
Navigating the complex landscape of cybersecurity regulations demands a deep understanding of CMMC compliance. As organizations encounter heightened scrutiny and evolving requirements, the stakes for adhering to the Cybersecurity Maturity Model Certification have never been higher. This article outlines five crucial steps that clarify when CMMC compliance is necessary and empower organizations to devise effective strategies for meeting these standards.
What challenges do businesses face as they strive to align with these stringent regulations? How can they prepare proactively for the compliance landscape ahead?
Understand the critical importance of the framework, which consists of three certification levels tailored to the sensitivity of the information you manage. Level 1 requires an annual self-assessment, while Level 2 involves both self-assessment and third-party evaluation. Level 3, the most rigorous, mandates certification by the Department of Defense.
Dive into the specific requirements outlined in the guidelines, focusing on the essential security practices for each level. This structured approach ensures that organizations are evaluated based on their risk profiles and data handling capabilities, which is vital in today’s threat landscape.
Identify the Controlled Unclassified Information (CUI) your organization oversees; this will dictate the level of adherence required. Understanding the nature of your data is crucial for determining the compliance level and associated practices. Are you aware of how your data impacts your compliance journey?
Stay informed about the staged rollout schedule, noting that adherence standards officially began on November 10, 2025. This phased strategy allows organizations to gradually adapt to the new requirements while ensuring compliance is effectively enforced throughout the defense ecosystem. Alarmingly, only 1% of Defense Industrial Base contractors are fully prepared for audits, underscoring the urgency for organizations to prioritize compliance.
Refer to official DoD resources, including the latest guidelines, for the latest guidelines and updates regarding compliance with the framework. Engaging with these materials will help organizations navigate the complexities of regulatory requirements and maintain audit readiness. Additionally, consider leveraging Compliance as a Service from Cyber Solutions, which provides comprehensive solutions for regulatory adherence, including audit preparation, ongoing monitoring, and expert guidance to ensure your organization meets security standards efficiently.

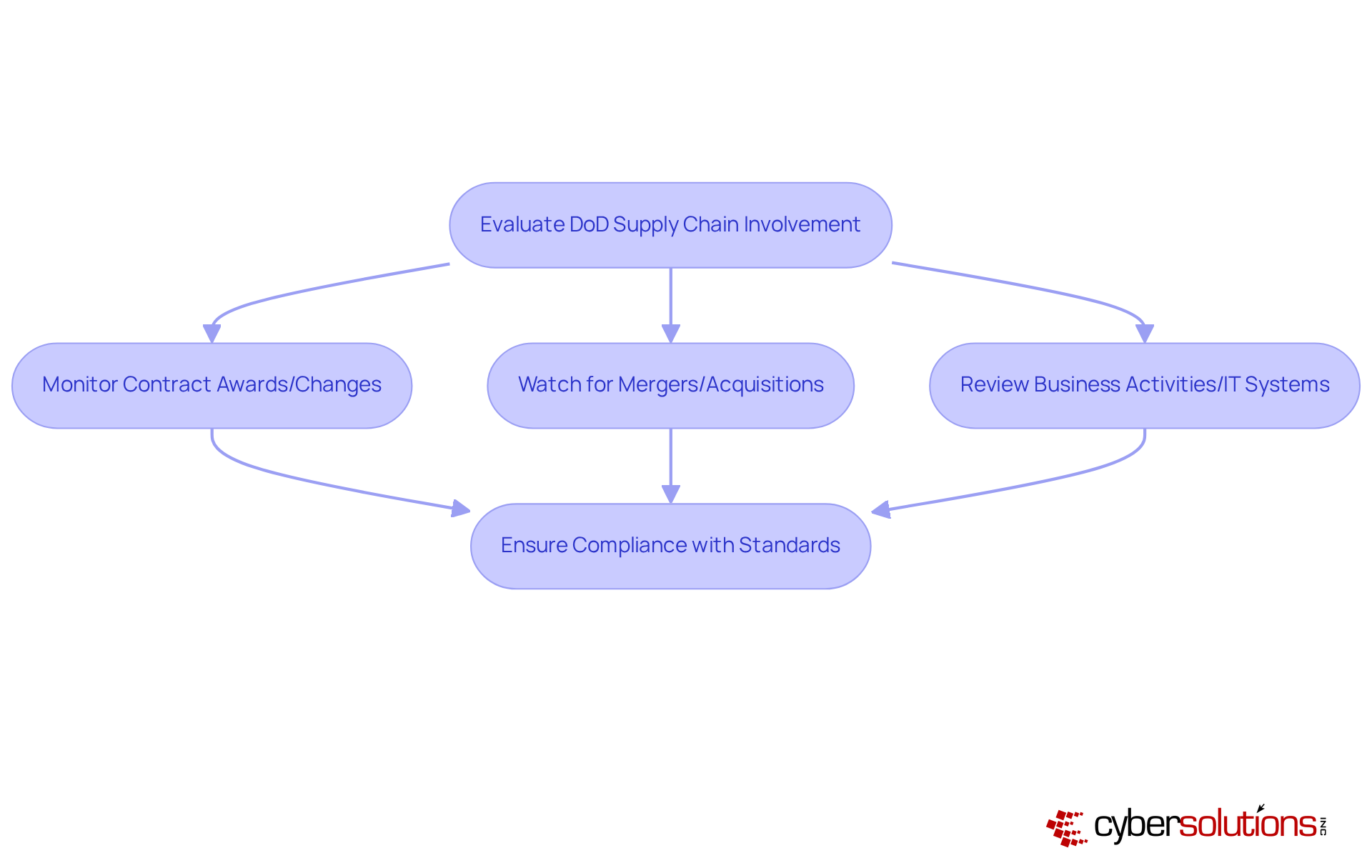
Evaluate whether your organization is part of the defense industrial base. This is crucial for meeting compliance requirements. Stay vigilant regarding contract awards and changes; it's important to know when CMMC compliance is required, as new agreements increasingly incorporate cybersecurity standards, which are vital for your eligibility.
Keep an eye on any contract modifications, as these events may require a reassessment of your adherence status to align with new operational structures. Additionally, monitor any changes in regulations or IT systems that could impact your compliance efforts. Ensure that every aspect of your organization complies with relevant standards.
It is important to regularly review your compliance status to understand potential triggers. Staying informed about new triggers or alterations is key to maintaining compliance.

To develop a tailored compliance strategy for achieving CMMC compliance, it’s crucial to understand when compliance is required and the pressing need for robust cybersecurity in healthcare. With the increasing frequency of cyberattacks, healthcare organizations face unique challenges that demand immediate attention.
By following these steps, organizations can cultivate a strong regulatory approach that not only fulfills necessary standards but also significantly enhances their overall security posture, particularly when compliance is required.

Execute the plan by implementing the identified changes and enhancements to your systems. Tackling adherence gaps is crucial; customized remediation approaches, including policy revisions and system enhancements, ensure alignment with regulations.
Educate staff on new policies and procedures related to cybersecurity. Structured programs that highlight the significance of cybersecurity awareness and adherence to standards are essential. Did you know that effective training can significantly reduce regulatory risks and enhance your overall compliance?
It is important to regularly review and update security controls to ensure they remain effective, especially when compliance is required. Organizations that conduct regular assessments are better equipped to adapt to changing threats and uphold regulations.
Schedule audits to evaluate adherence status and make necessary adjustments. These audits should be thorough, encompassing all facets of the compliance requirements to ensure preparedness for certification evaluations.
It is essential to document and maintain records to demonstrate compliance when audits are required during assessments. This documentation is crucial, providing evidence of adherence and being pivotal during audits or in the event of a data breach.
Understanding the requirements for CMMC compliance is not just important; it’s essential for businesses within the Department of Defense supply chain. As cybersecurity threats grow increasingly sophisticated, organizations must take decisive steps to meet the necessary standards for cybersecurity maturity. By recognizing specific certification levels, identifying compliance triggers, assessing current cybersecurity practices, developing a tailored compliance strategy, and implementing necessary changes, organizations can effectively navigate the complexities of CMMC.
Key points to consider include:
The reality is stark: many defense contractors are currently unprepared for the compliance demands ahead. Utilizing resources such as official DoD guidelines and Compliance As A Service (CaaS) can significantly ease this process.
Ultimately, CMMC compliance transcends mere regulatory obligation; it is a vital component of safeguarding sensitive information in an increasingly perilous digital landscape. Organizations must prioritize their cybersecurity strategies, ensuring they are not only compliant but also resilient against evolving threats. Taking decisive action today will fulfill compliance requirements and enhance overall cybersecurity posture, paving the way for a more secure future.
What is the Cybersecurity Maturity Model Certification (CMMC)?
The CMMC is a framework consisting of three certification levels designed to enhance cybersecurity practices in organizations, particularly those handling Controlled Unclassified Information (CUI).
What are the certification levels in CMMC?
There are three levels: Level 1 requires an annual self-assessment, Level 2 involves both self-assessment and third-party evaluation, and Level 3 mandates certification by the Defense Industrial Base Cybersecurity Assessment Center (DIBCAC).
How does the nature of data affect CMMC compliance?
The type of Controlled Unclassified Information (CUI) an organization manages determines the level of compliance required, influencing the necessary practices and certification level.
When did the CMMC compliance standards officially begin?
The adherence standards officially began on November 10, 2025, with a staged rollout strategy for organizations to gradually adapt to the new requirements.
What is the current state of compliance readiness among Defense Industrial Base contractors?
Alarmingly, only 1% of Defense Industrial Base contractors are fully prepared for audits, highlighting the urgency for organizations to prioritize compliance.
Where can organizations find official guidelines for CMMC compliance?
Organizations should refer to official Department of Defense (DoD) resources, including the Accreditation Body and the Defense Federal Acquisition Regulation Supplement (DFARS), for the latest compliance guidelines and updates.
What is Compliance As A Service (CaaS)?
Compliance As A Service (CaaS) is a service offered by Cyber Solutions that provides comprehensive solutions for regulatory adherence, including audit preparation, ongoing monitoring, and expert guidance to help organizations meet security standards efficiently.
How can organizations identify when CMMC compliance is required?
Organizations should evaluate their participation in the DoD supply chain, stay informed about contract awards and changes, and monitor any mergers, acquisitions, or modifications in business activities that could impact compliance requirements.
Why is it important to regularly review updates from the DoD?
Regularly reviewing updates from the DoD helps organizations stay informed about new triggers or changes that may affect their compliance status, ensuring they remain aligned with regulatory standards.