology, helping to recognize vulnerabilities and ensure the team is prepared for actual events.
What role do training and simulation exercises play in a DRP?
Regular training sessions and emergency simulation exercises help familiarize the Recovery Team with their roles during crises, which is crucial for effective recovery and minimizing downtime.
What are automated failover tools and how do they benefit a DRP?
Automated failover tools detect system failures and switch to backup systems without human intervention, significantly reducing downtime and ensuring quick transitions during routine failures.
Why is clear communication important during a crisis?
Clear communication protocols ensure timely updates to employees, customers, partners, and media, helping to preserve trust and manage expectations during a crisis.
List of Sources
- Identify Key Components of a Disaster Recovery Plan
- Key Disaster Recovery Plan Elements and Measures | Cutover (https://cutover.com/blog/essential-elements-disaster-recovery-plan-bounce-back-outage)
- Disaster Recovery Testing: What You Need to Know in 2026 (https://harness.io/blog/an-introduction-to-disaster-recovery-testing-what-you-need-to-know-in-2026)
- Disaster Recovery Plan: Key Components Explained | SysGen (https://sysgen.ca/blog-what-is-a-disaster-recovery-plan-what-to-include)
- Business Continuity Planning 2026: Disaster Recovery for SMBs (https://technijian.com/business-continuity/business-continuity-planning-2026-how-to-recover-faster-from-it-failures?srsltid=AfmBOoodfEksh6PuRJqIReDUlNTXSC3pfzKbEzJbSDLvjUESVK5920dZ)
- Why 2026 Will Redefine Disaster Recovery as We Know It (https://drj.com/journal_main/disaster-recovery-trends-2026)
- Conduct Comprehensive Risk Assessments
- The Top 10 Business Risks Organizations Can’t Ignore in 2026 - RiskVersity (https://riskversity.com/the-top-10-business-risks-organizations-cant-ignore-in-2026)
- Everbridge Releases 2026 Regional Threat Assessment Highlighting Risk Trends Shaping the Global Security Landscape - Everbridge (https://everbridge.com/newsroom/article/everbridge-releases-2026-regional-threat-assessment-highlighting-risk-trends-shaping-the-global-security-landscape)
- Disaster Recovery in Cybersecurity Explained (2026) (https://eccu.edu/blog/disaster-recovery-cybersecurity-2026)
- Press Releases | DRI International (https://drii.org/pressreleases/details/f9ea6da53c32/dri-international-releases-11th-annual-predictions-report-highlighting-risk-and-resilience-trends-for-2026)
- Key Risks for 2026: How U.S. Organizations Can Build Resilience (https://zurichresilience.com/knowledge-and-insights-hub/articles/2026/02/key-risks-to-watch-for-in-2026-how-us-organizations-can-build-resilience)
- Implement Regular Testing and Continuous Improvement
- An Introduction to Disaster Recovery Testing in 2026 (https://harness.io/blog/an-introduction-to-disaster-recovery-testing-what-you-need-to-know-2026)
- How Often Should a Disaster Recovery Plan Be Tested? | Cutover (https://cutover.com/blog/how-often-should-recovery-plans-be-tested)
- DR Testing Is Dead: The Rise of Continuous Resilience Validation (https://drj.com/journal_main/dr-testing-dead-continuous-resilience-validation)
- Announcing Disaster Recovery Testing (https://gremlin.com/blog/announcing-disaster-recovery-testing)
- Establish Clear Communication Protocols
- Your Emergency Plans Will be Activated – Are You Ready? (https://thebci.org/news/your-emergency-plans-will-be-activated-are-you-ready.html)
- Red Cross Completes Communications Drill for Preparedness (https://maarcofrancis.com/red-cross-successfully-executes-communications-drill-for-come-what-may-preparedness)
- Crisis Communications Plans (https://ready.gov/business/emergency-plans/crisis-communications-plans)
- Strengthening disaster risk communication in the Indian Ocean: Media and institutions work together in Mauritius (https://undrr.org/news/strengthening-disaster-risk-communication-indian-ocean-media-and-institutions-work-together)
- Crisis Communication Plan for 2026: 7 Emergency Steps (https://alertmedia.com/blog/crisis-communication)