Introduction
In an era where cyber threats are not just a possibility but a reality, the healthcare sector must prioritize the protection of sensitive patient information like never before. Advanced threat analysis emerges as a vital strategy, offering organizations a framework to identify, assess, and mitigate potential dangers before they escalate into crises.
But here's the real question: how can organizations effectively implement best practices that not only enhance their cybersecurity posture but also foster a culture of continuous improvement in an ever-evolving threat environment?
Organizations struggle to keep pace with rapidly evolving cyber threats, often finding themselves reactive rather than proactive. Failure to address these challenges can lead to devastating breaches, jeopardizing patient trust and organizational integrity.
Understand the Fundamentals of Advanced Threat Analysis
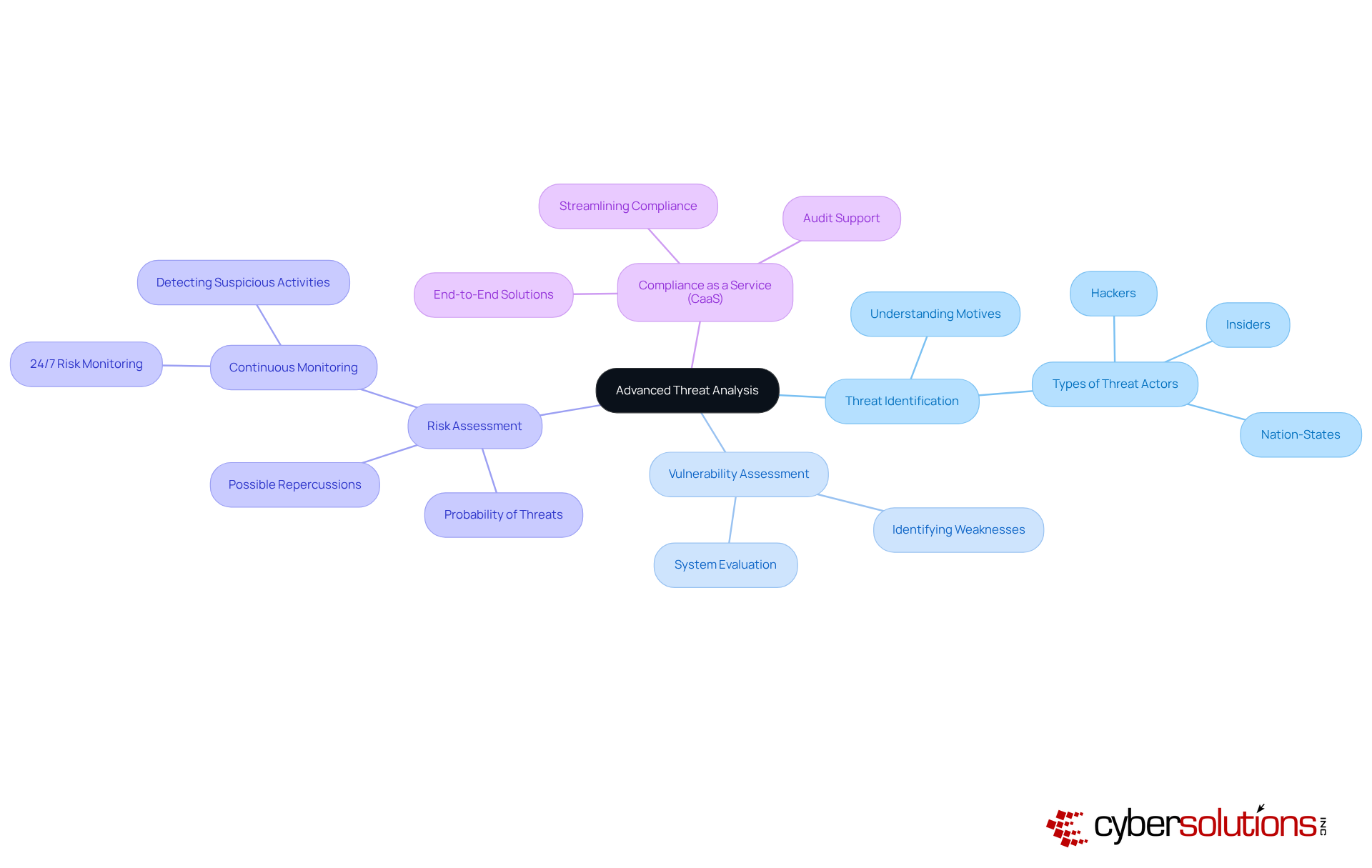
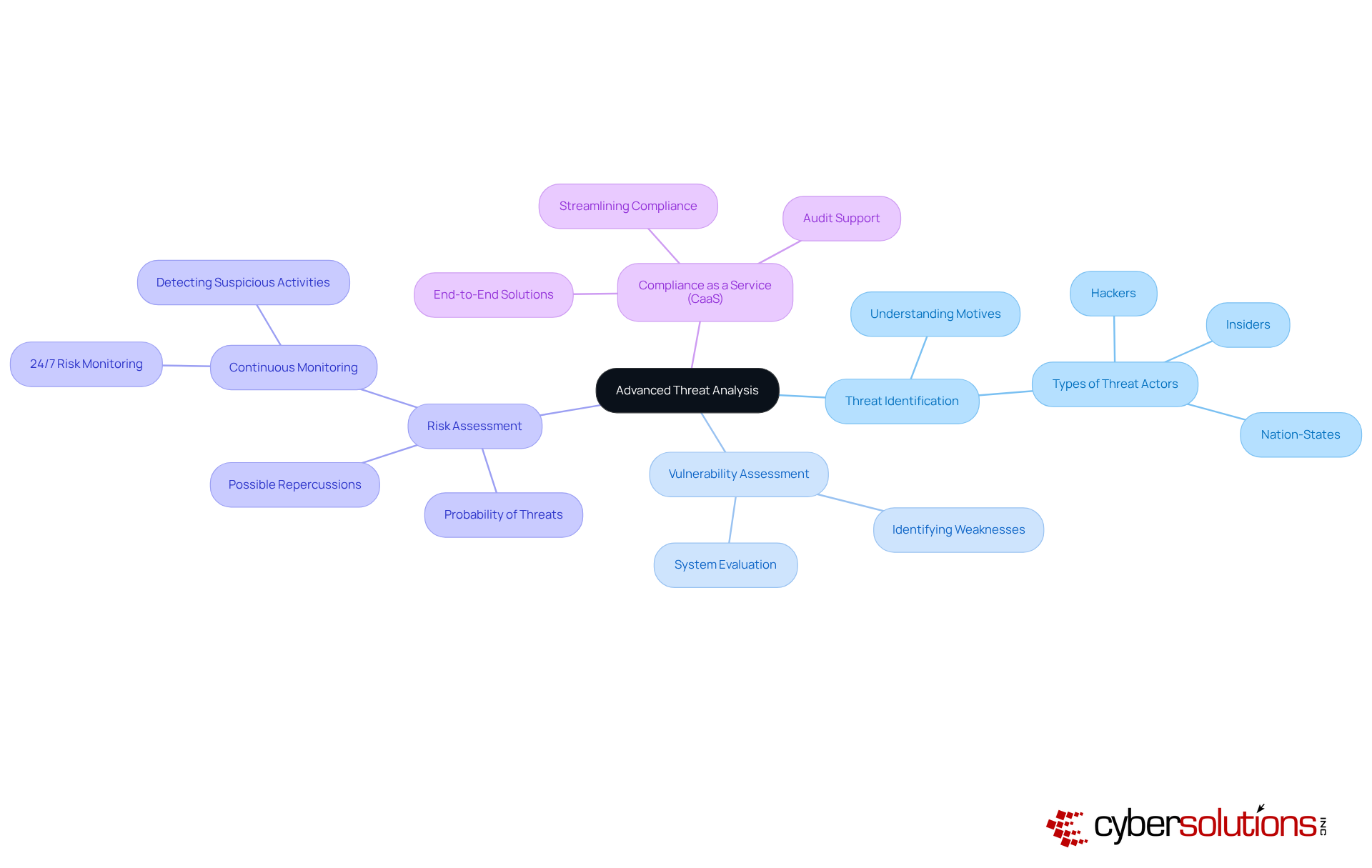
In an era where cyber threats loom larger than ever, the healthcare sector faces unprecedented challenges in safeguarding sensitive information. Advanced risk analysis involves a systematic examination of potential dangers to an organization's information systems. It encompasses understanding the various types of risks, their origins, and the possible effects on business operations. Key components include:
- Threat Identification: Recognizing various threat actors, such as hackers, insiders, and nation-states, and understanding their motives.
- Vulnerability Assessment: Evaluating the organization's systems to identify weaknesses that could be exploited by threats.
- Risk Assessment: Evaluating the probability of a threat taking advantage of a vulnerability and the possible repercussions of such an occurrence.
To truly stay ahead, organizations must embrace 24/7 risk monitoring as a cornerstone of their cybersecurity strategy. Continuous monitoring ensures that suspicious activities are detected and stopped before they escalate into significant threats, protecting your business from ransomware, phishing, and other malware attacks. Moreover, understanding Compliance as a Service (CaaS) can significantly assist entities by delivering end-to-end solutions to satisfy regulatory requirements, streamlining the compliance process, and providing audit support. By prioritizing advanced threat analysis and continuous monitoring, organizations can not only defend against attacks but also foster trust and resilience in their operations.
Implement Effective Methodologies for Threat Analysis
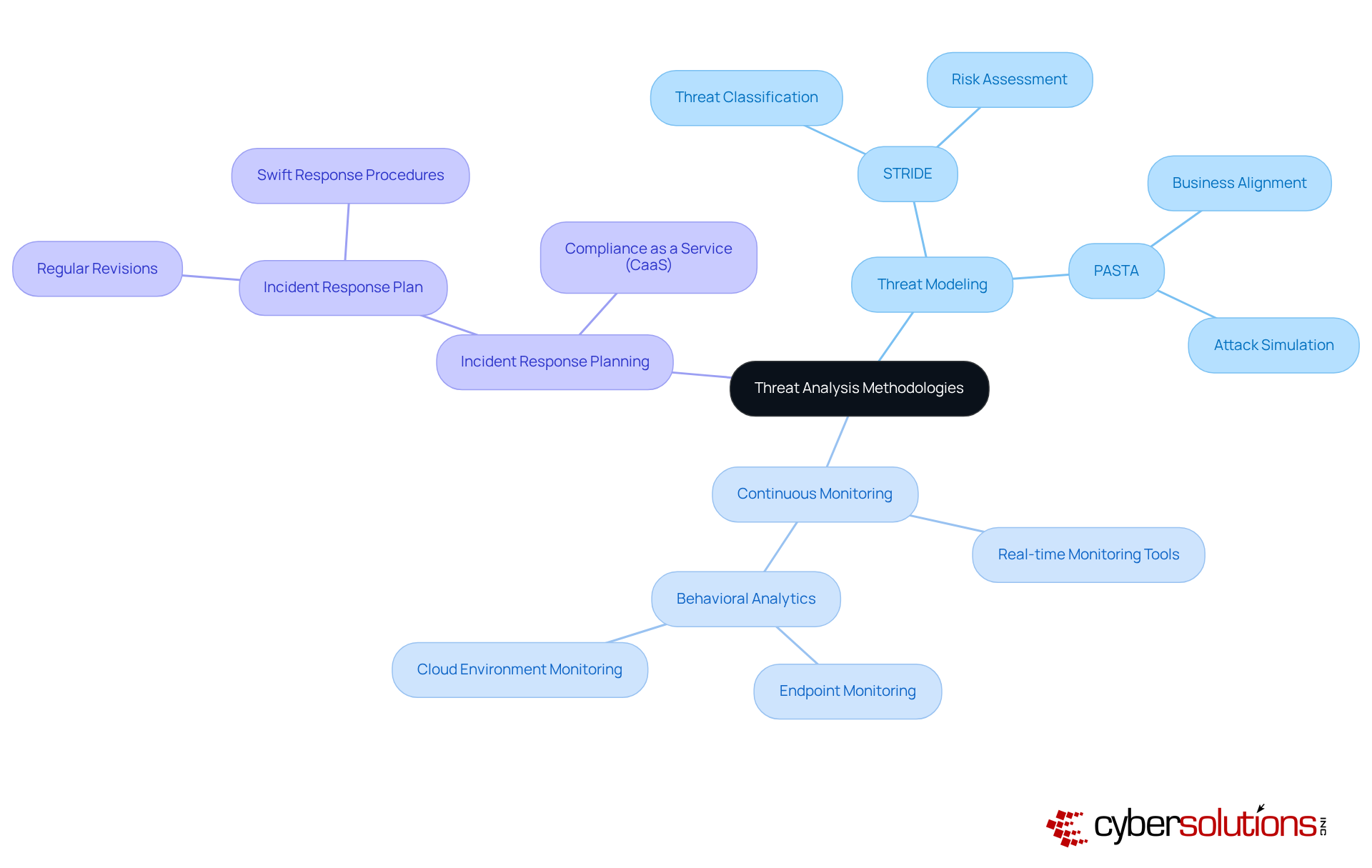
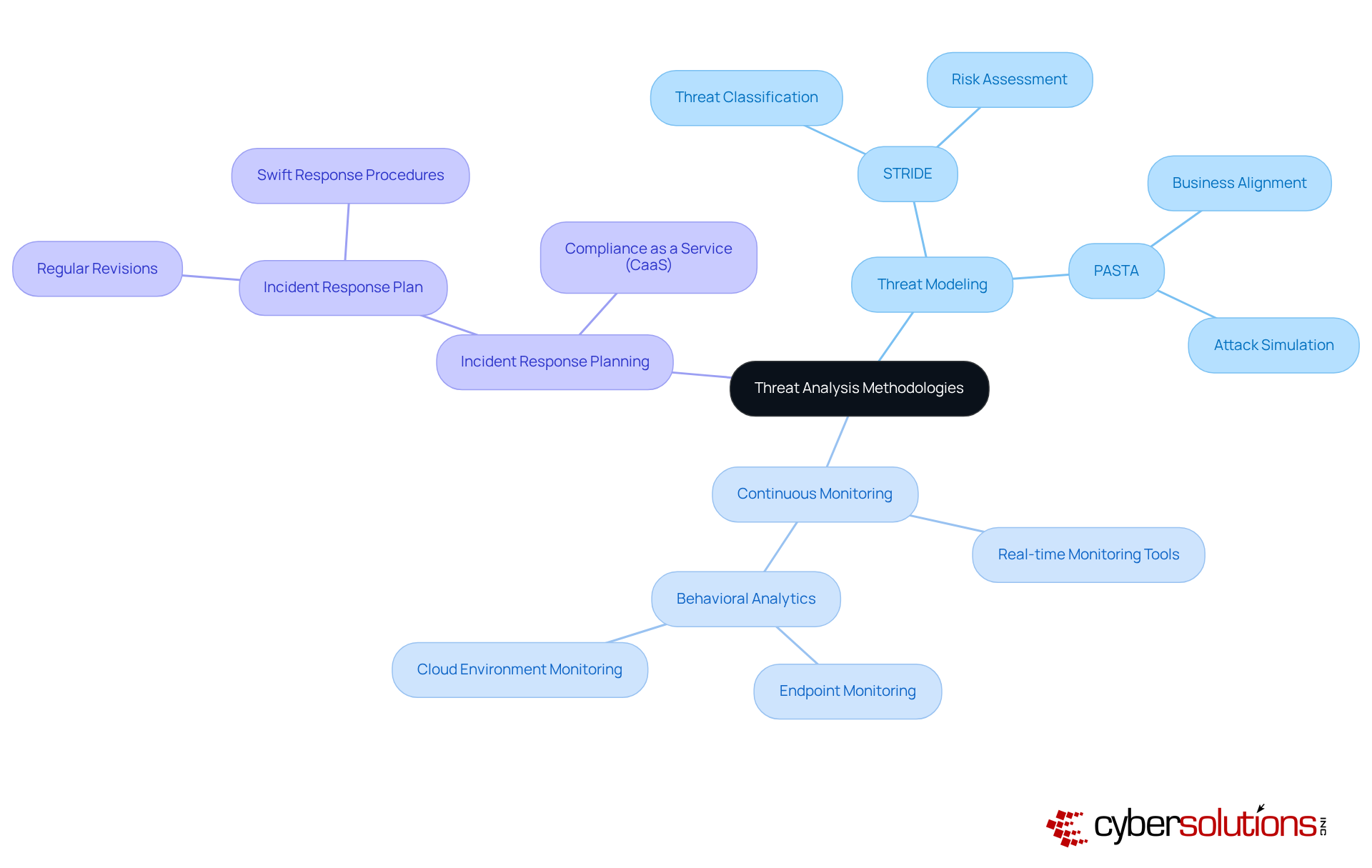
In an era where healthcare data breaches are on the rise, the stakes for cybersecurity have never been higher. To effectively analyze threats, organizations should adopt the following methodologies:
- Threat Modeling: Employ frameworks such as STRIDE and PASTA to systematically identify and evaluate potential threats based on the organization's architecture and operations. STRIDE assists in classifying risks while PASTA aligns risk modeling with business objectives, making it especially effective for organizations managing sensitive data.
- Continuous Monitoring: Implement real-time monitoring tools that provide ongoing visibility into network activities, enabling quick detection of anomalies. The integration of behavioral analytics across endpoints and cloud environments is crucial for identifying risky behaviors and enhancing security posture.
- Incident Response Planning: Create and periodically revise an incident response plan that details procedures for addressing recognized risks, ensuring a swift and organized response. With the average eCrime breakout time dropping to just 29 minutes, having a robust incident response strategy is essential for minimizing damage and maintaining operational integrity. Cyber Solutions provides customized incident response services that swiftly recognize, contain, and reduce risks, ensuring business continuity and a fast recovery. Additionally, our Compliance as a Service (CaaS) solutions assist entities in navigating regulatory requirements, further enhancing their cybersecurity posture.
By embracing these methodologies, organizations not only protect their assets but also enhance their reputation through advanced threat analysis in a risk-laden landscape.
Leverage Technology for Enhanced Threat Detection
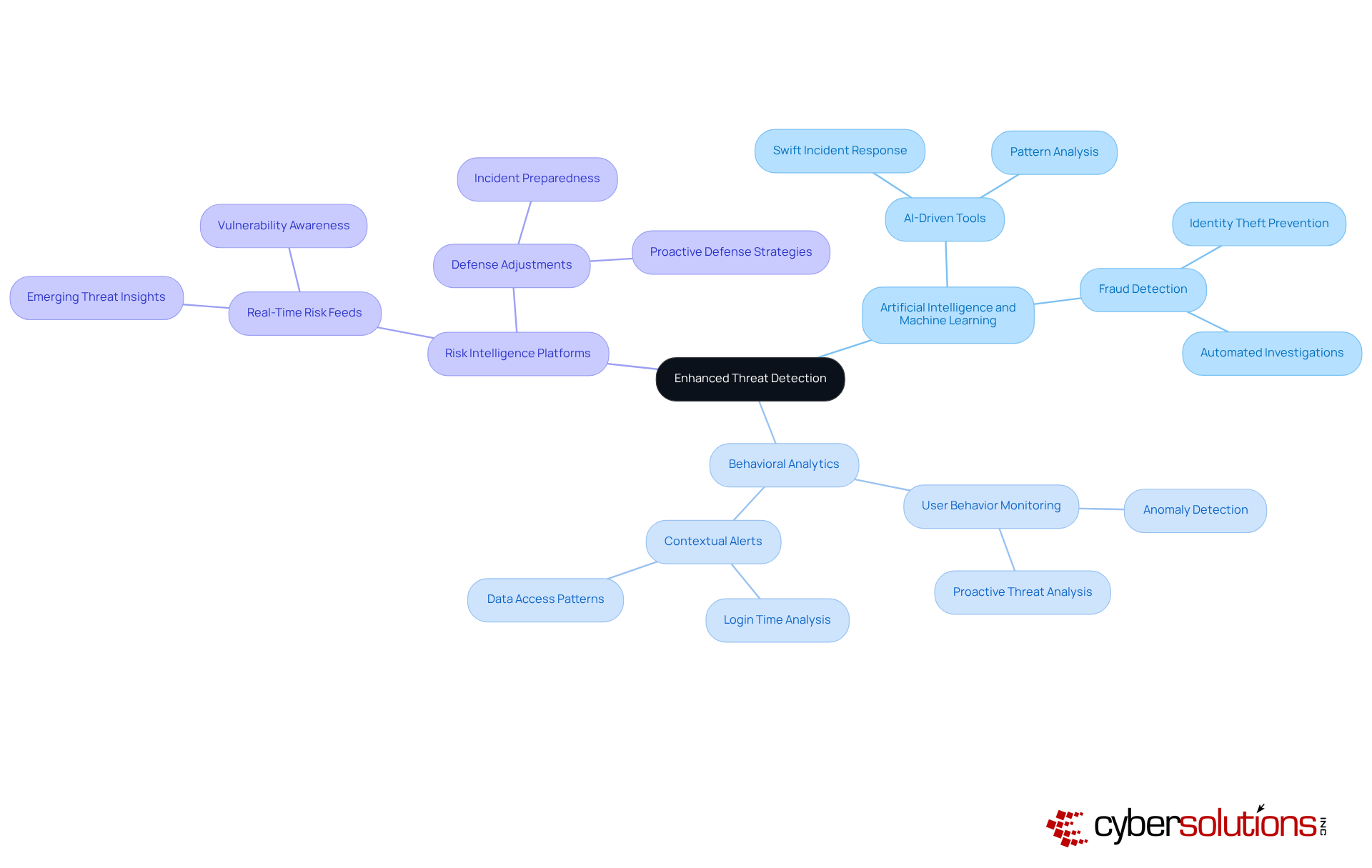
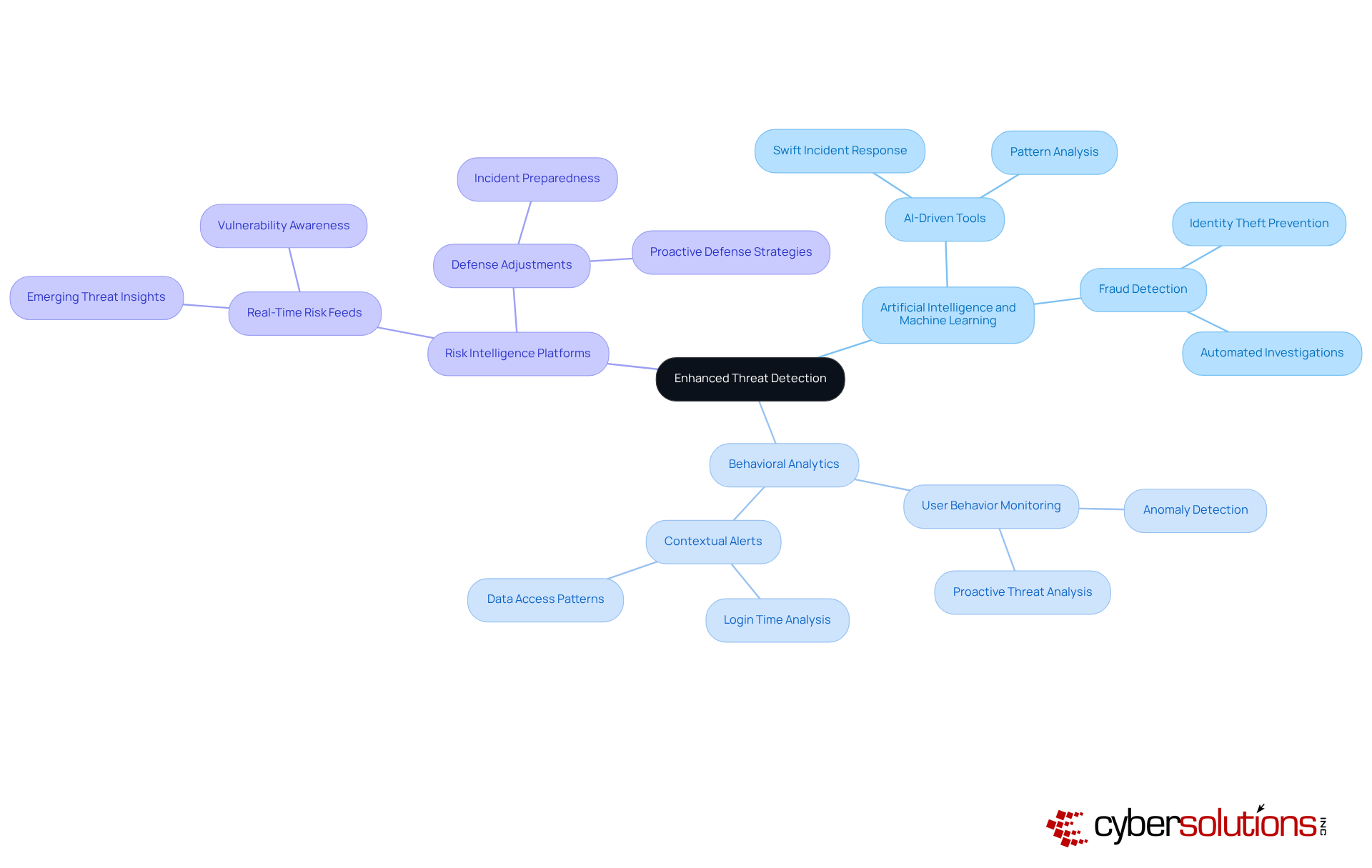
In an era where cyber threats loom larger than ever, the healthcare sector must prioritize robust cybersecurity measures to safeguard sensitive patient information. Organizations can significantly bolster their threat detection capabilities by leveraging advanced technologies, including:
- Artificial Intelligence and Machine Learning: Deploy AI-driven tools that analyze extensive datasets to uncover patterns indicative of potential threats. This allows entities to detect and respond to incidents more swiftly, enhancing overall security effectiveness.
- Behavioral Analytics: Implement tools that continuously monitor user and entity behavior, identifying anomalies that may signal security breaches. This proactive approach facilitates advanced threat analysis, allowing for early detection of unusual activities, which is crucial in mitigating risks.
- Risk Intelligence Platforms: Integrate real-time risk intelligence feeds that offer insights into emerging dangers. By remaining aware of the most recent vulnerabilities and attack methods, entities can adjust their defenses in advance, ensuring a strong security stance.
By adopting these technologies, organizations can not only protect sensitive information but also foster trust among patients and stakeholders. Investing in these advanced technologies is not just a choice; it's a necessity for healthcare organizations aiming to maintain their integrity and trust in a digital age.
Foster a Culture of Continuous Improvement in Threat Analysis
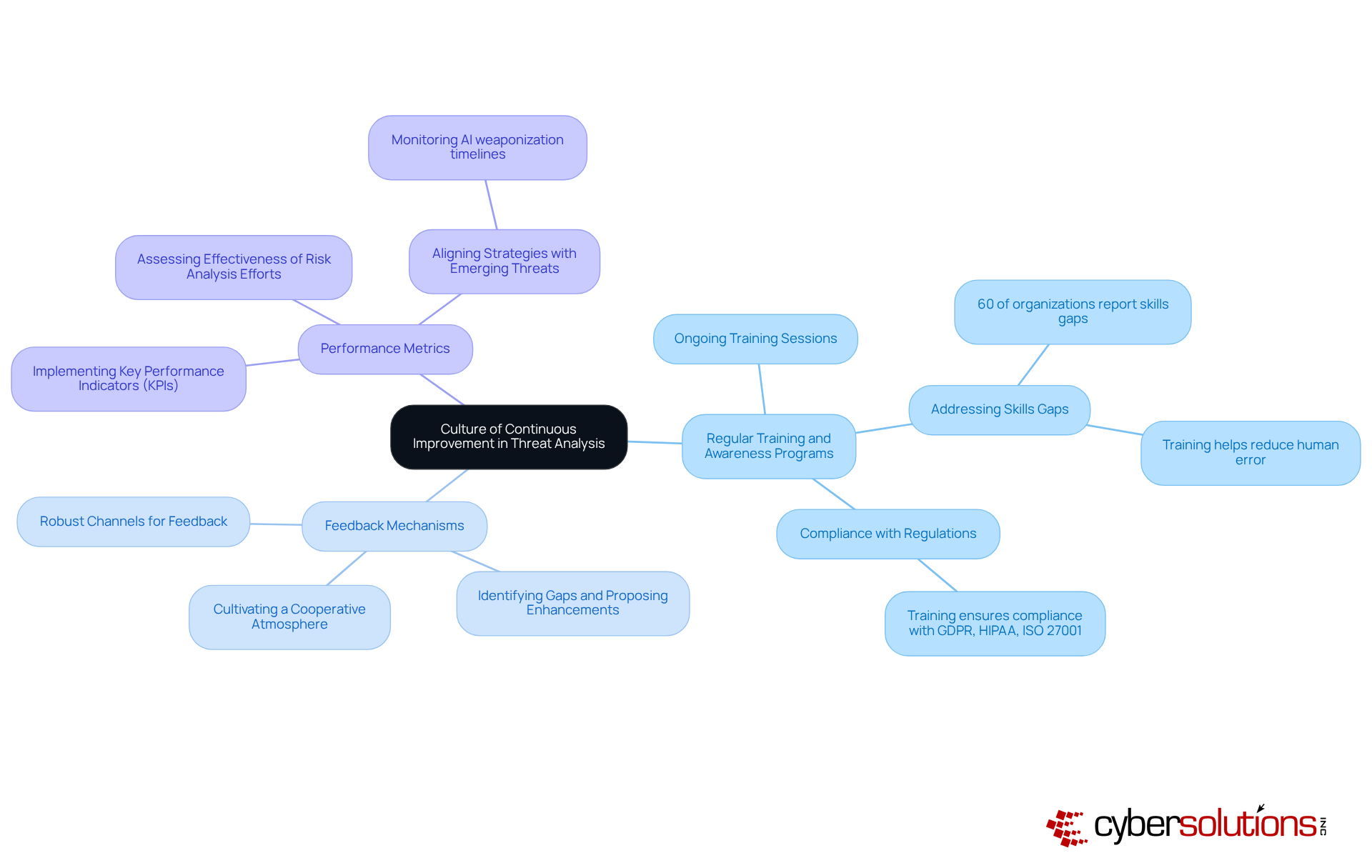
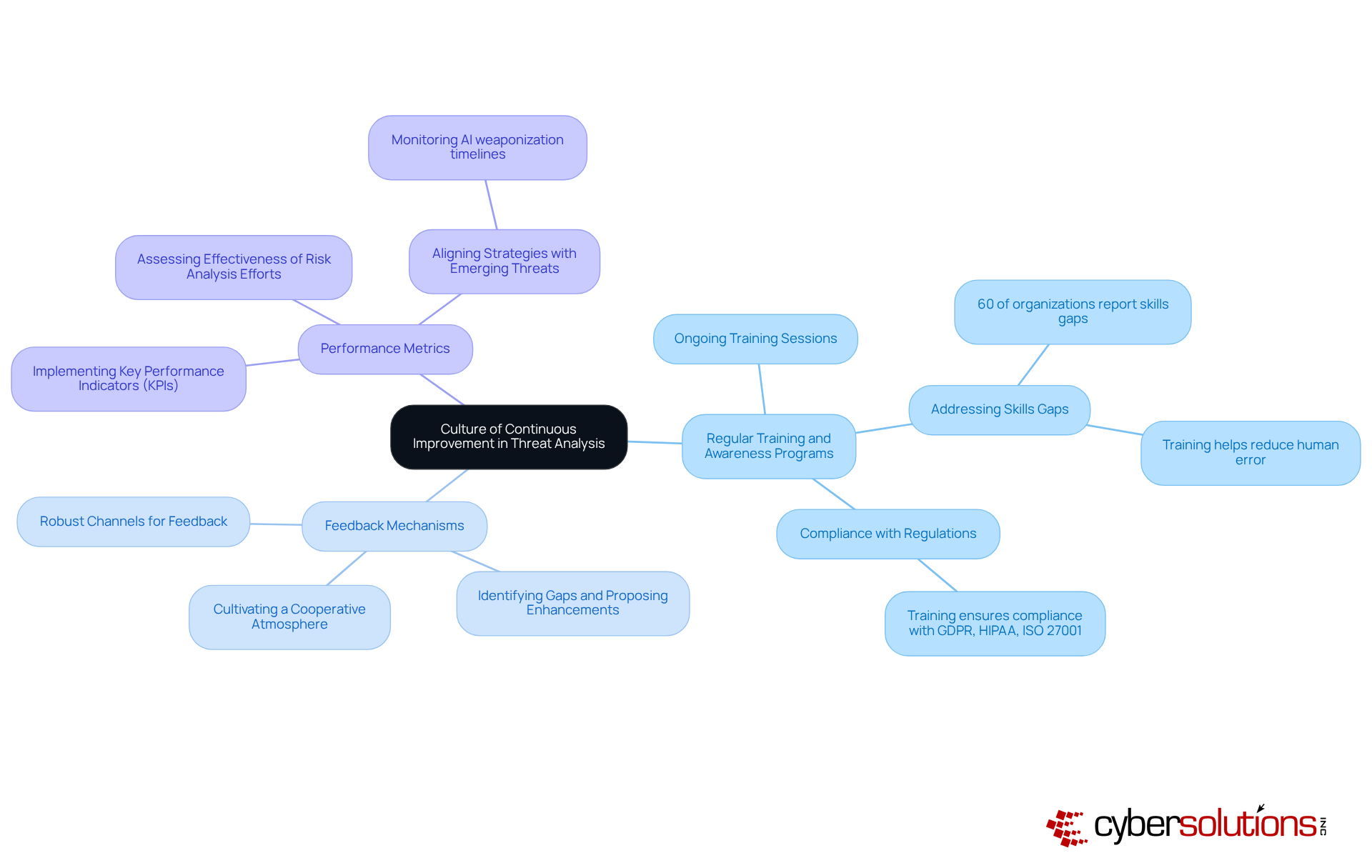
In an era where cyber threats are evolving at an unprecedented pace, healthcare organizations must prioritize cybersecurity to safeguard sensitive patient data and maintain trust. To cultivate a culture of continuous improvement in threat analysis, organizations should prioritize the following strategies:
- Regular Training and Awareness Programs: Ongoing training sessions are essential to keep employees updated on the latest threats and best practices in cybersecurity. With 60% of organizations identifying skills gaps as a significant issue, this proactive approach not only enhances individual skills but also strengthens the organization's overall security posture.
- Feedback Mechanisms: Establishing robust channels for feedback on risk analysis processes is crucial. These mechanisms allow teams to exchange insights, recognize gaps, and propose enhancements, cultivating a cooperative atmosphere that improves risk detection and response abilities. Organizations must proactively identify and mitigate common pitfalls in these mechanisms to ensure their cybersecurity strategies remain robust.
- Performance Metrics: Implementing key performance indicators (KPIs) allows entities to assess the effectiveness of their risk analysis efforts. By examining these metrics, companies can identify areas for improvement and ensure that their strategies stay in line with emerging dangers, such as the decreasing interval between the public launch of AI capabilities and their weaponization by malicious actors.
Investing in continuous improvement not only fortifies defenses but also enables organizations to utilize advanced threat analysis to outpace the ever-changing landscape of cyber threats. As Rob T. Lee, SANS chief AI officer, emphasizes, organizations need to invest in the skills of their existing personnel to navigate the complexities of the current threat landscape.
Conclusion
In an era where cyber threats loom larger than ever, the healthcare sector must prioritize cybersecurity to protect sensitive patient information. Organizations struggle to keep sensitive information secure amidst rising cyber threats. By understanding the fundamentals of risk assessment and implementing effective methodologies, they can enhance their cybersecurity posture and proactively address evolving threats.
Key insights from this article highlight the importance of:
- Continuous monitoring
- Threat modeling
- The integration of advanced technologies such as AI and behavioral analytics
These practices not only help in identifying vulnerabilities and potential threats but also ensure a swift response to incidents, thereby minimizing damage and maintaining operational integrity. Additionally, regular training and feedback mechanisms play a vital role in cultivating a resilient cybersecurity environment.
By investing in advanced threat analysis, organizations can transform their cybersecurity approach and build resilience against evolving threats. As cyber threats become increasingly sophisticated, embracing these best practices will empower organizations to stay ahead of potential risks and safeguard their critical assets. By taking decisive action today, organizations can not only protect their assets but also foster trust and resilience in an unpredictable digital landscape.
Frequently Asked Questions
What is advanced threat analysis in the context of cybersecurity?
Advanced threat analysis involves a systematic examination of potential dangers to an organization's information systems, understanding various types of risks, their origins, and their possible effects on business operations.
What are the key components of advanced threat analysis?
The key components include Threat Identification, Vulnerability Assessment, and Risk Assessment.
What does Threat Identification entail?
Threat Identification involves recognizing various threat actors, such as hackers, insiders, and nation-states, and understanding their motives.
What is involved in a Vulnerability Assessment?
A Vulnerability Assessment evaluates the organization's systems to identify weaknesses that could be exploited by threats.
How is Risk Assessment defined in advanced threat analysis?
Risk Assessment evaluates the probability of a threat taking advantage of a vulnerability and the possible repercussions of such an occurrence.
Why is continuous risk monitoring important for organizations?
Continuous risk monitoring is important because it ensures that suspicious activities are detected and stopped before they escalate into significant threats, helping to protect businesses from ransomware, phishing, and other malware attacks.
What is Compliance as a Service (CaaS)?
Compliance as a Service (CaaS) provides end-to-end solutions to satisfy regulatory requirements, streamline the compliance process, and offer audit support for organizations.
How can organizations benefit from prioritizing advanced threat analysis and continuous monitoring?
By prioritizing advanced threat analysis and continuous monitoring, organizations can defend against attacks and foster trust and resilience in their operations.
List of Sources
- Understand the Fundamentals of Advanced Threat Analysis
- 2026 Global Threat Report | Latest Cybersecurity Trends & Insights | CrowdStrike (https://crowdstrike.com/en-us/global-threat-report)
- Top Cybersecurity Threats [2025] (https://onlinedegrees.sandiego.edu/top-cyber-security-threats)
- Cybersecurity Forecast 2026 (https://cloud.google.com/security/resources/cybersecurity-forecast)
- Cybersecurity Trends 2026 | IBM (https://ibm.com/think/insights/more-2026-cyberthreat-trends)
- Navigating the Cyber Threat Landscape: 2026 Outlook and Emerging Risks (https://panorays.com/blog/cyber-threat-landscape-2026-emerging-risks)
- Implement Effective Methodologies for Threat Analysis
- 2026 Global Threat Report | Latest Cybersecurity Trends & Insights | CrowdStrike (https://crowdstrike.com/en-us/global-threat-report)
- Navigating the Cyber Threat Landscape: 2026 Outlook and Emerging Risks (https://panorays.com/blog/cyber-threat-landscape-2026-emerging-risks)
- STRIDE vs. DREAD vs. PASTA: Choosing the Right Threat Modeling Framework (https://apiiro.com/blog/stride-vs-dread-vs-pasta-choosing-the-right-threat-modeling-framework)
- The Top Cybersecurity Threats in 2026 & How to Prevent Them | Prime Secured (https://primesecured.com/top-cybersecurity-threats-2026-and-prevention)
- Leverage Technology for Enhanced Threat Detection
- AI and Cybersecurity: An Extended Report 2026 - AI World Journal (https://aiworldjournal.com/ai-and-cybersecurity-an-extended-report-2026)
- 9 AI Cybersecurity Trends to Watch in 2026 (https://sentinelone.com/cybersecurity-101/data-and-ai/ai-cybersecurity-trends)
- New And Expanding Cyberthreats To Watch For In 2026 (https://forbes.com/councils/forbestechcouncil/2026/01/05/new-and-expanding-cyberthreats-to-watch-for-in-2026)
- Must-Have Cybersecurity Tools for 2026 (https://uscsinstitute.org/cybersecurity-insights/blog/must-have-cybersecurity-tools-for-2026)
- AI Cybersecurity Statistics 2026 (Q1+Q2) (https://cybersecstats.com/ai-cybersecurity-statistics-2026-q1-q2)
- Foster a Culture of Continuous Improvement in Threat Analysis
- Annual Threat Dynamics 2026: Cyber threats in motion (https://pwc.com/gx/en/issues/cybersecurity/cyber-threat-intelligence/annual-threat-dynamics.html)
- Cybersecurity training and events for 2026 | CMS Information Security and Privacy Program (https://security.cms.gov/posts/cybersecurity-training-and-events-2026)
- SANS 2026 report flags cybersecurity skills crisis, putting critical infrastructure and OT sectors at measurable breach risk - Industrial Cyber (https://industrialcyber.co/reports/sans-2026-report-flags-cybersecurity-skills-crisis-putting-critical-infrastructure-and-ot-sectors-at-measurable-breach-risk)
- Preparing for looming national cyber security threats in 2026 and beyond | Federal News Network (https://federalnewsnetwork.com/commentary/2026/01/preparing-for-looming-national-cyber-security-threats-in-2026-and-beyond)
- Why Cybersecurity Training is the Smartest Investment for Organization in 2026 (https://uscsinstitute.org/cybersecurity-insights/blog/why-cybersecurity-training-is-the-smartest-investment-for-organization-in-2026)