
In today's healthcare landscape, where organizations are increasingly pressured by regulatory compliance and cybersecurity threats, the importance of managed services companies cannot be overstated. These firms provide critical support by enhancing operational efficiency and security, enabling CFOs to concentrate on strategic growth instead of getting mired in IT management. Yet, as the environment continues to evolve, how can healthcare leaders ensure they remain compliant and adequately prepared to confront the complexities of modern cyber threats?
By exploring the essential benefits of partnering with a managed services provider, we uncover a pathway not only to safeguard sensitive patient information but also to elevate the overall healthcare experience.
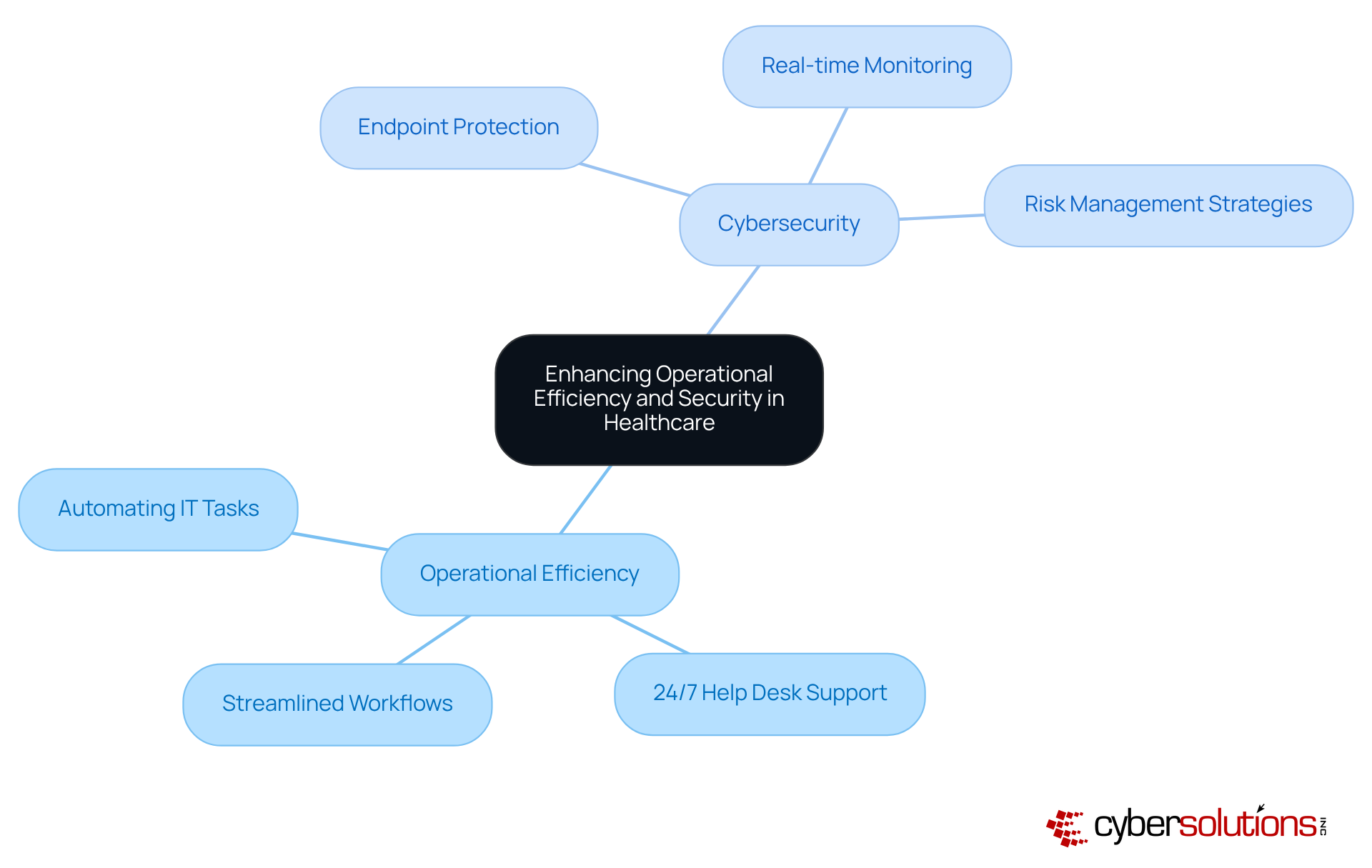
In the medical sector, efficiency is not just an objective; it is essential. The current landscape of healthcare presents unique challenges for healthcare organizations, making it crucial to focus on both efficiency and security. A managed services company, such as Cyber Solutions, plays a vital role in enhancing this efficiency by automating routine IT tasks. This enables healthcare organizations to concentrate on patient care rather than IT management. For instance, Cyber Solutions ensures that technical problems are swiftly addressed, significantly reducing downtime and service interruptions.
Moreover, the rising complexity of cyber threats necessitates advanced protective measures. Cyber Solutions offers cutting-edge cybersecurity solutions, which includes real-time monitoring and threat detection tools designed to safeguard sensitive client information from breaches. Our services and expert guidance ensure that medical entities remain audit-ready and compliant. This dual focus on efficiency and security not only streamlines operational workflows but also enhances the overall experience of patients, leading to improved health outcomes and increased trust in healthcare providers.
The implications of these advancements are profound: as healthcare organizations prioritize cybersecurity, they not only protect their operations but also foster a safer environment for patients. Are you ready to elevate your organization's efficiency while ensuring robust security? With Cyber Solutions, you can achieve both.
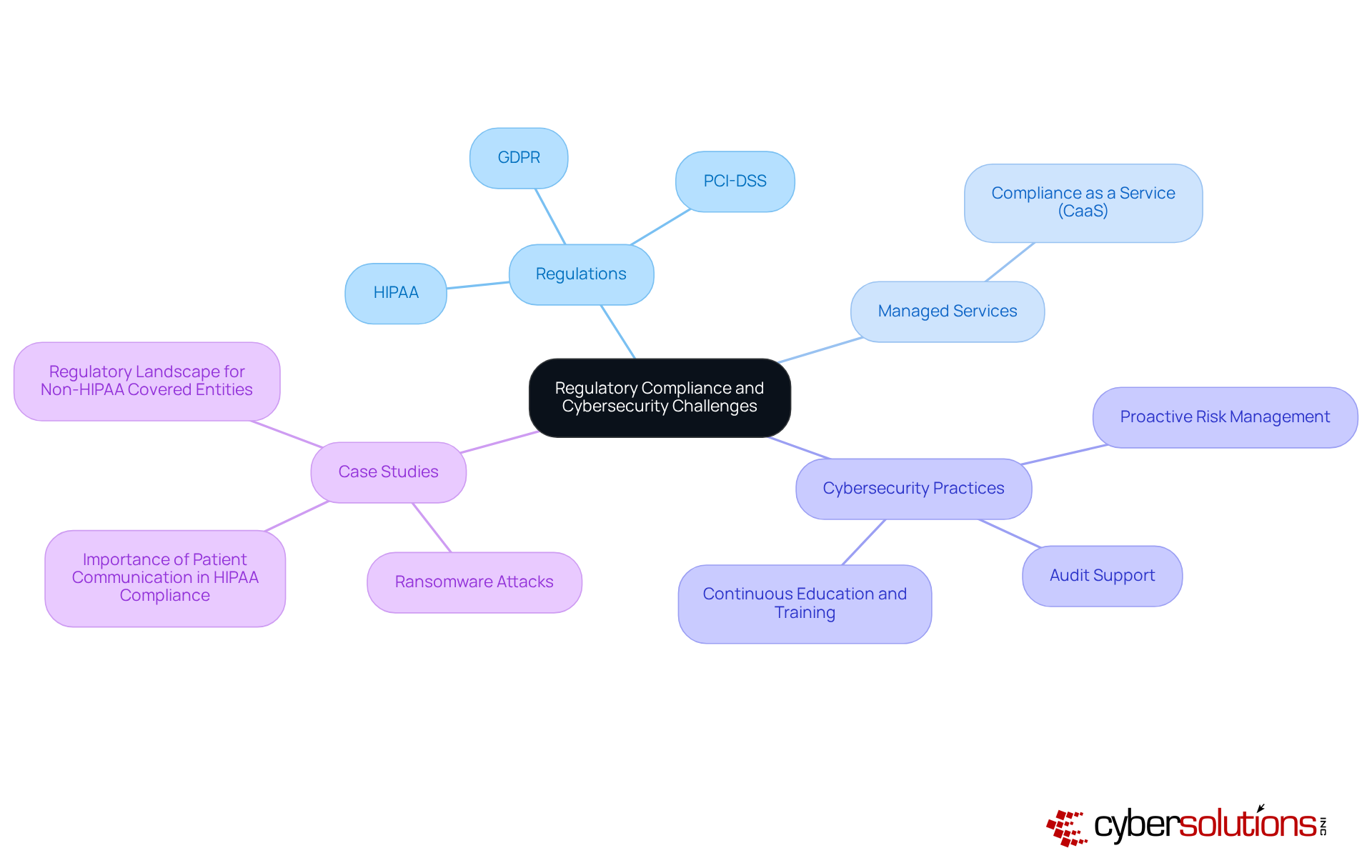
In today's digital age, the healthcare sector faces unprecedented challenges in cybersecurity, particularly in the realm of data protection. With stringent regulations such as HIPAA, HITECH, and GDPR governing the handling and protection of patient data, healthcare organizations must navigate a complex landscape. This is where a managed services company steps in, offering solutions that empower CFOs in the medical sector to adeptly manage these regulations. By leveraging their expertise in compliance frameworks, these providers not only help medical institutions meet regulatory standards but also instill best practices, including proactive risk management and audit support.
This proactive approach is critical in mitigating risks associated with data breaches and non-compliance, safeguarding organizations from potential fines and legal ramifications. Given the alarming rise in cyberattacks targeting the medical field, partnering with a managed services provider can significantly bolster a company’s security posture, ensuring readiness to respond to incidents swiftly and effectively. Moreover, ongoing education and training on compliance protocols are indispensable, as many breaches arise from human error or insufficient security measures.
Consider the recent data breach incident, which underscores the necessity for immediate response and continuous training. This example highlights that a managed services provider not only protects sensitive information but can also lead to substantial long-term savings and enhanced operational efficiency. By prioritizing compliance and security, medical institutions can not only improve their operational effectiveness but also ensure the protection of sensitive patient information.
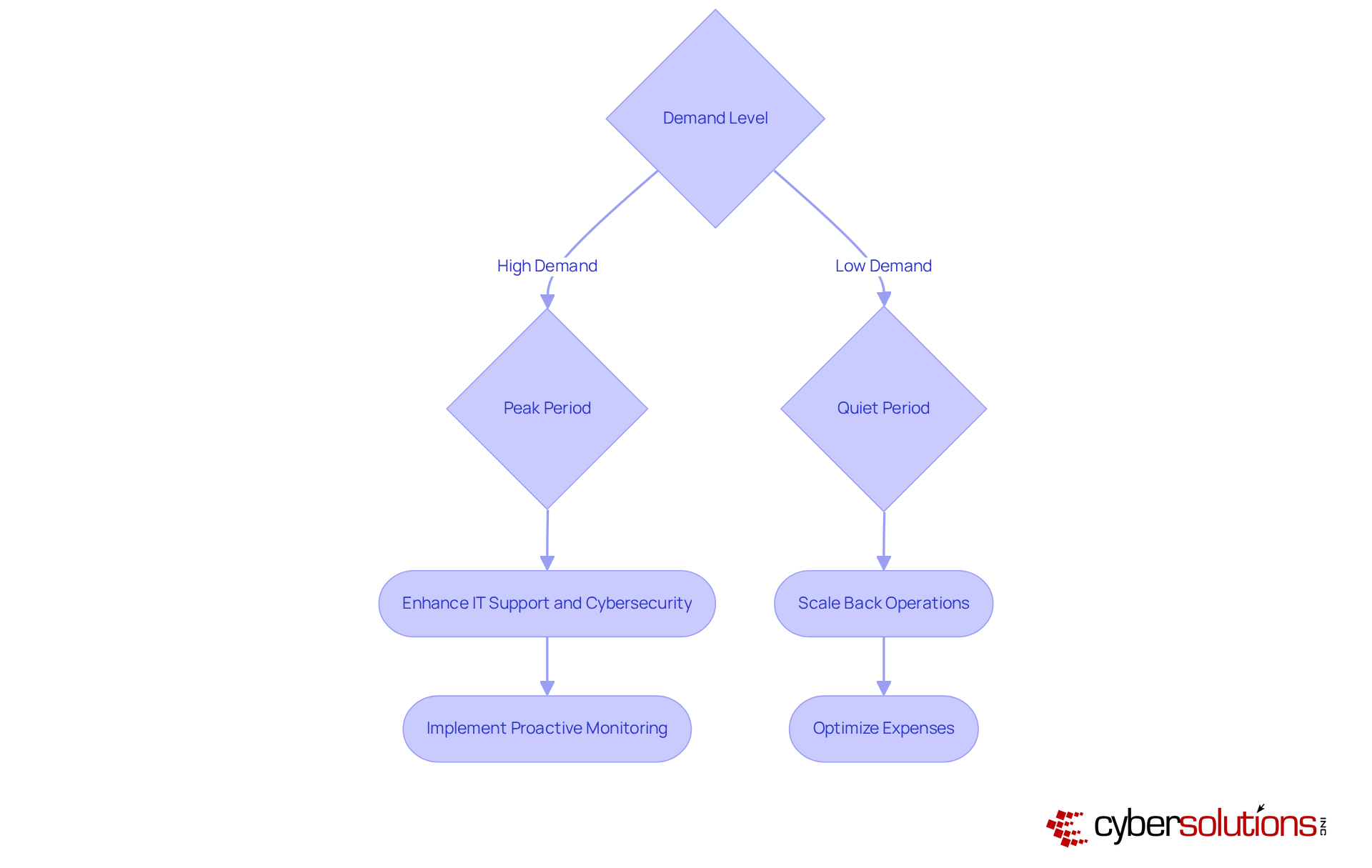
In today's dynamic medical environment, the cannot be overstated. Scalability and flexibility are essential for entities striving to grow and adapt amidst evolving threats. A provides solutions that empower CFOs in the medical field to adjust according to changing demands, ensuring that investments in infrastructure align with actual usage.
For instance, during peak periods like flu season, medical institutions can swiftly enhance their IT support and —implementing proactive monitoring and robust —to manage increased volumes and mitigate potential cyber threats. Conversely, in quieter times, they can scale back operations, optimizing expenses without sacrificing quality.
This adaptability not only boosts but also enables medical facilities to allocate resources more strategically, ultimately enhancing and satisfaction. By partnering with a like Cyber Solutions, can equip their organizations to navigate the complexities of modern healthcare delivery effectively, prioritizing growth and innovation.
As industry experts emphasize, and technology integration are critical for successfully managing these transitions.
A managed services company is not merely a support option; it is an essential partner for healthcare CFOs striving to enhance operational efficiency and security. In today's landscape, where cybersecurity threats loom large, automating routine IT tasks allows healthcare organizations to focus on what truly matters—providing quality care. The integration of advanced cybersecurity measures is crucial, ensuring that sensitive patient information is protected, fostering trust, and ultimately improving health outcomes.
Key insights underscore the dual importance of operational efficiency and regulatory compliance in healthcare. Managed services streamline IT processes while addressing the complex landscape of cybersecurity threats and compliance challenges. By leveraging expertise in risk management and offering scalable solutions, healthcare organizations can adapt to changing demands while safeguarding against potential breaches and regulatory fines.
The significance of embracing managed services in healthcare cannot be overstated. As the industry continues to evolve, organizations must prioritize robust cybersecurity measures and efficient operational practices. Investing in a managed services partnership is a proactive step toward achieving sustainable growth and ensuring the safety of patient information. This is an opportunity to enhance your healthcare operations and secure a brighter future for both providers and patients alike.
Why is operational efficiency important in healthcare?
Operational efficiency is essential in healthcare as it allows organizations to focus on patient care rather than IT management, especially in a landscape filled with cybersecurity threats.
How does Cyber Solutions enhance operational efficiency for healthcare organizations?
Cyber Solutions enhances operational efficiency by automating routine IT tasks and providing 24/7 help desk support, which helps to swiftly address technical problems and reduce downtime and service interruptions.
What cybersecurity measures does Cyber Solutions provide to healthcare organizations?
Cyber Solutions offers advanced endpoint protection, including real-time monitoring and threat detection tools to safeguard sensitive client information from breaches.
How does Cyber Solutions ensure compliance with regulations like HIPAA?
Cyber Solutions employs proactive risk management strategies and expert guidance to ensure that medical entities remain audit-ready and compliant with HIPAA standards.
What are the overall benefits of combining operational efficiency and security in healthcare?
Combining operational efficiency and security streamlines workflows, enhances the overall experience for patients, improves health outcomes, and increases trust in healthcare providers.
How can healthcare organizations elevate their operational efficiency and security?
Healthcare organizations can elevate their operational efficiency and security by partnering with managed services companies like Cyber Solutions to implement effective IT management and cybersecurity measures.