
In the healthcare sector, the stakes of cybersecurity are higher than ever, as data breaches can lead to catastrophic outcomes. Understanding the complexities of cybersecurity compliance is crucial for organizations, especially given the unique challenges they face. This alarming statistic highlights the widespread struggle organizations face in achieving compliance: a staggering 91% of organizations fall short of full compliance.
So, how can entities effectively navigate the intricate steps required to master the NIST 800-171 compliance audit? Let’s dive into six essential steps that will empower organizations to enhance their security posture while ensuring adherence to critical regulatory standards.
In an era where data breaches can cripple healthcare organizations, understanding cybersecurity frameworks like NIST SP 800-171 is not just beneficial - it's essential. This framework establishes vital protection requirements for safeguarding Controlled Unclassified Information (CUI) within non-federal systems, making it crucial for organizations involved in defense contracting. Adhering to these standards not only fortifies security but also opens doors to federal contracts, reinforcing operational integrity.
Organizations need to familiarize themselves with the 14 control families and their specific requirements - this foundational knowledge is crucial for successful adherence. For instance, the DoD Assessment Methodology evaluates contractor adherence to these standards, ensuring that sensitive data is adequately protected. Moreover, entities that successfully apply NIST SP 800-171 can improve their competitive advantage in the federal contracting arena, as adherence is increasingly regarded as a prerequisite for obtaining government contracts.
Compliance as a Service (CaaS) provides businesses with end-to-end solutions to meet regulatory requirements, including assessments, policy development, continuous monitoring, proactive risk assessments, and preparation for a NIST 800-171 compliance audit. This service is particularly beneficial for small and medium-sized businesses, allowing them to access enterprise-level compliance expertise without the high cost of hiring in-house compliance staff. By embracing these standards, organizations not only safeguard their data but also enhance their standing in a competitive federal contracting landscape.
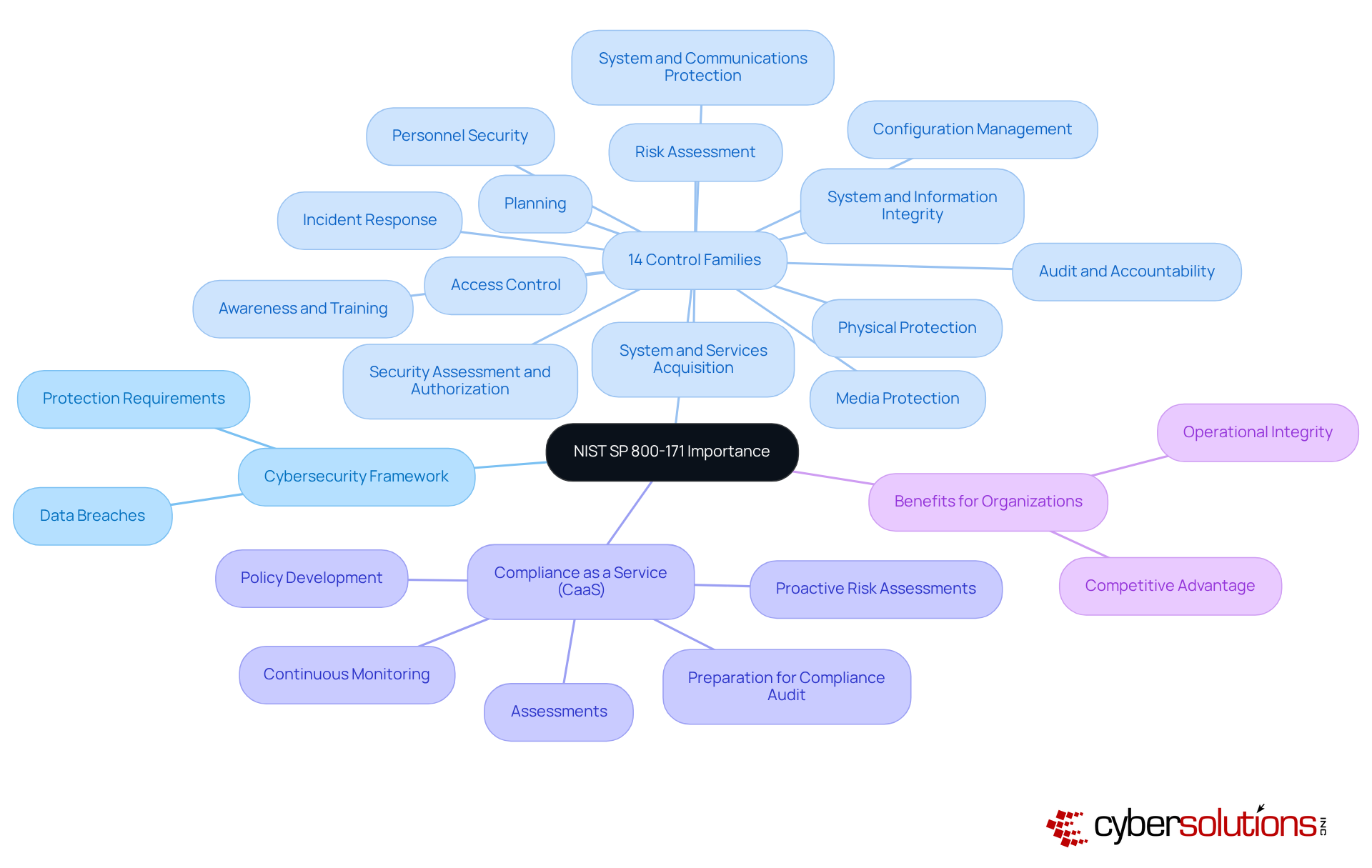
In an era where data breaches can cripple healthcare organizations, understanding NIST SP 800-171 is not just important - it's imperative for safeguarding sensitive information. This framework includes 14 categories of security requirements, each outlining specific measures that entities must adopt to protect Controlled Unclassified Information (CUI). These families encompass:
To effectively identify the requirements pertinent to your organization, start by assessing the types of CUI you manage and the associated risks. You need to evaluate each measure's importance and how thoroughly you need to implement it to boost your compliance efforts. Employing verification checklists can assist in ensuring that all required measures are considered.
Staggeringly, 91% of organizations have failed to fully implement the necessary controls, with an average compliance rate of only 39%. This highlights the pressing need for a comprehensive evaluation and proactive handling of CUI risks. Without a proactive approach, organizations risk severe data breaches and regulatory penalties, leaving them exposed to significant risks that extend beyond financial loss.

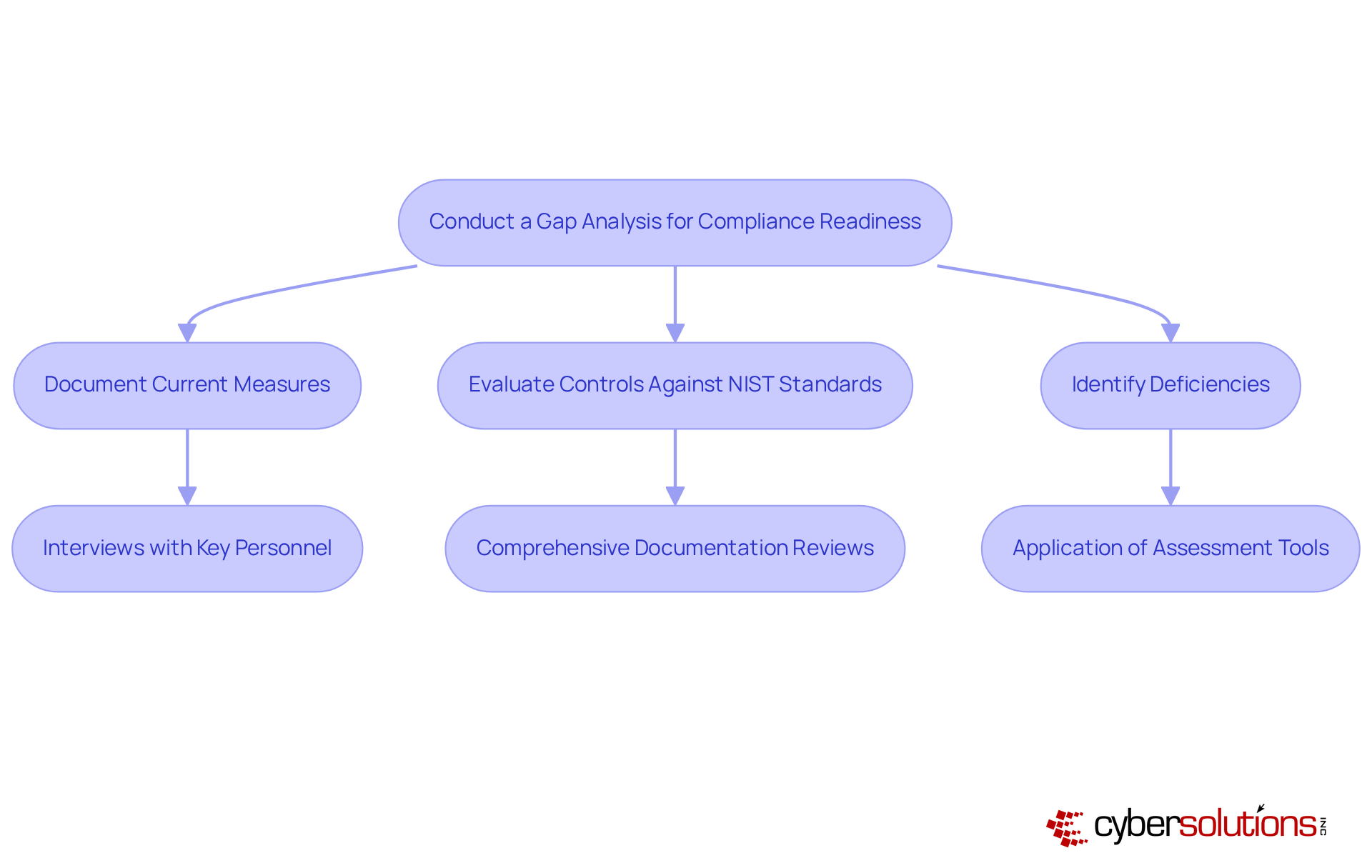
In an era where cyber threats loom large, healthcare organizations must prioritize robust cybersecurity measures to safeguard sensitive information. Conducting a gap analysis is essential for aligning your organization's security practices with the NIST 800-171 compliance audit requirements. Begin by thoroughly documenting your current measures and processes related to the protection of Controlled Unclassified Information (CUI).
How can you ensure your organization is truly secure? Evaluate each control against the NIST standards to pinpoint any deficiencies. This assessment can be achieved through:
The results from this gap analysis will not only emphasize areas requiring urgent enhancement but also direct the creation of your Plan of Action and Milestones (POA&M) for attaining NIST 800-171 compliance audit conformity. By taking these proactive steps, your organization not only meets compliance but also fortifies its defenses against evolving cyber threats.
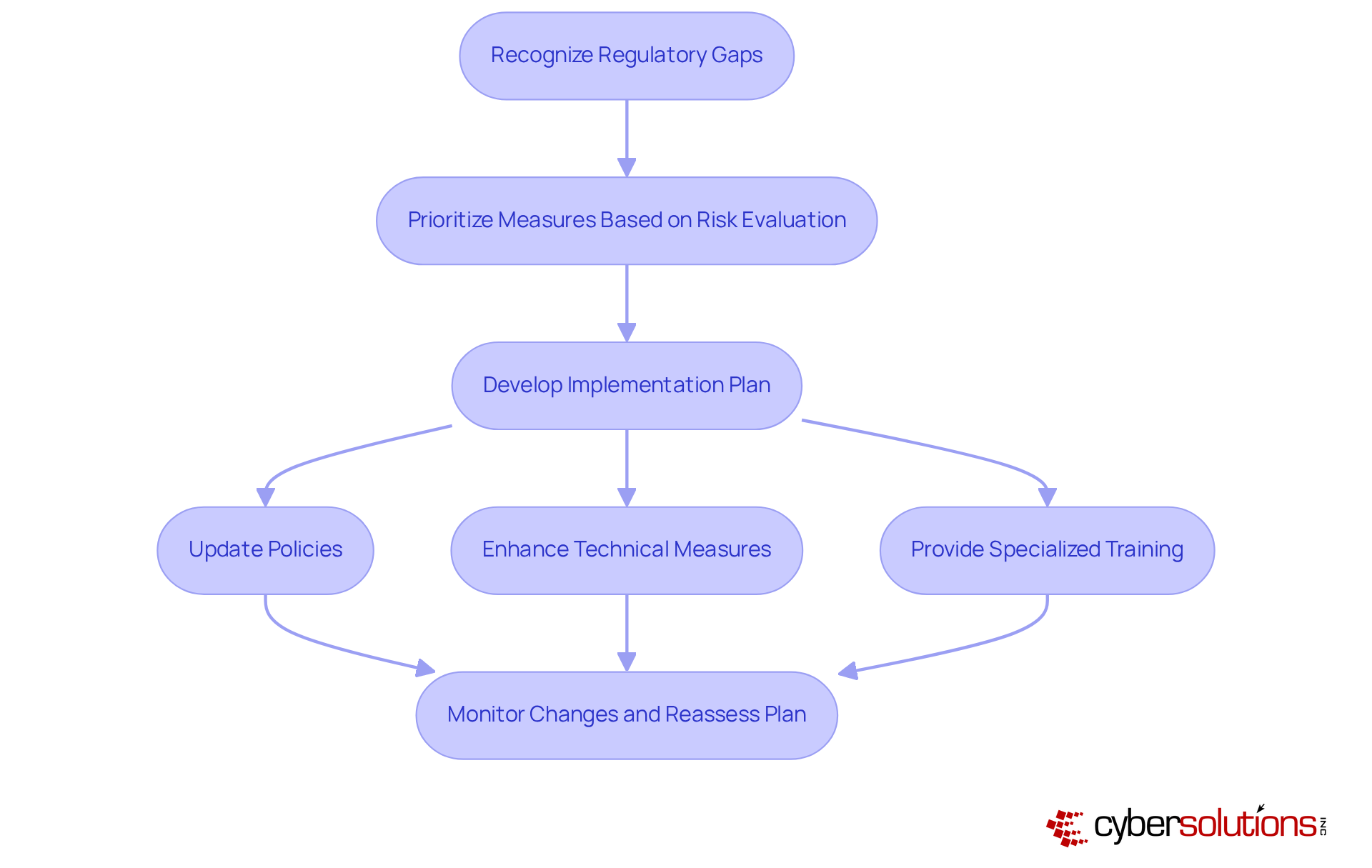
In an era where cybersecurity threats loom large, healthcare organizations must act decisively to safeguard their operations. After recognizing regulatory gaps, the next step is to implement the necessary changes effectively. Start by prioritizing measures based on the outcomes of your risk evaluation and the specific needs of your organization. Develop a comprehensive implementation plan that outlines the required actions, assigns responsibilities, and sets timelines for completion. This process might include:
Keep a close eye on all changes and make sure you have a solid record of your compliance efforts.
Frequently reassess and modify your implementation plan to respond to changing threats and regulatory demands, particularly considering GSA's revised guidance, which highlights the significance of cybersecurity adherence. With the U.S. Department of Justice reporting $6.8 billion in settlements related to cybersecurity compliance in fiscal year 2025, the financial risks of noncompliance are significant. By learning from entities that have successfully attained a NIST 800 171 compliance audit, you can better navigate the complexities of the regulatory landscape and ensure your entity remains resilient and compliant. Additionally, ensuring your systems meet stringent cybersecurity standards is crucial for protecting Controlled Unclassified Information (CUI) and Federal Contract Information (FCI), thereby maintaining eligibility for lucrative government contracts. Cyber Solutions emphasizes a layered approach to cybersecurity, which not only enhances recovery from incidents but also fosters strong partnerships with clients, ensuring they are well-equipped to handle future threats. Ultimately, the ability to adapt and respond to evolving threats will determine the future success of healthcare organizations in a competitive landscape.
In an era where healthcare organizations face unprecedented cybersecurity threats, the importance of robust documentation cannot be overstated. Documentation is essential for demonstrating adherence during a NIST 800-171 compliance audit.
How can you ensure that your Plan of Action and Milestones (POA&M) effectively identifies gaps and sets a clear timeline for remediation? Moreover, maintaining detailed records of training sessions and incident response strategies is crucial for demonstrating your commitment to a NIST 800-171 compliance audit. Did you know that 60% of regulatory failures stem from inadequate documentation? This statistic underscores the critical need for meticulous record-keeping.
Consistently revising your SSP to indicate alterations in adherence status or organizational structure ensures that it remains a dynamic document that precisely portrays your protective measures and practices. Involving cross-functional teams in the creation of the SSP not only enhances compliance but also strengthens your overall security posture.

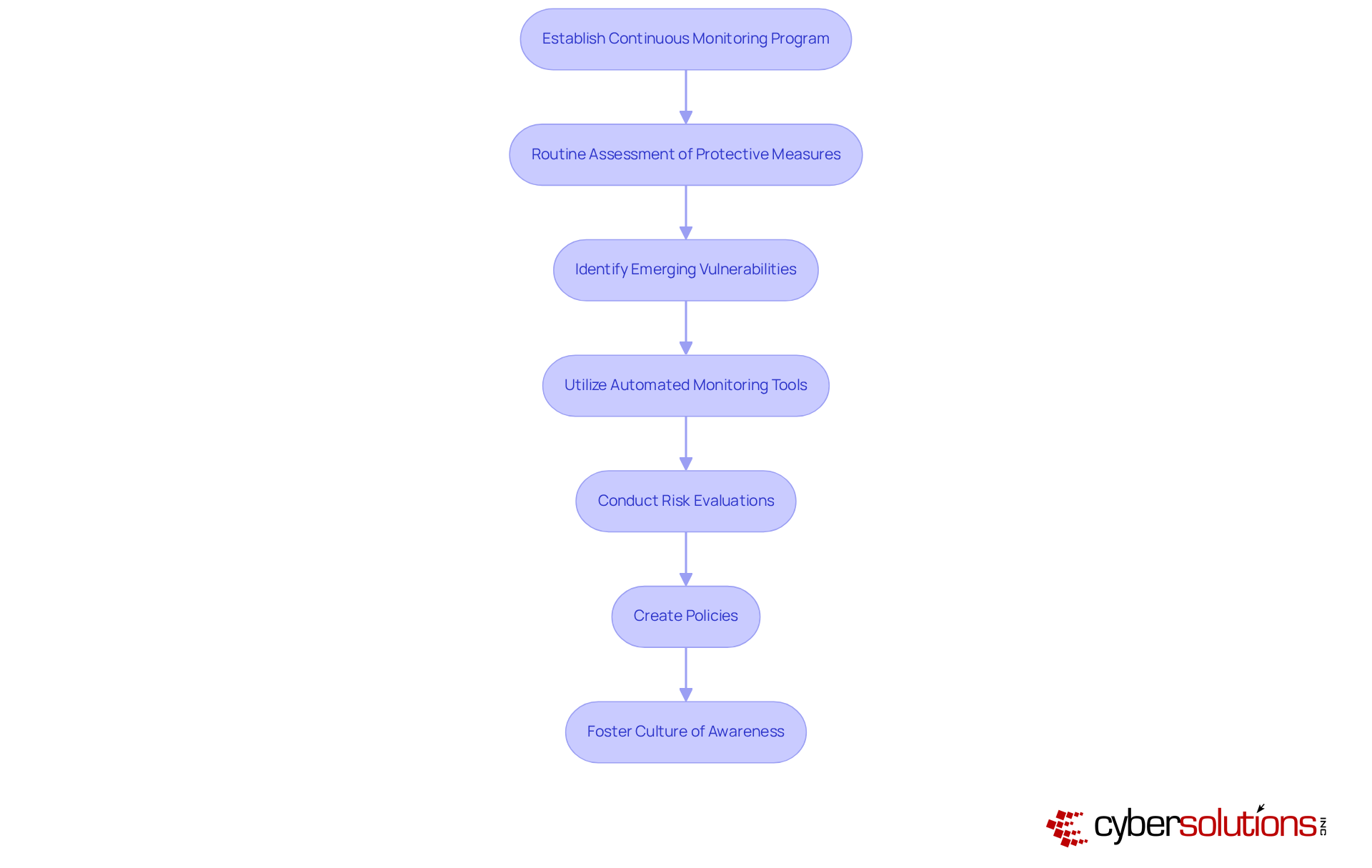
In an era where cyber threats loom large, the healthcare sector faces unprecedented challenges in safeguarding sensitive information. NIST 800 171 compliance audit is not just a checkbox; it requires a dedicated continuous monitoring program that adapts to new challenges. This program should routinely assess protective measures and identify emerging vulnerabilities, utilizing automated tools to monitor adherence status effectively.
Cyber Solutions' Compliance as a Service (CaaS) solutions streamline this process by offering risk evaluations, policy creation, and continuous oversight monitoring customized to meet the requirements of a NIST 800 171 compliance audit, as well as other standards such as HIPAA, PCI-DSS, CMMC, SOX, and GDPR. It's crucial for organizations to foster a culture of awareness, where every employee recognizes their vital role in maintaining compliance. Regular updates to policies and procedures are essential to adapt to evolving technologies, threats, and regulatory requirements, thereby ensuring that the entity remains compliant and secure.
By embracing continuous monitoring, organizations can significantly boost their compliance success rates and reinforce their security defenses. This not only enhances compliance but also strengthens overall security posture, as evidenced by organizations that have improved their defenses post-compliance. Without a proactive approach to compliance and security, organizations risk not only their reputation but also the trust of those they serve.
In an era where cyber threats loom large, mastering NIST 800-171 compliance is not just a regulatory checkbox; it’s a strategic necessity for organizations handling Controlled Unclassified Information (CUI). By understanding and implementing the framework's requirements, organizations can significantly enhance their cybersecurity posture while unlocking opportunities for federal contracts. Navigating the path to compliance can feel overwhelming, as it demands a solid understanding of control families, careful gap analysis, and proactive changes to your systems.
Throughout the article, key steps have been outlined to navigate the compliance audit effectively. These include:
Each step plays a vital role in ensuring that organizations not only meet compliance standards but also bolster their defenses against evolving cyber threats.
Ultimately, taking decisive action towards NIST 800-171 compliance today will not only safeguard your organization but also pave the way for future success in an increasingly challenging cybersecurity landscape. Embracing these practices not only protects sensitive information but also enhances operational integrity and competitiveness in the federal contracting landscape.
What is NIST SP 800-171 and why is it important?
NIST SP 800-171 is a cybersecurity framework that establishes protection requirements for safeguarding Controlled Unclassified Information (CUI) within non-federal systems. It is essential for organizations involved in defense contracting as it fortifies security and opens opportunities for federal contracts.
What are the main components of NIST SP 800-171?
NIST SP 800-171 includes 14 categories of security requirements, also known as control families, which outline specific measures organizations must adopt to protect CUI. These categories include Access Control, Awareness and Training, and Audit and Accountability, among others.
How can organizations assess their compliance with NIST SP 800-171?
Organizations can assess their compliance by evaluating the types of CUI they manage and the associated risks. They should use verification checklists to ensure all required measures are considered and determine the importance of each measure for boosting compliance efforts.
What is the current state of compliance among organizations regarding NIST SP 800-171?
Currently, 91% of organizations have failed to fully implement the necessary controls outlined in NIST SP 800-171, with an average compliance rate of only 39%. This indicates a significant gap in compliance efforts and the need for proactive handling of CUI risks.
What is Compliance as a Service (CaaS) and how does it help organizations?
Compliance as a Service (CaaS) provides businesses with end-to-end solutions to meet regulatory requirements, including assessments, policy development, continuous monitoring, and preparation for compliance audits. It is particularly beneficial for small and medium-sized businesses, allowing them to access enterprise-level compliance expertise without the high costs of hiring in-house staff.
What are the benefits of adhering to NIST SP 800-171 standards?
Adhering to NIST SP 800-171 standards not only safeguards sensitive data but also enhances an organization's competitive advantage in the federal contracting arena, as compliance is increasingly viewed as a prerequisite for obtaining government contracts.