Introduction
The Cybersecurity Maturity Model Certification (CMMC) stands as a pivotal framework aimed at enhancing the cybersecurity posture of organizations within the Defense Industrial Base. For C-Suite leaders, grasping the complexities of CMMC implementation transcends mere regulatory compliance; it emerges as a strategic necessity that not only protects their organizations from cyber threats but also fortifies their competitive edge. As the cybersecurity landscape continues to evolve, executives must ask themselves: how can they ensure their organizations not only meet compliance standards but also harness CMMC as a springboard for operational excellence?
Understanding the current landscape of cybersecurity threats is essential. Organizations face an array of challenges, from sophisticated cyber attacks to evolving regulatory requirements. The implications for healthcare organizations, in particular, are profound. Cybersecurity is not just a technical issue; it’s a critical component of operational integrity and trust. By addressing these challenges head-on, organizations can position themselves not only to comply with CMMC but to thrive in an increasingly competitive environment.
Understand CMMC: Purpose and Importance
The Cybersecurity Readiness Model Certification is not just a framework; it’s a vital strategy crafted by the Department of Defense (DoD) to bolster the defense posture of organizations within the Defense Industrial Base (DIB). This framework mandates that contractors undertake measures to protect Controlled Unclassified Information (CUI) and Federal Contract Information (FCI). For contractors, grasping the significance of CMMC is essential for several compelling reasons:
- Regulatory Adherence: Compliance is a critical obligation for all DoD contractors. It’s not merely about meeting requirements; it’s about securing contracts and maintaining eligibility in a fiercely competitive landscape. Contractors are also required to submit annual affirmations regarding their information security policies, reinforcing their commitment to compliance with standards like NIST SP 800-171.
- Risk Mitigation: Adhering to cybersecurity standards dramatically reduces the risk of data breaches and cyberattacks, which can inflict significant financial damage and tarnish reputations. Organizations that embrace the framework’s practices report a notable decline in security incidents, underscoring its effectiveness. Moreover, incorporating application allowlisting into your security strategy can proactively block unauthorized software, further minimizing vulnerabilities and protecting against malware and ransomware. Ignoring cybersecurity post-breach could lead to severe repercussions, including legal risks under the False Claims Act (FCA), especially if compliance is not prioritized.
- Competitive Edge: The certification distinguishes your organization in the marketplace, showcasing a commitment to cybersecurity that can attract new business opportunities. With nearly 80,000 firms requiring compliance, adherence can set your business apart from competitors. The framework 2.0 simplifies the requirements into three tiers, making it easier for organizations to plan and maintain compliance.
- Operational Efficiency: The implementation of the cybersecurity maturity model requirements not only fortifies security but also streamlines processes, enhancing overall IT efficiency. Organizations that have adopted the certification have experienced operational improvements alongside their strengthened security posture. Partnering with skilled external IT platform providers can bolster adherence initiatives and ensure that entities effectively support compliance to meet cybersecurity maturity model certification standards. Additionally, integrating application allowlisting into your cybersecurity framework can boost operational efficiency by permitting only approved applications to run, thereby reducing the attack surface.
In summary, this framework transcends mere compliance; it represents a strategic initiative that can fortify your organization’s security architecture and positively influence its financial health.

Identify CMMC Requirements by Level
Understanding the CMMC framework is crucial for organizations, especially in today’s landscape where cybersecurity threats are increasingly sophisticated. CMMC comprises three distinct levels, each with specific requirements that organizations must fulfill to achieve certification.
- Level 1 (Foundational): This level emphasizes fundamental security hygiene practices. Organizations are required to implement 17 essential security controls, including access control and incident response. Compliance at this level necessitates an annual self-assessment, with results posted in the Supplier Performance Risk System (SPRS). This foundational step is vital for establishing a secure environment.
- Level 2 (Advanced): Organizations must align with CMMC requirements, which encompass 110 security controls. Compliance involves conducting a self-assessment and developing a comprehensive System Security Plan (SSP). Notably, firms in the defense industry have effectively fulfilled these requirements, showcasing the practicality of attaining certification. This level not only enhances security but also builds trust with stakeholders.
- Level 3 (Expert): This level imposes more rigorous requirements, including advanced security practices and regular third-party assessments. Organizations must demonstrate a robust cybersecurity program and engage in continuous monitoring. Certification at this level is conducted by the CMMC Accreditation Body every three years, ensuring adherence to the highest standards. Achieving this level signifies a commitment to excellence in cybersecurity.
Grasping these particular requirements enables organizations to evaluate their organization’s existing compliance status and determine the essential actions needed for them to obtain certification at the various levels. By prioritizing cybersecurity, organizations can not only protect their assets but also enhance their reputation in the industry.

Prepare for CMMC Certification: Steps to Take
To effectively prepare for CMMC certification, C-Suite leaders must take decisive action. Cybersecurity is not just a regulatory requirement; it’s a critical component of organizational integrity and trust. Here are steps to ensure your organization is ready:
- Conduct a gap analysis: Evaluate your current security posture against the relevant standards to pinpoint areas that require enhancement. This examination is crucial, as entities that fail to recognize regulatory gaps may face serious repercussions, especially in the event of a data breach.
- Develop a security plan: Create a comprehensive document that outlines your organization’s security practices and their alignment with CMMC standards. A successful security plan serves as a roadmap for compliance and operational security, guiding your organization toward its goals.
- Implement Required Controls: Based on the findings from the gap analysis, establish necessary security measures to meet the standards of your desired level. This proactive approach not only enhances security but also prepares your organization for future evaluations.
- Conduct a self-assessment: Perform an internal evaluation of your organization’s adherence to CMMC standards. This self-assessment helps identify any remaining deficiencies and ensures readiness for the official assessment in the context of certification.
- Engage a C3PAO: For Levels 2 and 3, collaborating with a certified third-party assessment organization is essential for conducting an official evaluation. Partnering with a reputable C3PAO significantly increases the likelihood of successful certification.
- Prepare Documentation: Ensure that all relevant documentation, including policies and procedures, is current and easily accessible for review. Well-structured documentation is vital during the evaluation process and demonstrates a commitment to compliance.
- Train Employees: Implement training programs to ensure that all employees understand their roles in upholding regulations. A knowledgeable workforce is crucial for maintaining security practices and fostering a culture of adherence.
By diligently following these steps, C-Suite executives can position their organizations for successful certification, which will strengthen their security posture and ensure compliance with Department of Defense requirements.

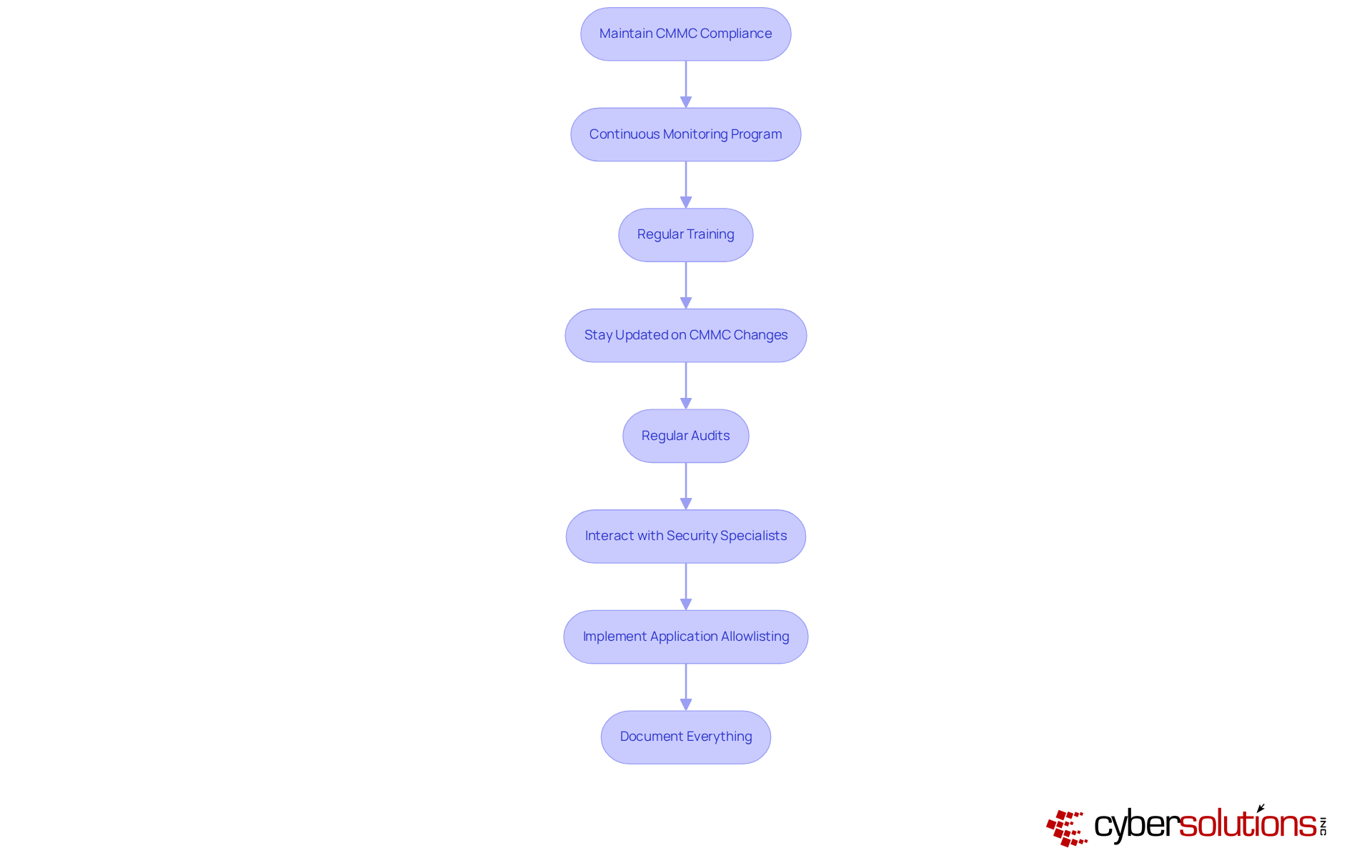
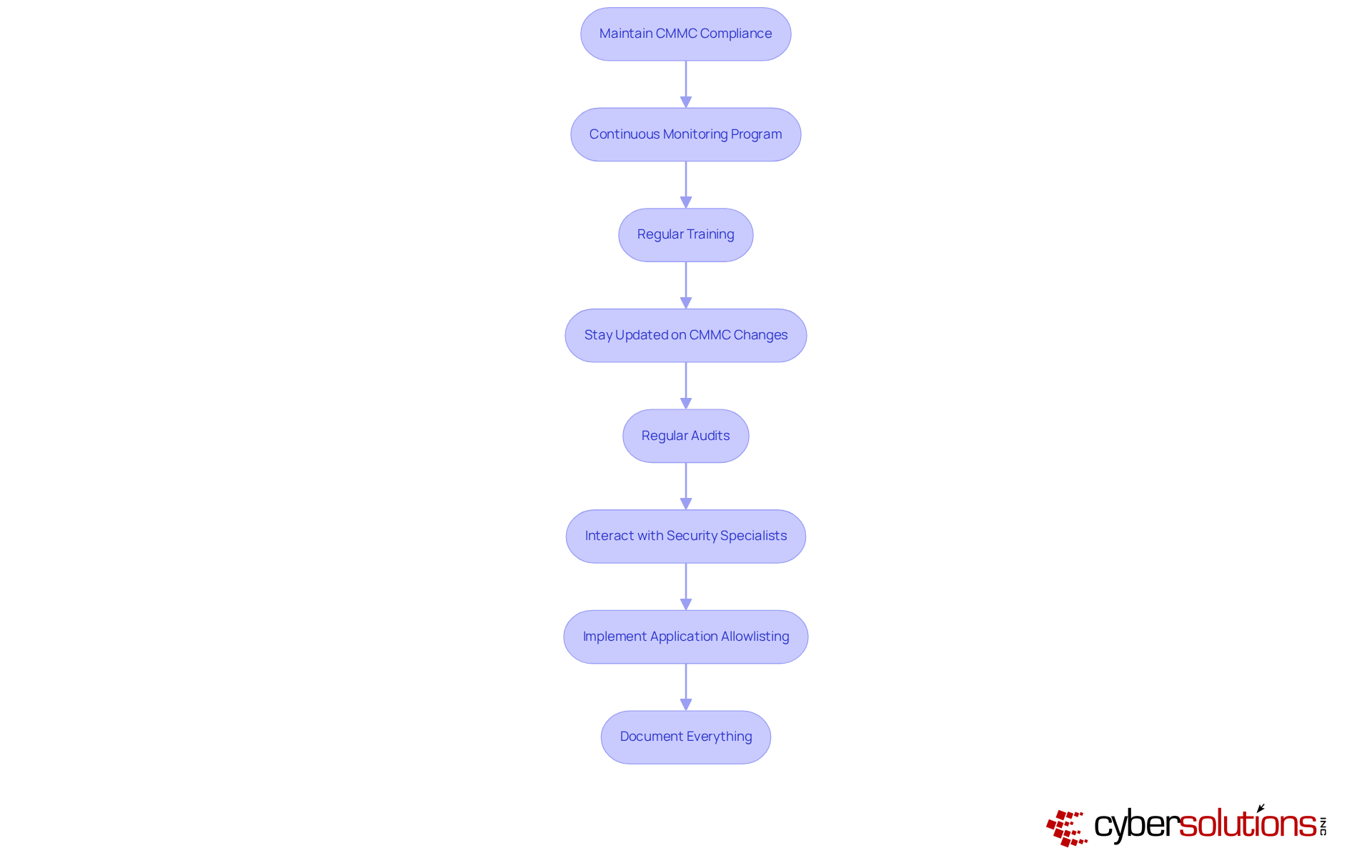
Maintain Compliance: Strategies for Ongoing Success
To maintain compliance, C-Suite leaders must implement the following strategies:
- Establish a routine: Regularly assess your information security practices and controls to ensure they remain effective and compliant with CMMC requirements. Ongoing oversight is crucial, enabling entities to adapt to evolving threats and regulatory developments, thereby ensuring continuous adherence.
- Provide training: Provide ongoing training for employees to keep them informed about cybersecurity best practices and regulatory requirements. Effective training programs not only enhance awareness but also empower employees to recognize and respond to potential threats, significantly reducing the risk of non-compliance.
- Stay informed: Keep abreast of any updates or changes to regulations to ensure your organization remains compliant. With regulatory mandates evolving, proactive engagement with the latest guidelines is essential for maintaining eligibility for Department of Defense contracts.
- Conduct audits: Arrange routine audits to evaluate adherence and pinpoint areas for enhancement. These evaluations assist companies in measuring their preparedness for CMMC assessments and guarantee that all necessary documents are organized, as contractors must retain these records for a minimum of six years.
- Collaborate with experts: Collaborate with security professionals to enhance your organization’s protective stance and adherence initiatives. Partnering with knowledgeable managed service providers, such as Cyber Solutions, can offer valuable insights and resources, facilitating a smoother regulatory journey. Their comprehensive approach, which includes endpoint isolation, malware elimination, and user education, promotes a quicker and more thorough recovery from incidents, fostering a robust collaboration that enhances overall security.
- Implement controls: Adopt security controls as a proactive measure to prevent unauthorized or malicious applications from executing on your systems. This strategy reduces the attack surface and aids in fulfilling requirements for standards such as HIPAA, PCI-DSS, and GDPR. By ensuring that only authorized applications can operate, companies can significantly bolster their security posture and protect against malware and ransomware.
- Maintain documentation: Maintain thorough records of regulatory efforts, including training sessions, audits, and evaluations, to demonstrate continuous adherence to the standards. Comprehensive documentation is essential, serving as proof of compliance during audits and evaluations, thereby reinforcing your entity’s commitment to cybersecurity.
By executing these strategies, C-Suite leaders can ensure their organizations achieve certification through CMMC implementation while also upholding compliance in the long run, safeguarding their operations from potential cyber threats. Given that only 1% of contractors are fully prepared for compliance audits, the urgency of these strategies cannot be overstated. As Jacob Horne, chief cybersecurity evangelist at Summit 7, emphasizes, "CMMC isn’t really an end state. It feels like an end state, but it’s really operational capabilities that matter."
Conclusion
Mastering CMMC implementation is not merely a regulatory obligation; it stands as a strategic imperative that can significantly bolster an organization's cybersecurity posture and operational efficiency. For C-Suite leaders, grasping the multifaceted benefits of CMMC - from ensuring compliance and mitigating risks to gaining a competitive edge - forms the bedrock of a robust cybersecurity strategy. Recognizing the importance of CMMC is crucial for securing contracts and maintaining trust within the Defense Industrial Base.
This article outlines critical steps for successful CMMC implementation, including:
- Conducting a gap analysis
- Developing a System Security Plan
- Engaging third-party assessors
Each of these actions is meticulously designed to fortify an organization’s defenses against cyber threats while ensuring adherence to stringent compliance standards. Moreover, maintaining ongoing compliance through continuous monitoring, regular training, and thorough documentation is vital for long-term success in an ever-evolving cybersecurity landscape.
Ultimately, the journey toward CMMC compliance is an ongoing commitment to excellence in cybersecurity. C-Suite leaders must understand that achieving certification is just the beginning; fostering a culture of security awareness and proactive engagement with compliance strategies will not only protect organizational assets but also enhance reputation and trust within the industry. Taking decisive action now will position organizations to thrive in a competitive marketplace while safeguarding against the increasing threat of cyberattacks.
Frequently Asked Questions
What is the purpose of the Cybersecurity Maturity Model Certification (CMMC)?
The CMMC is a strategic framework developed by the Department of Defense (DoD) to enhance the cybersecurity posture of organizations within the Defense Industrial Base (DIB) by mandating the implementation of robust cybersecurity measures to protect Controlled Unclassified Information (CUI) and Federal Contract Information (FCI).
Why is CMMC compliance important for DoD contractors?
Compliance with CMMC is crucial for all DoD contractors as it is a regulatory obligation that secures contracts and maintains eligibility in a competitive landscape. Contractors must also submit annual affirmations regarding their information security policies to demonstrate their commitment to compliance with standards like HIPAA, PCI-DSS, and GDPR.
How does CMMC implementation help in risk mitigation?
Adhering to CMMC standards significantly reduces the risk of data breaches and cyberattacks, which can lead to financial damage and reputational harm. Organizations that adopt the framework report a decline in security incidents, and incorporating practices like application allowlisting can further minimize vulnerabilities and protect against malware and ransomware.
What competitive advantages does CMMC certification provide?
Achieving CMMC certification distinguishes an organization in the marketplace by showcasing a commitment to cybersecurity, potentially attracting new business opportunities. With nearly 80,000 firms requiring Level 2 certification, compliance can set a business apart from its competitors.
How does CMMC implementation enhance operational efficiency?
CMMC implementation not only strengthens security but also streamlines processes, leading to improved overall IT efficiency. Organizations that adopt the certification often experience operational improvements, and integrating application allowlisting can reduce the attack surface by permitting only approved applications to run.
What are the consequences of ignoring CMMC standards after a breach?
Ignoring CMMC standards post-breach can lead to severe repercussions, including legal risks under the False Claims Act (FCA), especially if CMMC implementation is not prioritized.
List of Sources
- Understand CMMC: Purpose and Importance
- Lori Crooks (https://c-suitenetwork.com/steering-through-cmmc-compliance-a-critical-path-for-defense-contractors)
- CMMC compliance reckoning for defense contractors arrives | Federal News Network (https://federalnewsnetwork.com/commentary/2025/12/cmmc-compliance-reckoning-for-defense-contractors-arrives)
- US Finalizes CMMC Rule: Cybersecurity Verification Now Determines Contract Eligibility for Defense Contractors (https://corporatecomplianceinsights.com/us-finalizes-cmmc-rule-cybersecurity-verification-defense-contractors)
- Pentagon begins enforcing CMMC compliance, but readiness gaps remain (https://defensescoop.com/2025/11/10/cmmc-compliance-dod-enforcement-defense-industry-readiness-gaps)
- Report finds large gap in CMMC readiness among defense industrial base (https://defensescoop.com/2025/01/28/redspin-report-cmmc-readiness-gap-2025-defense-industrial-base)
- Identify CMMC Requirements by Level
- CMMC Regulations: Key Questions and Answers for Defense Contractors | Insights | Holland & Knight (https://hklaw.com/en/insights/publications/2025/11/cmmc-regulations-key-questions-and-answers-for-defense-contractors)
- What You Need to Know Heading Into 2026 | Fortra (https://fortra.com/blog/cmmc-compliance-what-you-need-know-heading-2026)
- Pentagon begins enforcing CMMC compliance, but readiness gaps remain (https://defensescoop.com/2025/11/10/cmmc-compliance-dod-enforcement-defense-industry-readiness-gaps)
- accorian.com (https://accorian.com/cmmc-2-0-in-2026-whats-new-and-what-organizations-must-know)
- Prepare for CMMC Certification: Steps to Take
- What You Need to Know Heading Into 2026 | Fortra (https://fortra.com/blog/cmmc-compliance-what-you-need-know-heading-2026)
- klcconsulting.net (https://klcconsulting.net/cmmc-implementation-strategies-case-study)
- Planning Your 2026 CMMC Compliance Roadmap (https://cybersheath.com/resources/blog/planning-your-2026-cmmc-compliance-roadmap)
- CMMC compliance reckoning for defense contractors arrives | Federal News Network (https://federalnewsnetwork.com/commentary/2025/12/cmmc-compliance-reckoning-for-defense-contractors-arrives)
- Pentagon begins enforcing CMMC compliance, but readiness gaps remain (https://defensescoop.com/2025/11/10/cmmc-compliance-dod-enforcement-defense-industry-readiness-gaps)
- Maintain Compliance: Strategies for Ongoing Success
- CMMC: New Era of Cybersecurity Compliance for Defense Contractors | Alston & Bird (https://alston.com/en/insights/publications/2025/11/cmmc-cybersecurity-compliance-defense)
- Why CMMC compliance may matter for your company in 2026 (https://integrisit.com/blog/why-cmmc-compliance-may-matter-for-your-company-in-2026)
- SANS Survey Report: Organizations’ Continuous Monitoring Programs Must Keep Maturing to Yield Full Benefits | Qualys (https://blog.qualys.com/product-tech/2016/12/05/sans-survey-report-organizations-continuous-monitoring-programs-must-keep-maturing-to-yield-full-benefits)
- Pentagon begins enforcing CMMC compliance, but readiness gaps remain (https://defensescoop.com/2025/11/10/cmmc-compliance-dod-enforcement-defense-industry-readiness-gaps)
- Planning Your 2026 CMMC Compliance Roadmap (https://cybersheath.com/resources/blog/planning-your-2026-cmmc-compliance-roadmap)