
In today's digital landscape, where cyber threats are becoming increasingly sophisticated, organizations are confronted with the critical challenge of protecting their digital assets. Managed Security Service Providers (MSSPs) emerge as a vital resource, offering essential cybersecurity services that not only enhance protection but also facilitate compliance with regulatory standards. As the threat landscape continues to evolve, businesses must ask themselves: how can they effectively leverage MSSP partnerships to strengthen their defenses while navigating the complexities of compliance and risk management?
The implications for organizations are profound. Cybersecurity is no longer just an IT issue; it’s a fundamental aspect of business strategy. With the rise of data breaches and cyberattacks, the stakes have never been higher. Organizations that fail to prioritize cybersecurity risk not only their assets but also their reputation and customer trust. Therefore, understanding how to utilize MSSPs effectively is crucial for any organization aiming to stay ahead in this challenging environment.
By partnering with MSSPs, businesses can access a wealth of expertise and resources that may otherwise be out of reach. These partnerships can lead to enhanced security measures, streamlined compliance processes, and ultimately, a more resilient organization. As we delve deeper into the unique challenges faced by organizations today, it becomes clear that the right MSSP partnership can be a game-changer in the fight against cyber threats.
In today's digital landscape, cybersecurity is not just an option; it's a necessity. (MSSPs) are specialized firms that deliver a comprehensive suite of , including:
By adopting a subscription model, these providers enable organizations to delegate their security needs, gaining access to a wealth of expertise without the burden of maintaining extensive internal resources.
As the cybersecurity environment evolves, the benefits of partnering with MSSPs become increasingly clear. For instance, organizations utilizing (MDR) services have reported a remarkable 62% reduction in incidents and a 50% decrease in detection and response times. By 2026, a significant number of organizations are expected to rely on MSSPs to bolster their , driven by the escalating complexity of cyber threats and the urgent need for .
Key trends indicate that MSSPs will continue to integrate advanced technologies, such as AI and machine learning, to enhance and streamline incident response processes. This evolution underscores the vital role that plays in protecting businesses from the ever-expanding array of cyber risks. Are you prepared to take the necessary steps to protect your organization?

In today's digital landscape, the importance of cybersecurity cannot be overstated, especially for healthcare organizations. play a pivotal role in fortifying an organization's through a range of essential functions:
By leveraging these functions, organizations can effectively assess their protection needs and recognize the substantial value that managed service provider cybersecurity partnerships can bring to their .

Partnering with a is not just a choice; it’s a strategic imperative for organizations looking to enhance their . In today’s landscape, where cyber threats are increasingly sophisticated, the need for robust protection has never been more critical.
These advantages collectively highlight the significance of in enhancing a firm's overall protection strategy. Notably, 80% of SMBs with a formal incident response plan were able to prevent major damage during an attack, showcasing the effectiveness of MSSP partnerships in improving protection outcomes.

(MSSPs) are essential in guiding organizations toward achieving and maintaining compliance with various regulatory frameworks. In today’s landscape, where cybersecurity threats loom large, the expertise of MSSPs becomes invaluable.
By partnering with a , companies can mitigate the risk of non-compliance penalties while also enhancing their overall security posture. This proactive approach positions them for success in an increasingly regulated environment.

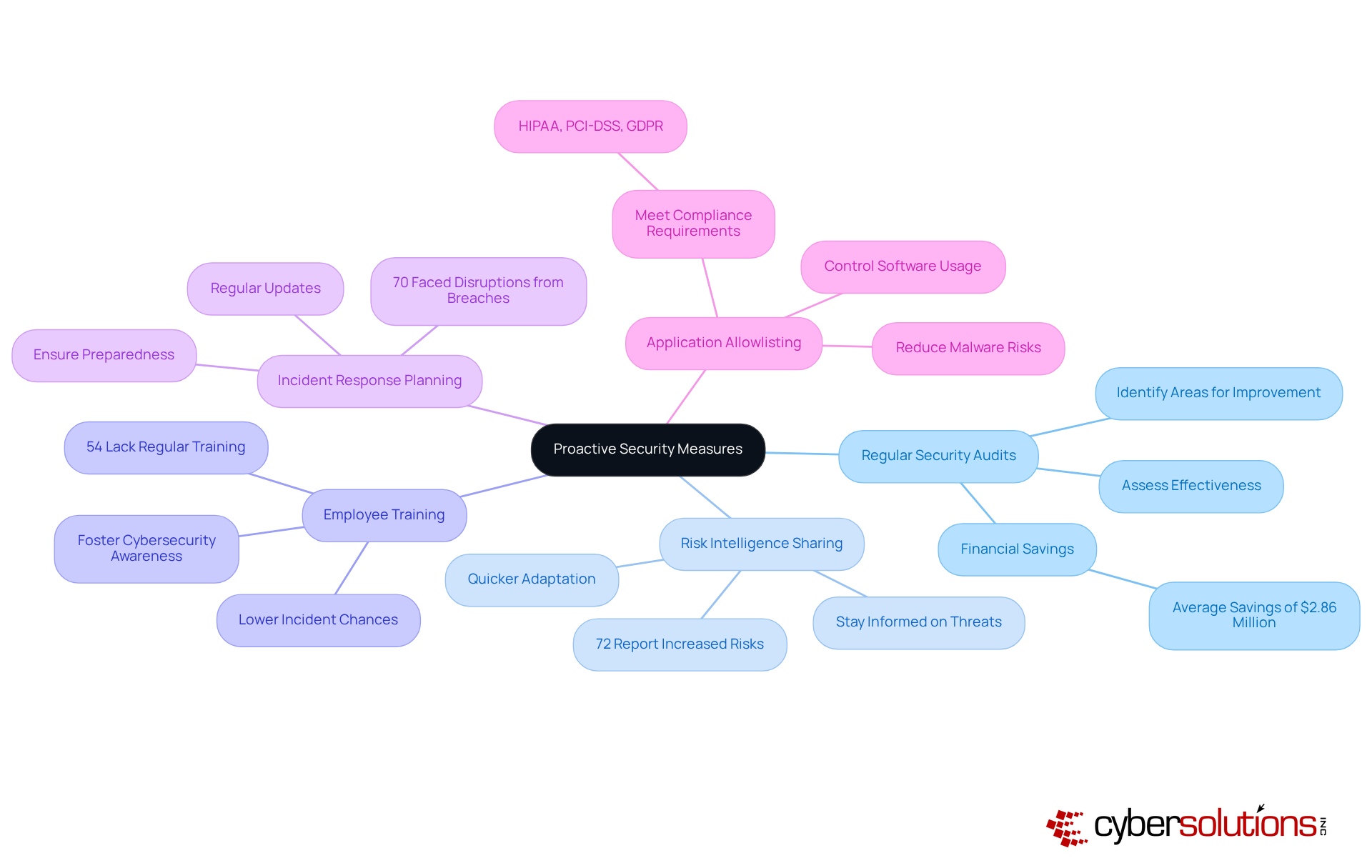
In today’s digital landscape, the importance of cybersecurity in healthcare cannot be overstated. As cyber threats continue to evolve, healthcare organizations face unique challenges that demand proactive measures. Partnering with a cyber security is essential for implementing effective protective strategies.
By adopting these proactive measures, organizations can significantly enhance their cybersecurity resilience and reduce the likelihood of successful attacks. Are you ready to navigate the complexities of modern cyber threats effectively?
In today’s rapidly evolving cybersecurity landscape, the role of Managed Security Service Providers (MSSPs) is not just important; it’s essential for organizations aiming to strengthen their security postures. By tapping into the expertise and resources that MSSPs provide, businesses can effectively tackle the complexities of cyber threats, ensuring they remain resilient in an ever-changing environment.
Partnering with MSSPs offers several key advantages:
These services not only help organizations mitigate risks but also allow them to concentrate on their core operations while ensuring regulatory compliance and the continuous enhancement of their security frameworks. The integration of advanced technologies, such as AI and machine learning, further boosts the effectiveness of MSSP strategies in combating cyber threats.
As cyber risks continue to escalate, the necessity of adopting proactive security measures cannot be overstated. Organizations must take decisive action by engaging with MSSPs to strengthen their defenses, conduct regular security audits, and invest in employee training. By doing so, they can foster a robust cybersecurity culture that not only safeguards sensitive information but also positions them for long-term success in an increasingly regulated landscape. Embracing these strategies empowers organizations to navigate the complexities of modern cyber threats with confidence and resilience.
What are Managed Security Service Providers (MSSPs)?
MSSPs are specialized firms that provide a comprehensive suite of cybersecurity services, including continuous monitoring, threat detection, incident response, and compliance management, allowing organizations to delegate their security needs.
How do MSSPs help organizations in cybersecurity?
MSSPs enable organizations to access expert cybersecurity services through a subscription model, reducing the burden of maintaining extensive internal resources and enhancing their cybersecurity posture.
What are the reported benefits of using MSSPs?
Organizations utilizing Managed Detection and Response (MDR) services have reported a 62% reduction in incidents and a 50% decrease in detection and response times.
What key trends are expected in the MSSP industry?
MSSPs are expected to integrate advanced technologies, such as AI and machine learning, to enhance risk detection capabilities and streamline incident response processes.
What are the primary functions of MSSPs?
The primary functions of MSSPs include 24/7 monitoring, incident response, vulnerability management, compliance management, and reporting and analytics.
How does 24/7 monitoring benefit organizations?
Continuous surveillance of network traffic and systems allows MSSPs to detect and respond to threats in real-time, providing comprehensive protection across various platforms.
What is the significance of incident response provided by MSSPs?
MSSPs offer rapid response capabilities that minimize damage and recovery time, often addressing cyber incidents within 12 hours.
How do MSSPs assist with vulnerability management?
MSSPs conduct regular assessments to identify and remediate security weaknesses, helping organizations maintain a robust security posture.
What role do MSSPs play in compliance management?
MSSPs ensure organizations meet industry-specific regulatory requirements, enhancing their ability to protect sensitive information and qualify for government contracts.
What type of reporting and analytics do MSSPs provide?
MSSPs provide comprehensive reports on incidents and trends, helping organizations understand their risk environment and make informed cybersecurity investment decisions.