
In an era where cyber threats are more pronounced than ever, organizations must navigate the intricate landscape of IT security outsourcing with precision. Choosing the right provider transcends mere convenience; it is a pivotal step in protecting sensitive information and ensuring compliance with industry regulations. This article explores four essential steps that empower businesses to effectively evaluate potential IT security outsourcing companies.
How can organizations ensure they select a partner that not only meets their security needs but also adapts to the constantly evolving threat landscape?
In today's digital landscape, the importance of IT security cannot be overstated, especially for organizations that handle sensitive information. With the rise of cyber threats, it’s essential to thoroughly research outsourcing companies to ensure they have the necessary expertise and industry knowledge. Look for certifications like CISSP and CISM, which serve as critical indicators of proficiency in information security. For instance, certified professionals, with holders earning an average salary of $115,000, underscoring their value in the industry.
When evaluating potential suppliers, examine the range of services they offer to ensure alignment with your organization's specific needs. Key offerings to consider include managed security services, incident response, and risk assessment. These are vital for maintaining a robust defense. A reputable supplier should be delivering tailored solutions that enhance security frameworks and improve incident management efficiency.
To gauge the effectiveness of a supplier's offerings, request case studies or client testimonials. For example, Auxis established a partnership that significantly bolstered a client's resilience through continuous monitoring and rapid response capabilities. Such real-world examples provide valuable insights into how a supplier has successfully tackled challenges akin to those your organization may encounter.
Moreover, assess the ability of the supplier to scale their services as your organization grows. The landscape is ever-evolving, and a flexible supplier can adapt to changing requirements, ensuring that your protective measures remain effective over time. With nearly 60% of data incidents stemming from third-party risks, selecting a supplier that integrates seamlessly with your existing systems is crucial for minimizing vulnerabilities and enhancing overall security.

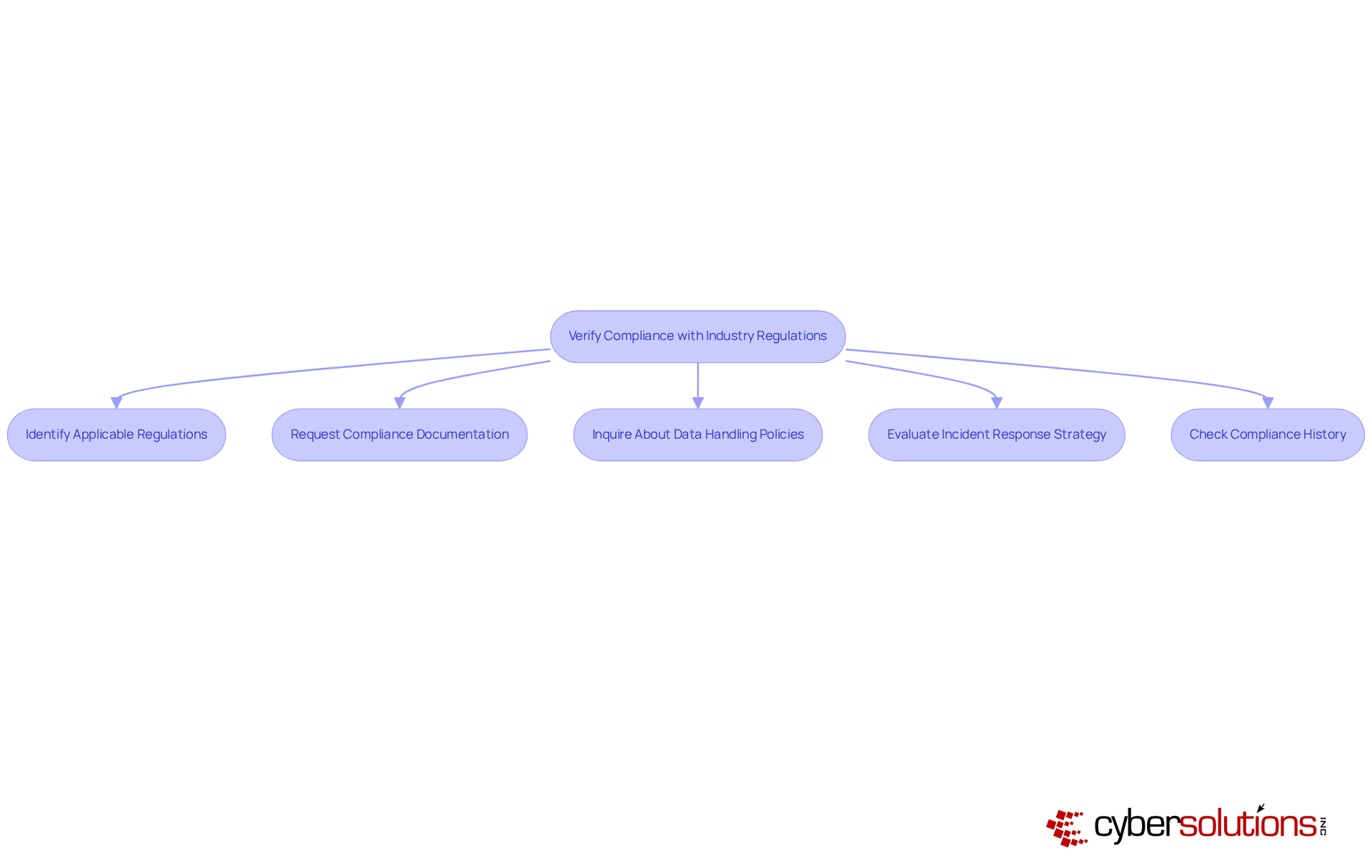
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially in industries like healthcare and finance. Identifying the frameworks such as HIPAA or PCI DSS is crucial, as these frameworks dictate essential security measures.
Request comprehensive documentation of the provider's policies. This ensures they adhere to regulations and best practices, which is vital for safeguarding sensitive information. Inquire about their certifications to confirm alignment with regulatory standards. After all, protecting sensitive information is paramount.
Evaluate their history concerning regulatory standards. Are they prepared to handle potential violations effectively? A proactive approach is essential for mitigating risks. Additionally, verify their compliance record by looking for any significant breaches or penalties. A strong track record is indicative of a reliable partner in cybersecurity, one who can navigate the complexities of regulatory demands with confidence.
By taking these steps, you not only protect your organization but also position yourself as a leader in the commitment to cybersecurity excellence.
When it comes to budgeting, choosing the right pricing model is crucial. Flat-rate pricing offers predictability, simplifying financial planning by eliminating unexpected IT expenses. This model typically encompasses everything from email licenses to software updates, providing peace of mind in one comprehensive package. On the other hand, pay-as-you-go models offer flexibility, allowing you to adapt to changing needs.
It's essential to examine contracts closely to ensure a clear understanding of pricing and performance metrics. SLAs outline the expected standard of support, including response times and uptime guarantees, which are vital for maintaining service quality in your organization.
Be vigilant for hidden costs that may arise from usage. Understanding the full range of potential costs can help you avoid surprises and ensure that your chosen supplier aligns with your financial expectations.
Make sure the contract includes termination clauses. This flexibility is key to avoiding long-term commitments that may not suit your evolving business needs.
Finally, assess the overall value by considering both services and costs. A thorough evaluation should weigh the benefits of the services provided against their costs, ensuring that the selected provider delivers optimal value for your investment.

In today's digital landscape, the importance of cybersecurity cannot be overstated. Organizations face a myriad of threats, from ransomware to phishing attacks, making robust protection technologies essential. Ask about the security technologies, such as firewalls and intrusion detection systems, which are crucial for safeguarding networks against unauthorized access. Cyber Solutions offers comprehensive services tailored to your business needs, ensuring a strong defense against cyber threats.
Evaluate the provider's approach to incident response. Efficient systems can significantly lower incident costs by an average of $3.81 million while enhancing overall risk posture. Organizations that leverage automation and AI for protection can save over $3 million for each data incident, underscoring the financial benefits of strong cybersecurity practices. Continuous monitoring from Cyber Solutions ensures that suspicious activities are detected and halted before they escalate into serious threats, protecting your business from various cyberattacks.
Examine their security protocols and data loss prevention tactics to ensure sensitive information is adequately safeguarded. In the first half of 2023 alone, data breaches increased significantly. Alarmingly, this trend continues, highlighting the urgency of adopting effective protective measures.
Assess their compliance measures to guarantee transparency and accountability. Organizations with strong cybersecurity practices are more resilient compared to those that do not. With 94% of SMBs reporting cyberattacks in 2024, the need for robust security solutions is more critical than ever. Finally, inquire about their incident management strategies to understand their preparedness for potential incidents.

Evaluating IT security outsourcing companies is not just a task; it’s a vital process that requires strategic planning and careful consideration. The security of sensitive information depends on selecting a provider with the right expertise, adherence to industry regulations, a transparent pricing structure, and robust security measures. By following the outlined steps, organizations can ensure they partner with a capable supplier that aligns with their cybersecurity needs and objectives.
Key points to consider include:
These elements are essential in creating a comprehensive evaluation framework that not only protects an organization from cyber threats but also enhances its overall security posture.
Ultimately, the significance of thorough evaluation cannot be overstated. Organizations must prioritize cybersecurity by choosing providers that demonstrate proven capabilities and a commitment to compliance and innovation. By taking these proactive steps, businesses can safeguard their assets, maintain customer trust, and position themselves as leaders in the ever-evolving landscape of cybersecurity.
Why is cybersecurity important for organizations?
Cybersecurity is crucial for organizations that handle sensitive information, especially in today's digital landscape where the rise of cyber threats poses significant risks.
What should I look for when evaluating IT security outsourcing companies?
When evaluating IT security outsourcing companies, consider their expertise, industry knowledge, and relevant certifications such as CISSP and CISM, which indicate proficiency in cybersecurity.
What is CISSP certification and why is it important?
CISSP certification is recognized as the gold standard in information protection. It signifies a high level of expertise in cybersecurity, with holders earning an average salary of $115,000, highlighting their value in the industry.
What key services should I consider when choosing a cybersecurity provider?
Key services to consider include incident response and vulnerability assessments, which are vital for maintaining a robust cybersecurity defense.
How can I assess a supplier's effectiveness in cybersecurity?
To assess a supplier's effectiveness, request case studies or references from similar industries. Real-world examples, such as the establishment of a Security Operations Center (SOC) that enhances cybersecurity resilience, can provide valuable insights.
Why is it important for a cybersecurity provider to scale their services?
It is important for a cybersecurity provider to scale their services as your organization grows because the cybersecurity landscape is constantly evolving. A flexible supplier can adapt to changing requirements, ensuring that protective measures remain effective over time.
What percentage of data incidents are related to third-party risks?
Nearly 60% of data incidents stem from third-party risks, making it crucial to select a supplier that integrates seamlessly with your existing systems to minimize vulnerabilities and enhance overall security.