
The rapid evolution of technology is fundamentally reshaping how businesses operate. Virtual Desktop as a Service (DaaS) stands out as a transformative solution in the IT landscape, enhancing flexibility and mobility while providing a cost-effective alternative to traditional desktop infrastructures. However, as organizations increasingly embrace DaaS, they encounter critical decisions regarding its implementation and optimization.
How can companies effectively navigate the complexities of adopting DaaS to maximize efficiency and drive success? This question is pivotal as businesses seek to leverage the full potential of this innovative technology.
Virtual Environment as a Service (VaaS) is revolutionizing the way users interact with technology, offering virtual workspaces accessible via the internet. Unlike traditional setups where operating systems and software reside on local machines, virtual desktop as a service (DaaS) provides these environments on remote servers managed by external providers. This innovative model empowers users to access their desktops from any device with an internet connection, enhancing flexibility and mobility.
DaaS solutions come equipped with features such as centralized management, automatic updates, and security measures. These attributes make them an attractive option for companies looking to improve productivity and reduce costs. In fact, the DaaS market is expanding, with projections indicating significant growth, increased adoption rates, and a compound annual growth rate (CAGR) exceeding 19.4% through 2035. This surge reflects the increasing demand for cloud-based solutions, particularly for virtual desktop as a service, driven by trends in remote work and BYOD policies, alongside the necessity for efficient, scalable IT solutions.
Key players in the Desktop as a Service market include industry giants like:
These companies are not only shaping the competitive landscape but also fostering innovation in cloud-based computing solutions. As organizations navigate the complexities of modern IT environments, the adoption of DaaS could be the strategic move that enhances operational efficiency and drives business success.

While both DaaS and VDI offer virtual desktop solutions, they differ significantly in management and deployment. VDI requires organizations to maintain their own hardware and software infrastructure, leading to higher upfront costs and ongoing maintenance expenses. In contrast, DaaS operates on a subscription-based model where the service provider manages the infrastructure, allowing companies to avoid capital expenses and reduce operational costs. Moreover, DaaS enhances scalability, enabling businesses to swiftly adjust their desktop resources according to fluctuating demands without significant IT involvement.
However, C-suite leaders must be aware of common pitfalls associated with both models. For instance, while DaaS can lower initial expenses, it’s crucial for companies to choose a reliable service provider to prevent potential service interruptions. Conversely, VDI may offer greater control over the environment but can result in unexpected costs if not managed properly.
To illustrate the effectiveness of DaaS, consider a mid-sized healthcare organization that transitioned from VDI to DaaS. By adopting DaaS, they not only reduced their IT overhead by 30% but also improved their ability to scale resources during peak patient intake periods. This flexibility allowed them to maintain service levels without compromising service quality.
Furthermore, social media platforms and Facebook can enhance engagement and provide valuable insights to peers in the industry.

Implementing virtual desktop as a service is not just a trend; it’s a strategic move that offers organizations a wealth of advantages.

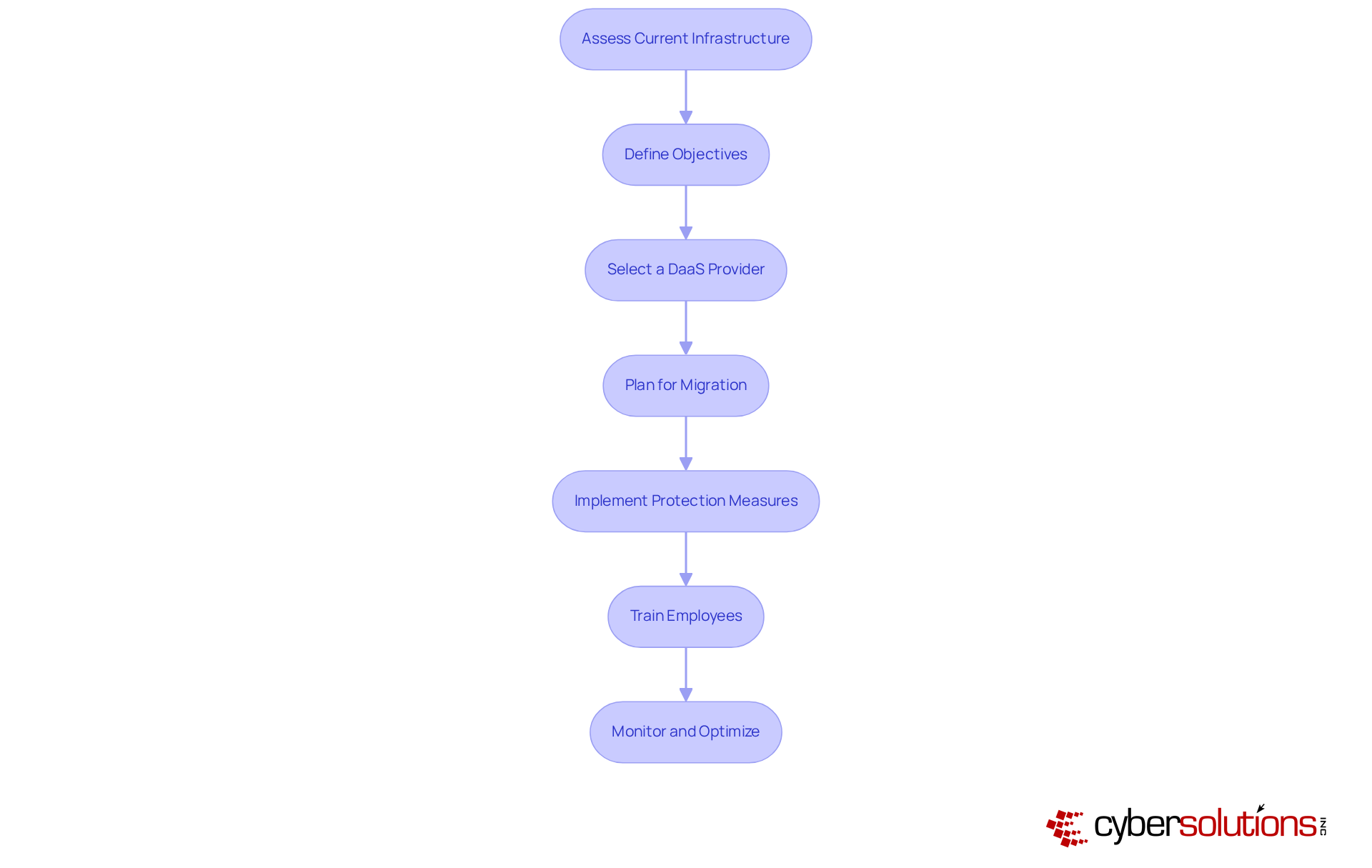
To successfully implement DaaS, organizations must take decisive action. Here’s how to navigate this transformative journey:
By following these steps, organizations can effectively harness the power of DaaS, transforming their IT landscape and enhancing operational efficiency.
Embracing Virtual Desktop as a Service (DaaS) is not just a trend; it’s a pivotal shift in how organizations manage their IT environments. By leveraging cloud-based solutions, businesses can significantly enhance flexibility, reduce costs, and improve operational efficiency. The ability of DaaS to streamline processes and adapt to the evolving demands of the workforce highlights its critical role in modern IT strategies.
This article has illuminated the numerous advantages of DaaS over traditional Virtual Desktop Infrastructure (VDI). From cost efficiency and scalability to enhanced security and simplified management, DaaS presents a compelling case for organizations eager to modernize their desktop solutions. The outlined steps for successful implementation act as a roadmap, guiding organizations through this transition effectively, ensuring they maximize benefits while minimizing disruption.
Ultimately, adopting DaaS transcends a mere technological upgrade; it’s a strategic decision that can propel business success in a competitive landscape. Organizations must evaluate their current IT infrastructures, define clear objectives, and select the right service providers to fully harness the potential of DaaS. By doing so, they position themselves to thrive in an increasingly digital world, where flexibility and efficiency are not just advantages but necessities.
What is Virtual Desktop as a Service (DaaS)?
Virtual Desktop as a Service (DaaS) is a cloud computing model that provides virtual workspaces accessible via the internet, where operating systems and software are hosted on remote servers managed by external providers.
How does DaaS differ from traditional desktop setups?
Unlike traditional setups where operating systems and software are installed on local machines, DaaS allows users to access their desktops from any device with an internet connection, enhancing flexibility and mobility.
What features are included in DaaS solutions?
DaaS solutions typically include centralized management, automatic updates, and robust security measures, making them a favorable option for companies looking to streamline IT operations and reduce costs.
What is the market outlook for DaaS?
The virtual desktop as a service market was valued at over USD 9.82 billion in 2025 and is projected to reach USD 11.53 billion in 2026, with a compound annual growth rate (CAGR) exceeding 19.4% through 2035, reflecting increasing demand for cloud-based services.
What factors are driving the growth of DaaS?
The growth of DaaS is driven by trends in remote work, Bring Your Own Device (BYOD) policies, and the need for efficient, scalable IT solutions.
Who are the key players in the DaaS market?
Key players in the DaaS market include VMware, Citrix Systems, Microsoft, Google Cloud, and Amazon Web Services, which are shaping the competitive landscape and fostering innovation in cloud-based computing solutions.
How can DaaS benefit organizations?
DaaS can enhance operational efficiency and drive business success by providing flexible, scalable, and cost-effective IT solutions that meet the complexities of modern IT environments.