
In today's digital landscape, where cyber threats are more pervasive than ever, organizations must embrace a dual approach to cybersecurity that includes both penetration testing and vulnerability assessments. These essential methodologies play distinct yet complementary roles in protecting sensitive information and strengthening defenses against potential breaches. As C-Suite leaders navigate the complexities of cybersecurity, grasping the nuanced differences between these two strategies is crucial.
How can organizations effectively leverage both to not only identify vulnerabilities but also mitigate risks in an increasingly hostile environment? By understanding the unique challenges posed by cyber threats, organizations can implement robust cybersecurity measures that not only safeguard their assets but also foster trust among stakeholders.
In today's digital landscape, cybersecurity is not just a technical concern; it's a critical priority for organizations across all sectors, especially in healthcare. Penetration testing serves as a vital tool in this arena, simulating cyberattacks conducted by ethical hackers to identify weaknesses. The primary goal? To uncover vulnerabilities that malicious actors could exploit, providing a real-world perspective on potential flaws.
Unlike a standard vulnerability assessment, which systematically identifies, classifies, and prioritizes risks within an organization's IT infrastructure, the penetration testing process shows that vulnerabilities can be exploited. While risk evaluations focus on pinpointing possible weaknesses without exploiting them, penetration tests actively attempt to exploit these vulnerabilities. This approach not only reveals security gaps but also evaluates the effectiveness of existing security measures.
As healthcare organizations face increasing cyber threats, understanding these assessments is crucial. By integrating penetration testing into their strategies, organizations can better prepare for potential attacks, ensuring that their defenses are robust and effective. Cyber Solutions can help navigate these challenges, providing the expertise needed to safeguard sensitive information and maintain trust in healthcare systems.

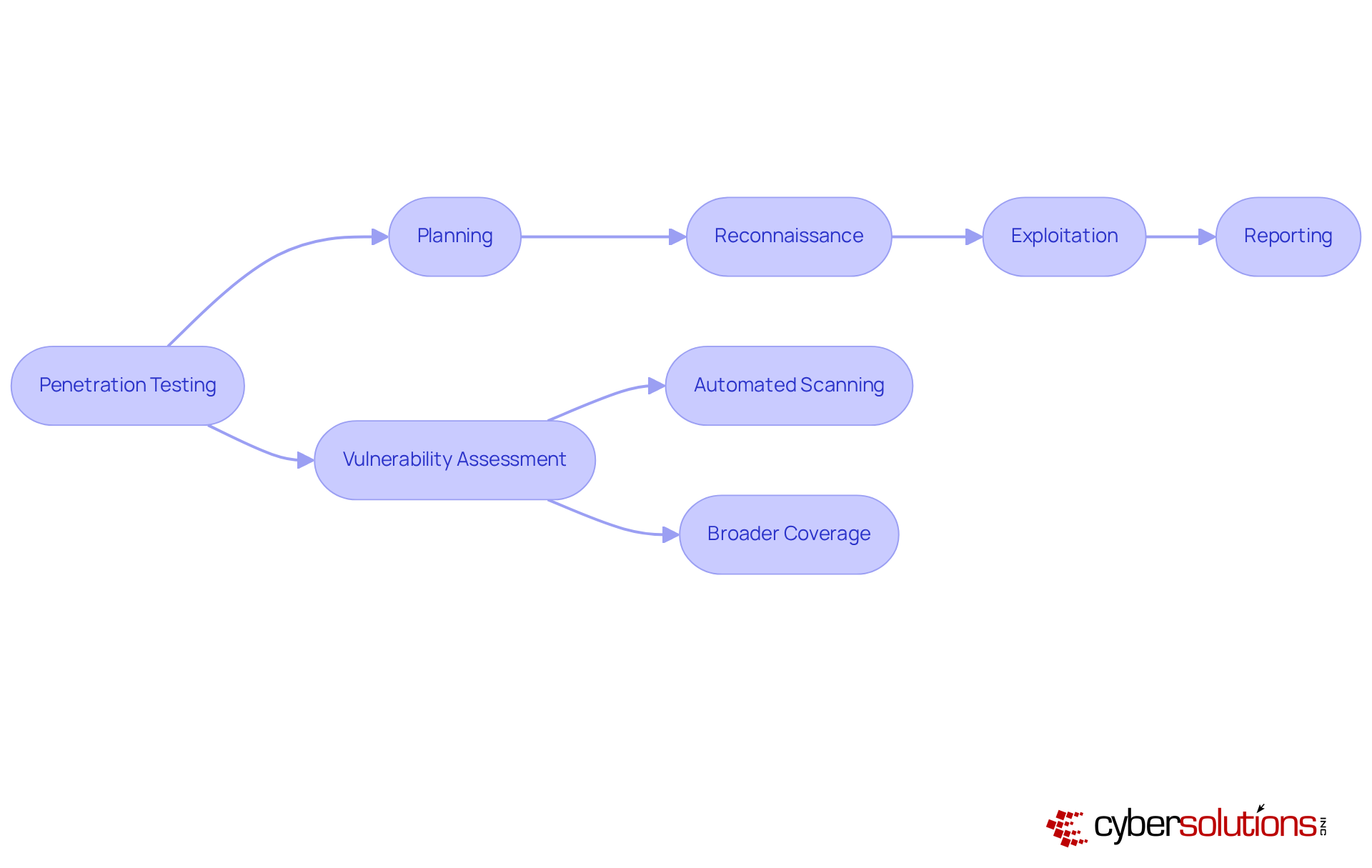
Understanding the nuances of penetration testing and vulnerability assessment is crucial for C-Suite leaders as they navigate today’s cybersecurity landscape. Penetration testing follows a meticulous process that includes:
This method is often labor-intensive, demanding skilled professionals who simulate real-world attack scenarios to identify vulnerabilities. Notably, the average time to resolve all findings from penetration tests is approximately 67 days, underscoring the necessity for swift remediation to uphold security.
On the other hand, vulnerability assessments leverage automated tools to scan systems for known weaknesses, offering a comprehensive view of potential risks across an organization’s infrastructure. While vulnerability assessments typically focus on specific systems or applications - ideal for targeted security reviews - penetration tests cover a broader spectrum of assets, making them suitable for ongoing monitoring. Organizations that engage in proactive evaluations can save an average of $1.9 million per breach, highlighting the financial benefits of security measures.
This dual approach empowers organizations to effectively manage their security posture by combining the in-depth insights from penetration testing with the extensive coverage provided by vulnerability assessments in the context of risk management. Furthermore, assessments such as vulnerability scans require that they be conducted at least annually and after significant changes, reinforcing their essential role in compliance and risk management.
stands as a critical component, essential for pinpointing exploitable weaknesses and evaluating the real-world ramifications of potential attacks. By simulating actual attack scenarios, organizations can gain a comprehensive understanding and the effectiveness of their security measures. In contrast, vulnerability assessments excel at uncovering a broad spectrum of potential vulnerabilities across systems, providing a detailed overview of security flaws. However, they often fall short in offering insights into the exploitability of these vulnerabilities. Thus, while penetration testing delivers depth in risk identification, understanding the methodologies reveals that provide breadth, making them indispensable partners in a robust cybersecurity strategy.
Organizations that successfully integrate both methodologies can significantly bolster their security posture, ensuring a proactive approach against the ever-evolving landscape of cyber threats. For instance, Cyber Solutions adopted a layered strategy that encompassed:
This not only enhanced recovery times but also fortified client relationships. Looking ahead to 2026, the emphasis on continuous improvement is expected to grow, as assessments play a vital role in identifying and prioritizing threats, ultimately contributing to the establishment of a more resilient security framework.

In today’s digital landscape, the importance of robust cybersecurity cannot be overstated, especially for organizations navigating the complexities of pen test vs vulnerability assessment. These assessments are typically conducted annually or biannually due to their resource intensity, requiring skilled professionals and a comprehensive understanding of security protocols. The costs for penetration testing can vary widely, ranging from $4,000 to $30,000, depending on the scope and complexity of the systems involved.
Conversely, vulnerability assessments can be performed more frequently - often on a monthly or quarterly basis - thanks to automated tools that streamline the process. Organizations that engage in quarterly vulnerability evaluations see a remarkable 53% reduction in security incidents, underscoring the effectiveness of regular assessments. Moreover, a striking 75% of cybersecurity professionals conduct penetration tests to comply with industry standards, emphasizing the critical role of adherence to regulations in decision-making.
Given that 67% of U.S. enterprises have experienced a breach in the past 24 months, it’s essential for organizations to weigh these factors against their specific needs and budget constraints. How can your organization ensure it’s taking the right steps to protect its assets? By carefully considering these evaluations, you can determine the most suitable approach to bolster your cybersecurity posture.

Understanding the distinctions between penetration testing and vulnerability assessments is vital for organizations looking to strengthen their cybersecurity strategies. Both methodologies aim to identify and mitigate risks, but they do so in distinct ways. Penetration testing simulates real-world attacks to uncover exploitable vulnerabilities, while vulnerability assessments provide a broader overview of potential risks without active exploitation. This nuanced understanding empowers C-suite leaders to make informed decisions about their cybersecurity investments.
Key insights from the article underscore the necessity of integrating both penetration testing and vulnerability assessments into a comprehensive security framework. Penetration tests deliver in-depth analysis and insights into the effectiveness of existing security measures, whereas vulnerability assessments facilitate ongoing monitoring and risk identification. The financial implications further highlight the value of these assessments; proactive evaluations can lead to significant cost savings in the event of a breach.
As cyber threats continue to evolve, organizations must prioritize a dual approach to cybersecurity. By embracing both penetration testing and vulnerability assessments, leaders can enhance their risk management strategies, ensure compliance with regulatory standards, and foster a culture of security awareness. Taking these steps not only protects sensitive information but also strengthens trust within the organization and among its stakeholders, paving the way for a more resilient future in cybersecurity.
What is penetration testing?
Penetration testing, or pen testing, is a cybersecurity practice that simulates cyberattacks conducted by ethical hackers to evaluate the defenses of systems, networks, or applications. Its primary goal is to uncover vulnerabilities that malicious actors could exploit.
How does penetration testing differ from a vulnerability assessment?
While a vulnerability assessment systematically identifies, classifies, and prioritizes risks within an organization's IT infrastructure, penetration testing goes further by actively attempting to exploit identified vulnerabilities. This approach assesses the consequences of breaches and evaluates the effectiveness of existing security measures.
Why is penetration testing important for healthcare organizations?
Penetration testing is crucial for healthcare organizations as they face increasing cyber threats. By integrating penetration testing into their cybersecurity strategies, organizations can better prepare for potential attacks, ensuring their defenses are robust and effective.
What are the benefits of conducting a penetration test?
The benefits of conducting a penetration test include identifying potential vulnerabilities in systems, evaluating the effectiveness of security measures, and providing a real-world perspective on potential flaws that could be exploited by malicious actors.
How can Cyber Solutions assist organizations with penetration testing?
Cyber Solutions can provide the expertise needed to navigate cybersecurity challenges, helping organizations safeguard sensitive information and maintain trust in healthcare systems through effective penetration testing strategies.