
In today's healthcare landscape, cybersecurity threats are a pressing concern that CFOs must confront head-on. Choosing an outsourced IT provider is not merely a strategic decision; it is essential for enhancing operational efficiency, reducing costs, and ensuring compliance with regulations such as HIPAA. By outsourcing, healthcare organizations can leverage specialized expertise that is crucial in mitigating cybersecurity risks. This allows CFOs to reallocate resources towards patient care, ultimately leading to improved service delivery and significant financial savings.
The implications of failing to address these cybersecurity challenges can be severe, risking both patient data and organizational integrity. As healthcare CFOs navigate these complexities, the importance of partnering with a knowledgeable IT provider becomes increasingly clear. By doing so, they can focus on what truly matters—delivering quality care to patients while safeguarding their information. The decision to outsource IT is not just about cost; it is about securing the future of healthcare services.
In the rapidly evolving landscape of healthcare, the integration of technology is not merely advantageous; it is essential. As healthcare organizations confront the complexities of IT management, the benefits of outsourcing these services become increasingly evident. By collaborating with specialized IT providers, CFOs can unlock significant operational efficiencies and cost savings, enabling a renewed focus on the primary mission of patient care.
Yet, amid escalating cybersecurity threats and the challenge of adhering to stringent regulations, a pivotal question arises: how can healthcare CFOs adeptly navigate the intricacies of IT outsourcing to ensure both security and quality in patient services?
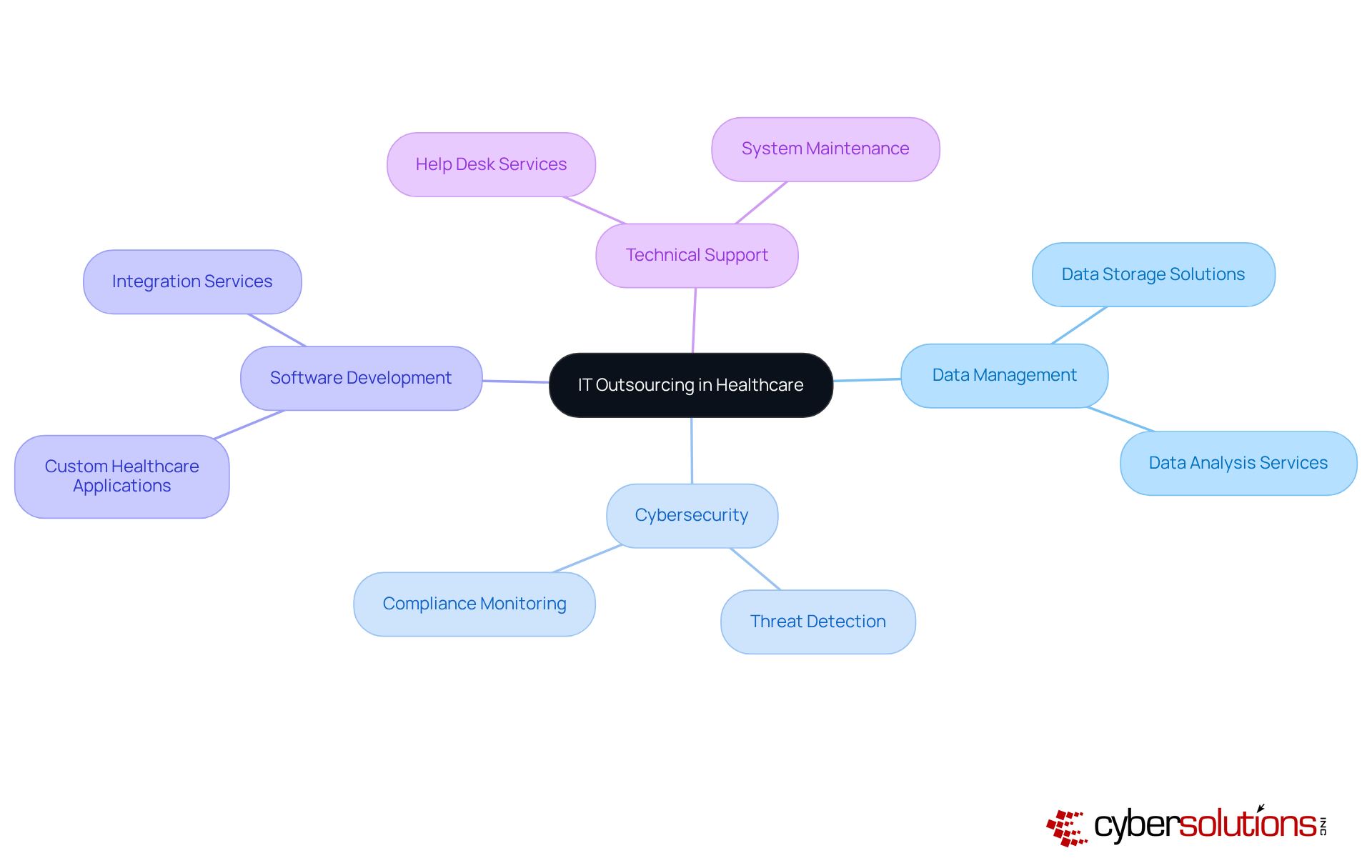
In the medical field, the use of an outsourced IT provider is a critical practice that involves assigning specific IT functions and responsibilities to external providers. This encompasses a variety of services, including:
Given the pressing need for compliance with regulations such as HIPAA, an outsourced IT provider becomes essential, allowing healthcare entities to leverage specialized expertise while focusing on core patient care tasks. By partnering with third-party vendors, medical service providers can ensure their IT infrastructure is managed by professionals adept in navigating the unique challenges and requirements of the healthcare sector. This strategic approach not only enhances operational efficiency but also , ultimately safeguarding patient information.
Outsourcing IT services in medical institutions through an outsourced IT provider is not merely a trend; it is a strategic move that can significantly enhance operational efficiency and patient care. The primary advantage lies in substantial cost savings, which arise from eliminating the need for extensive in-house IT teams and their associated infrastructure costs. By leveraging an outsourced IT provider, medical providers can access specialized skills without the financial burden of full-time hires. This strategic shift allows organizations to concentrate on their core mission—delivering quality patient care—while alleviating the complexities of IT management.
Moreover, delegating IT tasks empowers medical organizations to allocate additional resources to clinical functions, thereby improving service delivery. A case study of a medical facility that outsourced its IT services revealed a remarkable 30% reduction in operational costs, facilitating reinvestment in patient care initiatives. External partners often introduce advanced technologies and best practices that bolster security and compliance—an essential consideration in an era of escalating cyber threats. This proactive strategy not only protects sensitive patient data but also ensures compliance with regulatory standards, including HIPAA.
Statistics demonstrate that 62% of medical entities realize savings ranging from 10% to 25% through outsourcing IT functions. Additionally, an outsourced IT provider has been shown to improve patient care by streamlining processes and reducing wait times, as evidenced by facilities that have successfully integrated these solutions. By choosing to collaborate with a proficient IT service provider, CFOs in the medical sector can achieve both financial and operational advancements, positioning their organizations for sustained success in a competitive landscape.
A robust cybersecurity strategy, featuring 24-hour on-site incident response, can significantly mitigate operational disruptions during security incidents. This layered approach—comprising endpoint isolation, malware removal, and user training—facilitates a quicker and more comprehensive recovery. Furthermore, implementing application allowlisting within the cybersecurity framework guarantees that only authorized applications can execute, effectively preventing malware and unauthorized software, thus reinforcing compliance with regulations such as HIPAA and GDPR. Through the adoption of these proactive security measures, medical entities can bolster their cybersecurity posture and .

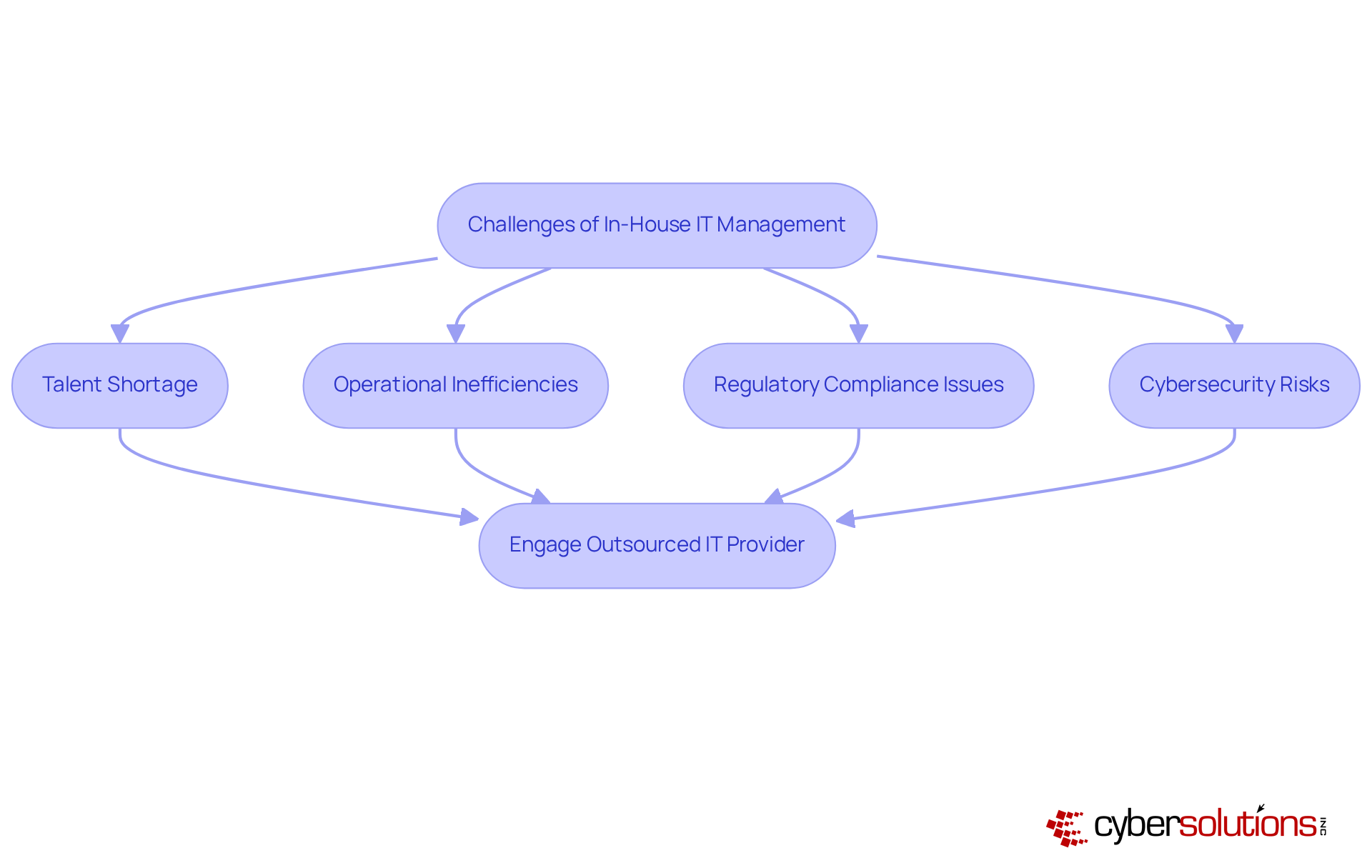
In today's healthcare landscape, the importance of cybersecurity cannot be overstated. Medical institutions face significant challenges when handling IT internally, primarily due to the difficulty in recruiting and retaining skilled IT professionals in a competitive job market, which has led to a reliance on an outsourced IT provider. This talent shortage can lead to operational inefficiencies and increased workloads for existing staff, ultimately detracting from their core mission of patient care.
Moreover, in-house teams often lack the specialized knowledge necessary to navigate the complex regulatory landscape of healthcare, raising the risk of compliance violations. The rapid pace of technological change further compounds these issues, as in-house teams must continuously invest in training and development, straining budgets and resources. These challenges not only expose healthcare entities to greater cybersecurity risks but also jeopardize their ability to deliver quality patient care.
Without robust measures such as , which proactively prevents unauthorized software from running, organizations become more vulnerable to malware and ransomware attacks. Application allowlisting not only restricts the applications that can execute but also incorporates features like continuous monitoring and centralized management, significantly enhancing overall security and ensuring compliance with regulations like HIPAA.
Given these complexities, engaging an outsourced IT provider emerges as a compelling option for healthcare organizations. By leveraging specialized knowledge and extensive managed IT solutions from an outsourced IT provider, entities can ensure adherence to strict regulations while enhancing their cybersecurity posture. This strategic approach enables healthcare providers to focus on what truly matters: delivering exceptional patient care.
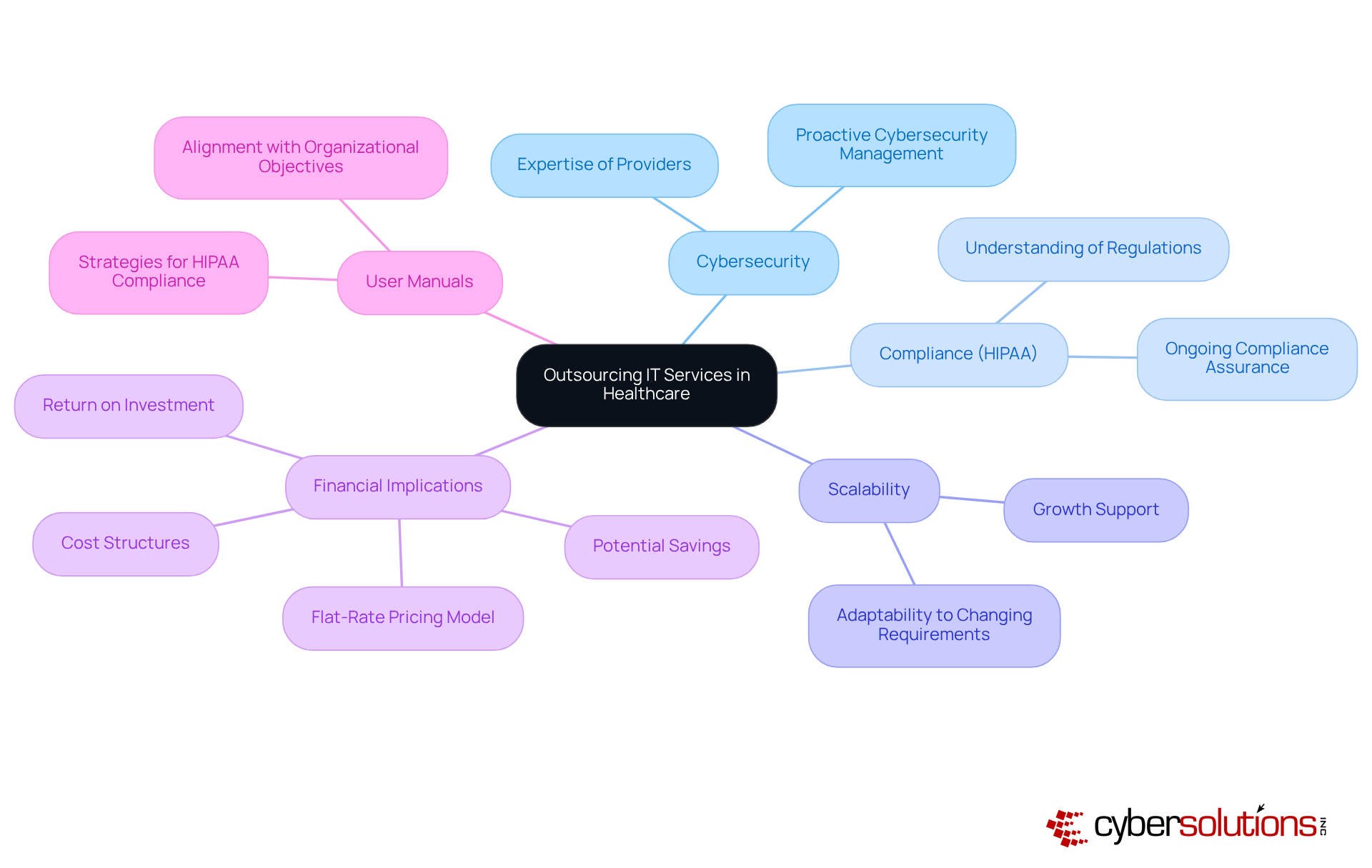
In today's healthcare landscape, the delegation of IT functions to an outsourced IT provider is a critical consideration for medical institutions. As cybersecurity threats continue to evolve, assessing the expertise and experience of potential outsourced IT providers becomes paramount. Particularly, a partner's understanding of compliance regulations, such as HIPAA, is essential. Engaging an outsourced IT provider that specializes in Virtual CISO solutions can ensure ongoing HIPAA compliance and proactive cybersecurity management, which are vital for protecting sensitive patient information.
Moreover, scalability of services is a crucial factor; organizations must ensure that their chosen outsourced IT provider can adapt to changing requirements as they grow. The financial implications of working with an outsourced IT provider should also be carefully evaluated. Companies need to analyze cost structures, potential savings, and the overall return on investment. A flat-rate pricing model can simplify budgeting, eliminating unexpected IT costs and surprises, thereby enabling CFOs to allocate resources more effectively.
Additionally, leveraging User Manuals can offer comprehensive strategies for achieving and maintaining HIPAA compliance. This approach ensures that the aligns with the organization's objectives and delivers the anticipated benefits. In conclusion, by thoughtfully evaluating these strategic elements, healthcare institutions can enhance their cybersecurity posture while effectively managing their IT functions.
Outsourcing IT services has become an essential strategy for healthcare organizations, enabling them to concentrate on core patient care while leveraging specialized expertise in complex IT management. By collaborating with external providers, healthcare CFOs can significantly enhance operational efficiency, reduce costs, and bolster cybersecurity measures, ensuring compliance with vital regulations such as HIPAA.
The discussion reveals substantial advantages of outsourcing, including considerable cost savings, access to cutting-edge technologies, and the capacity to allocate more resources toward patient care. The challenges linked to in-house IT management—such as talent shortages, compliance risks, and the continuous training burden—underscore the critical need for engaging outsourced IT providers. These partnerships not only streamline operations but also fortify security protocols, ultimately safeguarding sensitive patient information.
Given these insights, healthcare organizations are urged to critically assess their IT management strategies. By opting to outsource IT functions, they can more effectively navigate the complexities of cybersecurity and compliance, positioning themselves for long-term success in a competitive landscape. Embracing this strategic approach not only protects patient data but also empowers healthcare providers to deliver exceptional care, reinforcing the indispensable role of technology in modern healthcare delivery.
What is IT outsourcing in the healthcare context?
IT outsourcing in healthcare involves assigning specific IT functions and responsibilities to external providers, allowing healthcare entities to focus on core patient care while leveraging specialized expertise.
What types of services are included in IT outsourcing for healthcare?
IT outsourcing in healthcare includes services such as data management, cybersecurity, software development, and technical support.
Why is IT outsourcing important for healthcare providers?
IT outsourcing is important for healthcare providers because it helps ensure compliance with regulations like HIPAA, enhances operational efficiency, and improves security, ultimately safeguarding patient information.
How does partnering with third-party vendors benefit medical service providers?
Partnering with third-party vendors allows medical service providers to have their IT infrastructure managed by professionals who are skilled in addressing the unique challenges and requirements of the healthcare sector.