
In an era where healthcare data breaches are alarmingly prevalent, the stakes for cybersecurity have never been higher. Managed cybersecurity services present a strategic solution, empowering healthcare CFOs to safeguard sensitive patient information while optimizing their IT budgets.
As the landscape of cyber threats continues to evolve, how can financial leaders ensure their organizations remain compliant with stringent regulations and resilient against potential attacks?
This article explores best practices for implementing managed cybersecurity in healthcare, equipping CFOs with the essential knowledge to navigate these challenges effectively.
In today's digital age, the importance of cybersecurity in healthcare cannot be overstated. Managed cybersecurity in medical settings involves outsourcing critical cybersecurity tasks to specialized providers who vigilantly monitor, detect, and respond to threats on behalf of medical entities. These services include essential components such as:
For healthcare organizations, leveraging these services is vital for effectively protecting their organizations against evolving threats while optimizing IT budgets.
Consider this: medical providers that collaborate with managed security services benefit from round-the-clock monitoring and rapid response capabilities—both crucial for minimizing downtime and safeguarding sensitive patient information. Continuous monitoring allows for the detection and cessation of suspicious activities before they escalate into significant threats, protecting against ransomware, phishing, and other malware attacks. This proactive strategy not only enhances overall security but also enables medical institutions to concentrate on their primary functions without the burden of cybersecurity tasks.
The trend towards outsourcing digital security is increasingly recognized as a strategic decision, with 81% of firms opting for external expertise to bolster their defenses. Moreover, organizations that utilize managed security services can achieve cost reductions of 20%-30%, making this a financially prudent choice in a sector where data breaches are on the rise. In 2023 alone, nearly 158 million medical records were compromised, highlighting the urgency of cybersecurity measures. Alarmingly, 58% of the 77.3 million individuals affected by data breaches in 2023 were victims of attacks on third-party providers within the medical field, underscoring the risks associated with in-house management.
By entrusting digital security to expert companies, healthcare providers can ensure compliance with stringent regulations while focusing their resources on delivering high-quality patient care. Implementing access controls and restrictions is also crucial for protecting sensitive patient data. A key feature of managed cybersecurity services is the presence of a security operations center, which offers continuous monitoring and rapid response capabilities essential for maintaining security. Case studies reveal that entities with a structured response plan and swift recovery mechanisms can recover more effectively from incidents, further emphasizing the significance of these services.

In the realm of healthcare, the significance of cybersecurity cannot be overstated. Healthcare organizations navigate a complex regulatory framework, encompassing pivotal laws such as the Health Insurance Portability and Accountability Act and the Health Information Technology for Economic and Clinical Health Act. These regulations impose stringent requirements for safeguarding patient data and ensuring privacy, making it imperative for CFOs to allocate resources effectively for compliance. Regular risk assessments and comprehensive training emerge as vital strategies that not only facilitate adherence to compliance standards but also mitigate potential risks.
The financial stakes are substantial; in 2023, the average data breach cost soared to $10.93 million, underscoring the urgent need for compliance measures. Non-compliance can result in severe penalties, with fines ranging from $141 per violation to over $2 million for serious infractions. Additionally, entities that fail to comply with GDPR may incur fines up to 4% of their annual global revenue, further emphasizing the financial ramifications of regulatory adherence.
Engaging with cybersecurity service providers can significantly streamline regulatory efforts. These providers offer managed cyber security solutions to ensure that all essential security protocols are implemented and regularly updated, allowing healthcare entities to focus on their core functions while upholding regulatory requirements. This proactive approach not only enhances compliance but also shields the organization from the substantial costs associated with non-compliance. As one regulatory officer aptly stated, "Compliance is challenging, but investing in adherence is crucial for safeguarding our organization and our patients." By prioritizing compliance, CFOs can bolster their organization's resilience against cyber threats and regulatory penalties.
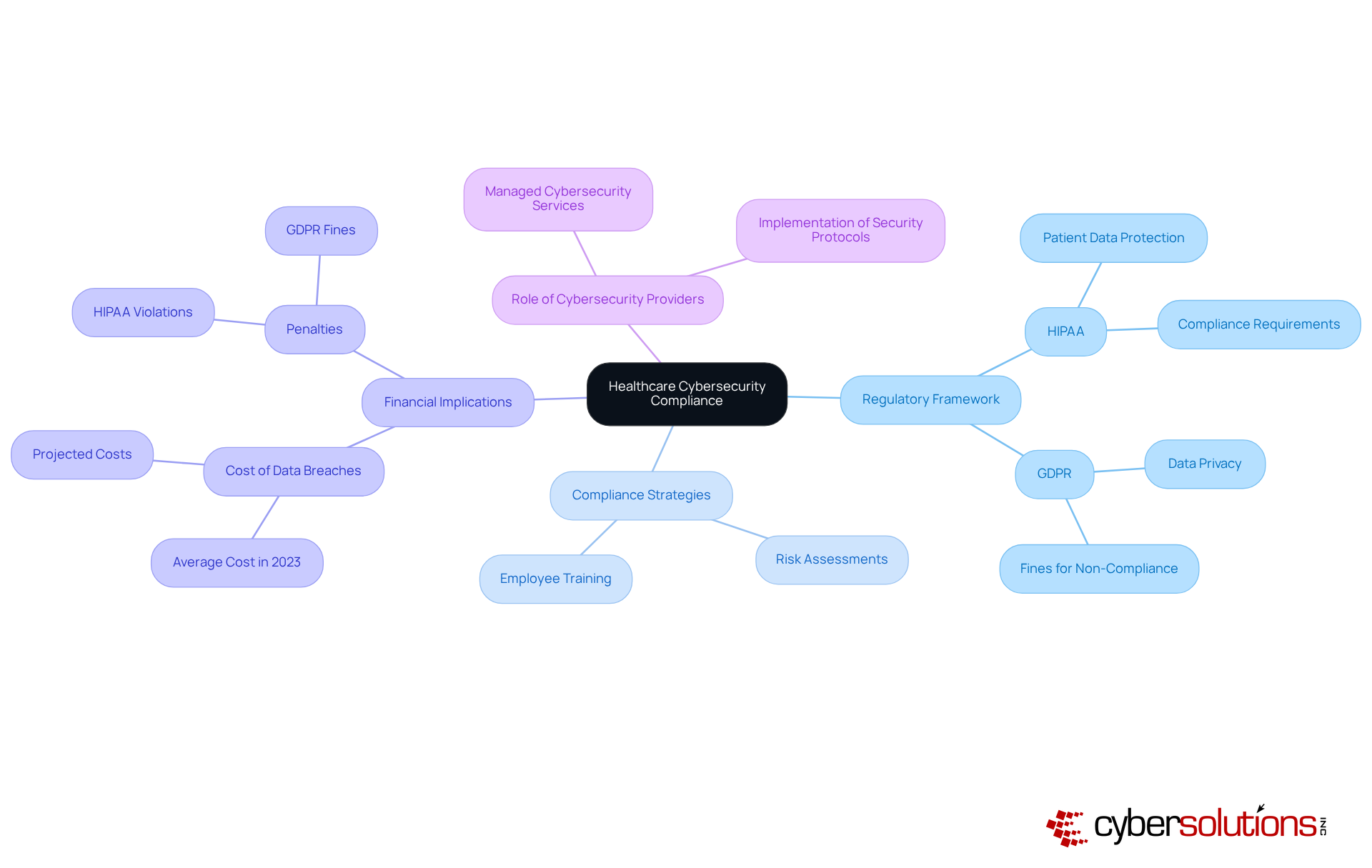
In today's digital landscape, the importance of robust cybersecurity in healthcare cannot be overstated. As cyber threats continue to evolve, healthcare CFOs must adopt and ensure effective security measures. The following strategies are essential for effectively implementing managed cybersecurity services:
By adopting these best practices, healthcare organizations can enhance their security posture, demonstrating to stakeholders their commitment to protecting patient data and maintaining trust.

In the realm of healthcare, the integration of managed cybersecurity services stands as a critical strategy for safeguarding sensitive patient data and ensuring compliance with regulatory standards. Outsourcing cybersecurity tasks to specialized providers enables healthcare CFOs to bolster their organizations' defenses against evolving cyber threats while optimizing operational costs. This proactive approach not only mitigates risks but also empowers medical professionals to focus on delivering quality care without the constant burden of cyber incidents.
The article delineates several key practices essential for effectively implementing managed cybersecurity:
These practices are pivotal in fortifying an organization’s security posture. Furthermore, leveraging advanced technologies can significantly enhance threat detection and response capabilities, ultimately fostering a more resilient healthcare environment.
As the landscape of cyber threats continues to evolve, it is imperative for healthcare organizations to prioritize their cybersecurity strategies. By adopting these best practices and engaging with managed cybersecurity services, CFOs can not only shield their institutions from financial and reputational damage but also ensure compliance with stringent regulations. The commitment to robust cybersecurity transcends a mere technical necessity; it is a vital component of delivering trustworthy and secure healthcare services in an increasingly digital world.
What are managed cybersecurity services in healthcare?
Managed cybersecurity services in healthcare involve outsourcing critical cybersecurity tasks to specialized providers who monitor, detect, and respond to cyber threats on behalf of medical entities.
What components are included in managed cybersecurity services?
Essential components include threat detection, incident response, vulnerability assessments, and compliance management.
Why is it important for financial officers in healthcare to leverage managed cybersecurity services?
It is vital for protecting their organizations against evolving cyber threats while optimizing IT budgets.
How do managed service providers (MSPs) benefit medical providers?
MSPs offer round-the-clock monitoring and rapid incident response, which are crucial for minimizing downtime and safeguarding sensitive patient information.
What are the advantages of continuous monitoring in managed cybersecurity?
Continuous monitoring allows for the detection and cessation of suspicious activities before they escalate, protecting against ransomware, phishing, and other malware attacks.
What is the trend regarding outsourcing digital security in healthcare?
The trend shows that 81% of firms are opting for external expertise to enhance their cybersecurity defenses.
How can organizations benefit financially from managed security services?
Organizations that utilize managed security services can achieve cost reductions of 20%-30%, making it a financially prudent choice in a sector with rising data breaches.
What statistics highlight the urgency of robust cybersecurity measures in healthcare?
In 2023, nearly 158 million medical records were compromised, and 58% of the individuals affected by data breaches were victims of attacks on third-party providers within the medical field.
How do managed cybersecurity services help ensure compliance?
By entrusting digital security to expert companies, healthcare providers can ensure compliance with stringent regulations while focusing on delivering high-quality patient care.
What is the role of a 24/7 Security Operations Center (SOC) in managed cybersecurity?
A SOC provides continuous monitoring and rapid incident response capabilities, which are essential for maintaining security in healthcare settings.
What do case studies reveal about structured response plans in cybersecurity?
Case studies indicate that entities with a structured response plan and swift incident response mechanisms can recover more effectively from incidents, highlighting the importance of managed cybersecurity services.