
In today’s rapidly changing landscape, cybersecurity threats are evolving at an alarming rate, making it imperative for organizations - especially in sensitive sectors like healthcare - to prioritize compliance with the Cybersecurity Maturity Model Certification (CMMC). This compliance is not just a regulatory checkbox; it’s a critical step in safeguarding operations and protecting sensitive patient data.
However, many organizations face unique challenges in navigating this complex regulatory environment. With only a fraction of companies currently meeting the necessary standards, the pressing question arises: how can organizations effectively leverage expert consultants to not only achieve compliance but also enhance their overall cybersecurity posture?
This article presents a curated list of ten expert CMMC consultants who offer invaluable guidance and tailored strategies. By partnering with these professionals, businesses can navigate the intricate landscape of regulatory requirements with confidence, ensuring they not only meet compliance standards but also bolster their defenses against potential cyber threats.
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially in the healthcare sector. Cyber Solutions Inc. stands out by offering tailored services that address the unique challenges faced by healthcare organizations. With threats evolving daily, CFOs must navigate a complex web of compliance requirements and security risks.
Cyber Solutions provides a comprehensive suite of services, including:
These offerings are meticulously designed to assist organizations in navigating the intricate terrain of cybersecurity with the guidance of industry experts. By leveraging advanced technology and expert insights, Cyber Solutions empowers businesses to focus on their core operations while ensuring they remain secure and compliant with ever-changing regulations.
This strategic approach not only enhances operational efficiency but also significantly reduces the risks associated with non-compliance. As organizations strive to foster a resilient business environment, partnering with Cyber Solutions can be a game-changer. Are you ready to secure your organization’s future?

Consultants play a pivotal role in helping organizations navigate the complexities of regulatory standards. They offer tailored strategies, guidance, and implementation support to ensure businesses meet the stringent requirements of the CMMC. By leveraging their expertise, organizations can streamline regulatory processes and bolster their cybersecurity posture.
Current trends indicate that many companies are increasingly relying on Managed Service Providers (MSPs) for support, identifying security gaps, and deploying essential cybersecurity tools, including software solutions. These services simplify the navigation of regulatory requirements by providing risk evaluations, policy development, and ongoing monitoring to ensure compliance with standards like CMMC. This shift highlights the necessity of selecting qualified partners, as only a limited number of authorized firms (C3PAOs) are available to assist with assessments.
Experts stress that early preparation and meticulous documentation are vital for achieving certification. As organizations face impending deadlines for compliance, particularly with the required C3PAO certification for Level 2 contracts starting November 10, 2026, the urgency to collaborate with experienced consultants has never been more critical. Currently, only about 200 companies have been evaluated for cybersecurity maturity model certification, while as many as 80,000 firms will need Level 2 certification, underscoring the scale of the challenge.
Key strategies provided by consultants include conducting readiness assessments to evaluate existing processes and ensure they align with NIST 800-171 requirements. This proactive approach not only prepares entities for regulation but also enhances their market position, offering a competitive advantage in today’s threat landscape. Furthermore, implementing application allowlisting can significantly enhance security by preventing unauthorized software from executing, thereby reducing vulnerabilities and ensuring compliance with stringent data protection protocols. Cyber Solutions also offers services to swiftly address and mitigate any security threats, ensuring business continuity.
As the landscape evolves, organizations must recognize that adherence is not a one-time event; it requires ongoing effort and continuous monitoring of security measures. As Kristen Latimer aptly states, "For businesses that prepare early, document thoroughly, and partner with the right IT experts, certification is absolutely achievable." By partnering with experienced consultants, organizations can effectively navigate these challenges, ensuring they remain compliant and secure in an increasingly regulated environment.

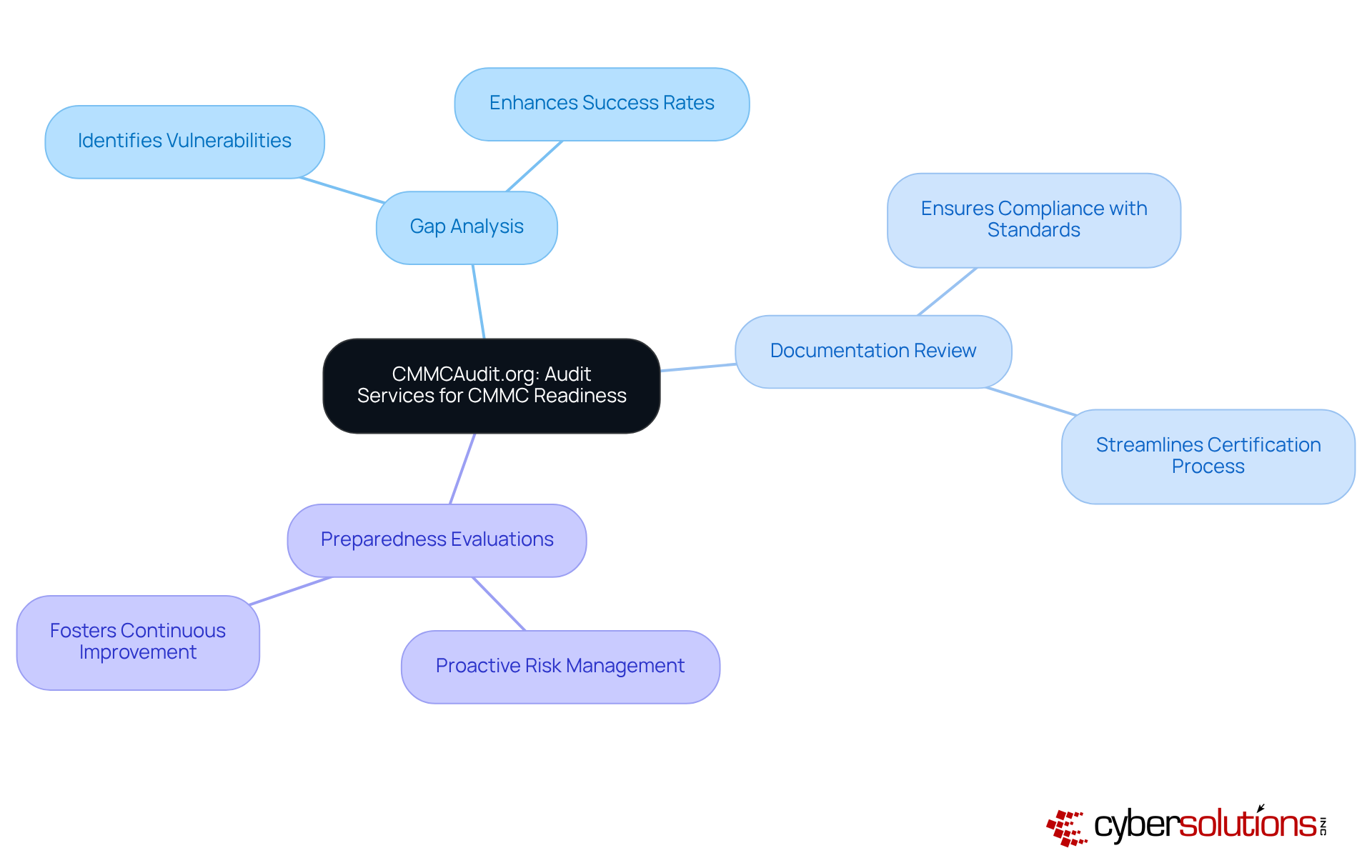
In today’s rapidly evolving cybersecurity landscape, compliance measures are not just a regulatory requirement; they are essential for safeguarding your organization’s integrity. CMMCAudit.org offers vital services tailored to prepare entities for these evaluations, ensuring they meet the necessary standards with confidence.
Their comprehensive offerings include:
These services are crucial for identifying vulnerabilities. By adopting this strategic approach, organizations significantly enhance their chances of achieving compliance. In fact, entities that engage in detailed assessments and documentation evaluations often report improved success rates, with a notable percentage passing evaluations after audits.
Compliance experts assert that these preparatory actions streamline the compliance process while fostering a culture of readiness. As the regulatory landscape continues to shift, leveraging these services becomes increasingly vital for organizations striving to meet specific standards efficiently. Are you ready to take the necessary steps to ensure your organization’s compliance?
In today’s rapidly evolving landscape, businesses face unprecedented threats that can jeopardize their operations and compliance. SecurityMetrics provides a comprehensive plan and tailored services to meet stringent standards. This structured approach empowers organizations to assess risks, prioritize remediation efforts, and chart a clear path to certification. By leveraging the services of SecurityMetrics, entities not only bolster their cybersecurity posture but also ensure compliance, crucial for maintaining eligibility for government contracts.
The emphasis on risk evaluation is paramount. It enables organizations to understand their current vulnerabilities and effectively address weaknesses, leading to a robust adherence strategy. Alarmingly, only 1% of Defense Industrial Base contractors are fully prepared for CMMC compliance, underscoring the urgency for assistance from experienced consultants. As Dr. Brian Luckey, Chief Information Officer, aptly notes, "MSPs can guide you through regulations, but a partner that has passed the Level 2 audit understands exactly what evidence auditors anticipate and how to establish a defensible, sustainable stance."
Moreover, integrating advanced cybersecurity tools from Cyber Solutions, such as threat detection systems and secure access controls, can significantly enhance regulatory compliance and safeguard sensitive federal data. Cyber Solutions also offers a management portal that simplifies monitoring and confirming compliance, ensuring entities remain audit-ready.
Achieving the required standards is not just beneficial; it’s essential. Failing to do so can result in severe consequences, including ineligibility for upcoming DoD contracts. Therefore, these services provided by SecurityMetrics are vital for any entity aiming to solidify its position in the defense industry.

In today's digital landscape, cybersecurity is not just a necessity; it's a critical component of organizational integrity. Redspin offers specialized training and preparation services tailored for organizations aiming to achieve compliance with CMMC. Their programs equip employees with the knowledge needed to navigate the complexities of the certification process, ensuring teams are thoroughly prepared for evaluations with guidance from experts.
Investing in such training does more than enhance readiness; it significantly reduces the risk of non-compliance. Statistics reveal that organizations prioritizing employee education see improved outcomes in their evaluations. Many report a direct correlation between training initiatives and successful assessments. Isn't it time to consider how proactive training can transform your approach to compliance?
This strategy is essential for managing the intricacies of CMMC requirements and securing long-term success. By choosing Redspin, organizations not only invest in their workforce but also fortify their defenses against the evolving threats that loom over the healthcare sector.

Encompass Consultants recognizes the critical need for businesses to achieve compliance in an increasingly complex regulatory environment. Their comprehensive checklist, paired with professional advisory services, simplifies the compliance process, ensuring that organizations can meet all requirements with confidence.
This checklist meticulously outlines every regulatory aspect, allowing entities to methodically address compliance challenges. By leveraging Encompass Consultants' expertise, businesses can navigate the intricacies of CMMC compliance effectively. This not only enhances their chances of success but also positions them as leaders in their respective industries.
In a landscape where compliance is paramount, Encompass Consultants stands out as a trusted partner. Their commitment to guiding organizations through the CMMC process empowers businesses to focus on their core operations while ensuring they meet all necessary standards.
In today's digital landscape, cybersecurity is not just a necessity; it's a critical imperative for organizations, especially in healthcare. The Cloud Security Alliance serves as an essential resource for entities striving to meet security standards. Their extensive library offers best practices, guidelines, and tools that organizations use to help businesses navigate the complex landscape. By leveraging these resources, organizations can deepen their understanding of cybersecurity and significantly bolster their defenses.
The CSA underscores the importance of translating research into actionable security enhancements, a vital step for effective compliance. Experts advocate for utilizing structured operational maturity programs offered by consultants, which provide customized assessments and hands-on workshops to address specific needs. These initiatives not only simplify the regulatory process but also foster a culture of continuous improvement in cybersecurity practices.
To further enhance their security efforts, organizations can tap into managed security service providers. With these services, organizations ensure a robust defense against cyber threats. Additionally, the CSA equips SMBs in regulated sectors with the expertise needed to navigate regulatory demands effectively. This includes audit preparation assistance and ongoing monitoring to ensure alignment with standards.
As companies adopt these best practices, they can expect a significant improvement in their compliance efforts, ultimately leading to a stronger defense against cyber threats. However, the certification introduced in 2019 faced delays due to industry concerns, highlighting the ongoing challenges organizations encounter in achieving compliance. Are you ready to take the next step in fortifying your cybersecurity strategy?
In today's rapidly evolving landscape, cybersecurity is not just a necessity; it's a critical component of operational integrity, especially in healthcare. CyberSheath stands out by offering solutions that ensure compliance and robust security, addressing the multifaceted challenges organizations face. Their comprehensive services range from initial gap evaluations to ongoing adherence monitoring, which is vital for maintaining a strong security posture.
As highlighted by industry experts, continuous adherence is essential. Organizations leveraging CyberSheath's expertise can significantly enhance their compliance efforts while ensuring alignment with regulatory standards. Alarmingly, as of early 2026, fewer than 800 entities have achieved Level 2 certification, despite an estimated 80,000 needing it. This stark statistic underscores the critical role of compliance consulting in navigating the complex regulatory environment.
Cybersecurity experts emphasize that not only mitigates risks but also strengthens overall security frameworks. This makes it a crucial investment for organizations committed to safeguarding sensitive information. Are you prepared to elevate your strategy and ensure compliance? With CyberSheath, you can confidently enhance your organization's security posture.

The CMMC-AB plays a pivotal role in the realm of cybersecurity, particularly for defense contractors. As the official entity overseeing compliance, it ensures that companies meet standards. This oversight is not just a formality; it’s a crucial support system that helps organizations navigate the intricate certification framework. Understanding this framework is vital for entities striving for certification and aiming to maintain a competitive edge in the defense contracting sector.
Currently, around 500 defense contractors have achieved Level 2 certification. However, the Pentagon anticipates that as the compliance requirements evolve, up to 80,000 companies will need certification. This statistic underscores the urgency for organizations to act. Accreditation through the CMMC-AB not only bolsters security posture but also positions companies favorably in a competitive market.
The CMMC-AB’s structured approach to certification, which includes a hierarchy of credentialed experts, highlights its commitment to fostering a robust regulatory ecosystem. To support adherence initiatives, Cyber Solutions offers consulting services, which includes:
Moreover, our consulting services are designed to swiftly identify and mitigate threats, ensuring business continuity and restoring operations efficiently and securely. In a landscape where threats are ever-evolving, proactive measures are not just beneficial - they are essential.

In today's landscape, compliance is not just a necessity; it's a critical component for organizations striving for success, often guided by expert consultants. PilieroMazza provides essential legal guidance, expertly navigating the intricate web of contracting obligations. Their deep understanding of the legal ramifications of CMMC regulations empowers businesses to grasp the necessary standards while safeguarding their interests.
By combining PilieroMazza's legal expertise with Cyber Solutions' compliance services, organizations can approach the CMMC process with newfound confidence and clarity. This partnership not only streamlines compliance but also significantly enhances regulatory outcomes. Cyber Solutions offers comprehensive support, policy development, and ongoing oversight, complementing PilieroMazza's legal support.
It's important to note that a substantial percentage of organizations face legal hurdles during their CMMC compliance journey, often requiring assistance from legal experts. This reality underscores the critical need for guidance in navigating these complexities. Are you prepared to tackle these challenges head-on? With the right support, your organization can not only achieve compliance but also thrive in a secure environment.
Navigating the complexities of CMMC compliance is not just essential; it’s a critical imperative for organizations determined to secure their operations and maintain eligibility for defense contracts. CMMC consultants play a vital role in this landscape, offering expert guidance, tailored strategies, and comprehensive support to help businesses meet stringent regulatory standards. By leveraging their expertise, organizations can significantly enhance their cybersecurity posture while simplifying the compliance process.
Key insights emphasize the importance of early preparation, thorough documentation, and continuous monitoring in achieving successful certification. With looming deadlines and an increasing number of companies requiring compliance, the urgency to engage qualified partners has never been more critical. From the tailored cybersecurity services offered by Cyber Solutions Inc. to comprehensive audit preparations by CMMCAudit.org, the resources available are designed to empower organizations on their compliance journey.
As the regulatory landscape evolves, it’s crucial for organizations to recognize that achieving and maintaining compliance is an ongoing commitment. Investing in the right consulting services and fostering a culture of continuous improvement not only helps businesses navigate compliance challenges but also strengthens their overall security framework. Taking proactive steps today prepares organizations for upcoming audits and positions them as leaders in their respective industries, ready to face the future with confidence.
What services does Cyber Solutions Inc. offer for cybersecurity and compliance?
Cyber Solutions Inc. offers a comprehensive suite of services including 24/7 help desk support, endpoint protection, and managed security solutions tailored for healthcare organizations.
How does Cyber Solutions Inc. assist organizations with CMMC standards?
Cyber Solutions provides guidance through CMMC consultants to help organizations navigate the complexities of CMMC standards, ensuring they remain secure and compliant with evolving regulatory requirements.
Why is cybersecurity particularly important in the healthcare sector?
The healthcare sector faces unique challenges and threats that are constantly evolving, making robust cybersecurity measures essential to protect sensitive information and maintain compliance with regulatory standards.
What role do CMMC consultants play in helping organizations achieve compliance?
CMMC consultants provide tailored strategies, risk assessments, and implementation support to help organizations meet the stringent requirements of the Cybersecurity Maturity Model Certification (CMMC).
What are some common services provided by Managed Service Providers (MSPs) for CMMC readiness?
MSPs typically offer CMMC readiness assessments, identify security gaps, and deploy essential cybersecurity tools, including Compliance as a Service (CaaS) solutions.
What is the significance of the C3PAO certification for Level 2 contracts?
The C3PAO certification is crucial for organizations seeking Level 2 contracts, with a deadline for compliance starting November 10, 2026. Only a limited number of authorized firms can assist with these assessments.
What strategies do CMMC consultants recommend for achieving certification?
Key strategies include conducting readiness assessments to evaluate existing security controls, ensuring alignment with NIST 800-171 requirements, and implementing application allowlisting to enhance security.
What services does CMMCAudit.org provide to prepare organizations for compliance evaluations?
CMMCAudit.org offers thorough gap analysis, documentation review, and preparedness evaluations to help organizations identify vulnerabilities and enhance their chances of successful certification.
How can organizations improve their chances of passing compliance evaluations?
Engaging in detailed gap analysis and documentation evaluations can significantly improve an organization's success rates in passing compliance evaluations.
Why is ongoing monitoring important for compliance?
Adherence to compliance standards is not a one-time event; it requires continuous effort and monitoring of security measures to adapt to the evolving regulatory landscape and maintain security.