
In an era where healthcare organizations increasingly depend on technology to deliver quality care, the role of IT support service providers is paramount. These specialized firms not only guarantee the seamless operation of IT infrastructure but also protect sensitive patient information amid rising cyber threats. As the stakes escalate, a pressing question arises: how can healthcare entities effectively leverage IT support to navigate regulatory complexities and enhance operational efficiency? This article explores the essential functions of IT support service providers in the healthcare sector, unveiling the transformative impact they can exert on patient care and organizational resilience.
In today's rapidly evolving healthcare landscape, the importance of IT support cannot be overstated. An IT support service provider is a specialized firm that offers a comprehensive range of services within medical organizations. With projections indicating that around 58% of medical organizations are expected to adopt IT support by 2025, there is a clear acknowledgment of the critical need for strong IT assistance. These providers play a vital role in ensuring operational efficiency, delivering tailored solutions that encompass:
As the healthcare sector becomes increasingly technology-driven, the role of an IT support service provider is more crucial than ever. They enable organizations to navigate complex regulatory environments and improve data management. Successful implementations of IT assistance have demonstrated improvements in workflow and patient care, allowing healthcare professionals to focus on their primary mission—delivering quality care. Authorities in the field emphasize that the role of an IT support service provider not only enhances compliance with regulations such as HIPAA but also fortifies defenses against cyber threats. This ensures that medical organizations can operate securely and efficiently in an ever-changing digital landscape.
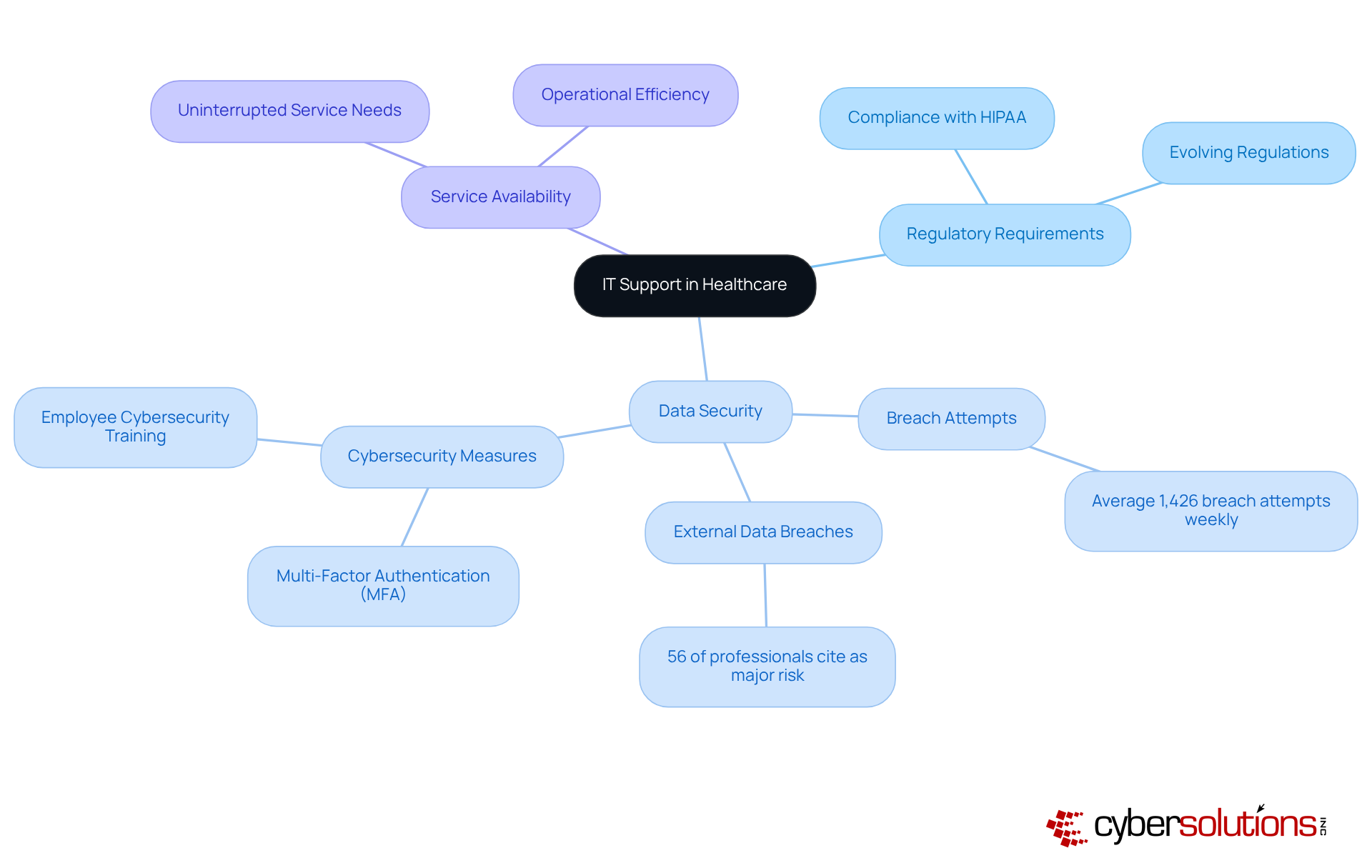
In the healthcare sector, an IT support service provider is not just a convenience; it is a vital element of operational success. Organizations are confronted with distinct challenges, such as:
The growing dependence on electronic health records (EHRs) and telemedicine amplifies the importance of a reliable IT infrastructure. Providers must ensure their IT systems are not only functional but also compliant with regulations like HIPAA, which governs data privacy. Effective assistance from an IT support service provider is essential for maintaining operational efficiency while safeguarding patient information.
Consider the alarming statistic that medical organizations encounter an average of 1,426 breach attempts weekly—this underscores the urgent need for robust cybersecurity measures. Furthermore, a significant 56% of medical professionals identify external data breaches as a major risk, highlighting the crucial role of an IT support service provider in mitigating these threats. By leveraging IT support services, healthcare organizations can bolster their security posture, ensuring compliance and ultimately enhancing care outcomes for patients. The time to act is now; the stakes are too high to overlook the necessity of dependable IT assistance in the face of increasing cyber threats.
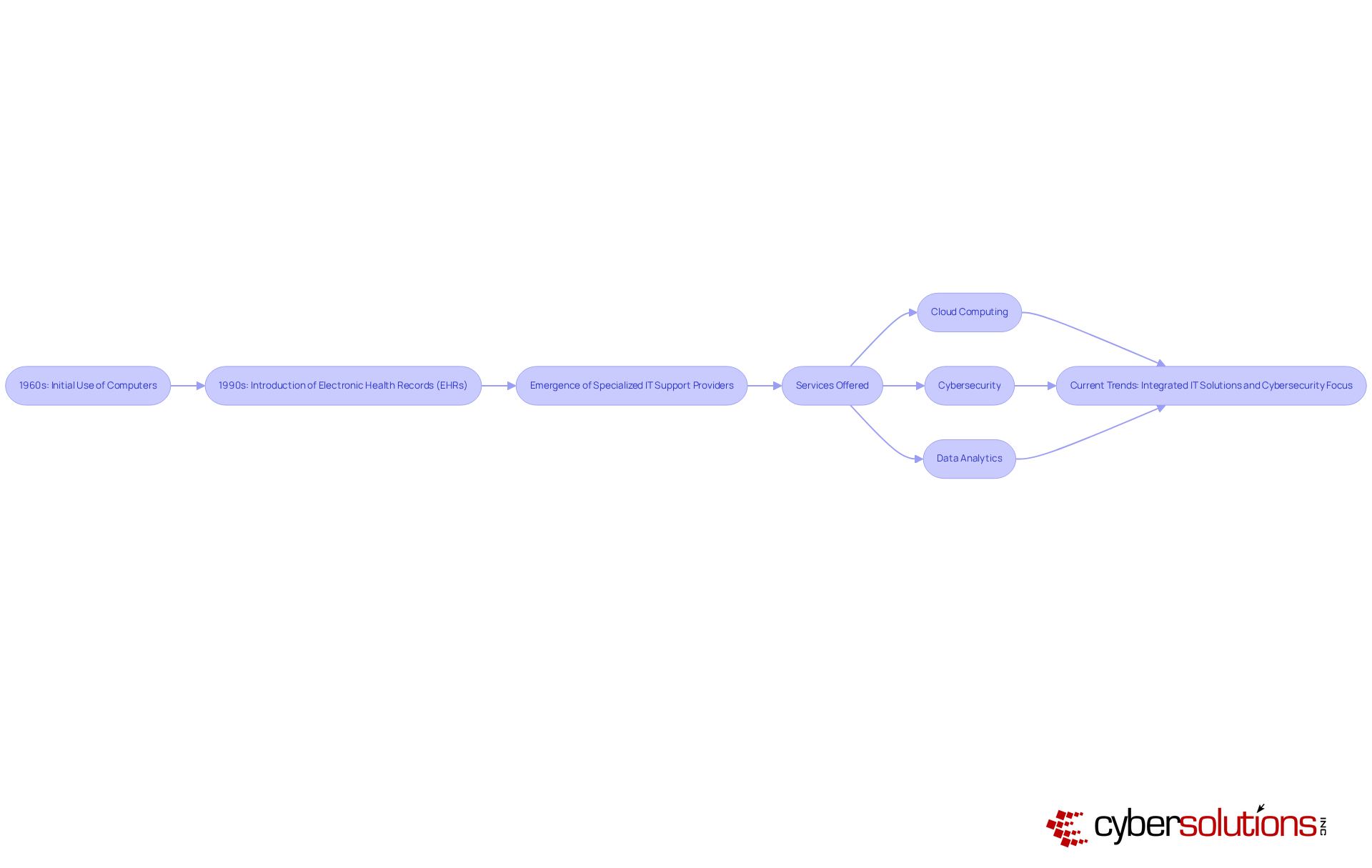
In today's healthcare landscape, the significance of IT support services is undeniable. The development of IT assistance services in medical care began with the initial use of computers in the 1960s, primarily aimed at optimizing administrative tasks. This foundational phase paved the way for a transformative shift in the 1990s with the introduction of electronic health records, revolutionizing data management and patient care. As technology has evolved, so too has the complexity of medical IT systems, leading to the emergence of specialized providers like managed service providers.
These providers offer a range of services, including:
These solutions reflect the ongoing digital transformation within the industry. This evolution highlights the essential role of IT support in enhancing both care quality and operational effectiveness, enabling medical organizations to adeptly navigate the complexities of modern technology. Recent trends reveal an increasing reliance on integrated IT solutions, with experts noting that the adoption of EHRs has fundamentally reshaped the role of healthcare providers, facilitating better patient outcomes.
Moreover, the critical need for cybersecurity has become glaringly evident. Incidents like ransomware attacks underscore the urgency for immediate action and response. The industry advocates for a layered approach to cybersecurity, ensuring that organizations not only recover from incidents but also bolster their security frameworks and enhance employee training to prevent future threats. With advanced security measures, proactive threat prevention strategies, and ongoing support, IT support services are committed to safeguarding medical operations and ensuring compliance.
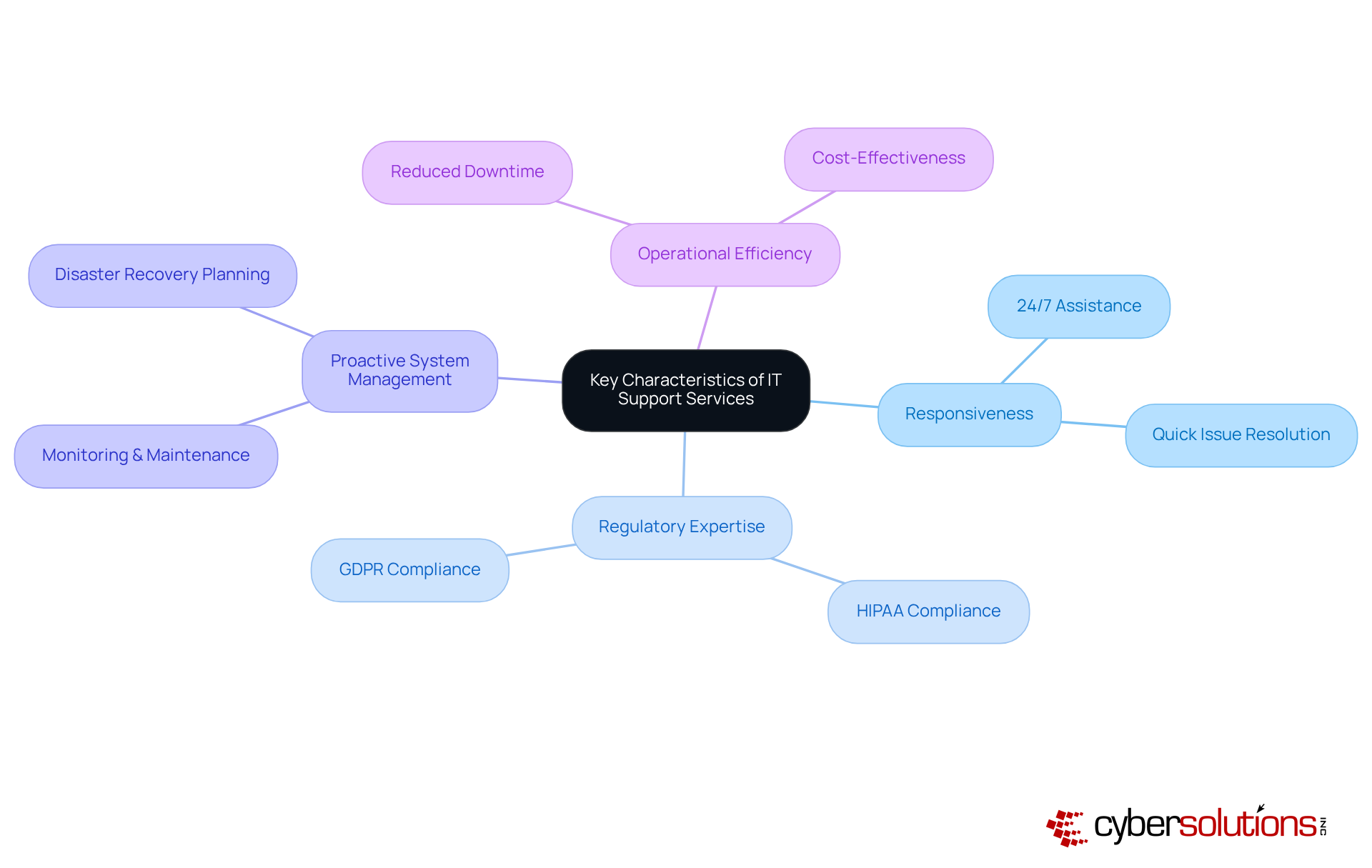
Effective IT support services in the medical field are paramount for ensuring responsiveness, efficiency, and proactive system management. The necessity of IT support cannot be overstated; it is crucial for addressing urgent matters swiftly, thereby minimizing disruptions to healthcare delivery. Statistics reveal that medical organizations utilizing IT support experience significantly reduced downtime, a vital factor in maintaining operations. Notably, organizations boasting robust IT assistance report a remarkable 30% decrease in system failures, which correlates directly with improved patient outcomes.
Furthermore, a deep understanding of medical regulations, such as HIPAA, is essential for ensuring compliance and safeguarding sensitive patient information. The management and maintenance of IT systems not only preempt potential issues but also bolster security. By prioritizing these critical characteristics, healthcare organizations can effectively select providers that align with their strategic goals and operational needs, ultimately enhancing patient care.
The significance of IT support service providers in the healthcare sector cannot be overstated; they are essential for ensuring operational efficiency and robust cybersecurity. As medical organizations grapple with increasing demands for compliance and data security, these specialized firms provide tailored solutions that effectively tackle the unique challenges of the healthcare environment. By harnessing the expertise of IT support service providers, healthcare institutions can adeptly navigate complex regulatory landscapes while safeguarding the integrity of sensitive patient information.
This article has delved into critical insights, including the evolution of IT support services, the urgent need for cybersecurity, and the defining characteristics of effective IT assistance in healthcare. The statistics presented—such as the alarming frequency of data breach attempts and the significant impact of continuous IT support on operational success—underscore the pressing necessity of investing in reliable IT solutions. As technology continues to evolve, the importance of integrating comprehensive IT support services becomes increasingly evident.
Given these considerations, healthcare organizations must prioritize their IT support strategies to elevate patient care and protect against cyber threats. The stakes are high; the necessity for dependable IT assistance is paramount in an industry where data breaches can jeopardize patient safety and trust. Embracing the capabilities of IT support service providers is not merely a convenience; it is a vital step toward achieving excellence in healthcare delivery.
What is an IT support service provider?
An IT support service provider is a specialized firm that offers a comprehensive range of technology solutions essential for managing IT infrastructure within medical organizations.
Why is cybersecurity important for healthcare organizations?
Cybersecurity is crucial for healthcare organizations due to the sensitive nature of patient information and the increasing threats posed by cyber attacks, leading to a need for robust IT assistance.
What services do IT support service providers offer?
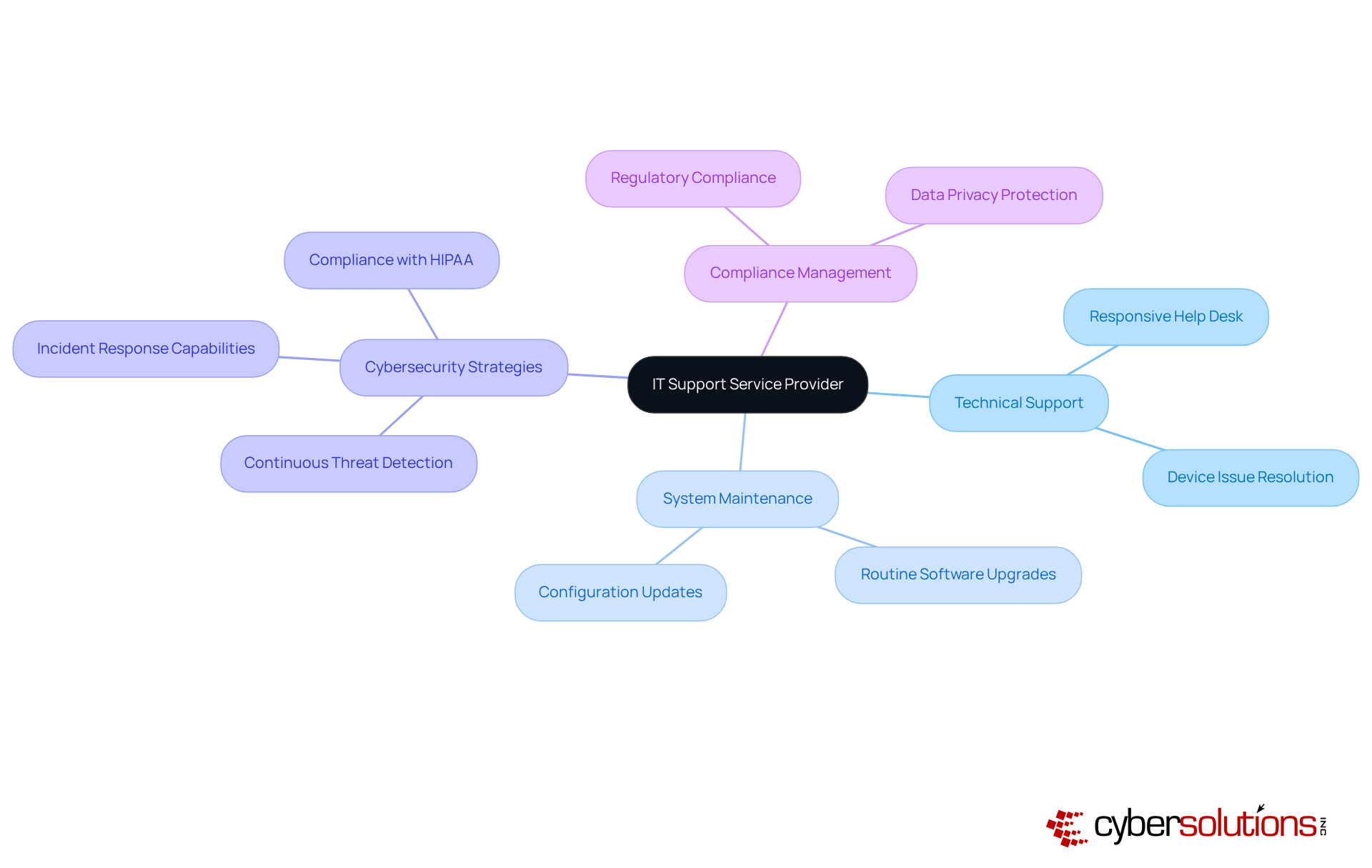
IT support service providers offer services including technical support, system maintenance, cybersecurity strategies, and compliance management specifically designed for medical requirements.
How are healthcare organizations planning to invest in cybersecurity?
Projections indicate that around 58% of medical organizations are expected to increase their cybersecurity budgets by 2025, reflecting the critical need for strong IT assistance.
What impact do IT support service providers have on healthcare operations?
IT support service providers enhance operational efficiency and patient care, allowing healthcare professionals to focus on delivering quality care while ensuring compliance with regulations and protection against cyber threats.
How do IT support service providers help with regulatory compliance?
They leverage specialized expertise and resources to enhance compliance with regulations such as HIPAA, ensuring that medical organizations operate securely and efficiently in a complex regulatory environment.