
Deep Packet Inspection (DPI) is not just a technical term; it’s a vital component of modern cybersecurity that organizations must embrace to combat increasingly sophisticated threats. As cybercriminals exploit the complexities of encrypted data, the need to implement DPI effectively alongside SSL best practices becomes paramount. Yet, organizations face a daunting challenge: how to balance robust security measures with privacy concerns, performance impacts, and implementation complexities.
How can organizations navigate these challenges? By enhancing their cybersecurity posture and safeguarding sensitive information, they can not only protect their assets but also build trust with their stakeholders. The implications for healthcare organizations are particularly significant, as they must ensure compliance while defending against evolving threats.
In this landscape, Cyber Solutions emerge as a critical ally, offering strategies that address these multifaceted challenges. With the right approach, organizations can leverage DPI to fortify their defenses without compromising on privacy or performance.
is a critical tool in the fight against sophisticated cyber threats. In an era where healthcare organizations face increasing risks, understanding and implementing DPI can be a game changer. Unlike traditional packet filtering that merely skims header information, DPI thoroughly analyzes the entire packet, including its payload. This comprehensive approach allows organizations to uncover and tackle complex threats that might otherwise remain hidden.
In today’s , DPI plays an essential role by enabling real-time monitoring of network traffic. It effectively detects harmful activities and enforces protection policies. For example, DPI can identify malware, unauthorized access attempts, and data exfiltration by scrutinizing packet content. As cyber threats evolve, the ability to conduct in-depth analysis becomes vital for maintaining a strong security posture.
Moreover, DPI helps organizations meet by ensuring sensitive information is protected during transmission. With approximately 98% of internet traffic in the U.S. utilizing HTTPS, implementing is crucial for into encrypted traffic. This step is necessary to fortify defenses against cybercriminals who exploit encryption. By integrating DPI with - an approach that proactively prevents unauthorized software from running and includes features like continuous monitoring and centralized management - businesses can significantly bolster their overall security framework.
not only minimizes the attack surface but also aids in meeting compliance standards such as , , and GDPR. This makes it an indispensable element of any cybersecurity strategy. Together, these measures ensure that organizations remain eligible for lucrative government contracts while effectively and Federal Contract Information (FCI).

In today's digital landscape, the integration of SSL (Secure Sockets Layer) certificates with is not just important - it's essential for organizations that handle sensitive information. With over 90% of now encrypted, relying solely on conventional protective measures is no longer enough to ensure .
play a vital role in encrypting data during transit, thereby protecting confidentiality. However, this . This is where DPI comes into play, enabling the examination of encrypted traffic to identify and manage potential risks.
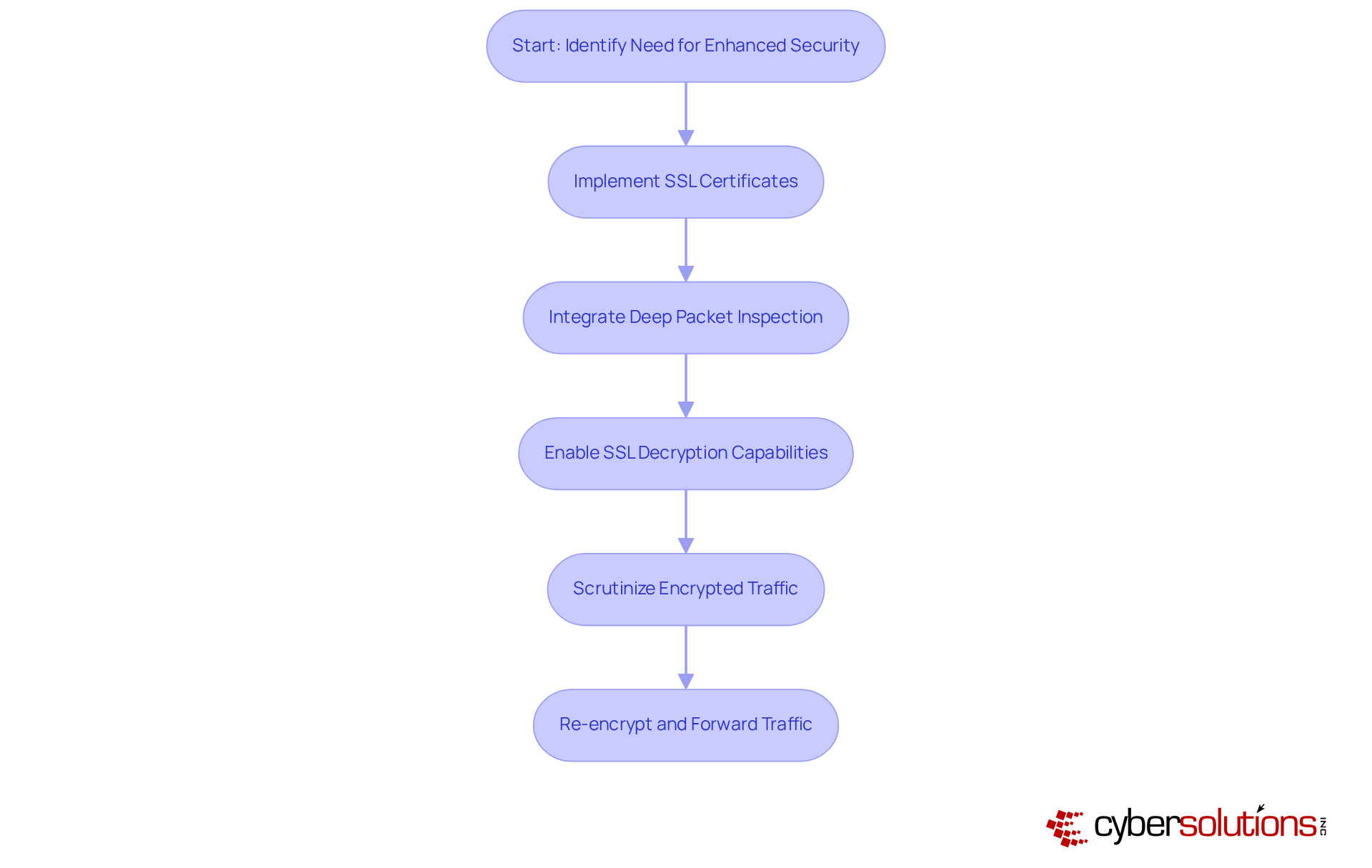
To effectively combine SSL with , within their DPI solutions. This allows security teams to scrutinize the contents of encrypted packets without compromising information integrity. For instance, a firewall equipped with DPI can decrypt SSL traffic, assess it for threats, and then re-encrypt it before forwarding it to its intended destination. This not only bolsters security but also ensures .
The necessity of is highlighted by the alarming statistic that , often worsened by the inability to effectively. By merging deep packet inspection SSL with SSL, organizations can adopt a robust strategy to secure network traffic, enabling them to detect and respond to risks that might otherwise remain concealed. This proactive approach is crucial in an era where cyber threats are increasingly sophisticated and pervasive.
To effectively implement in cybersecurity, organizations must prioritize that enhance their . ; it’s a strategic imperative that can safeguard sensitive data and maintain trust.
By adhering to these and addressing the associated challenges and pitfalls, organizations can maximize the effectiveness of their implementations, which significantly enhances their overall cyber. As Adam Fletcher noted, "Cybersecurity isn’t about avoiding risk - it’s about ," underscoring the necessity for a strategic approach to DPI.

Deploying Deep Packet Inspection (DPI) is crucial for enhancing cybersecurity, yet it comes with significant challenges that organizations must navigate:
By proactively addressing these challenges, organizations can facilitate a smoother deployment of DPI, ultimately strengthening their cybersecurity defenses and ensuring .

Deep Packet Inspection (DPI) is not just a technical term; it’s a cornerstone of modern cybersecurity strategies, especially for organizations that handle sensitive data. In a world where cyber threats are becoming increasingly sophisticated, the ability to analyze network traffic in detail is crucial. DPI empowers organizations to detect and mitigate threats that traditional methods might miss. By integrating SSL with DPI, organizations gain enhanced visibility into encrypted traffic and ensure compliance with essential data protection regulations, significantly strengthening their security frameworks.
The article highlights several key insights into DPI's role, including its effectiveness in identifying malware, preventing unauthorized access, and maintaining regulatory compliance. Implementing DPI effectively requires clear objectives, regular updates, and comprehensive staff training. However, organizations must also navigate challenges such as privacy concerns and the complexities of implementation. This underscores the need for strategic planning and ongoing management to ensure success.
The importance of adopting robust DPI practices cannot be overstated. As cyber threats evolve, organizations must prioritize the integration of DPI and SSL to establish a resilient cybersecurity posture. This proactive approach not only safeguards sensitive information but also fosters trust with stakeholders, creating a secure digital environment for everyone involved. Taking decisive steps in this direction is essential for navigating the ever-changing landscape of cybersecurity and protecting valuable assets against emerging threats.
What is Deep Packet Inspection (DPI)?
Deep Packet Inspection (DPI) is a cybersecurity tool that analyzes the entire packet of data, including its payload, to uncover and address complex cyber threats.
How does DPI differ from traditional packet filtering?
Unlike traditional packet filtering, which only examines header information, DPI thoroughly analyzes the entire packet, allowing for a more comprehensive understanding of potential threats.
What role does DPI play in cybersecurity?
DPI enables real-time monitoring of network traffic, detects harmful activities, enforces protection policies, and helps organizations maintain a strong security posture against evolving cyber threats.
What types of threats can DPI identify?
DPI can identify malware, unauthorized access attempts, and data exfiltration by scrutinizing the content of data packets.
How does DPI assist with regulatory compliance?
DPI helps organizations protect sensitive information during transmission, ensuring compliance with regulations such as HIPAA, PCI-DSS, and GDPR.
Why is implementing DPI for HTTPS traffic important?
With approximately 98% of internet traffic in the U.S. utilizing HTTPS, implementing DPI for SSL is crucial for enhancing visibility into encrypted traffic and fortifying defenses against cybercriminals.
What is application allowlisting and how does it relate to DPI?
Application allowlisting is a proactive approach that prevents unauthorized software from running. When integrated with DPI, it enhances overall security by minimizing the attack surface and aiding in compliance.
What are the benefits of combining DPI with application allowlisting?
The combination significantly bolsters an organization's security framework, minimizes the attack surface, and helps meet compliance standards, ensuring eligibility for government contracts while protecting sensitive information.