
In healthcare, where patient data is paramount, the escalating cybersecurity threats demand an unwavering commitment to robust managed services strategies. Organizations that embrace managed services not only streamline their IT operations but also enhance their ability to respond to vulnerabilities and compliance challenges. Yet, many organizations struggle to navigate the complexities of cybersecurity, often feeling overwhelmed by the myriad of options available.
How can they effectively assess their needs and choose the right service provider? This article delves into six best practices that guide organizations in crafting a resilient managed services strategy, ensuring they stay ahead in an increasingly competitive and perilous digital environment.
Without a robust managed services strategy, organizations risk falling victim to cyber threats that could compromise patient data and trust.
In an era where cybersecurity threats loom large, healthcare organizations must prioritize robust IT management to safeguard their operations. Managed solutions mean outsourcing your IT operations to a Managed Service Provider (MSP). This approach allows organizations to focus on their core activities while leveraging the MSP's expertise in monitoring, maintenance, and support. Imagine having 24/7 network monitoring at your fingertips, ready to alert you to any anomalies and vulnerabilities, so you can act quickly to prevent downtime or breaches.
The managed services strategy plays a vital role in IT. They enhance operational efficiency, provide scalability, and ensure compliance with industry regulations. Organizations using managed solutions see significant drops in downtime and faster incident response times. This is crucial for maintaining productivity and customer trust. Are you struggling to keep up with the demands of IT management while ensuring cybersecurity? Without these solutions, your organization could face significant operational setbacks and loss of customer trust.
With features like:
Integrating these solutions into your managed services strategy is essential to effectively tackle evolving technological challenges and threats. Successful implementations show that businesses can achieve not only cost efficiency but also strategic advantages, positioning themselves for growth and resilience in a competitive landscape. By embracing managed solutions, organizations not only enhance their operational resilience but also secure their future in an increasingly competitive landscape.

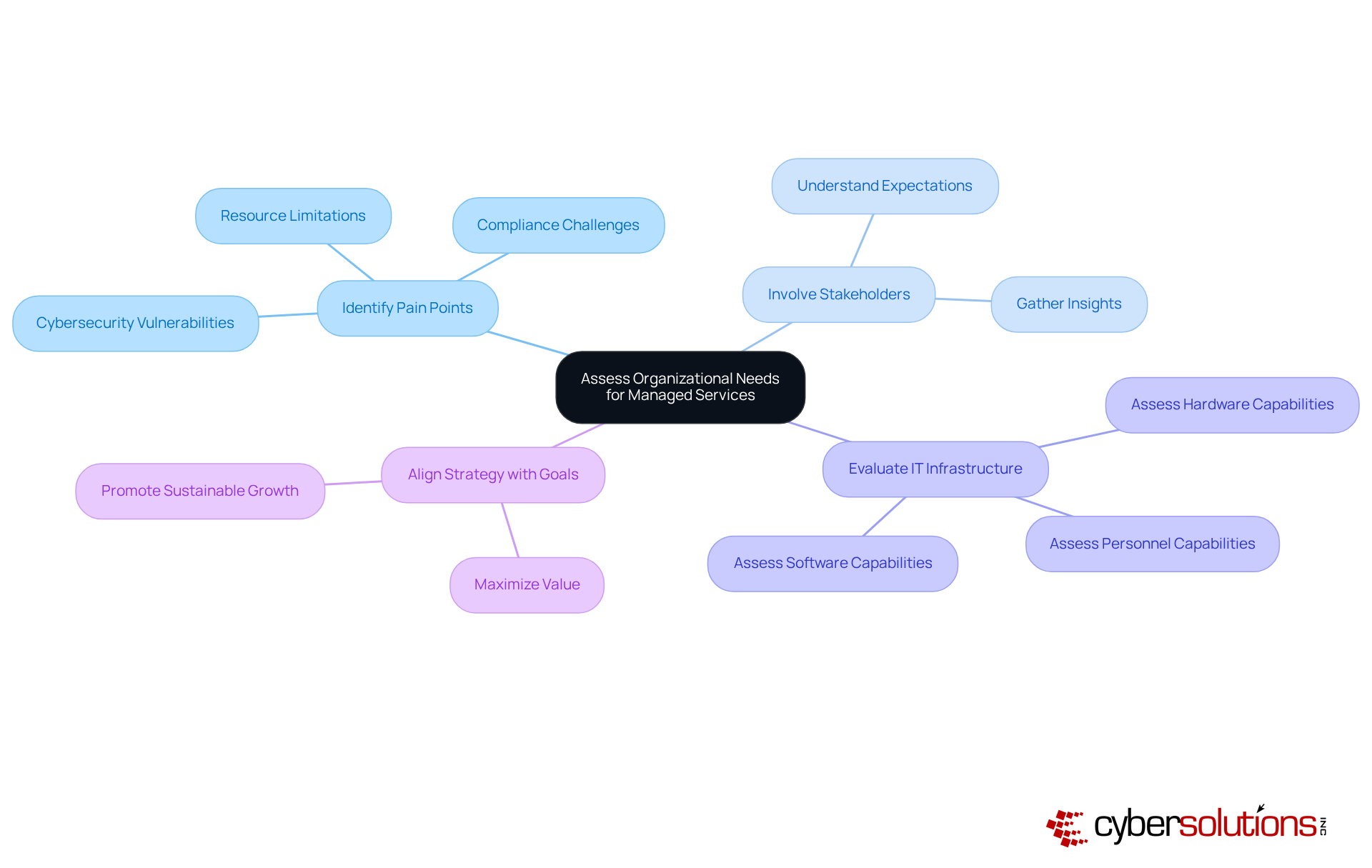
In an era where cybersecurity threats are escalating, healthcare organizations must prioritize a thorough evaluation of their IT environments to safeguard sensitive data. Start by pinpointing existing pain points, such as cybersecurity vulnerabilities, compliance challenges, and resource limitations. It's crucial to involve stakeholders from various departments to gather insights on their specific needs and expectations regarding the managed services strategy. Evaluating the current IT infrastructure - hardware, software, and personnel capabilities - will clarify the support needed.
As we approach 2026, organizations face increasing cybersecurity threats, making it essential to focus on vulnerabilities that could compromise sensitive data. Without a comprehensive assessment, many organizations struggle to pinpoint their cybersecurity vulnerabilities, risking exposure to significant threats. Aligning a managed services strategy with organizational goals ensures companies invest in solutions that deliver maximum value and promote sustainable growth.
This strategic approach not only enhances operational efficiency but also strengthens resilience against evolving digital threats. Failing to address these vulnerabilities could leave organizations exposed to significant risks, undermining their operational integrity and trust.
In an era where cyber threats loom large, healthcare organizations must prioritize their cybersecurity oversight strategies to safeguard their operations and reputation. Organizations should set clear goals for their managed services strategy, focusing on critical areas such as system uptime, security posture, and reducing operational costs. These objectives should align with overarching business goals and be articulated in measurable terms. For instance, entities may focus on a 99.9% uptime rate or strive for a 30% decrease in incident response durations. This focus is vital, especially as existing standards for incident response times in 2026 are anticipated to show considerable enhancements due to progress in supervised solutions.
Rapid incident response strategies are crucial; having a specialized team ready to act within 24 hours can drastically reduce the damage during a cybersecurity incident, as demonstrated by a healthcare provider's experience with ransomware. Furthermore, success indicators should encompass customer satisfaction ratings, cost reductions, and compliance adherence levels, allowing organizations to evaluate the efficiency of their administered offerings. Frequent evaluations of these metrics promote ongoing enhancement and ensure that the managed services strategy adapts to changing organizational requirements.
Industry analysts stress that quantifiable success metrics are essential for showcasing the worth of overseen offerings, as they deliver a clear structure for assessing performance and aligning IT initiatives with business results. Moreover, establishing round-the-clock network surveillance and alert systems can proactively identify anomalies and possible vulnerabilities, ensuring that entities are well-prepared to react to threats before they escalate. By implementing these strategies, organizations not only protect themselves but also enhance their overall operational resilience against future threats.

In an era where cyber threats loom large, the choice of a managed service provider (MSP) can make or break an organization's cybersecurity posture. Choosing the right MSP is vital for organizations looking to enhance their IT capabilities and ensure robust cybersecurity. Key factors to consider include the provider's experience, offerings, and industry-specific expertise. Organizations should evaluate the MSP's history of delivering similar services and their capacity to scale with business growth. A strong emphasis on cybersecurity and compliance is essential; providers must demonstrate effective measures to protect sensitive data against evolving threats.
By 2026, successful MSPs will leverage automation, AI, and predictive capabilities to enhance their service delivery. This shift underscores the importance of selecting an MSP that not only meets immediate needs but also aligns with long-term strategic goals. For instance, Cyber Solutions offers 24/7 network monitoring and alert options that identify various anomalies, such as unusual traffic patterns and unauthorized access attempts, providing instant notifications and real-time insights to prevent downtime or breaches. Reviewing client testimonials and case studies can provide valuable insights into the provider's reliability and performance, showcasing successful partnerships that have led to improved operational outcomes.
Building a strong partnership with your MSP is crucial for long-term success. Regular communication and alignment on business goals foster a collaboration that can adapt to evolving needs and challenges, ultimately driving innovation and efficiency within the organization.

In an era where cybersecurity threats loom large, healthcare organizations must prioritize robust solutions to safeguard sensitive data. To achieve this, a comprehensive project plan outlining essential milestones, timelines, and responsibilities is crucial.
It's vital to involve stakeholders throughout the implementation process to secure their support and tackle any concerns head-on. Establishing clear communication channels with the support provider can significantly boost collaboration and facilitate valuable feedback.
Training internal staff on new procedures and tools is crucial for maximizing the benefits of these solutions and ensuring compliance with regulatory standards. Additionally, organizations should conduct regular check-ins and evaluations during implementation to quickly identify and address any issues, ensuring a smooth transition to the new supervised model.
Integrating Compliance as a Service (CaaS) can significantly bolster this process, offering essential expertise and support for audit preparation and ongoing monitoring - critical for organizations in highly regulated sectors.

In an era where cybersecurity threats are increasingly sophisticated, organizations must prioritize the continuous monitoring of their cybersecurity solutions. This means keeping an eye on key performance indicators (KPIs) for network security and regularly assessing how well the solutions are working. Open conversations with your provider, like Cyber Solutions, are essential for addressing challenges and identifying opportunities for improvement. With Cyber Solutions' 24/7 network oversight and alert capabilities, organizations can detect anomalies and potential vulnerabilities in real-time, enabling prompt action to prevent downtime or breaches.
Moreover, organizations must also be proactive in adjusting their strategies to keep up with changing business needs, technology advancements, and regulatory requirements. By fostering a culture of continuous improvement and leveraging comprehensive firewall and network security solutions, organizations can ensure that their managed services strategy remains effective, efficient, and aligned with their strategic goals. By embracing a proactive approach, organizations can safeguard their assets and ensure resilience against ever-evolving threats.

In an era where cyber threats loom larger than ever, healthcare organizations must prioritize cybersecurity to protect sensitive patient data and maintain operational integrity. Embracing a managed services strategy is crucial for organizations aiming to bolster their IT operations and enhance cybersecurity resilience. By outsourcing IT management to a Managed Service Provider (MSP), organizations can focus on their core functions while gaining expert support to navigate the complexities of cybersecurity threats. This strategic shift not only mitigates risks but also positions organizations for sustained growth in a competitive landscape.
Throughout the article, we've highlighted key practices for implementing an effective managed services strategy. These include:
Each of these elements plays a vital role in ensuring that the managed services approach aligns with business goals and adapts to evolving technological challenges. By focusing on measurable success metrics and fostering strong partnerships with MSPs, organizations can enhance operational efficiency and resilience against potential threats.
Ultimately, by embracing a proactive managed services strategy, organizations not only shield their assets but also position themselves as leaders in a rapidly changing digital landscape. As cybersecurity challenges continue to escalate, proactive measures and continuous improvement become essential for safeguarding sensitive data and maintaining customer trust.
What are managed services in the context of IT strategy?
Managed services refer to outsourcing IT operations to a Managed Service Provider (MSP), allowing organizations to focus on their core activities while benefiting from the MSP's expertise in monitoring, maintenance, and support.
How do managed services benefit healthcare organizations?
Managed services enhance operational efficiency, provide scalability, ensure compliance with industry regulations, reduce downtime, and improve incident response times, which are crucial for maintaining productivity and customer trust.
What features are included in managed services?
Key features of managed services include pro-active monitoring, data backup solutions, and vendor management.
Why is it important to assess organizational needs for managed services?
Assessing organizational needs helps identify existing pain points, such as cybersecurity vulnerabilities and compliance challenges, ensuring that the managed services strategy aligns with specific needs and expectations.
What factors should organizations evaluate when assessing their IT environment?
Organizations should evaluate their current IT infrastructure, including hardware, software, and personnel capabilities, to clarify the support needed for effective managed services.
What risks do organizations face without a comprehensive assessment of their IT environment?
Without a comprehensive assessment, organizations may struggle to identify cybersecurity vulnerabilities, risking exposure to significant threats that could undermine their operational integrity and trust.
How can a managed services strategy align with organizational goals?
Aligning a managed services strategy with organizational goals ensures that companies invest in solutions that deliver maximum value and promote sustainable growth, enhancing operational efficiency and resilience against digital threats.
What is the significance of embracing managed solutions for organizations?
Embracing managed solutions enhances operational resilience and positions organizations for growth and competitiveness in an increasingly challenging landscape, while also securing their future against evolving threats.