Introduction
As cyber threats evolve, the stakes for organizations, especially those collaborating with the Department of Defense, have never been higher. The Cybersecurity Maturity Model Certification (CMMC) framework provides a structured approach to enhance security practices, ensuring organizations meet compliance requirements while effectively protecting sensitive information. Organizations often struggle to understand the intricate requirements of CMMC compliance. How can they implement best practices to achieve certification while fostering a culture of security that adapts to evolving threats? Let’s explore essential strategies that can empower organizations on their compliance journey.
Understand the CMMC Framework and Its Importance
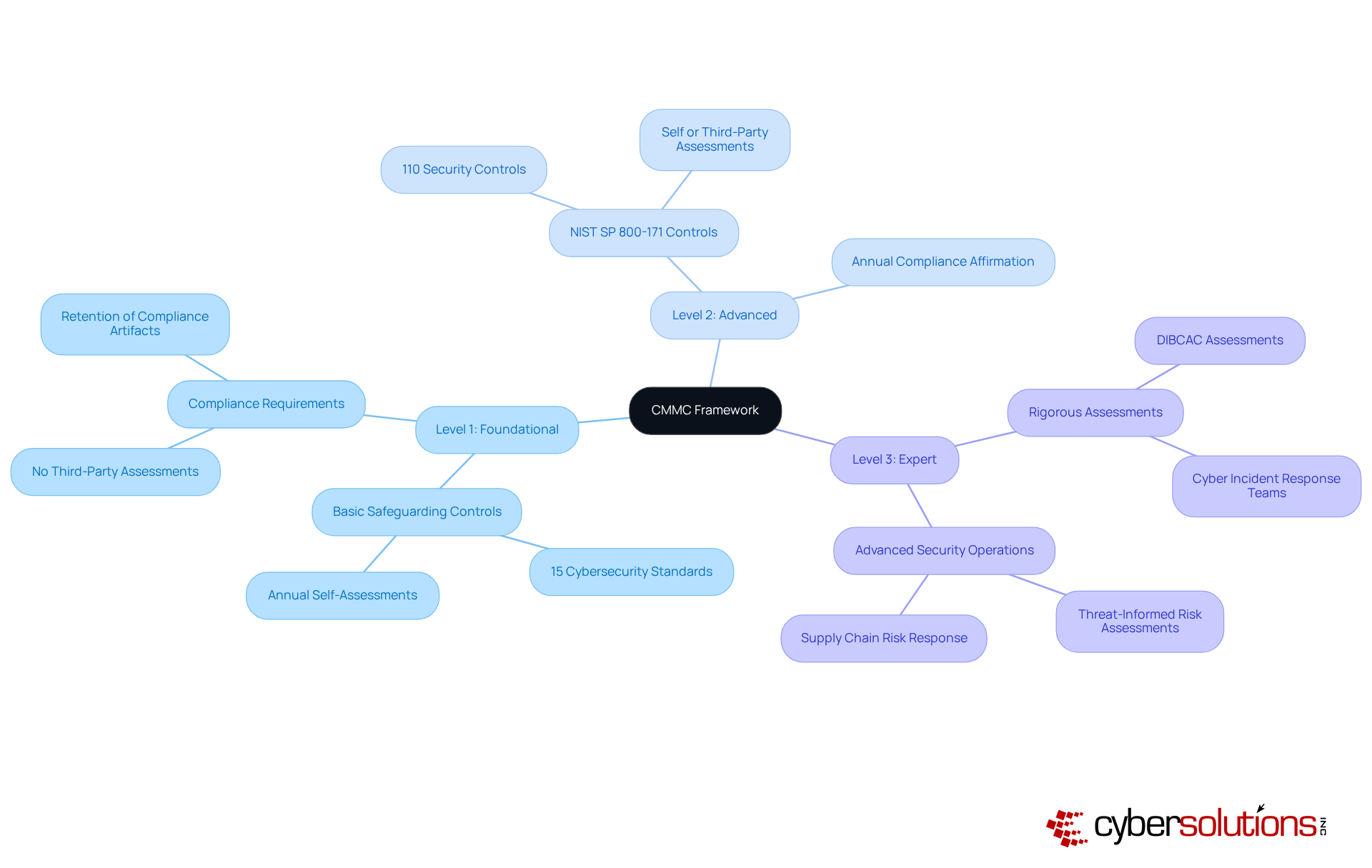
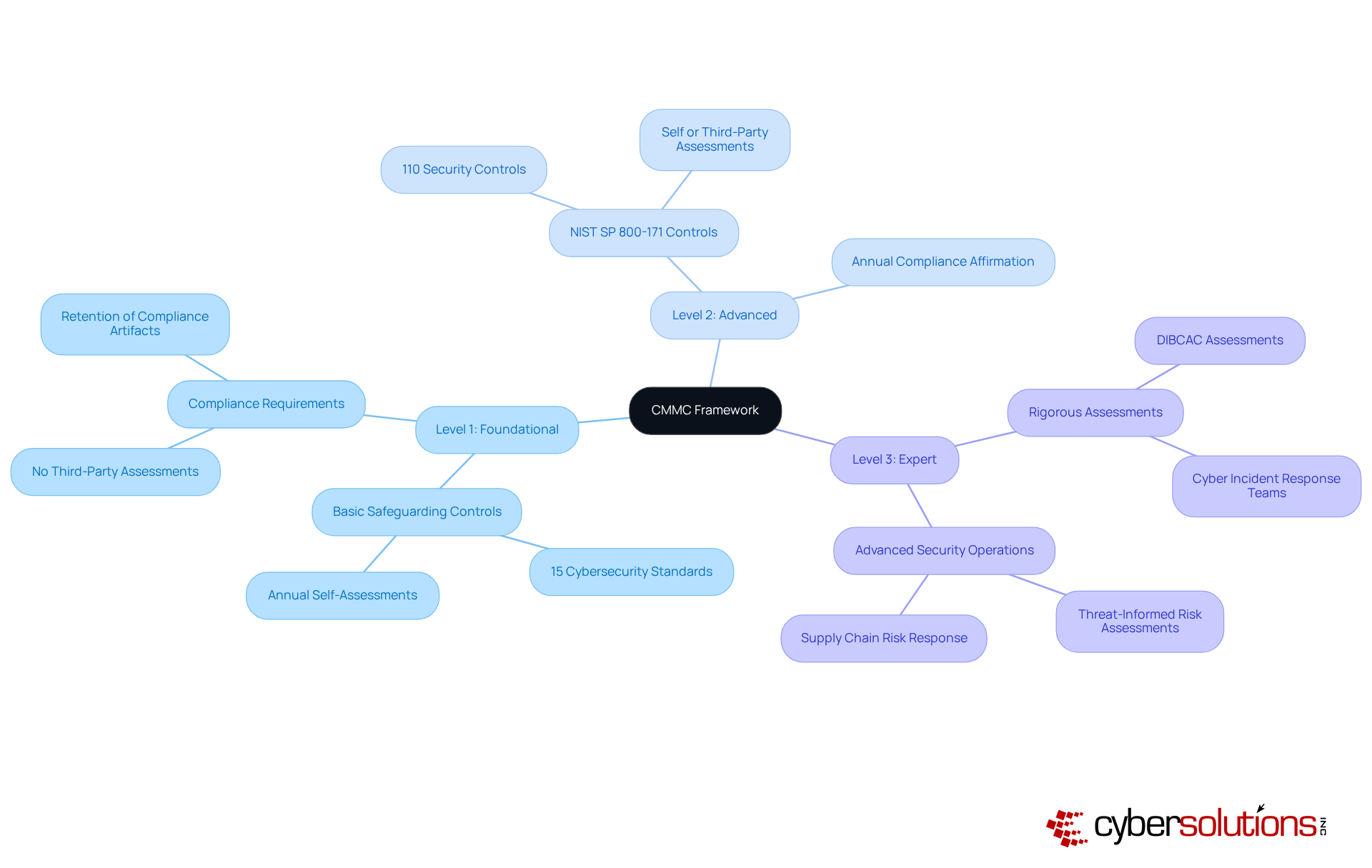
In an era where cyber threats loom larger than ever, the importance of robust cybersecurity in healthcare cannot be overstated. The CMMC processes are essential for entities involved with the Department of Defense (DoD) that aim to enhance their cybersecurity posture. This framework consists of three maturity levels, each requiring specific practices and CMMC processes to safeguard Controlled Unclassified Information (CUI).
Meeting these standards isn’t just about ticking boxes; it’s about fostering a culture that prioritizes security and actively mitigates risks. By implementing these cybersecurity practices, organizations not only fortify defenses against cyber threats but also secure eligibility for lucrative DoD contracts. Recent updates to the cybersecurity framework underscore the importance of ongoing monitoring and documentation, which are vital for maintaining standards and demonstrating a strong cybersecurity stance.
For instance, contractors must conduct yearly evaluations and retain necessary documents for six years, ensuring readiness for the evolving regulatory landscape. Real-world examples show that entities adopting these standards have significantly improved their operational integrity, reducing vulnerabilities and enhancing their overall security framework. As the implementation of security standards escalates, prioritizing these practices is not just a compliance measure; it’s a strategic imperative for success in the defense contracting arena.
Prepare for CMMC Compliance: Essential Steps to Take
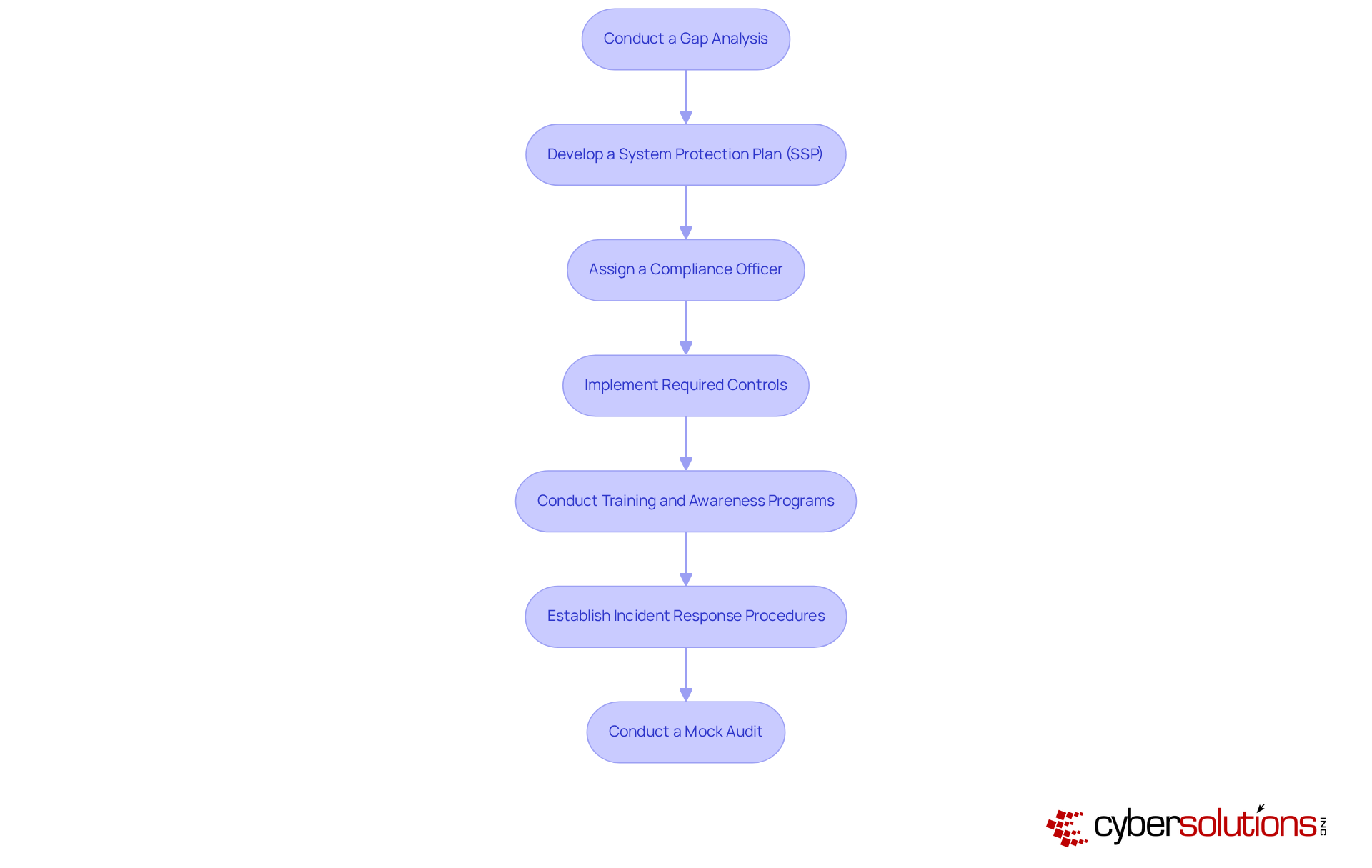
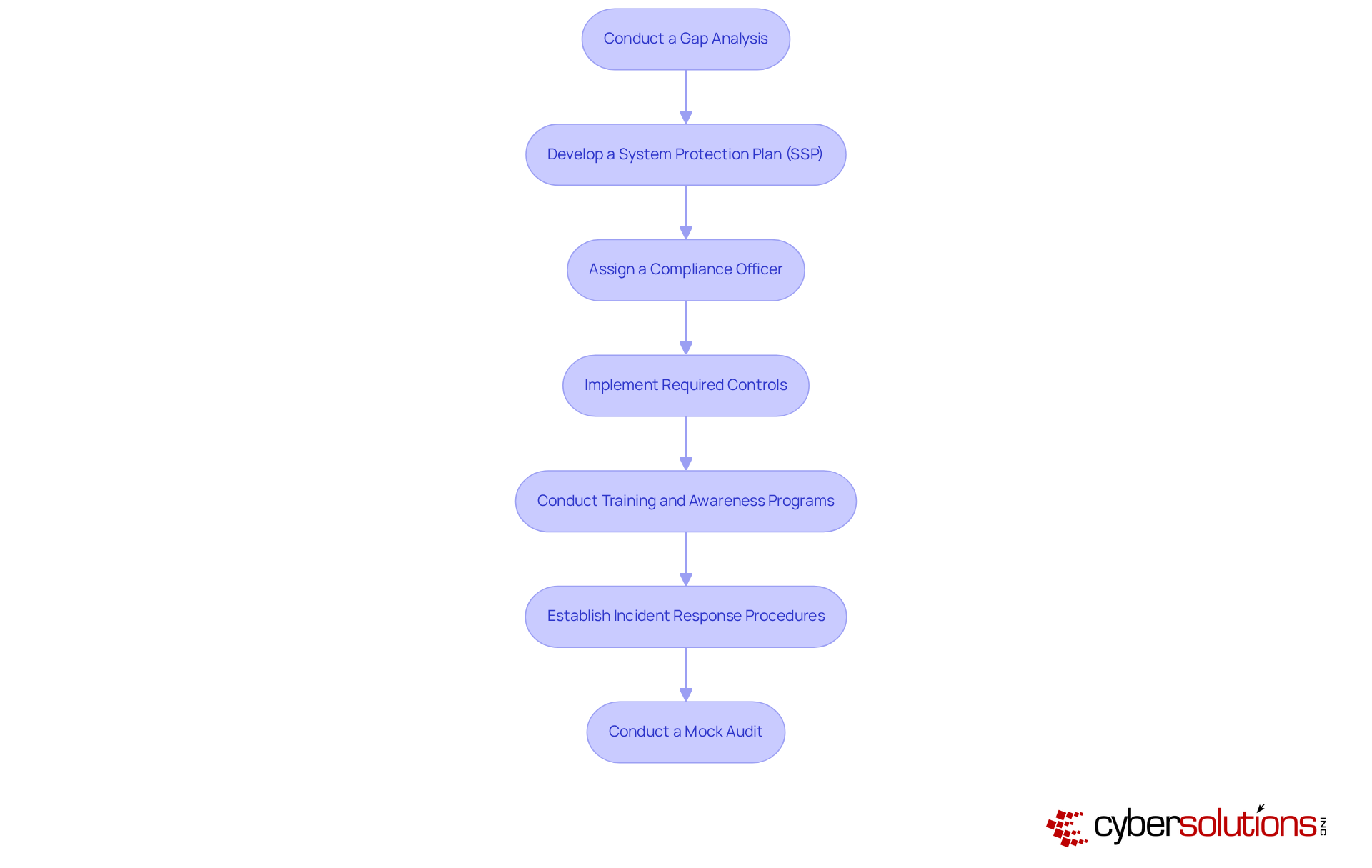
In an era where cybersecurity threats loom large, healthcare organizations must prioritize compliance to safeguard sensitive information and maintain trust. To effectively prepare for compliance, entities should undertake the following essential steps:
- Conduct a Gap Analysis: Evaluate current cybersecurity practices against CMMC processes to pinpoint areas needing enhancement. This analysis is crucial, as organizations that perform effective gap analyses can prioritize remediation efforts and avoid surprises during assessments. With tailored remediation strategies, Cyber Solutions helps organizations bridge regulatory gaps, ensuring they stay ahead of compliance challenges.
- Develop a System Protection Plan (SSP) that creates a comprehensive document detailing existing protective measures and outlines how they will align with CMMC processes. Accurate documentation is essential for meeting standards and successful certification, as it serves as the foundation for demonstrating adherence to requirements. Cyber Solutions assists in preparing detailed documentation, including security policies and procedures, to support organizations during audits.
- Assign a Compliance Officer: Designate a responsible individual or team to oversee adherence initiatives and ensure accountability. Organizations with a dedicated compliance officer are better positioned to manage their compliance status effectively.
- Implement Required Controls: Based on the findings from the gap analysis, prioritize and execute necessary protective measures, particularly those that safeguard Controlled Unclassified Information (CUI). This step is essential for meeting the 110 security practices mandated at Level 2. Cyber Solutions offers expert advice to ensure that entities meet these stringent cybersecurity standards.
- Conduct Training and Awareness Programs: Educate employees about their roles in maintaining compliance and the significance of cybersecurity. Awareness initiatives can greatly improve a company's overall defense stance.
- Establish Incident Response Procedures: Develop and document clear procedures for responding to security incidents, ensuring that the entity can act swiftly and effectively when threats arise.
- Conduct a Mock Audit: Perform a mock audit to identify any remaining issues and ensure preparedness for the official assessment.
By following these steps, companies can establish a strong basis for attaining CMMC processes and enhancing their cybersecurity structure. Without a proactive approach to compliance, organizations risk not only their certification but also the integrity of their operations and the trust of their patients. As Matt Graham stresses, "One of the major pitfalls I observe in Phase One is just poor or incomplete documentation," underscoring the significance of thorough documentation in the regulatory process.
Implement Continuous Monitoring and Assessment for Sustained Compliance
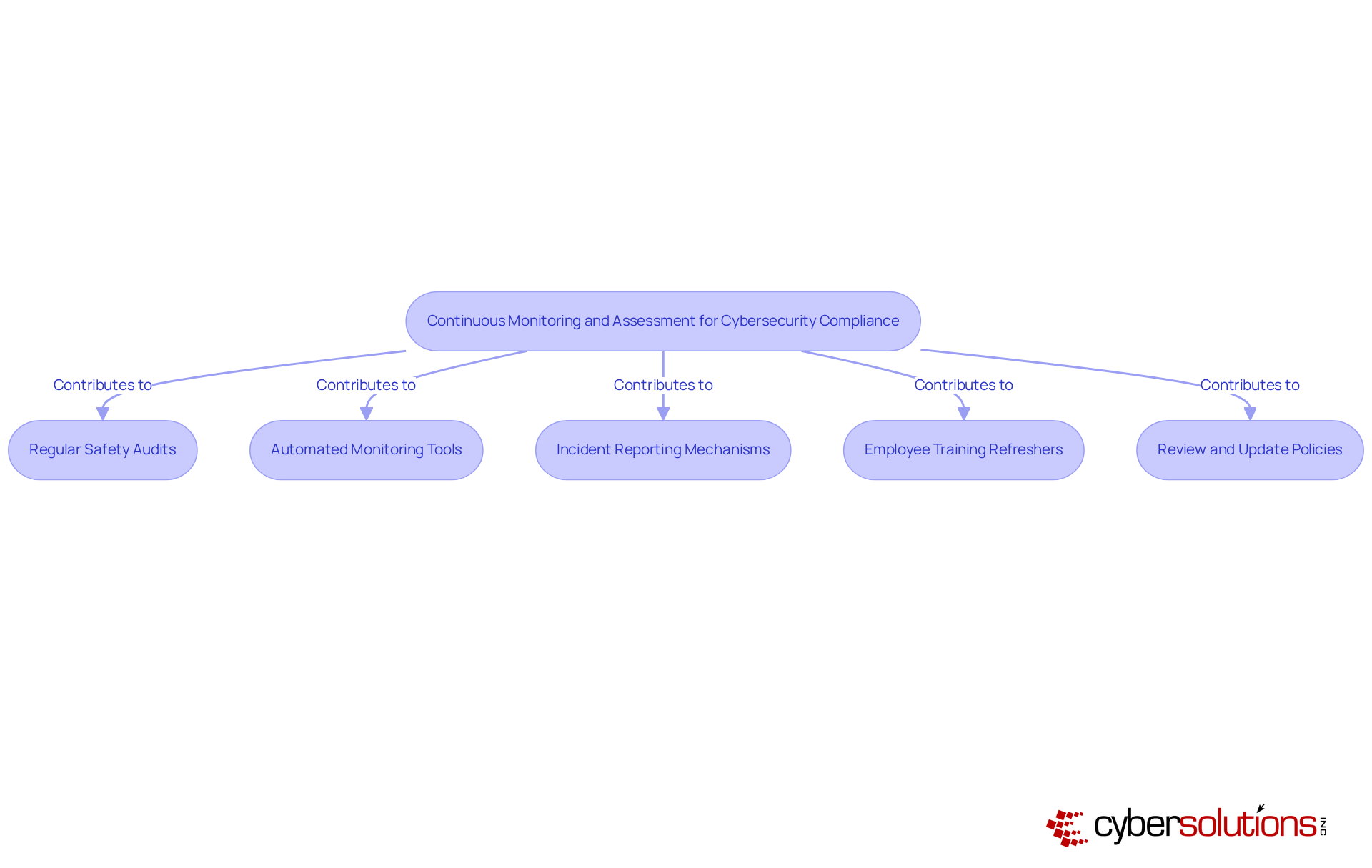
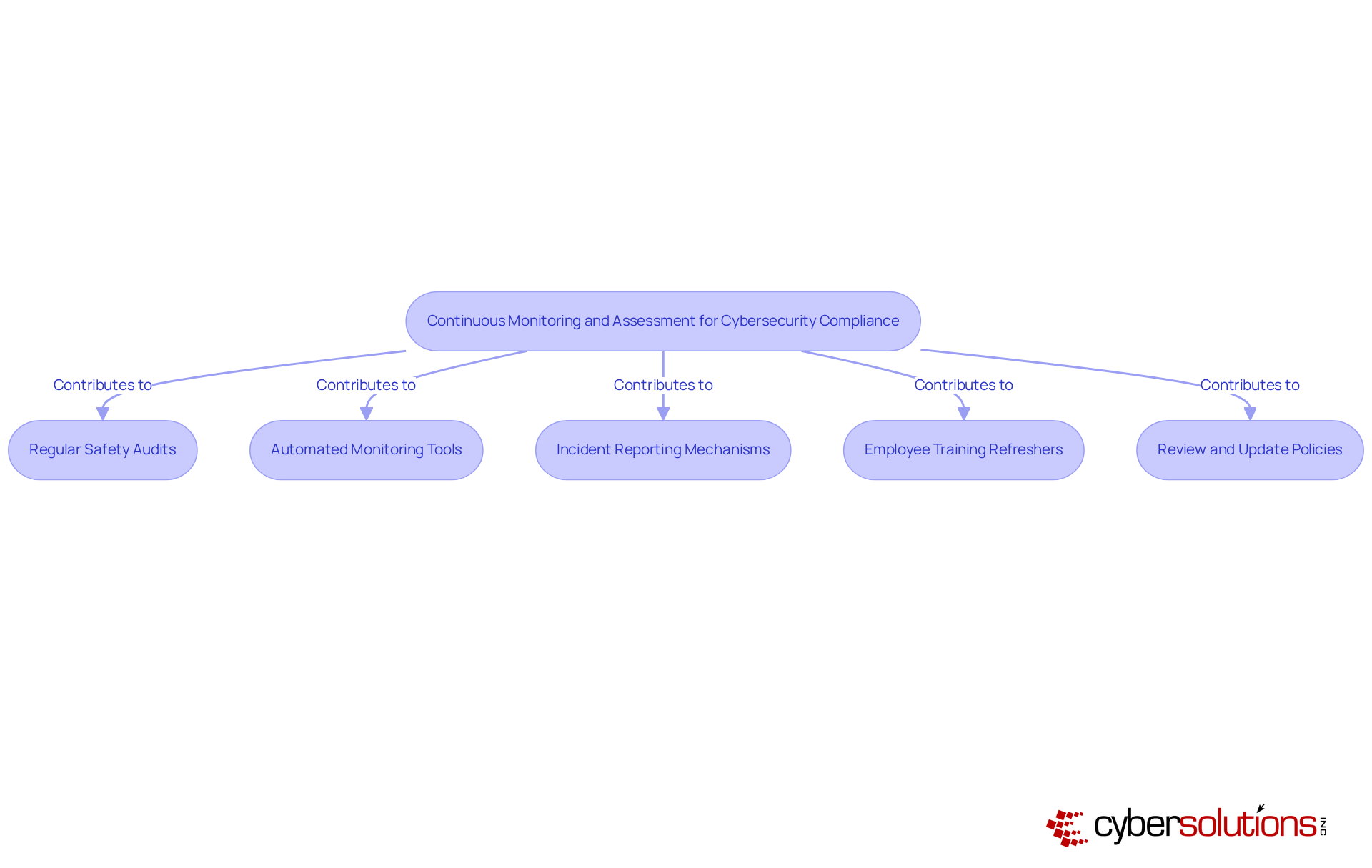
In an era where cyber threats loom larger than ever, the healthcare sector must prioritize robust cybersecurity measures to safeguard sensitive patient data. To achieve and uphold adherence to CMMC processes, entities must focus on continuous monitoring and evaluation practices. Key components include:
- Regular Safety Audits: Conducting periodic evaluations is essential for assessing the effectiveness of protective measures and identifying any gaps. This proactive strategy helps organizations stay ahead of compliance obligations and improves their overall defense posture.
- Automated Monitoring Tools: The adoption of automated monitoring tools is crucial for ensuring real-time visibility into cybersecurity measures. These technologies streamline the monitoring process, allowing organizations to detect and respond to threats swiftly.
- Incident Reporting Mechanisms: Establishing clear procedures for reporting and responding to safety incidents is vital. Recording and examining incidents not only assists in adherence to regulations but also guides future enhancements in protective measures.
- Employee Training Refreshers: It's crucial to keep training programs fresh to tackle new threats and meet changing regulations. Reinforcing the importance of cybersecurity among staff fosters a culture of vigilance and preparedness.
- Review and Update Policies: Ongoing assessment and modification of security policies are crucial to align with changes in the compliance framework and emerging cybersecurity threats.
By implementing these strategies, organizations can not only comply with CMMC processes but also strengthen their defenses against future threats. Embracing these practices not only ensures compliance but also empowers organizations to proactively defend against the ever-evolving landscape of cyber threats.
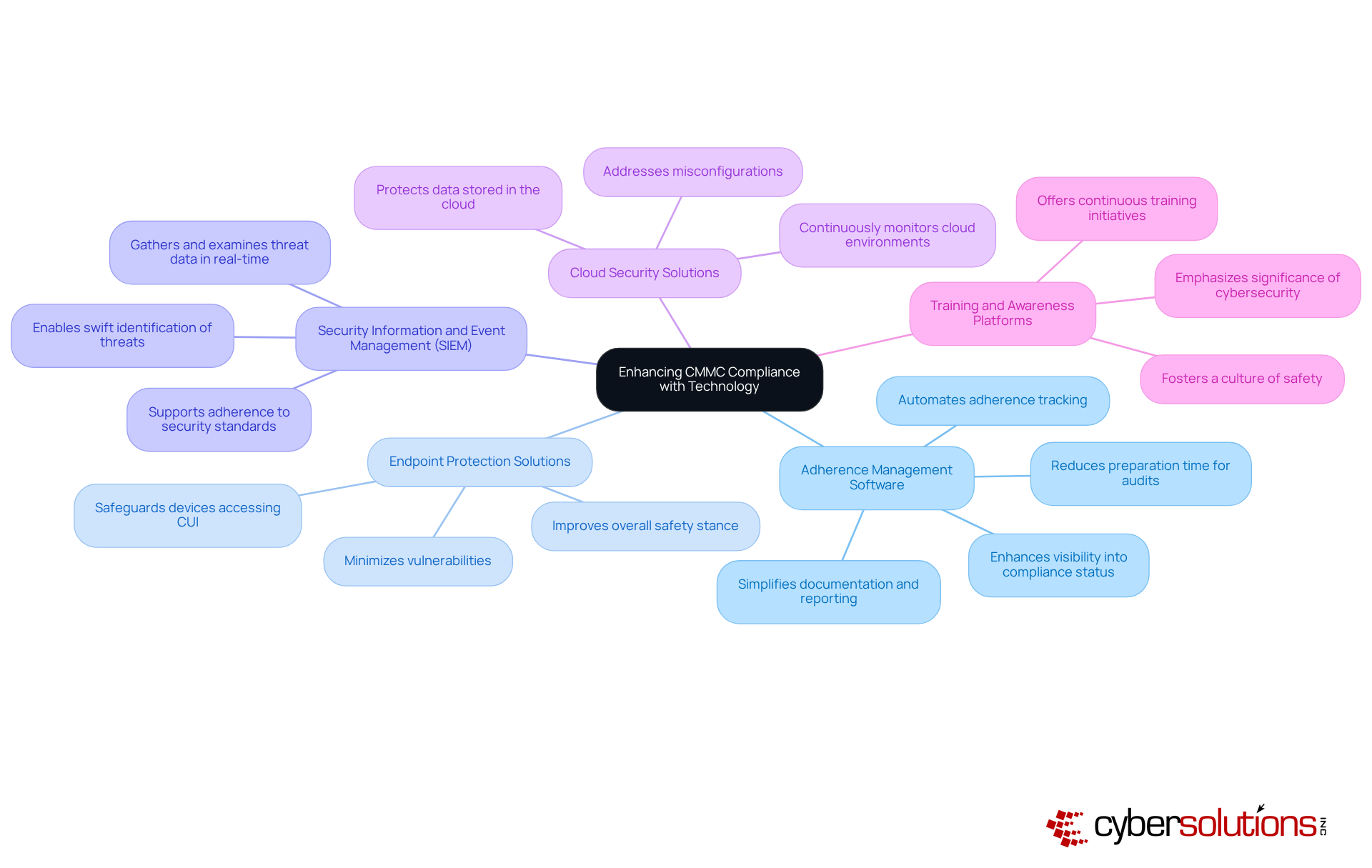
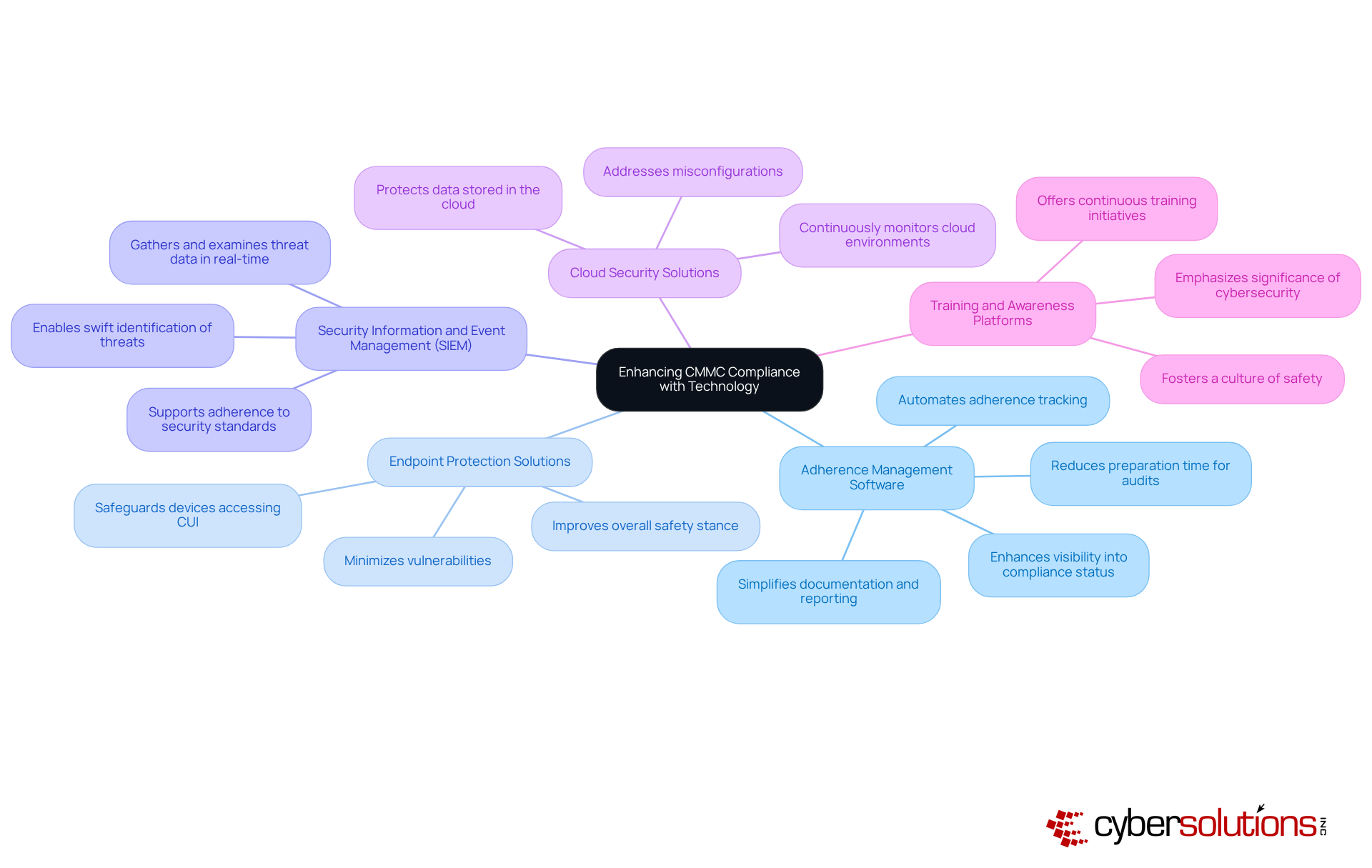
In an era where healthcare data breaches are on the rise, the need for robust cybersecurity measures has never been more critical. Organizations can leverage a variety of technologies and tools to bolster their CMMC compliance efforts effectively:
- Adherence Management Software: Implementing software solutions that automate adherence tracking, documentation, and reporting simplifies the management of CMMC processes. These tools enhance visibility into compliance status and streamline evidence collection, significantly reducing preparation time for audits.
- Endpoint Protection Solutions: Utilizing advanced endpoint protection tools is crucial for safeguarding devices that access Controlled Unclassified Information (CUI). These solutions guarantee that all endpoints are protected, minimizing vulnerabilities and improving the overall safety stance.
- Security Information and Event Management (SIEM): Implementing SIEM solutions enables organizations to gather and examine data related to threats in real-time. This capability allows swift identification and reaction to threats, which is crucial for upholding adherence to security standards.
- Cloud Security Solutions: Cloud-based security tools are vital for protecting data stored in the cloud. These solutions ensure adherence to CMMC processes for data protection by continuously monitoring cloud environments and addressing misconfigurations.
- Training and Awareness Platforms: Investing in platforms that offer continuous training and awareness initiatives for employees emphasizes the significance of cybersecurity and adherence. Consistent training fosters an environment of safety within the establishment, ensuring that all personnel comprehend their responsibilities in upholding regulations.
Failing to prioritize these technologies could leave your organization vulnerable to devastating breaches and compliance failures.
Conclusion
In an era where cyber threats are increasingly sophisticated, the CMMC framework emerges as a crucial safeguard for organizations engaging with the Department of Defense. By embracing the CMMC framework, entities can protect sensitive information, improve their security posture, and position themselves favorably for future contracts. A proactive approach to compliance, continuous monitoring, and technology integration highlight the need for organizations to make cybersecurity a core operational priority.
Throughout the article, we've highlighted key strategies for achieving and maintaining CMMC compliance. Conducting gap analyses, developing thorough documentation, assigning dedicated compliance officers, and implementing necessary controls are essential steps that pave the way for successful adherence. Additionally, continuous monitoring and leveraging advanced technology tools play critical roles in sustaining compliance and fortifying defenses against emerging cyber threats. These practices not only ensure regulatory alignment but also enhance operational integrity and trustworthiness.
It's clear that adopting these best practices is essential. As cyber threats continue to evolve, organizations must remain vigilant and proactive in their compliance efforts. Investing in training, utilizing innovative technology, and fostering a culture of cybersecurity will not only secure compliance but also empower organizations to navigate the complexities of the modern cyber landscape. Ultimately, the choice to prioritize CMMC compliance is a strategic investment in the future security and success of your organization.
Frequently Asked Questions
What is the CMMC framework?
The CMMC (Cybersecurity Maturity Model Certification) framework is a set of processes designed to enhance cybersecurity for entities involved with the Department of Defense (DoD). It consists of three maturity levels, each requiring specific practices to safeguard Controlled Unclassified Information (CUI).
Why is the CMMC framework important for healthcare and defense contractors?
The CMMC framework is crucial for healthcare and defense contractors as it helps them improve their cybersecurity posture, protect sensitive information, and secure eligibility for lucrative DoD contracts. It fosters a culture of security and actively mitigates risks associated with cyber threats.
What are the key components of the CMMC framework?
The key components of the CMMC framework include three maturity levels, each with specific practices and processes that organizations must implement to secure their systems and information.
How does the CMMC framework impact an organization’s culture?
Implementing the CMMC framework encourages organizations to prioritize security, fostering a culture that actively mitigates risks rather than merely complying with regulations.
What are the requirements for contractors under the CMMC framework?
Contractors must conduct yearly evaluations and retain necessary documentation for six years to demonstrate ongoing compliance and readiness for evolving regulatory standards.
How do organizations benefit from adopting the CMMC standards?
Organizations that adopt CMMC standards have shown significant improvements in operational integrity, reduced vulnerabilities, and enhanced overall security frameworks.
What is the significance of ongoing monitoring and documentation in the CMMC framework?
Ongoing monitoring and documentation are vital for maintaining compliance with CMMC standards and demonstrating a strong cybersecurity stance, which is essential for success in the defense contracting arena.
List of Sources
- Understand the CMMC Framework and Its Importance
- At Long Last, Cybersecurity Maturity Model Certification 2.0 Takes Effect - ConsensusDocs (https://consensusdocs.org/news/at-long-last-cybersecurity-maturity-model-certification-2-0-takes-effect)
- GAO report highlights risks to CMMC rollout as nation-state attacks target defense contractors - Industrial Cyber (https://industrialcyber.co/reports/gao-report-highlights-risks-to-cmmc-rollout-as-nation-state-attacks-target-defense-contractors)
- CMMC: New Era of Cybersecurity Compliance for Defense Contractors | Alston & Bird (https://alston.com/en/insights/publications/2025/11/cmmc-cybersecurity-compliance-defense)
- This Is Not a Drill: Cybersecurity Maturity Model Certification Goes into Effect on November 10, 2025 [Alert] (https://cozen.com/news-resources/publications/2025/this-is-not-a-drill-cmmc-will-go-into-effect-on-november-10-2025)
- CMMC 2.0 in 2026: What Defense Contractors Must Do Now (https://trustconsultingservices.com/cmmc-2-0-in-2026-defense-compliance-guide)
- Prepare for CMMC Compliance: Essential Steps to Take
- The Definitive Guide to CMMC in 2026 (https://strikegraph.com/blog/cmmc-overview)
- Planning Your 2026 CMMC Compliance Roadmap (https://cybersheath.com/resources/blog/planning-your-2026-cmmc-compliance-roadmap)
- CMMC Phase 2: What to Expect and How to Prepare [2026] (https://secureframe.com/blog/cmmc-phase-2-preparation)
- CMMC Basics: A Practical 2026 Roadmap for CMMC Compliance (https://securitymetrics.com/blog/cmmc-compliance-roadmap)
- Navigating CMMC Changes in 2026: What You Need to Know (https://vc3.com/blog/navigating-cmmc-changes-in-2026)
- Implement Continuous Monitoring and Assessment for Sustained Compliance
- CMMC 2.0 in 2026: What Defense Contractors Must Do Now (https://trustconsultingservices.com/cmmc-2-0-in-2026-defense-compliance-guide)
- CMMC Compliance in 2026: How Did We Get Here and What’s Coming Next (https://112cyber.com/blog/cmmc-compliance-in-2026)
- Continuous Compliance Monitoring: 2026 Technical Guide (https://apptega.com/blog/continuous-monitoring)
- FedRAMP and CMMC compliance deadlines are looming (https://washingtontechnology.com/opinion/2026/04/fedramp-and-cmmc-compliance-deadlines-are-looming/412995)
- CMMC Compliance in 2026: The Stakes Are High, But Success is Within Reach. (https://linkedin.com/pulse/cmmc-compliance-2026-stakes-high-success-eijqe)
- Leverage Technology and Tools to Enhance CMMC Compliance
- Rev. 3 is coming – Start preparing for the next CMMC requirement | Federal News Network (https://federalnewsnetwork.com/commentary/2026/04/rev-3-is-coming-start-preparing-for-the-next-cmmc-requirement)
- 7 Top CMMC Compliance Software Platforms to Simplify 2026 Audits (https://kiteworks.com/cmmc-compliance/cmmc-compliance-software-audit-readiness)
- Best CMMC Compliance Software 2026: Defense Contractor's Guide | PolicyCortex (https://policycortex.com/blog/best-cmmc-compliance-software-2026)
- CMMC Weekly Update (20-27 April 2026) (https://linkedin.com/pulse/cmmc-weekly-update-20-27-april-2026-vairavtechnology-ceaxc)
- Planning Your 2026 CMMC Compliance Roadmap (https://cybersheath.com/resources/blog/planning-your-2026-cmmc-compliance-roadmap)