
In an era where cyber threats are more prevalent than ever, the security of an organization hinges on one essential practice: monthly vulnerability scanning. These assessments act not just as a protective barrier against potential breaches but also as a proactive strategy to strengthen the overall cybersecurity posture. Yet, despite the evident advantages, many organizations still neglect the importance of regular evaluations.
What could be the repercussions of this oversight?
How can adopting a routine scanning schedule revolutionize an organization’s defense against the ever-evolving landscape of cyber threats?
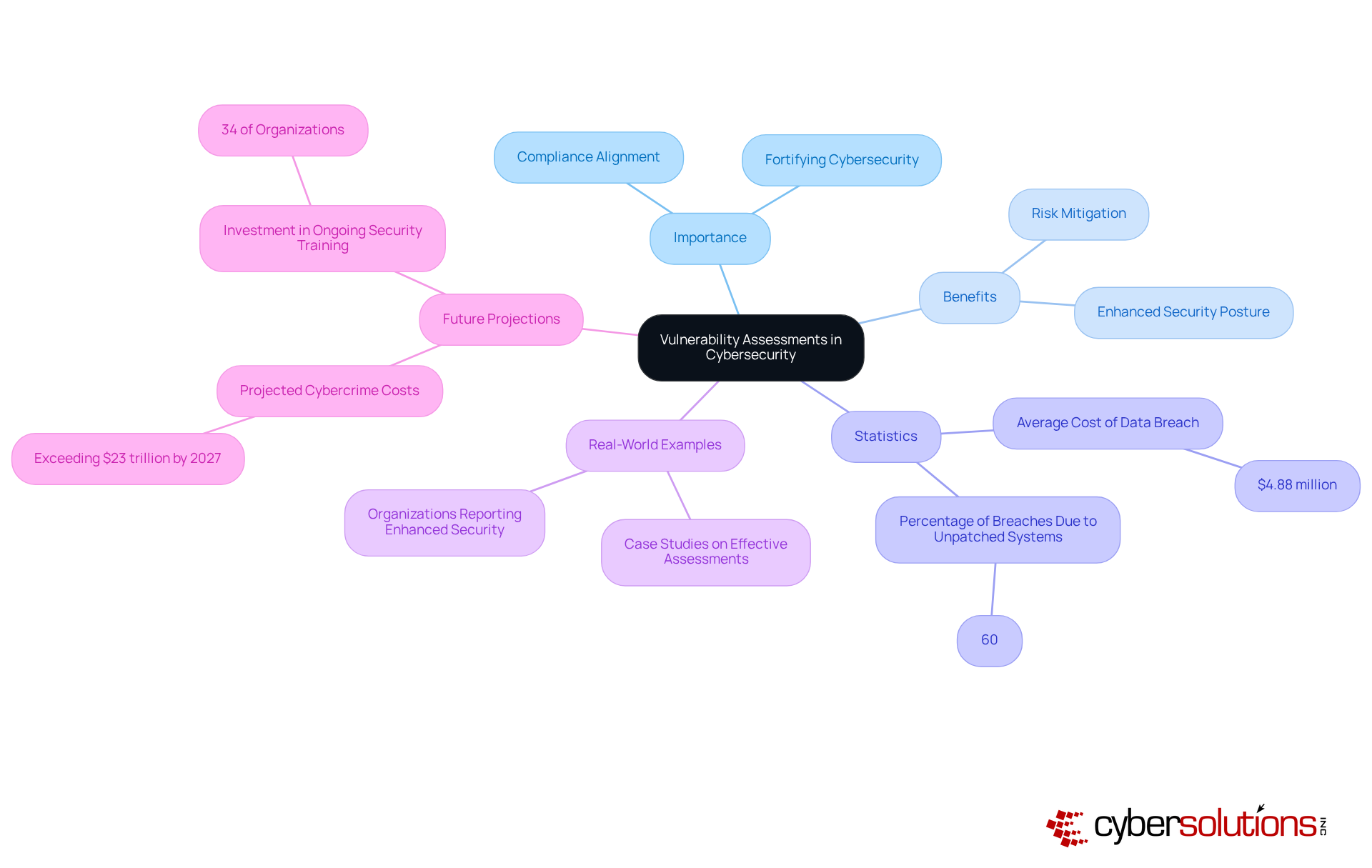
are not just a routine check; they are essential for any organization aiming to improve security. In 2026, these evaluations have become crucial, providing a clear view of a company’s security posture and the threats it faces. By pinpointing weaknesses, organizations can prioritize their remediation efforts, ensuring that the most critical vulnerabilities are addressed first. This proactive approach not only mitigates risks but also aligns with industry standards, making it a cornerstone of a robust cybersecurity strategy.
Regular threat evaluations indicate that security is a vital precaution, enabling organizations to stay ahead of potential dangers and maintain a secure environment. For instance, companies that conduct the assessments save money, which was approximately $4.88 million in 2024. Moreover, 60% of data breaches stem from the failure to apply available patches, underscoring the importance of timely updates. This connection highlights the anticipated surge in cybercrime costs, projected to exceed $23 trillion by 2027, emphasizing the financial repercussions of neglecting routine evaluations.
Real-world examples illustrate the effectiveness of regular assessments. Organizations that have implemented regular assessments report enhanced security postures and improved compliance. In fact, 85% of cybersecurity professionals link the increase in cyberattacks to evolving threats, reinforcing the necessity for continuous vigilance. As one expert noted, "Assessments provide the documented evidence of that auditors require."
Despite these clear advantages, a significant number of companies still neglect to implement practices necessary for regular evaluations. In 2026, it is estimated that only 34% of organizations will invest in ongoing security education, a statistic that underscores the urgent need for firms to prioritize risk evaluations and training to effectively mitigate threats. As the threat landscape evolves, embracing risk evaluations as a strategic imperative will be vital for organizations looking to protect their data, clients, and reputation.
In today's healthcare landscape, robust cybersecurity is not just an option; it's a necessity. To maintain strong cybersecurity defenses, it is essential that organizations conduct regular vulnerability scans. They allow for the early identification of vulnerabilities, enabling companies to tackle issues before cybercriminals can exploit them. This proactive approach is vital in an era where data breaches are increasingly common. Did you know that 60% of data breaches arise from unpatched vulnerabilities?
To protect sensitive information and maintain compliance, organizations must prioritize regular assessments. By conducting these evaluations, organizations reinforce the principle that security is a continuous process, creating a continuous feedback loop that strengthens their security posture and guides strategic decisions regarding cybersecurity investments. This ongoing vigilance not only minimizes the risk of data breaches but also helps prevent the substantial financial losses, which can exceed $10 million in the healthcare sector alone.
As trends indicate, organizations that prioritize routine security assessments are better equipped to navigate the complexities of compliance and safety in today's digital environment. Are you ready to enhance your cybersecurity measures and safeguard your organization against potential threats?

Rare vulnerabilities pose significant risks to businesses. To avoid extended periods during which new vulnerabilities can go unnoticed, systems should be scanned monthly rather than only quarterly or annually. This delay can lead to severe consequences, including data breaches, financial loss, and damage to a company's reputation. Additionally, regulatory bodies may impose fines for failing to comply with mandated scanning frequencies, further amplifying the financial burden. Given the rapidly evolving nature of cyber threats, vulnerabilities can emerge quickly, and without regular evaluations, companies may find themselves exposed to attacks that could have been prevented.
It is essential that systems should be scanned monthly, particularly for small and medium-sized businesses (SMBs) that can greatly benefit from enhanced security measures. CaaS provides comprehensive solutions that include continuous monitoring, proactive evaluations, and policy development, ensuring that your systems remain compliant with current regulatory requirements. This proactive approach not only protects your organization from potential penalties but also enhances your overall security posture. Therefore, the risks associated with infrequent scanning underscore the importance of integrating CaaS solutions, such as network monitoring and alerts, to effectively safeguard against vulnerabilities.

In today's digital landscape, organizations aiming to safeguard their assets must recognize that systems should be scanned as part of their security strategy. It is crucial to establish a clear scanning schedule since systems should be regularly assessed. This should include both authenticated and unauthenticated scans, providing a comprehensive view of the security posture. Automation significantly enhances efficiency and precision, enabling quicker detection of vulnerabilities that could be exploited.
Prioritizing vulnerabilities based on severity and potential impact ensures that critical issues are addressed promptly, minimizing the risk of exploitation. Regular reviews and updates of scanning methodologies are essential, as the threat landscape is constantly evolving. Moreover, integrating scanning results into the overall security framework allows organizations to leverage insights for informed budgeting and resource allocation in cybersecurity initiatives.
By adopting these practices, organizations can not only strengthen their defenses but also maintain a proactive stance against threats. Are you ready to fortify your cybersecurity measures and protect your organization from potential risks?

Regular vulnerability assessments are not just important; they are essential for maintaining a robust cybersecurity posture. Organizations that prioritize monthly scans can proactively identify and address potential weaknesses before cybercriminals have a chance to exploit them. This proactive approach not only protects sensitive information but also ensures compliance with industry standards, ultimately strengthening the overall security framework.
Consider the staggering costs associated with data breaches - many of which stem from unpatched vulnerabilities. By integrating continuous monitoring and proactive evaluations into their cybersecurity strategies, organizations can significantly reduce their risk exposure and enhance their incident response capabilities. Are you prepared to face the financial and reputational consequences of a breach?
In today’s evolving threat landscape, where cyberattacks are becoming increasingly sophisticated, adopting a proactive stance on cybersecurity is imperative. Implementing monthly vulnerability scans is not merely a recommendation; it is a strategic necessity that safeguards an organization’s data, reputation, and financial stability. Organizations must act decisively now to ensure they are equipped to tackle the challenges of tomorrow’s cyber environment.
What are vulnerability assessments and why are they important for organizations?
Vulnerability assessments are evaluations that identify weaknesses in an organization's cybersecurity. They are essential for fortifying cybersecurity, providing a clear view of a company’s security posture and the threats it faces.
How often should organizations conduct vulnerability evaluations?
Organizations should conduct vulnerability evaluations monthly as a vital precaution to stay ahead of potential dangers and maintain a secure environment.
What are the financial implications of neglecting vulnerability assessments?
Neglecting vulnerability assessments can lead to significant financial repercussions, including an average cost of a data breach, which was approximately $4.88 million in 2024. Additionally, 60% of data breaches result from failing to apply available patches.
What is the projected cost of cybercrime by 2027?
The projected cost of cybercrime is expected to exceed $23 trillion by 2027, emphasizing the importance of routine evaluations to mitigate risks.
How do regular vulnerability assessments impact an organization's security posture?
Organizations that implement regular vulnerability assessments report enhanced security postures and improved incident response capabilities, which are crucial for managing evolving threats.
What percentage of cybersecurity professionals link the increase in cyberattacks to evolving threats?
85% of cybersecurity professionals link the increase in cyberattacks to evolving threats, reinforcing the necessity for continuous vigilance through regular assessments.
What is the estimated investment in ongoing security education by organizations in 2026?
It is estimated that only 34% of organizations will invest in ongoing security education in 2026, highlighting the urgent need for firms to prioritize risk evaluations and training.
What role do vulnerability assessments play in compliance requirements?
Vulnerability assessments align with compliance requirements, making them a cornerstone of a robust cybersecurity strategy and demonstrating proactive management to auditors.