
In today's healthcare landscape, where organizations grapple with rising cyber threats and stringent regulatory demands, the significance of managed IT services has reached unprecedented heights. This article explores ten essential IT solutions that enable CFOs in the healthcare sector to enhance operational efficiency while protecting sensitive data. By examining customized strategies designed to address the unique challenges of healthcare finance, CFOs can learn to navigate complexities and achieve improved financial outcomes. However, with an abundance of options available, how can they discern which services will genuinely elevate their organization’s performance and security?
In today's rapidly evolving digital landscape, the importance of managed IT services cannot be overstated. Cyber Solutions provides a comprehensive suite of services specifically tailored for medical organizations, significantly enhancing operational efficiency and cybersecurity. By prioritizing solutions that address the distinct security and compliance needs, the company empowers CFOs to allocate resources more effectively, alleviating the complexities associated with IT management. This strategic support enables healthcare providers to focus on delivering quality treatment, free from the distractions of IT challenges.
As the medical IT market is projected to expand at a compound annual growth rate of 19.8% from 2022 to 2027, the need for managed IT services has become increasingly vital. Industry leaders emphasize that managed IT services not only streamlines operations but also enhances overall organizational performance, allowing CFOs to drive better financial outcomes. How can organizations ensure they are not left behind in this competitive landscape? Successful executions of IT strategies have demonstrated that companies can reduce downtime and enhance compliance, ultimately leading to greater staff satisfaction and improved patient care.
For instance, a recent case study highlighted that a medical institution decreased manual workloads by five times in pharmacy claim processing through efficient IT assistance. Furthermore, Cyber Solutions' offerings—including 24-hour on-site support and layered recovery approaches—ensure minimal operational disruption and bolster cybersecurity confidence. By collaborating with Cyber Solutions, healthcare organizations can guarantee their entities remain flexible and adaptive in a swiftly changing digital environment.
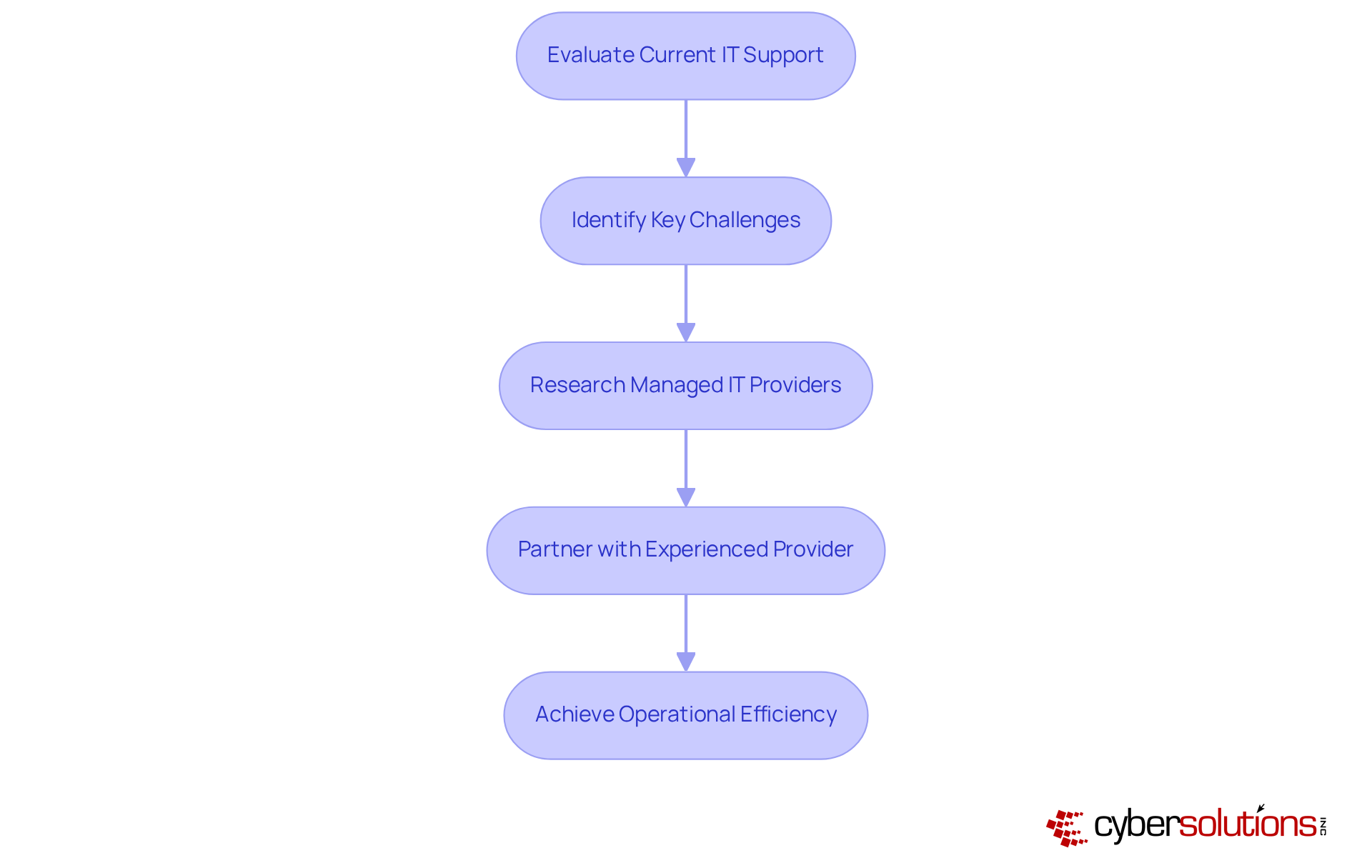
To prepare for growth, CFOs should critically evaluate their current IT support structures and consider partnerships with experienced providers of managed IT services. This proactive approach not only addresses immediate IT challenges but also positions organizations for sustainable growth in an increasingly complex healthcare landscape.
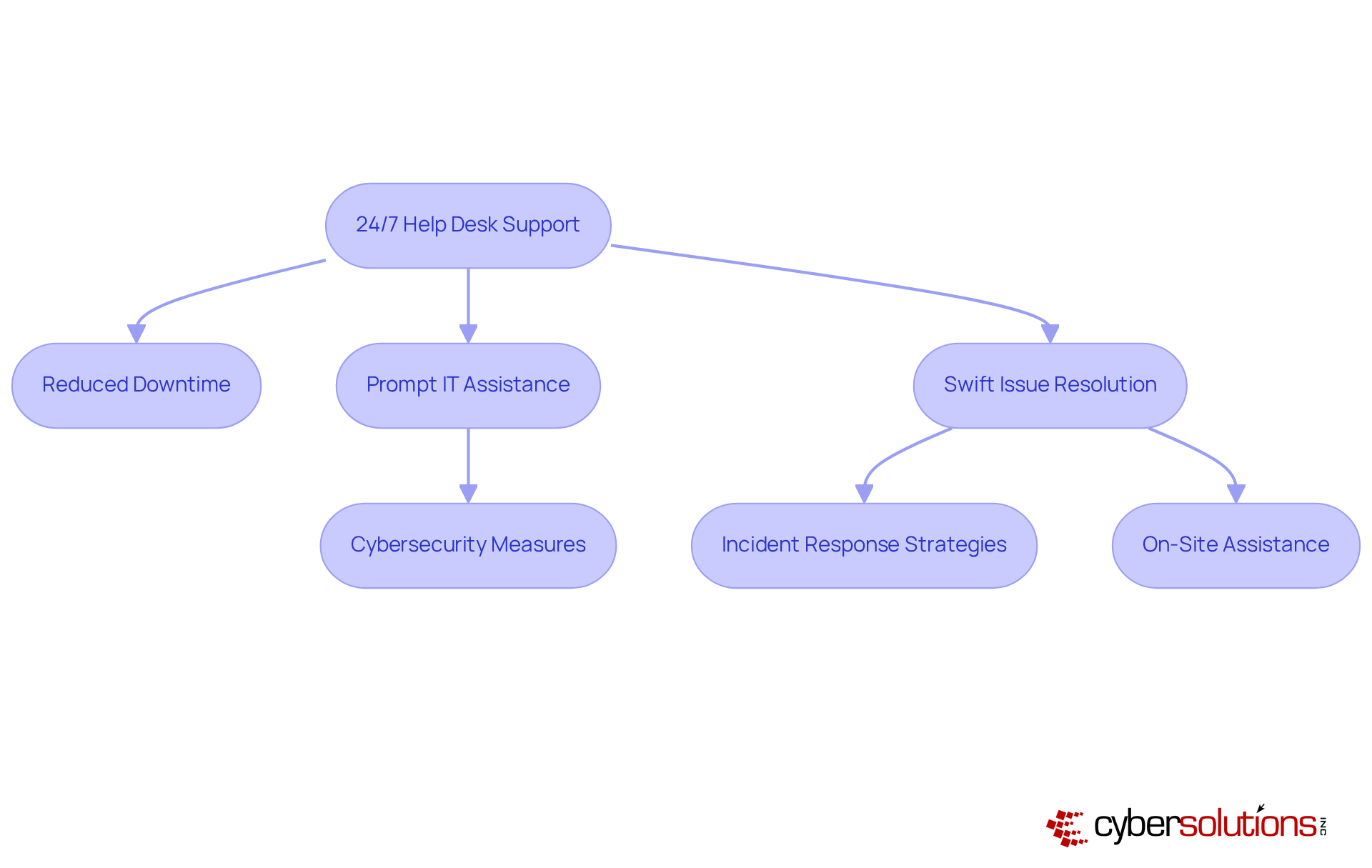
In today's digital landscape, cybersecurity is not just an option; it's a necessity for healthcare organizations. Cyber Solutions offers comprehensive support by providing round-the-clock help desk support, ensuring medical entities have prompt access to IT assistance. This continuous availability significantly reduces downtime, which can disrupt patient care. Furthermore, the average time to restore medical IT systems after an incident exceeds 17 days, highlighting the critical need for rapid response. By swiftly resolving technical issues, medical personnel can focus on their primary responsibilities, ultimately enhancing efficiency and care for patients.
The presence of a dedicated support team available 24/7, which includes trained IT professionals, empowers organizations to promptly tackle IT challenges, and reinforcing trust in medical services. Additionally, support services covering cybersecurity and data management are specifically designed for the medical sector, ensuring compliance with industry regulations and protecting sensitive patient data. IT experts emphasize that minimizing downtime through effective support not only boosts operational efficiency but also positively impacts patient outcomes, making it an essential component of modern medical IT infrastructure.
Moreover, our service offerings, which include on-site assistance within 24 hours and a structured response plan, equip medical facilities to effectively manage and recover from cyber threats. This proactive approach not only enhances security but also instills confidence in their ability to protect patient information and maintain high standards of care.
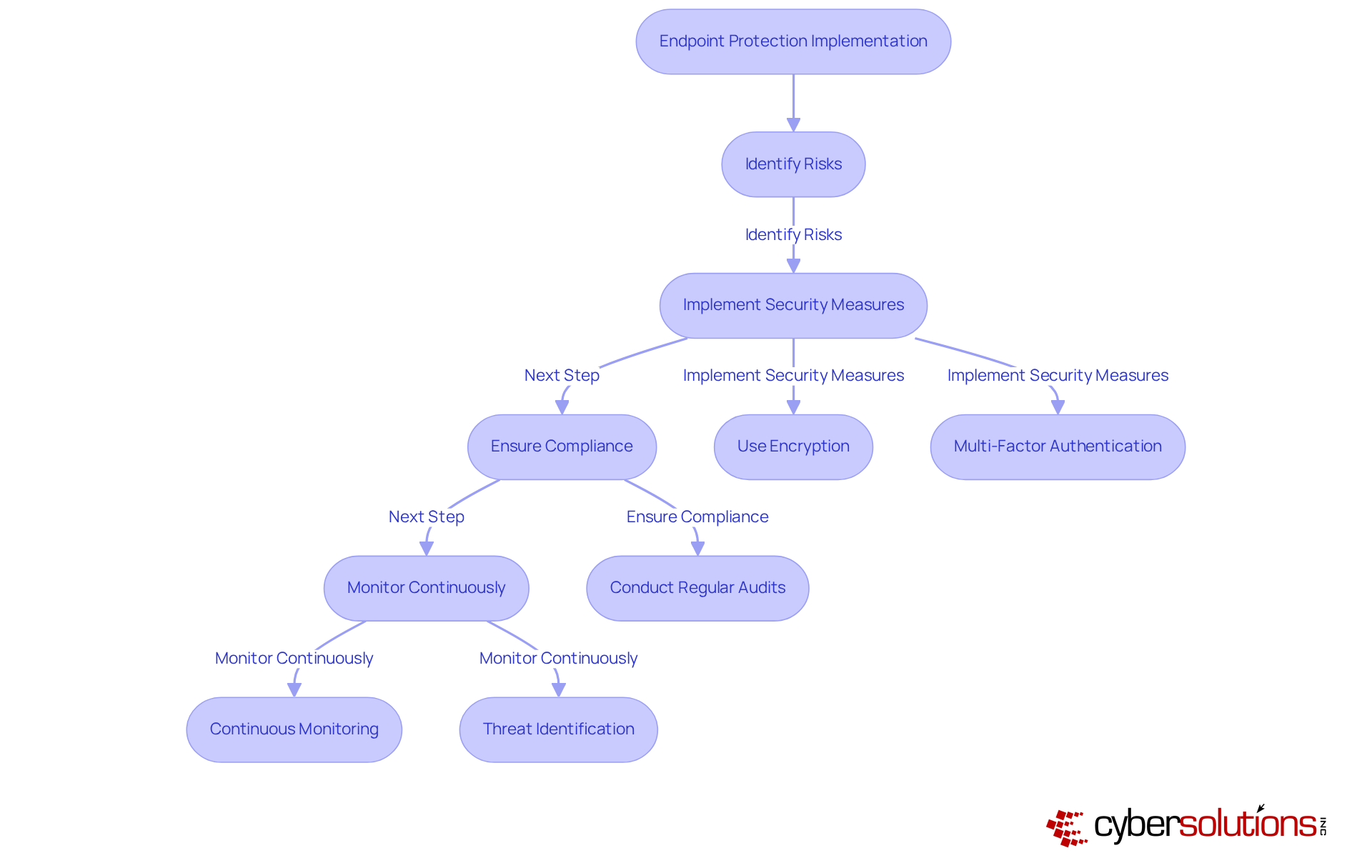
Endpoint Protection is a critical pillar of Cyber Solutions' strategy, particularly for medical facilities grappling with escalating cyber threats. With over 31% of organizations reporting data breaches this year, the healthcare sector faces heightened vulnerability due to the sensitive nature of individual health information and the surge of connected medical devices. Advanced security measures, such as sophisticated encryption and multi-factor authentication, are essential for defending these devices against malware, ransomware, and other cyber attacks.
Implementing robust security protocols not only secures sensitive patient data but also ensures compliance with regulatory frameworks like HIPAA, effectively mitigating the risk of costly data breaches. There is a necessity of a proactive approach; as Ajay Unni from StickmanCyber articulates, healthcare entities must prepare for cyberattacks, recognizing that it is not a question of 'if' but 'when'.
Moreover, effective strategies significantly enhance the safety posture of medical devices, which are frequent targets for attackers. By employing methods such as continuous monitoring and threat identification, Cyber Solutions aids medical facilities in maintaining the integrity of their systems and protecting them from unauthorized access. Our swift incident response capabilities, demonstrated in recent case studies, ensure that organizations can recover promptly from attacks, restoring operations and strengthening protective measures to prevent future incidents. This comprehensive approach not only reduces risks but also fosters confidence among patients and stakeholders, underscoring the critical importance of cybersecurity in the medical field. Healthcare CFOs are urged to evaluate their current strategies and consider partnering with Cyber Solutions' tailored offerings for enhanced security posture.
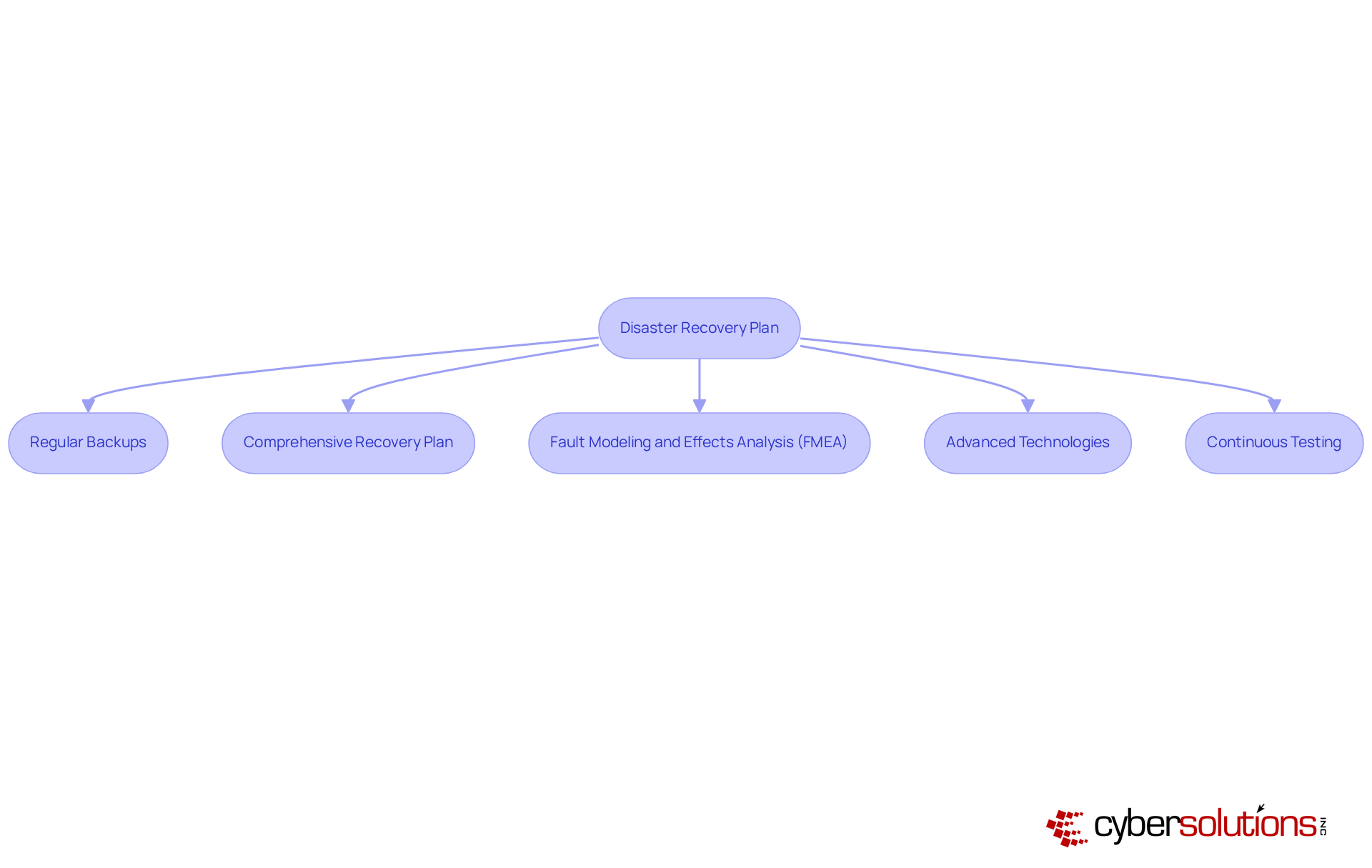
In today's digital landscape, the importance of robust cybersecurity in healthcare cannot be overstated. Cyber Solutions provides strong services tailored to the unique needs of healthcare entities, ensuring the safeguarding of essential data against potential loss. With 395 documented breaches affecting over 59 million individuals in 2023 alone, the urgency for effective disaster recovery is evident. By implementing a systematic approach that incorporates regular backups and a comprehensive recovery plan, organizations can swiftly restore critical information in the event of a disaster.
This proactive strategy not only protects patient care but also aligns with regulatory compliance, mitigating the financial repercussions associated with data breaches. Industry leaders emphasize that a well-structured disaster recovery plan is vital for maintaining and securing sensitive information. For instance, integrating Fault Modeling and Effects Analysis (FMEA) into recovery planning enables entities to identify potential vulnerabilities and refine their response strategies. Furthermore, the typical recovery duration for data loss events in the medical sector can significantly impact patient care, underscoring the necessity for organizations to prioritize their recovery strategies.
By leveraging advanced technologies and continuous testing, including the flexibility, scalability, and cost-effectiveness of cloud solutions, Cyber Solutions guarantees that medical organizations can sustain uninterrupted services and maintain patient trust. Our services address the distinct protection and recovery needs of the medical sector, offering tools such as endpoint safeguarding, data encryption, backup solutions, and secure access controls designed to defend against evolving cyber threats. This comprehensive approach not only enhances recovery efforts but also fosters strong collaboration with healthcare providers, ensuring continuity of care and adherence to regulations in the face of potential ransomware attacks.
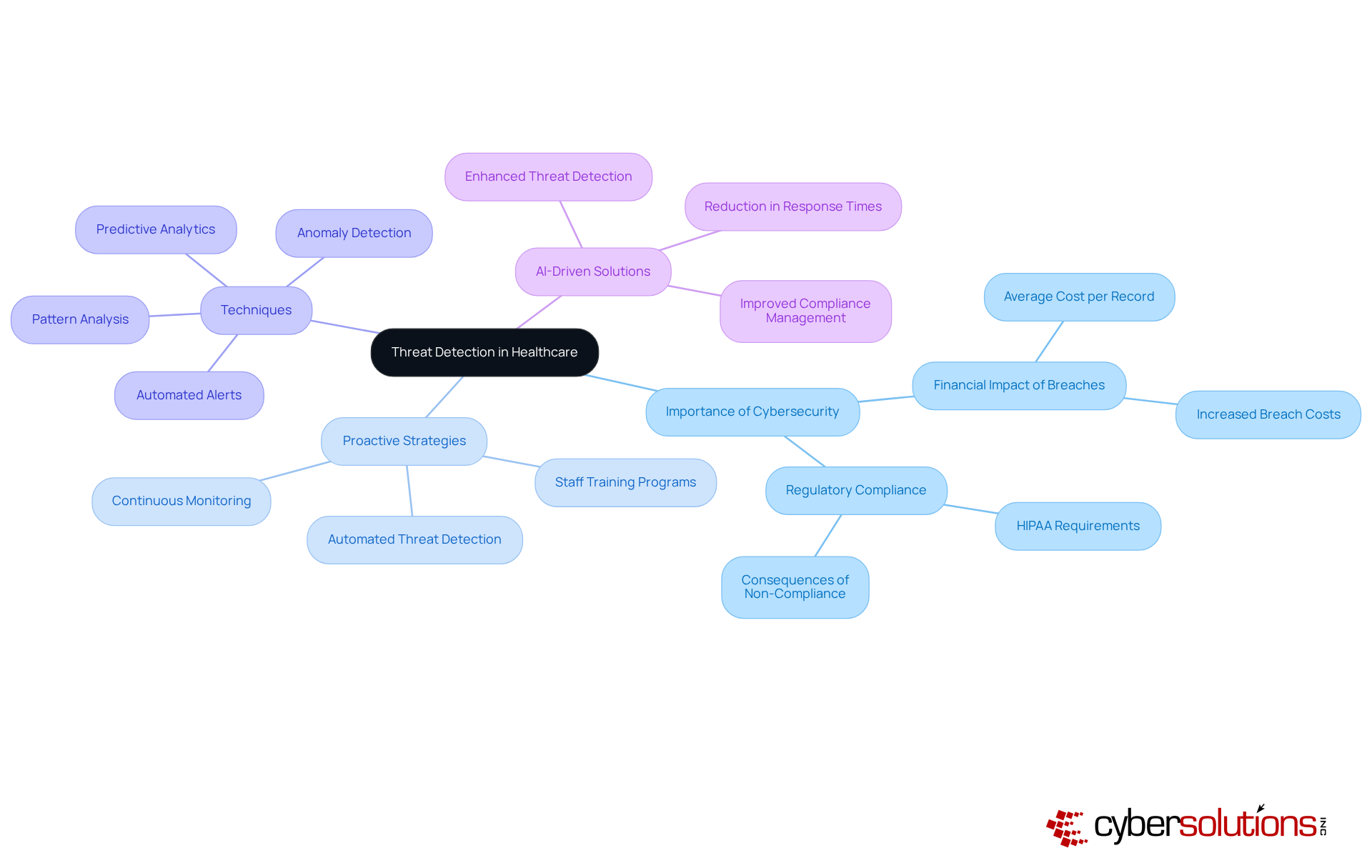
In today's healthcare landscape, the importance of threat detection is paramount. Cyber Solutions harnesses technologies to proactively identify and mitigate risks before they escalate into serious incidents. By continuously monitoring network activity and analyzing potential vulnerabilities, healthcare organizations can respond swiftly to emerging threats. This proactive strategy not only enhances protection but also significantly reduces the financial repercussions of potential breaches. For instance, entities that have implemented AI-driven threat detection report an impressive 70% reduction in response times, enabling them to resolve issues before they compromise patient data.
As emphasized by experts, investing in specialized protective measures is crucial, especially given that data breaches can cost an average of $408 per record. This stark reality underscores the necessity for robust defenses. Effective proactive measures encompass strategies that leverage techniques such as:
These techniques help identify unusual access patterns. Furthermore, comprehensive training programs empower staff to recognize and report potential threats, thereby enhancing overall security.
To further bolster your defenses, consider implementing advanced technologies, along with expert guidance from a Chief Information Security Officer (CISO). This approach ensures your organization remains audit-ready and aligned with regulatory requirements. By prioritizing these strategies, healthcare institutions can fortify their protective stance, safeguard patient information, and preserve their financial well-being.
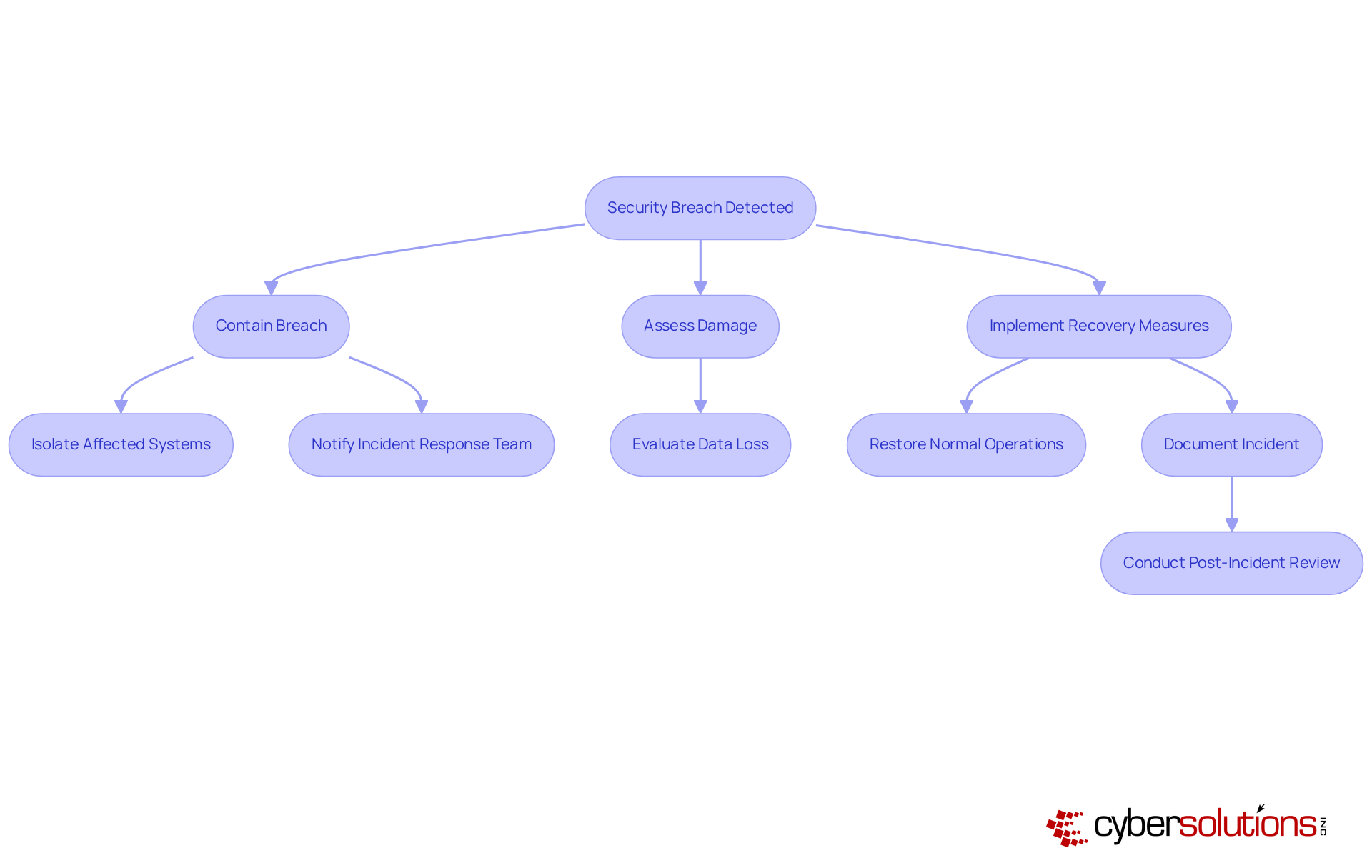
In today's rapidly evolving digital landscape, the importance of incident response cannot be overstated. In the event of a security breach, Cyber Solutions deploys a dedicated team that acts with urgency and precision. This specialized team is equipped to swiftly contain breaches, assess the extent of damage, and implement strategies to restore normal operations. Statistics reveal that entities with a robust incident response plan can recover from a breach, enhancing their ability to respond effectively and uphold compliance with regulations.
Cybersecurity experts emphasize that timely intervention is critical, where the stakes are high. The potential for operational disruption can lead to substantial financial consequences. By effectively managing incidents, teams not only mitigate immediate threats but also protect the entity's reputation, ensuring that patient trust and financial interests remain intact.
The proactive approach of these teams is crucial in minimizing damage. It underscores the necessity for medical entities to prioritize planning as a fundamental element of their cybersecurity strategy. In an era where the integrity of health information is paramount, understanding and implementing robust measures is essential for safeguarding both patient data and organizational stability.
In today's digital landscape, the importance of cybersecurity cannot be overstated. Cyber Solutions conducts regular vulnerability evaluations to pinpoint potential flaws in the IT infrastructure of healthcare entities. By systematically assessing systems and processes, organizations can prioritize remediation efforts, thus fortifying their protective measures. This proactive approach not only mitigates the risk of cyberattacks but also ensures data security, safeguarding the financial health of the organization.
As industry experts emphasize, the continuous identification of security weaknesses is crucial for maintaining compliance and operational integrity. With increasing cyber threats, the necessity for robust security measures has never been more critical. By investing in these evaluations, medical facilities can adeptly navigate the complexities of cybersecurity and compliance, ultimately enhancing their operational resilience.
In conclusion, the vulnerability assessment process is essential for healthcare organizations aiming to protect sensitive information and ensure the trust of their patients. Cyber Solutions is here to assist in this vital endeavor, offering expertise that empowers healthcare entities to stay ahead of emerging threats.

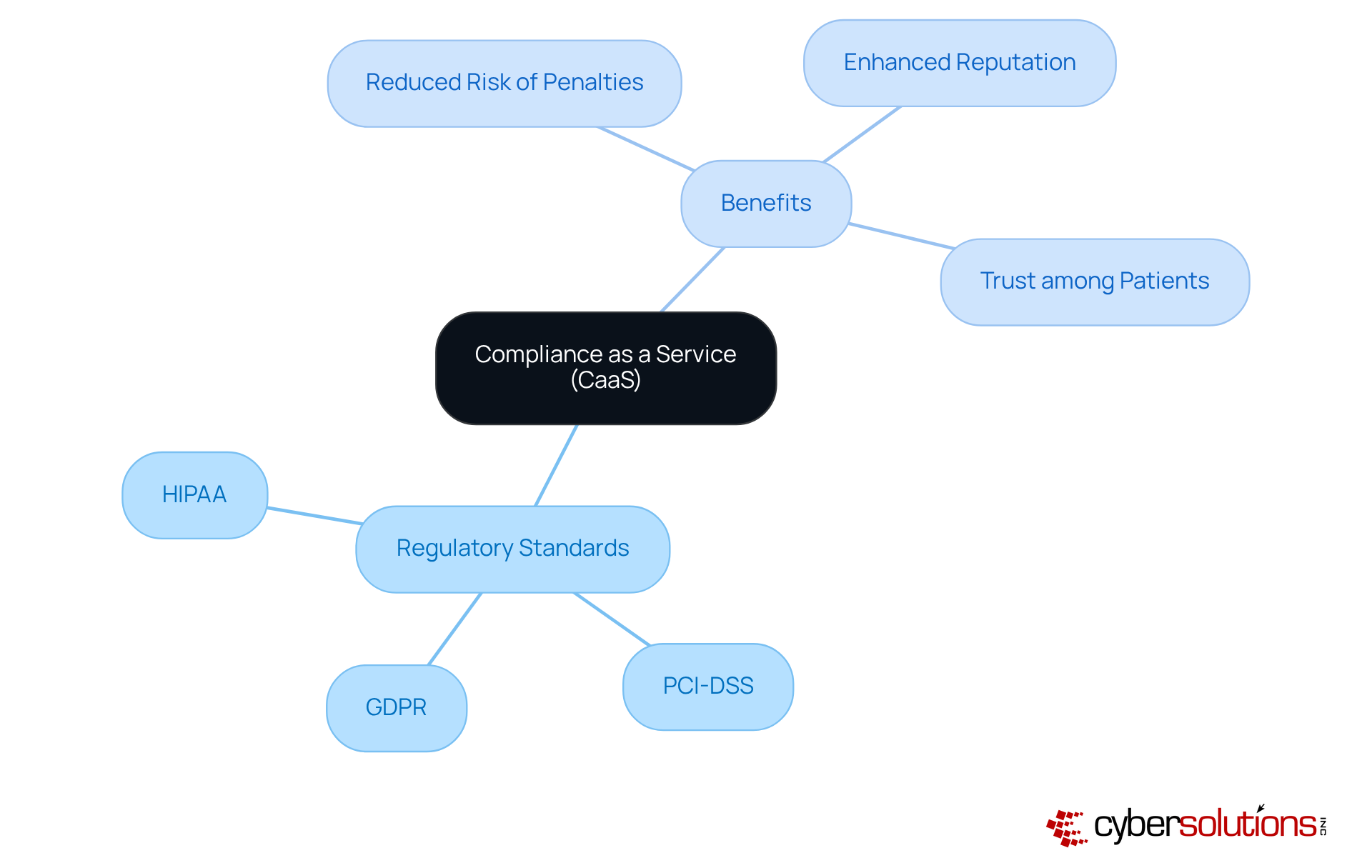
In today's healthcare landscape, compliance is an essential priority. Cyber Solutions offers CaaS, a critical asset for medical entities navigating the intricate web of regulations. This service delivers support such as risk assessments, empowering organizations to adeptly maneuver through these complexities. By leveraging CaaS, healthcare providers can ensure compliance, while simultaneously enhancing their reputation and fostering trust among patients.
Regulatory specialists emphasize that a robust compliance strategy not only shields against financial repercussions but also positions entities as frontrunners in patient care and data protection. Consider this: organizations utilizing CaaS have reported improved adherence to regulations, showcasing the service's vital role in maintaining compliance and mitigating risks in an increasingly regulated environment. With the stakes higher than ever, the question remains: can your organization afford to overlook the importance of compliance in today's digital age?
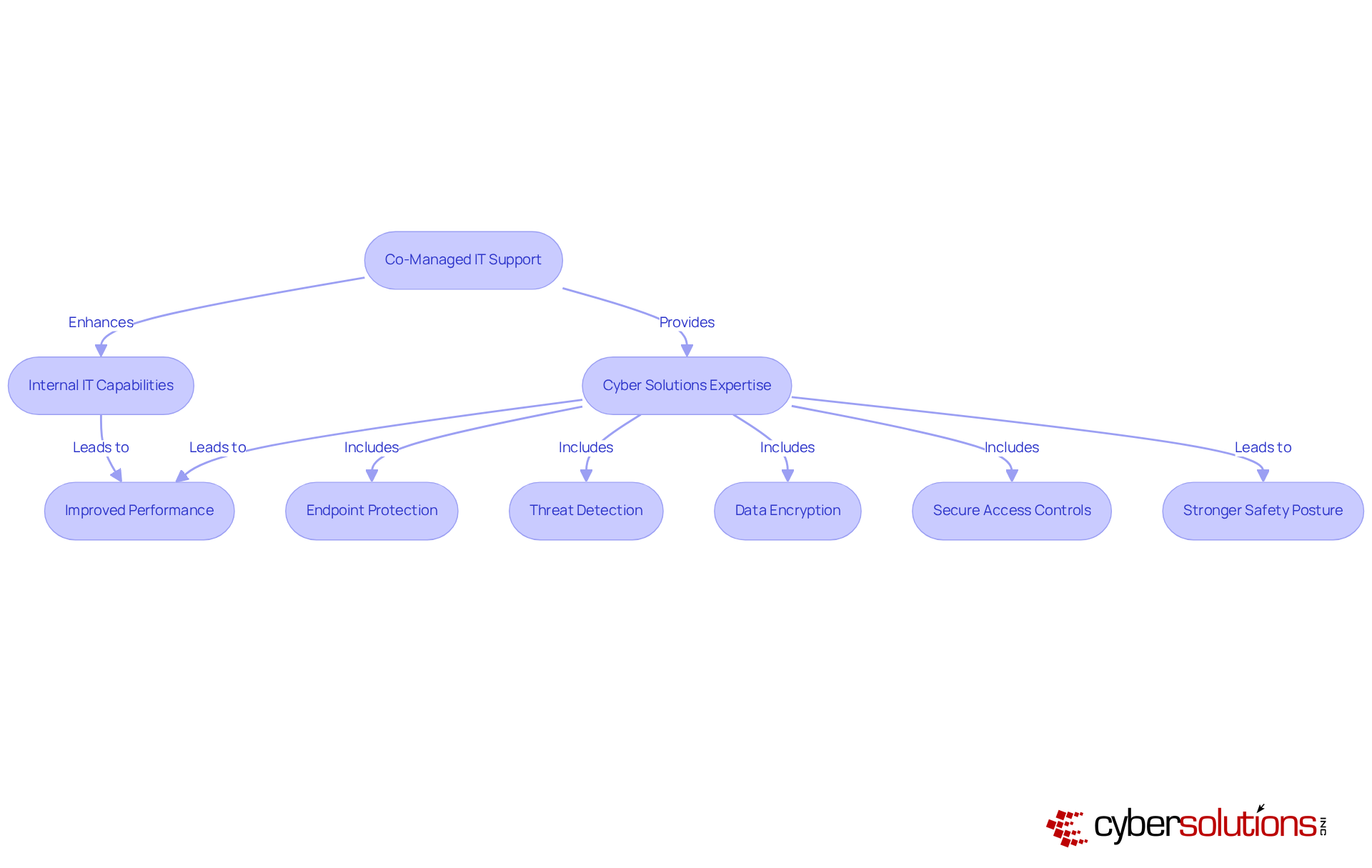
In today's rapidly evolving landscape of cybersecurity threats, healthcare organizations face unique challenges that demand immediate solutions. Cyber Solutions provides services that empower medical facilities to bolster their internal IT capabilities without the burden of extensive hiring. By partnering with Cyber Solutions, these entities gain access to resources that enhance their IT systems for optimal performance and protection. This strategic partnership not only enhances operational efficiency but also enables faster response times. Organizations employing these services report quicker problem resolution and predictable costs—critical factors in the medical field, where downtime can directly impact patient care.
Furthermore, this collaborative model allows IT teams in the medical sector to leverage external expertise while retaining control over their operations. This dynamic ultimately leads to improved outcomes when best practices are implemented. As one IT professional noted, 'We work alongside in-house teams, sharing responsibilities and skills, which fosters a more resilient IT environment.' This partnership is particularly advantageous in maintaining security, ensuring compliance and safeguarding sensitive patient data.
The tailored IT services provided by Cyber Solutions, including network monitoring, threat detection, data encryption, and secure access controls, significantly reduce resolution times for IT issues. Moreover, their swift incident response tactics and organized response plans ensure that threats are managed promptly, while layered recovery methods enhance overall safety. The ongoing support allows organizations to adapt their IT infrastructure as they grow, thereby strengthening their cybersecurity assurance and operational continuity.
In today's healthcare landscape, the importance of robust cybersecurity cannot be overstated. Managed IT services and support from experts provide protection for CFOs in the medical sector by providing a comprehensive range of solutions tailored to their specific requirements. Our industry-focused IT services are designed to meet the distinct needs of healthcare entities, ensuring that organizations can safeguard sensitive patient information.
By outsourcing IT services and support, healthcare organizations can not only lower operational expenses but also enhance their security strategies with advanced tools such as data encryption and threat detection. This ensures adherence to regulatory standards, allowing for better resource allocation. Ultimately, this strategic approach enhances the organization's overall performance while minimizing operational disruption and maintaining a secure environment.
The unique challenges faced by CFOs in the healthcare sector require a knowledgeable partner. Cyber Solutions stands ready to address these challenges effectively, empowering CFOs to navigate the complexities of compliance and security with confidence.
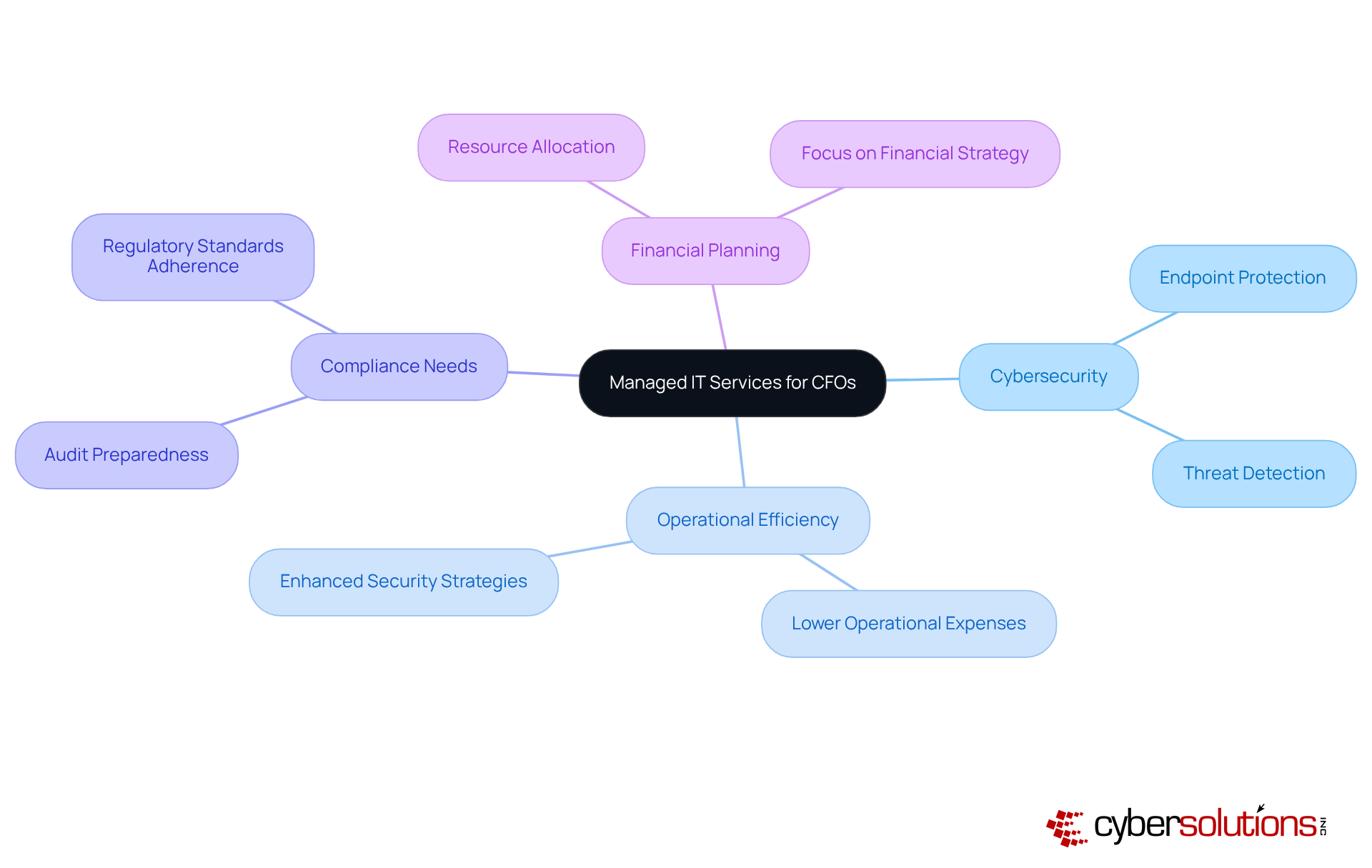
In the intricate landscape of healthcare, the significance of Managed IT Services has reached unprecedented heights, particularly for CFOs who are grappling with the complexities of operational efficiency and cybersecurity. By harnessing customized IT solutions, healthcare organizations can significantly bolster their operational capabilities while adhering to rigorous compliance standards. This strategic alliance empowers CFOs to concentrate on financial stewardship and resource allocation, ultimately enhancing patient care and organizational performance.
The article highlights several pivotal aspects that underscore the necessity of comprehensive managed IT support:
Each service is essential in upholding the integrity of healthcare operations, further strengthening the security posture of medical facilities and ensuring they are well-equipped to confront emerging cyber threats.
As the healthcare environment continues to evolve, adopting managed IT services is imperative for organizations striving to excel amidst escalating challenges. CFOs are urged to assess their existing IT frameworks and consider collaboration with seasoned providers like Cyber Solutions. This forward-thinking approach not only addresses immediate IT issues but also positions healthcare entities for sustained success in a swiftly transforming digital landscape, reinforcing the urgent need for robust cybersecurity and operational efficiency.
What services does Cyber Solutions Inc. provide for healthcare organizations?
Cyber Solutions Inc. provides a comprehensive suite of managed IT services and support specifically tailored for medical organizations, focusing on enhancing operational efficiency and cybersecurity.
Why is cybersecurity important in healthcare?
Cybersecurity is crucial in healthcare due to the sensitive nature of patient information and the increasing prevalence of cyber threats, which can lead to significant data breaches and operational disruptions.
How does Cyber Solutions help CFOs in healthcare organizations?
Cyber Solutions empowers CFOs by offering customized IT solutions that address security and compliance requirements, enabling them to allocate resources more effectively and focus on quality treatment without IT management distractions.
What are the projected growth rates for the medical IT market?
The medical IT market is projected to expand at a compound annual growth rate of 19.8% from 2022 to 2027.
What impact does effective IT support have on healthcare organizations?
Effective IT support streamlines operations, enhances organizational performance, reduces downtime, and improves compliance, ultimately leading to better financial outcomes and patient care.
Can you provide an example of Cyber Solutions' impact on a medical institution?
A case study showed that a medical institution decreased manual workloads by five times in pharmacy claim processing through efficient IT assistance provided by Cyber Solutions.
What type of support does Cyber Solutions offer for incident response?
Cyber Solutions offers rapid incident response strategies, including 24-hour on-site support and layered recovery approaches, to ensure minimal operational disruption and bolster cybersecurity confidence.
How does 24/7 help desk support benefit healthcare organizations?
24/7 help desk support ensures prompt access to IT assistance, significantly reducing downtime and allowing medical personnel to focus on patient care, ultimately enhancing operational efficiency.
What are the risks of downtime for medical organizations?
Downtime can cost medical organizations approximately $1.9 million per day, and the average time to restore IT systems after an incident exceeds 17 days.
What is endpoint protection and why is it important?
Endpoint protection is a security measure that safeguards devices from cyber threats, essential for protecting sensitive patient data and ensuring compliance with regulations like HIPAA.
What strategies does Cyber Solutions use for endpoint protection?
Cyber Solutions employs advanced security measures such as encryption, multi-factor authentication, continuous monitoring, and threat identification to protect medical devices from cyber threats.
What should healthcare CFOs consider regarding their endpoint protection strategies?
Healthcare CFOs are encouraged to evaluate their current endpoint protection strategies and consider partnering with Cyber Solutions to enhance their security posture against cyber threats.