
In today's world, cyber threats are more prevalent than ever, making robust security management essential - especially in sensitive sectors like healthcare. Security Information and Event Management (SIEM) systems have become crucial tools, providing organizations with a comprehensive approach to threat detection and incident response. Yet, many organizations find themselves grappling with the effective implementation and management of these solutions. What best practices can transform SIEM from a mere compliance tool into a formidable ally against sophisticated cyber threats?
As the landscape of cybersecurity continues to evolve, healthcare organizations face unique challenges that demand immediate attention. The implications of inadequate security measures can be dire, affecting not only patient safety but also organizational integrity. By understanding these challenges, CFOs can better appreciate the necessity of investing in robust cybersecurity solutions.
To address these pressing issues, organizations must adopt a proactive stance. Implementing best practices for SIEM can significantly enhance an organization's security posture, ensuring that they are not just compliant but also resilient against emerging threats. This is not merely a technical upgrade; it’s a strategic imperative that can safeguard sensitive data and maintain trust in healthcare systems.
In today's digital landscape, cybersecurity is not just a necessity; it's a critical component of operational integrity, especially in healthcare. The role of SIEM is pivotal in this arena, meticulously collecting and analyzing data from a company's entire IT infrastructure. By providing immediate insights into incidents, SIEM empowers organizations to swiftly identify and mitigate risks, significantly reducing potential harm. For instance, entities leveraging advanced SIEM systems have reported a remarkable 70% decrease in false positives, enhancing their ability to detect genuine threats.
The centralization of security data through SIEM not only strengthens proactive security measures but also assists in meeting compliance requirements. As organizations navigate an increasingly complex risk environment, the importance of SIEM becomes even more pronounced. Current trends indicate that effective security teams are shifting their focus from merely acknowledging risks to actively seeking out anomalies, which facilitates more efficient risk identification.
Moreover, with Cyber Solutions offering advanced analytics, organizations gain the advantage of instant alerts and real-time insights. This capability allows for rapid responses to prevent downtime or breaches. Continuous monitoring ensures that suspicious activities are identified and neutralized before they escalate into serious threats, safeguarding businesses against ransomware, phishing, and other malware attacks. Additionally, Cyber Solutions provides tailored access controls, ensuring that only authorized users can access sensitive information, further enhancing security.
Statistics reveal that companies typically see a favorable return on investment within 6 to 9 months of implementing SIEM. However, it's crucial to note that 70% of industry leaders find their existing systems inadequate for identifying sophisticated risks, highlighting the challenges organizations face. Legacy systems often struggle to manage billions of daily events while maintaining performance, making the adoption of SIEM essential for modern security. With the upcoming cybersecurity regulations, the focus on SIEM's role in defending against ransomware threats remains both timely and relevant.

In today's digital landscape, the importance of cybersecurity cannot be overstated. With increasing threats from cybercriminals, healthcare organizations face challenges that demand immediate attention. The SIEM system is crucial for security management by collecting and standardizing information from various sources, such as firewalls, intrusion detection systems, and endpoint devices.
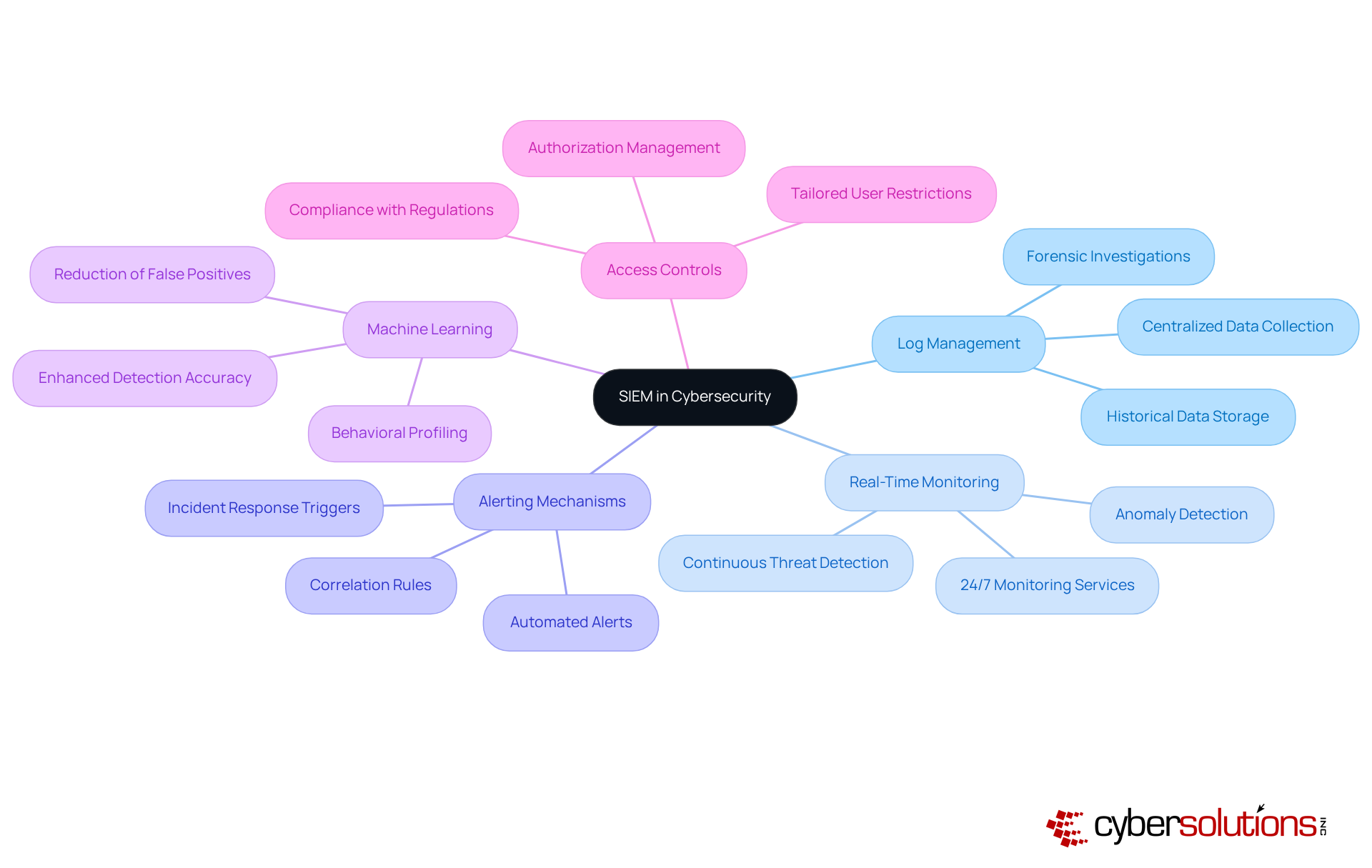
Among the standout features of SIEM in security solutions are data aggregation, real-time monitoring, and alerting mechanisms. These capabilities enable security teams to respond promptly to incidents, ensuring that potential threats are addressed before they escalate. By employing correlation rules, SIEM systems in security platforms analyze data patterns to identify suspicious activities, generating alerts that prompt immediate investigation. This proactive approach is essential in a sector where the stakes are high.
Moreover, sophisticated SIEM systems in security platforms utilize machine learning and artificial intelligence to enhance detection accuracy, significantly reducing false positives. This capability allows organizations to respond swiftly to potential dangers, minimizing the risk of data breaches and operational disruptions. With Cyber Solutions' advanced analytics, entities can detect anomalies and vulnerabilities in real-time, facilitating quick action to prevent downtime or breaches.
Additionally, Cyber Solutions offers access controls and restrictions, ensuring that only authorized users have access to sensitive information. Our services are designed to grow with your business, adapting to new challenges as your operations expand. In a world where cybersecurity threats are ever-evolving, partnering with a trusted provider like Cyber Solutions is not just a choice - it's a necessity.
In today’s digital landscape, SIEM is a critical component of operational integrity, especially in healthcare. With the rise of sophisticated cyber threats, healthcare organizations face unique challenges that demand immediate attention. Deploying a SIEM solution can significantly enhance risk detection and streamline response times, ensuring that organizations are not just reactive but proactive in their security measures.
A centralized perspective on incidents allows teams to swiftly identify and address threats, minimizing potential damage. Organizations that have integrated SIEM technology report a marked decrease in response times. By centralizing security events and automating alerts, the response process becomes more efficient, ultimately bolstering the overall security posture of the organization.
Moreover, SIEM solutions are instrumental in ensuring compliance. Effective monitoring and reporting not only alleviates the burden on IT teams but also enables organizations to maintain regulatory standards. This capability is particularly crucial in sectors like healthcare and finance, where adherence to regulations is non-negotiable.
The impact of SIEM on response times is profound. Organizations leveraging SIEM can react to security incidents with remarkable speed, significantly reducing the risk of data loss and reputational harm. Advanced features such as event correlation and real-time monitoring enhance visibility into network activities, allowing for the prompt detection of unusual behaviors. This results in reduced downtime and increased operational efficiency.
Incorporating a layered approach to security, such as endpoint isolation, malware removal, and user training, further amplifies the effectiveness of SIEM solutions. Continuous monitoring capabilities, as evidenced by case studies on 24/7 network monitoring and incident response, fortify the overall security framework of organizations, providing robust protection against threats like ransomware and phishing attacks.

In today's digital landscape, the importance of cybersecurity cannot be overstated, especially in healthcare. While beneficial, the limitations in security solutions are significant and must be navigated by organizations. One of the most pressing challenges is false positives, stemming from an overwhelming number of alerts. This not only diminishes response effectiveness but also leads to a staggering statistic: up to 30% of a Security Operations Center (SOC) analyst's time is wasted chasing these false alarms. This loss contributes to analyst fatigue and slows down response times, creating a critical vulnerability in an already strained system.
Moreover, the complexity of integrating SIEM tools with existing infrastructures poses additional hurdles. Organizations require skilled personnel to interpret and manage the data effectively, which can be a daunting task. To combat these challenges, Cyber Solutions offers monitoring services of your network, ensuring that anomalies and threats are detected promptly. Ongoing surveillance guarantees that questionable activities are identified and halted before they escalate into serious risks, enabling swift action to prevent interruptions or violations.
As technologies evolve, future advancements in SIEM capabilities in security technology are anticipated to focus on machine learning, automation, and artificial intelligence, including hyperautomation. These innovations can significantly enhance detection and response capabilities, making it imperative for organizations to stay informed and proactive. By embracing these advancements, organizations can ensure their security teams effectively combat emerging threats, safeguarding their operations and protecting sensitive data.

In today’s healthcare landscape, cybersecurity isn’t just important - it’s essential. With regulations like HIPAA and PCI-DSS in play, organizations must navigate a complex compliance environment. SIEM solutions are crucial for entities striving to meet these standards. By automating log collection, monitoring, and reporting, the system simplifies the compliance process, allowing organizations to efficiently produce necessary documentation during audits.
Consider this: organizations utilizing SIEM tools can streamline their compliance initiatives, effectively preventing penalties and minimizing audit fatigue. They achieve this by ensuring data integrity. Moreover, the system’s capability to identify and respond to incidents in real-time significantly enhances a company’s defense posture, thereby reinforcing compliance efforts.
To truly maximize effectiveness, organizations should prioritize integrating compliance considerations into their strategies for security management. This ensures they not only meet regulatory requirements but also enhance their overall security posture. Leveraging Cyber Solutions' Compliance as a Service (CaaS) - which includes risk assessments, policy development, and ongoing compliance monitoring - can further strengthen their efforts.
Additionally, adopting a proactive approach through security measures is vital. This strategy prevents unauthorized software from executing, reducing vulnerabilities and ensuring adherence to stringent data protection protocols. As the regulatory landscape continues to evolve, this comprehensive strategy becomes increasingly important, necessitating ongoing diligence and adaptation. Are you ready to fortify your organization’s compliance and security posture?

In today's digital landscape, the importance of robust cybersecurity cannot be overstated. Organizations face an ever-evolving array of cyber threats that challenge their ability to protect sensitive information. This is where the implementation of Security Information and Event Management (SIEM) becomes essential. By centralizing and analyzing security data, SIEM not only streamlines incident response but also strengthens compliance with regulatory standards. As cyber threats grow more sophisticated, the urgency for effective SIEM solutions has never been greater.
Key practices for leveraging SIEM effectively have been outlined throughout this article. Understanding its core functionalities is crucial, as is recognizing the benefits it brings in enhancing incident response times and compliance management. Additionally, acknowledging the limitations and necessary future enhancements for optimizing performance is vital. These insights underscore the necessity of adopting a proactive approach to security, ensuring organizations are not merely reactive but are equipped to anticipate and mitigate risks.
In a landscape where cybersecurity is paramount, the call to action is clear: organizations must prioritize the integration of advanced SIEM systems into their security frameworks. By doing so, they not only protect sensitive information but also position themselves to navigate the evolving regulatory environment with confidence. Embracing these best practices will empower organizations to build a resilient security posture, ultimately safeguarding their operations against the ever-present threat of cyber incidents.
What is SIEM and why is it important in cybersecurity?
SIEM (Security Information and Event Management) is a system that collects and analyzes data from an organization's entire IT infrastructure. It plays a crucial role in cybersecurity by providing immediate insights into incidents, helping organizations swiftly identify and mitigate risks, thereby reducing potential harm.
How does SIEM improve threat detection?
SIEM improves threat detection by centralizing security information, which enhances proactive security measures and assists in meeting regulatory compliance. Advanced SIEM systems have reported a 70% decrease in false positives, allowing organizations to focus on genuine threats.
What are the key features of SIEM systems?
Key features of SIEM systems include robust log management, real-time monitoring, alerting mechanisms, and the use of correlation rules to analyze data patterns for suspicious activities. These features enable security teams to respond promptly to potential threats.
How does SIEM utilize machine learning and artificial intelligence?
Sophisticated SIEM platforms utilize machine learning and artificial intelligence to enhance detection accuracy, significantly reducing false positives. This allows organizations to respond quickly to potential dangers, minimizing the risk of data breaches and operational disruptions.
What role does continuous monitoring play in SIEM?
Continuous monitoring in SIEM allows organizations to detect anomalies and vulnerabilities in real-time, enabling rapid responses to prevent downtime or breaches. This proactive approach helps safeguard businesses against ransomware, phishing, and other malware attacks.
How do tailored access controls enhance security in SIEM?
Tailored access controls in SIEM ensure that only authorized users can access sensitive information, further enhancing security and protecting against unauthorized access.
What is the expected return on investment for implementing SIEM solutions?
Companies typically see a favorable return on investment within 6 to 9 months of implementing next-generation SIEM solutions.
What challenges do organizations face with existing security systems?
70% of industry leaders find their existing systems inadequate for identifying sophisticated risks. Legacy systems often struggle to manage billions of daily events while maintaining performance, making the adoption of SIEM essential for improving oversight and resilience against evolving cyber threats.
Why is the focus on SIEM relevant with regard to ransomware threats?
The upcoming 2026 Ransomware Summit highlights the ongoing focus on SIEM's role in defending against ransomware threats, emphasizing its importance in the current cybersecurity landscape.