
Managed services hosting has become a crucial strategy for C-suite leaders aiming to enhance operational efficiency and strengthen cybersecurity in today’s intricate digital landscape. As cyber threats grow more sophisticated, organizations must adapt. By partnering with specialized providers, they can streamline IT management, allowing internal teams to focus on core business functions while enjoying advanced security measures and predictable costs.
However, as compliance regulations tighten and cyber threats evolve, executives face a pressing question: how can they ensure that their chosen managed services not only meet current needs but also future-proof their operations? This is where strategic foresight becomes essential.
In an era where the stakes are high, the right managed services can be a game-changer. They not only safeguard sensitive data but also empower organizations to thrive amidst uncertainty. As you consider your options, reflect on how these services can not only address immediate challenges but also position your organization for long-term success.
Managed services are crucial for enhancing operational efficiency, especially in the area of IT management. With the rise of digital transformation, it’s imperative for entities to delegate routine IT responsibilities to specialized experts. This strategic move allows internal teams to focus on core business functions, free from the distractions of daily IT management.
Consider a healthcare entity partnering with a managed solutions firm like Cyber Solutions. Such collaboration can lead to ongoing monitoring and maintenance of IT systems, significantly reducing downtime and improving service delivery. Cyber Solutions provides a comprehensive suite of features, including:
These services are essential for small to medium businesses aiming to enhance their operational capabilities.
Moreover, managed services hosting enables organizations to leverage advanced technologies and automation to streamline processes, resulting in faster response times and heightened productivity. By embracing these offerings, C-suite leaders can ensure their organizations operate at peak efficiency, fostering growth and innovation.
A compelling case study illustrates this point: after a ransomware attack, a healthcare organization received immediate training on recognizing suspicious emails and maintaining proper cybersecurity hygiene. This efficient response and remediation process allowed critical healthcare operations to continue with minimal downtime. Such experiences underscore the importance of cybersecurity training and a Zero Trust approach, highlighting the value of partnerships with firms like Cyber Solutions.
According to projections, the U.S. services market is expected to reach $69.55 billion by 2025, underscoring the growing significance of MSPs in today’s business environment. As industry expert Matt Rosenthal emphasizes, the right managed IT provider can align technology with business goals, eliminate inefficiencies, and future-proof operations. This reinforces the value of these partnerships in navigating the complexities of cybersecurity.

In today’s digital landscape, the threat of cyberattacks looms large, making robust cybersecurity measures essential for organizations. Managed services hosting offers a comprehensive framework to bolster cybersecurity posture. By partnering with a managed security service provider like Cyber Solutions, organizations gain access to advanced security tools, continuous monitoring, and expert capabilities.
For instance, those utilizing supervised security solutions benefit from:
This significantly mitigates the impact of cyber threats. In fact, compared to those without such support, organizations with MSSPs experience fewer breaches.
Furthermore, MSSPs conduct regular assessments and audits. This proactive approach not only enhances security but also builds trust among stakeholders, positioning organizations favorably for C-suite leaders. Notably, 40% of executives express a desire for predictive capabilities to foresee and prevent attacks, underscoring the importance of continuous surveillance in the services provided.
As organizations navigate an increasingly intricate threat landscape, collaborating with an MSSP becomes crucial for maintaining strong cybersecurity defenses.

C-suite executives are increasingly drawn to solutions, primarily because of the benefits they offer. With Cyber Solutions' services, organizations can effectively budget their IT expenses, minimizing the risk of unexpected costs that could disrupt financial planning. This pricing structure encompasses everything from email licenses to advanced cybersecurity, ensuring no surprise expenses arise.
For instance, consider a mid-sized retail firm that experienced significant savings after transitioning to a cloud-based solution. This case illustrates how outsourced options can lead to cost reductions. Moreover, the return on investment (ROI) from managed services is often realized through substantial savings, increased productivity, and improved operational efficiency. Studies show that entities utilizing managed solutions can achieve a decrease in IT expenses between 20% and 30%, alongside a boost in efficiency by 15% to 25%.
Additionally, proactive management can result in an impressive 85% reduction in unplanned downtime, further underscoring the financial advantages of this approach. By investing in managed services from Cyber Solutions, organizations can ensure their companies save money while also achieving a greater return on their IT investments.

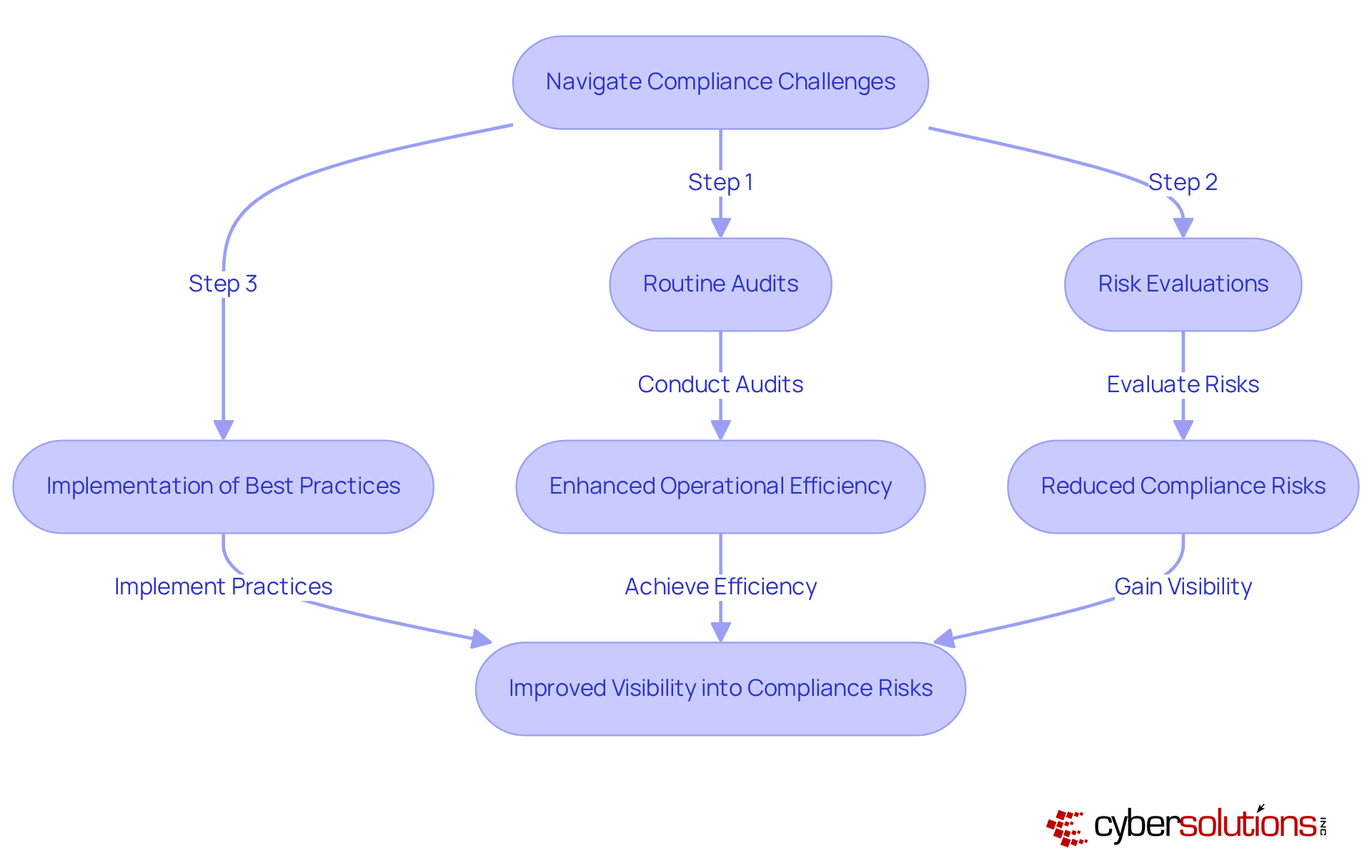
Navigating compliance is crucial for C-suite leaders, especially in highly regulated sectors like healthcare and finance. With the increasing complexity of regulations, how can organizations ensure they effectively maintain compliance? Managed services hosting emerges as a strategic solution, providing businesses with the expertise and resources necessary to maintain compliance.
By partnering with a managed solutions provider (MSP), organizations can leverage specialized knowledge. This approach encompasses:
Not only does this collaboration relieve internal teams of the compliance burden, but it also enhances overall efficiency.
Focusing on core business activities allows companies to significantly reduce the risk of incurring penalties associated with non-compliance. In fact, organizations utilizing CaaS report improved visibility into compliance risks and quicker identification of issues. This makes managed services hosting an essential component of a robust compliance strategy, ensuring that businesses can thrive in a challenging regulatory landscape.
Managed services hosting stands as a crucial strategy for C-suite leaders intent on boosting operational efficiency and fortifying cybersecurity within their organizations. By outsourcing IT responsibilities to specialized providers, executives can concentrate on core business functions, all while ensuring their companies remain resilient against the ever-evolving landscape of cyber threats.
The advantages of managed services hosting are compelling:
Case studies reveal tangible benefits, such as significant cost reductions and increased productivity, underscoring the value of partnering with firms like Cyber Solutions. Moreover, navigating compliance challenges becomes more manageable, as organizations can leverage expert resources to maintain adherence to complex regulations.
Ultimately, embracing managed services hosting transcends a mere tactical decision; it emerges as a strategic imperative for organizations striving to thrive in a competitive environment. C-suite leaders are urged to evaluate how these solutions can transform their operations, safeguard sensitive data, and drive long-term growth. The future of business success hinges on leveraging the expertise of managed services to navigate complexities and seize new opportunities.
What are managed services hosting solutions?
Managed services hosting solutions involve delegating routine IT responsibilities to specialized experts, enhancing operational efficiency, particularly in cybersecurity for organizations like healthcare entities.
How do managed services hosting solutions benefit healthcare organizations?
They allow healthcare organizations to focus on core business functions by offloading daily IT management tasks, leading to reduced downtime and improved service delivery.
What services does Cyber Solutions offer as part of managed services hosting?
Cyber Solutions provides a comprehensive suite of features, including 24/7 IT support, proactive monitoring, data backup solutions, patch management, endpoint protection, and network optimization.
Why are managed services important for small to medium businesses?
Managed services are essential for maximizing ROI in a competitive landscape, enabling businesses to leverage advanced technologies and automation for streamlined processes and increased productivity.
How can managed services hosting improve response times and productivity?
Managed Service Providers (MSPs) utilize advanced technologies and automation to streamline processes, resulting in faster response times and heightened productivity.
Can you provide an example of the effectiveness of managed services in a real-world scenario?
After a ransomware attack, a healthcare organization received immediate training on recognizing suspicious emails, which allowed them to maintain operations with minimal downtime, highlighting the importance of proactive cybersecurity strategies.
What is the projected growth of the U.S. services market by 2025?
The U.S. services market is projected to reach $69.55 billion by 2025, indicating the increasing significance of Managed Service Providers (MSPs) in the business environment.
What does industry expert Matt Rosenthal say about managed IT providers?
Matt Rosenthal emphasizes that the right managed IT provider can align technology with business goals, eliminate inefficiencies, and future-proof operations, underscoring the value of these partnerships in cybersecurity.