Introduction
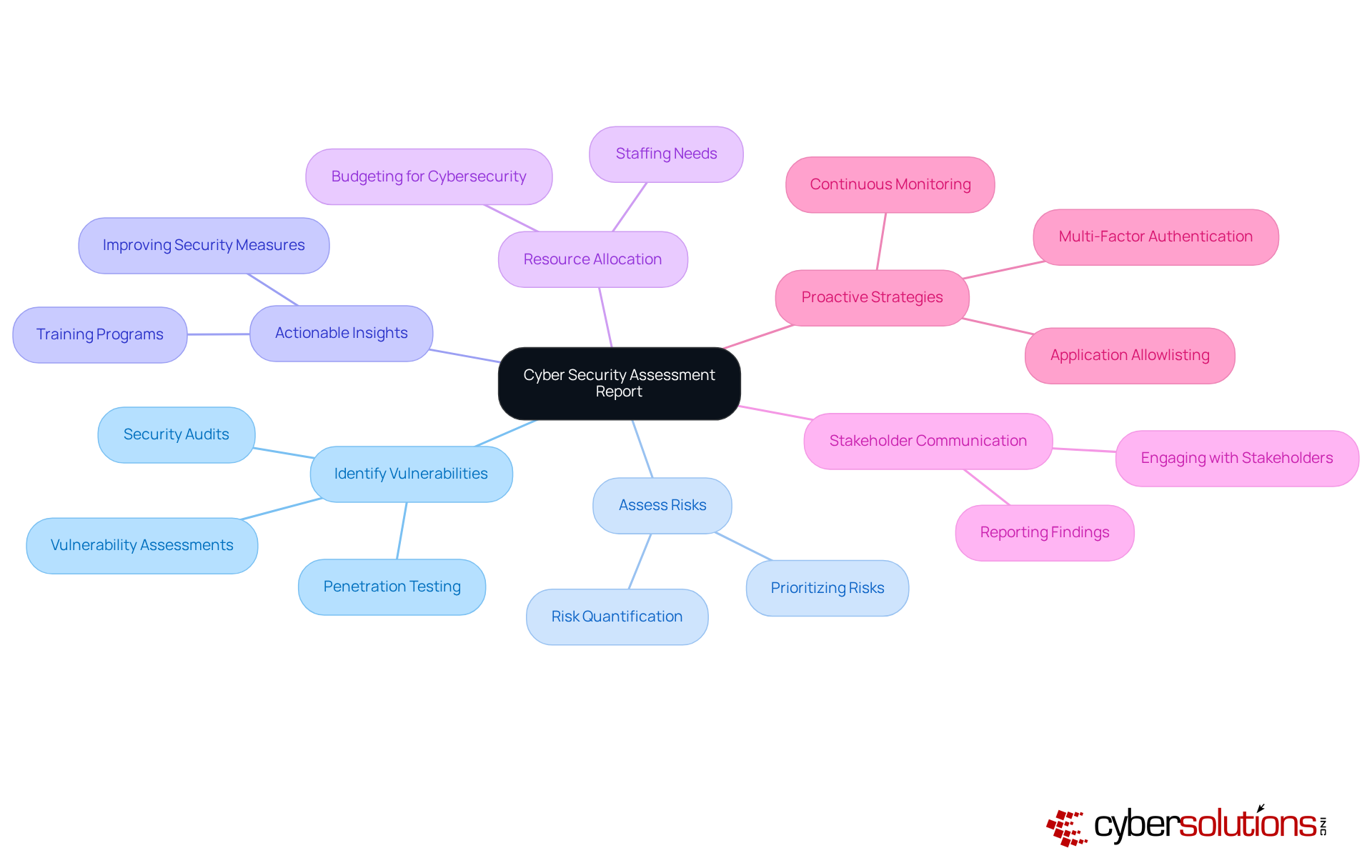
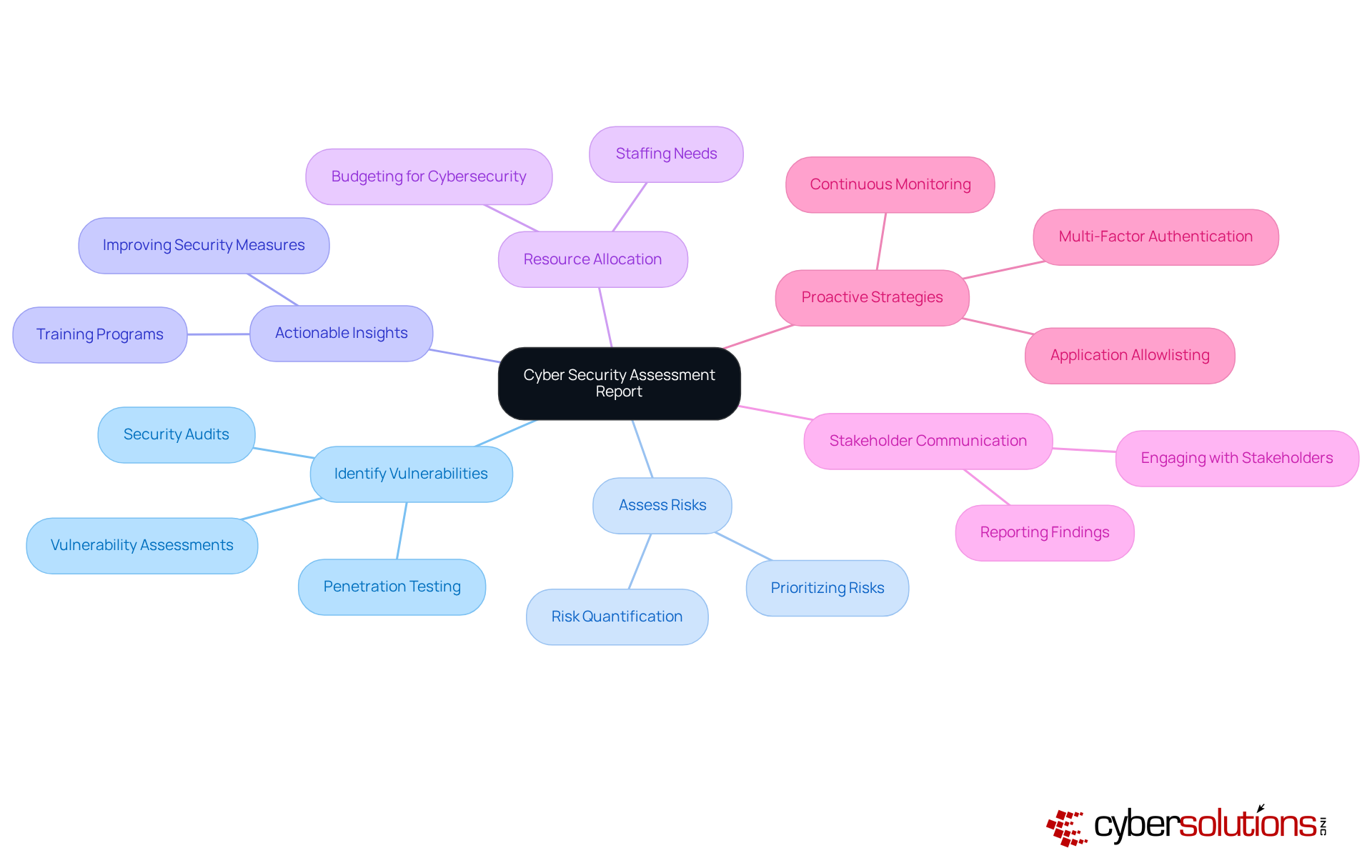
In today's world, where cyber threats are a pressing concern, especially in critical sectors like healthcare, grasping the nuances of a Cyber Security Assessment Report is essential. This vital document not only identifies vulnerabilities and risks but also provides organizations with actionable insights to strengthen their defenses. With the landscape of cyber threats constantly evolving, how can healthcare entities ensure their assessment reports are thorough and effective in tackling these challenges?
Healthcare organizations face unique challenges in safeguarding sensitive information. The stakes are high; a breach can lead to devastating consequences, not just financially but also in terms of patient trust and safety. As CFOs navigate these turbulent waters, understanding the intricacies of cybersecurity becomes paramount.
Cyber Solutions can play a crucial role in addressing these challenges. By leveraging comprehensive assessment reports, healthcare entities can identify weaknesses and implement strategies to mitigate risks effectively. This proactive approach not only enhances security but also fosters a culture of resilience within the organization.
In conclusion, as cyber threats continue to evolve, the importance of a robust Cyber Security Assessment Report cannot be overstated. Organizations must prioritize these assessments to protect their assets and ensure the safety of their patients.
Understand the Purpose of a Cyber Security Assessment Report
In today's digital landscape, the importance of cybersecurity cannot be overstated. A cyber security assessment report serves as a crucial document that outlines a company's current protective stance. Its primary goal is to identify vulnerabilities, assess risks, and provide recommendations to mitigate potential threats. By understanding the significance of the assessment report, healthcare organizations can allocate resources more effectively, prioritize protective measures, and ensure safety.
This not only aids in managing threats but also enhances communication with stakeholders by providing a clear overview of the organization's security posture. Moreover, implementing strategies such as endpoint protection can significantly strengthen defenses. This proactive measure prevents unauthorized software from executing, thereby reducing risks and ensuring compliance with stringent regulations like HIPAA and GDPR.
Such a proactive approach is vital for protecting against malware, ransomware, and phishing attacks. It becomes an essential element of any comprehensive cybersecurity strategy. As healthcare organizations navigate these challenges, the need for robust security measures becomes increasingly clear. Are you prepared to safeguard your organization against evolving threats?
Identify Key Components of the Assessment Report
To create a robust assessment report, it’s essential to include several key components that not only inform but also drive action:
- Overview: Start with a concise overview of the assessment findings and recommendations. This allows stakeholders to quickly grasp the report's significance. An effective summary is critical; studies show that well-crafted summaries significantly enhance comprehension and retention of key information, ultimately influencing decision-making.
- Scope: Clearly define the systems, timeframes, and audiences covered in the assessment. This clarity ensures that all stakeholders understand the boundaries of the evaluation and the context of the findings presented in the report, fostering a shared understanding.
- Methodology: Outline the approach taken to conduct the assessment, including the tools and techniques used. A clear methodology enhances transparency and credibility, as demonstrated in the assessment, showcasing a thorough process.
- Results: Present the recognized weaknesses, threats, and dangers. For instance, highlighting that 72% of leaders reported an increase in organizational risks.
- Suggestions: Offer practical steps to mitigate identified risks and enhance protective measures. Recommendations should be tailored to the organization's unique context, ensuring they are feasible and effective. This may include specific remediation strategies such as policy updates and system upgrades to address vulnerabilities.
- Appendices: Include any supporting documents, data, or additional information relevant to the assessment. This section can provide deeper insights and context, helping to substantiate the findings and recommendations presented in the report. It ensures alignment with standards necessary for protecting Controlled Unclassified Information (CUI) and Federal Contract Information (FCI). Such preparation is essential for compliance.

Conduct the Cyber Security Assessment
To conduct a cyber security assessment effectively, it’s essential to follow these critical steps:
- Define the Scope: Clearly outline the systems, applications, and networks that will be assessed. This step is crucial as it sets the boundaries for the assessment, ensuring that all critical areas are covered. For instance, a manufacturing company might focus on production systems and sensitive customer data, while a financial institution may prioritize transaction processing systems and client information. Cyber Solutions provides customized IT services that meet the distinct requirements for protection and compliance across several sectors, such as healthcare, finance, manufacturing, and government.
- Collect Information: Utilize tools such as threat scanners, logs, and event management systems to gather relevant data. Automated flaw detection tools can recognize known weaknesses based on industry databases, which is crucial since 60% of data breaches arise from unaddressed issues. Additionally, consider employing advanced threat detection tools to enhance your data collection efforts.
- Inventory Assets: Catalog all digital assets, including hardware, software, and data, to understand what needs protection. This inventory should encompass everything from servers and applications to sensitive data repositories, ensuring that no critical asset is overlooked.
- Analyze Data: Analyze the collected data to identify weaknesses in the security posture. Regular evaluations are crucial, as they assist organizations in staying ahead of threats; for instance, SQL Injection remains a common weakness, underscoring the necessity for ongoing vigilance. Cyber Solutions provides comprehensive assessments designed to protect operations against evolving cyber threats.
- Evaluate Threats: Identify potential threats that could exploit recognized weaknesses. Understanding the threat landscape is crucial, especially as ransomware attacks surged by 78% in 2023, emphasizing the need for proactive measures.
- Document Findings: Record all findings systematically to ensure they are easily referenced in the report. A thorough report should include detailed descriptions of risks, susceptibility assessments, and recommendations for mitigation, enabling informed decision-making and prioritization of resources. Additionally, Cyber Solutions emphasizes the importance of preparing essential documentation, including security policies and procedures, to demonstrate compliance during audits.

Analyze and Interpret Assessment Findings
Once the assessment is complete, it’s crucial to analyze the findings through a structured approach:
- Prioritize Risks: Begin by ranking identified weaknesses according to their potential impact and likelihood of exploitation. For instance, consider that 76% of entities are expected to face at least one breach each year. This statistic underscores the necessity of addressing significant risks promptly.
- Contextualize Findings: Next, relate your findings to the specific context of the organization, taking into account industry standards and regulatory requirements. With 46% of organizations facing compliance challenges, grasping the regulatory implications is vital for ensuring security.
- Identify Trends: Look for patterns within the data that may reveal systemic issues or recurring vulnerabilities. For example, the recent data breach report, which highlights the urgent need for improved security measures.
- Develop Insights: Transform your findings into actionable insights that can steer decision-making and resource allocation. Employing statistical analysis can sharpen decision-making precision, providing a clearer perspective on exposure and necessary interventions.
- Prepare for Recommendations: Finally, leverage your analysis to inform the recommendations section of the report, ensuring that they are both targeted and relevant. Establishing a system for continuous threat monitoring can aid in tracking current and emerging dangers, ensuring that your suggestions remain aligned with evolving challenges.

Finalize the Report with Recommendations and Next Steps
To finalize the report, follow these essential steps:
- Summarize Findings: Begin with a concise summary of the main discoveries from the evaluation, highlighting vulnerabilities and threats.
- Develop Recommendations: Create recommendations based on the prioritized risks identified during the analysis phase. These should be specific, measurable, achievable, relevant, and time-bound (SMART). For example, implementing multi-factor authentication (MFA) can greatly enhance protection, as it reduces unauthorized access. Moreover, companies typically allocate around 12% of their IT budgets to cybersecurity measures, underscoring the importance of investment.
- Outline Next Steps: Suggest immediate actions the organization can take to mitigate identified vulnerabilities and strengthen its security posture. This may involve upgrading email spam filters to combat phishing attacks, which account for nearly 90% of data breaches. Acting swiftly is crucial, as organizations that do so can significantly reduce the average time to implement recommendations, often delayed by bureaucratic processes.
- Review and Revise: Ensure the report is clear, concise, and free of jargon. Gather feedback from stakeholders and revise the document as needed to enhance its effectiveness.
- Distribute the Report: Share the finalized report with relevant stakeholders, ensuring it reaches decision-makers who can implement the recommendations. Timely distribution is vital, as organizations that act quickly on cybersecurity evaluations can improve their security posture, which is frequently extended by bureaucratic procedures.
By following these steps, organizations can create a comprehensive report that not only highlights vulnerabilities but also outlines a clear strategy for improving their security measures.

Conclusion
Creating a comprehensive cybersecurity assessment report is not just important; it’s essential for any organization determined to protect its digital assets from a growing array of threats. By diligently following the outlined steps, stakeholders can clearly understand their current security posture, pinpoint vulnerabilities, and implement effective strategies to mitigate risks. This report acts as a roadmap for enhancing security and serves as a vital communication tool among stakeholders, ensuring everyone is aligned on the organization’s protective measures.
Key components such as an executive summary, scope definition, and actionable recommendations are crucial in crafting an effective report. Each element plays a pivotal role in conveying the assessment’s findings and guiding the organization toward improved security practices. The emphasis on continuous monitoring and adaptation to emerging threats underscores the necessity of a proactive approach in the ever-evolving cyber landscape.
Given the increasing frequency and sophistication of cyber threats, organizations must prioritize developing and executing cybersecurity assessment reports. By doing so, they not only protect sensitive information but also foster a culture of security awareness and compliance within their teams. Taking decisive action based on insights gained from these assessments can significantly enhance an organization’s resilience against cyber attacks. Engaging in this critical process without delay is imperative.
Frequently Asked Questions
What is the purpose of a cyber security assessment report in healthcare?
The purpose of a cyber security assessment report is to outline a company's current protective stance by identifying vulnerabilities, assessing risks, and providing actionable insights to mitigate potential threats. It helps healthcare organizations allocate resources effectively, prioritize protective measures, and ensure compliance with industry regulations.
How does a cyber security assessment report enhance communication with stakeholders?
The report provides a clear overview of the organization's security posture, which aids in managing threats and enhances communication with stakeholders by summarizing key findings and recommendations.
What is application allowlisting and why is it important?
Application allowlisting is a proactive security measure that prevents unauthorized software from executing. It is important because it reduces the attack surface and ensures compliance with regulations such as HIPAA and PCI-DSS, protecting against malware, ransomware, and phishing attacks.
What are the key components of a robust cyber security assessment report?
The key components include: - Executive Summary: A concise overview of findings and recommendations. - Scope of Assessment: Definition of systems, timeframes, and audiences covered. - Methodology: Outline of the approach and tools used in the assessment. - Results: Presentation of recognized weaknesses, threats, and dangers. - Suggestions: Practical steps to mitigate identified risks. - Appendices: Supporting documents and additional information relevant to the assessment.
Why is an executive summary critical in a cyber security assessment report?
An effective executive summary is critical because it allows stakeholders to quickly grasp the report's significance and enhances comprehension and retention of key information, ultimately influencing decision-making.
What should be included in the scope of assessment?
The scope of assessment should clearly define the systems, timeframes, and audiences covered to ensure that all stakeholders understand the boundaries of the evaluation and the context of the findings.
How does outlining the methodology promote trust in the assessment report?
A transparent methodology promotes trust and credibility by showcasing a systematic approach to identifying weaknesses and threats, thereby enhancing the reliability of the assessment findings.
What types of suggestions should be included in the assessment report?
Suggestions should offer practical steps to mitigate identified risks and enhance protective measures, tailored to the organization's unique context. This may include specific remediation strategies such as policy updates and system upgrades.
What role do appendices play in the cyber security assessment report?
Appendices include supporting documents, data, or additional information relevant to the assessment, providing deeper insights and context to substantiate the findings and recommendations, and ensuring alignment with cybersecurity standards.
List of Sources
- Understand the Purpose of a Cyber Security Assessment Report
- The Critical Role of Regular Cybersecurity Assessments in Risk… (https://visualedgeit.com/blog/the-critical-role-of-regular-cybersecurity-assessments-in-risk-management)
- huntress.com (https://huntress.com/blog/cybersecurity-statistics)
- 45 Cybersecurity Statistics and Facts [2025] (https://onlinedegrees.sandiego.edu/cyber-security-statistics)
- U.S. Businesses Strengthen Strategy with Cyber Security Audits Amid Rising Digital Threats (https://einpresswire.com/article/874504457/u-s-businesses-strengthen-strategy-with-cyber-security-audits-amid-rising-digital-threats)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Identify Key Components of the Assessment Report
- Top Cybersecurity Metrics and KPIs for 2026 | UpGuard (https://upguard.com/blog/cybersecurity-metrics)
- Tips for Creating a Strong Cybersecurity Assessment Report (https://sans.org/blog/tips-for-creating-a-strong-cybersecurity-assessment-report)
- secureframe.com (https://secureframe.com/blog/cybersecurity-statistics)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Conduct the Cyber Security Assessment
- Why and How to Perform Cybersecurity Risk Assessments in 2026 (https://maddevs.io/blog/how-to-perform-cybersecurity-risk-assessments)
- deliberatedirections.com (https://deliberatedirections.com/cybersecurity-quotes)
- The Top 20 Expert Quotes On Cyber Risk and Security (https://surtech.co.za/20-expert-quotes-on-cyber-risk-and-security)
- The top 20 expert quotes from the Cyber Risk Virtual Summit (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- Vulnerability Statistics Report (https://edgescan.com/stats-report)
- Analyze and Interpret Assessment Findings
- cybersecuritydive.com (https://cybersecuritydive.com)
- Cyber Risk Management Statistics 2025-2026 (https://c-risk.com/statistics)
- zengrc.com (https://zengrc.com/blog/the-statistical-analysis-of-measuring-cybersecurity-risk)
- 50+ Risk Management Statistics to Know in 2026 (https://secureframe.com/blog/risk-management-statistics)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Finalize the Report with Recommendations and Next Steps
- What Will a Cyber Security Assessment Report Show? 10 Common Findings & Recommendations (https://vc3.com/blog/cyber-security-assessment-report-findings-recommendations)
- Cybersecurity statistics: 100+ stats to know in 2025 (https://cybersecurity.asee.io/blog/cybersecurity-statistics)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- 45 Cybersecurity Statistics and Facts [2025] (https://onlinedegrees.sandiego.edu/cyber-security-statistics)
- Top Cybersecurity Statistics: Facts, Stats and Breaches for 2025 (https://fortinet.com/resources/cyberglossary/cybersecurity-statistics)